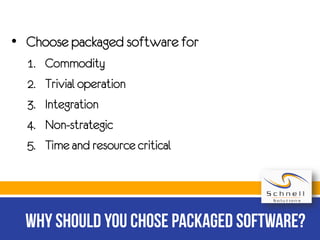
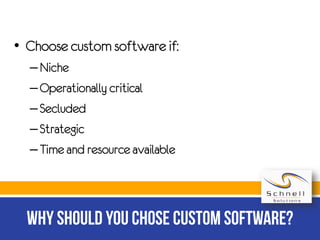
The document discusses two types of software: custom software, tailored for specific organizational needs, and packaged software, which is readily available for the general public. Custom software involves a detailed development process but can be more expensive and time-consuming, while packaged software is less costly and leverages economies of scale. The text also seeks to promote Schnell Solutions Limited as a provider of bespoke software development services.