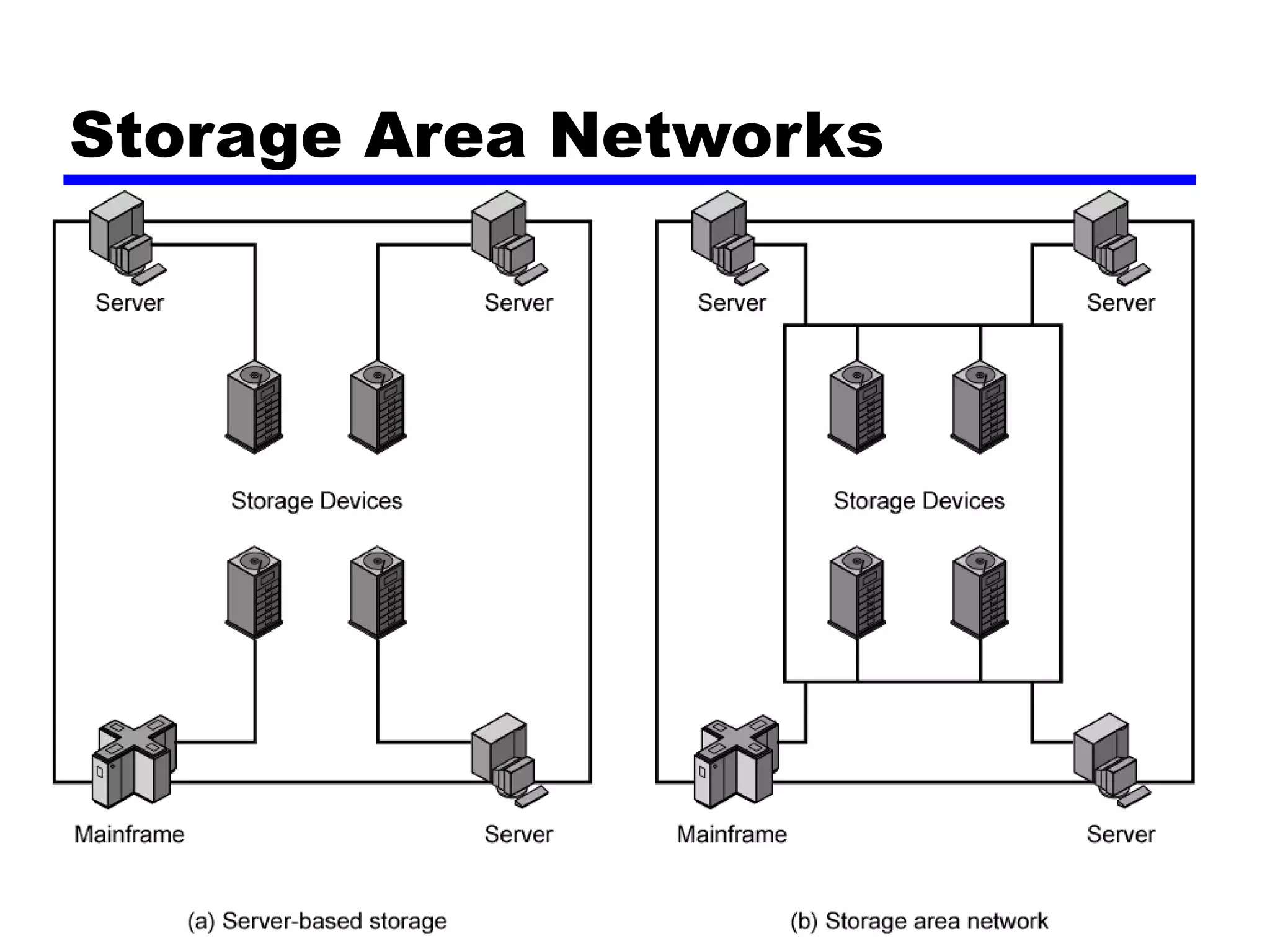
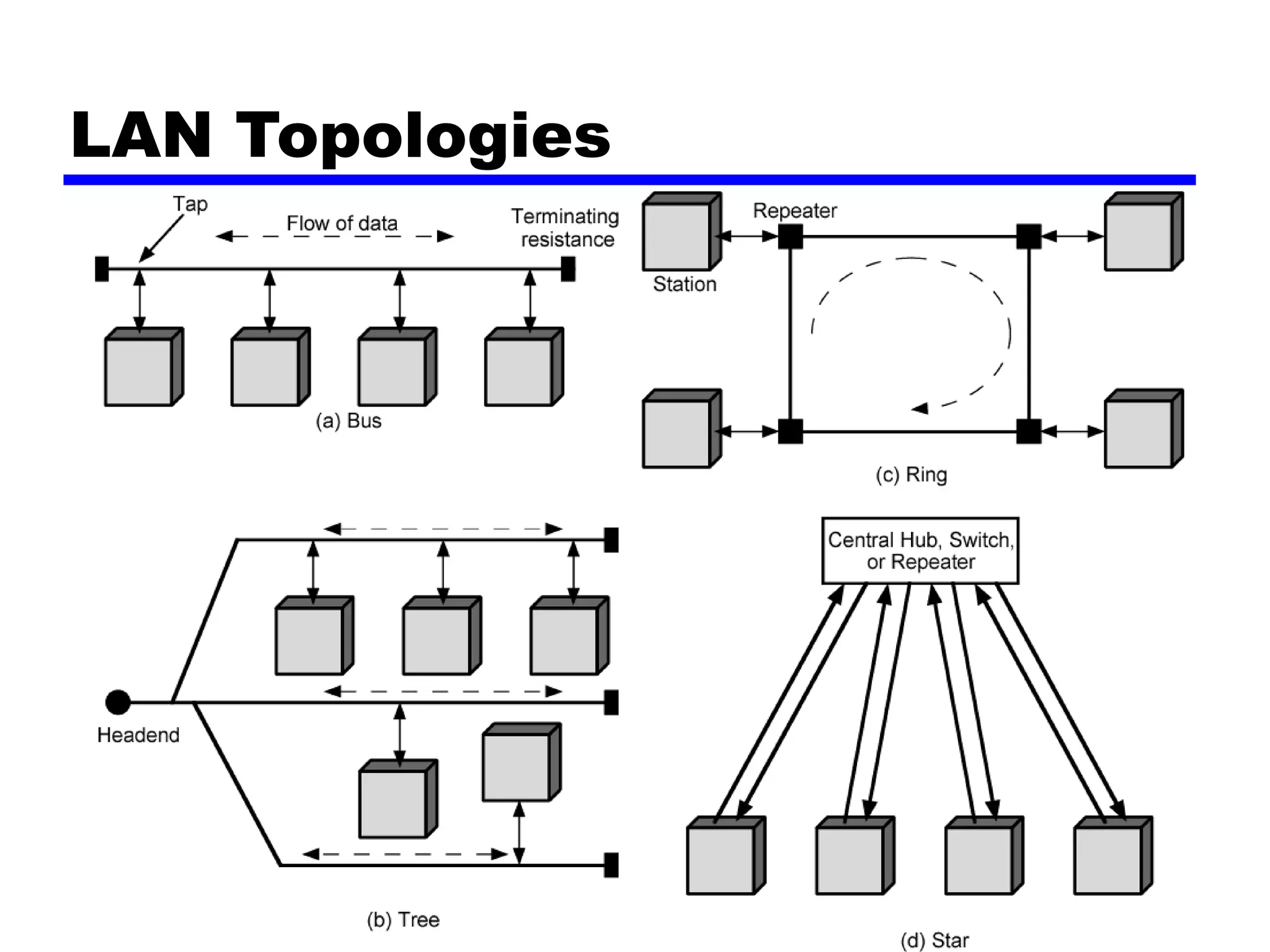
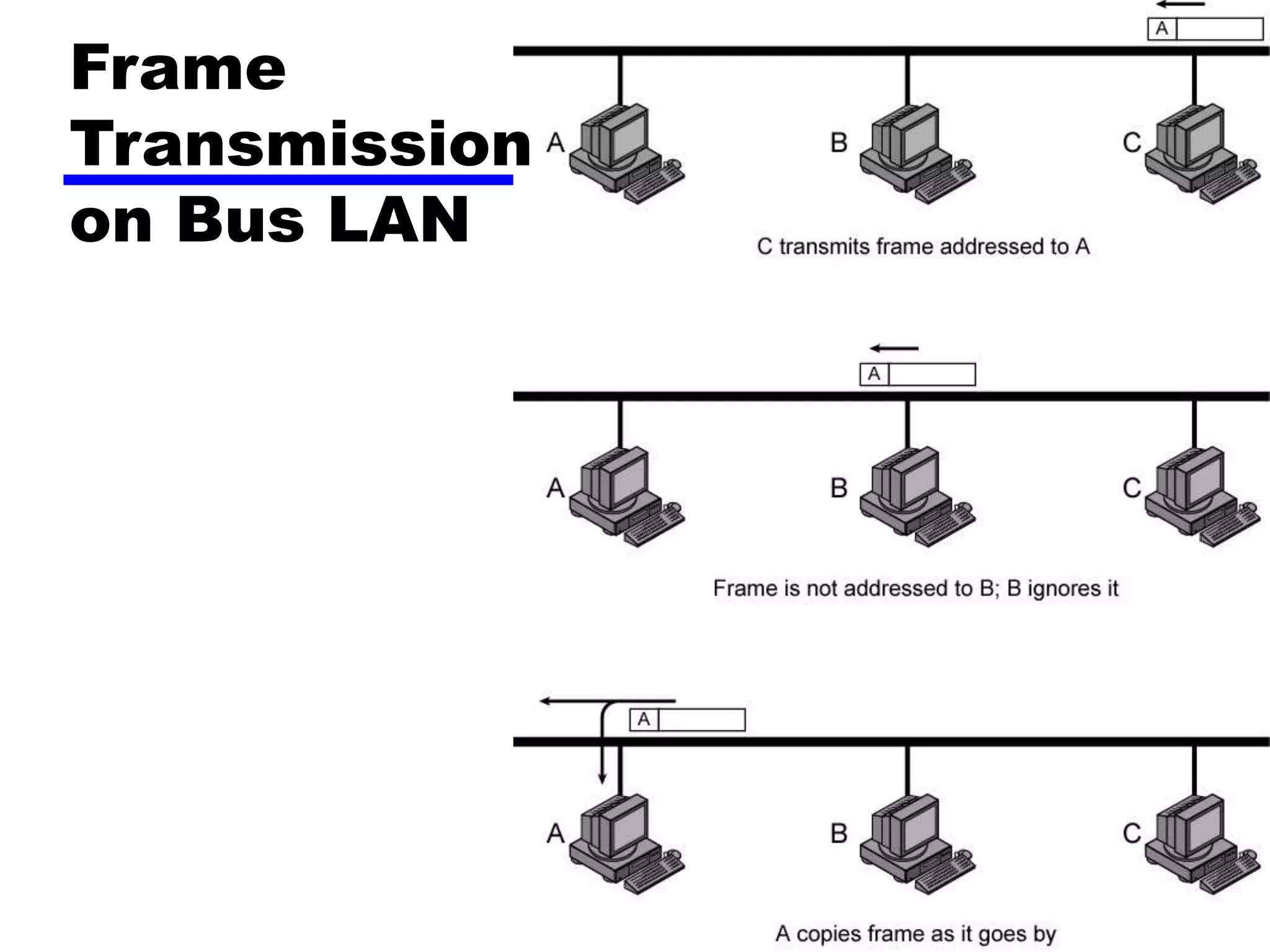
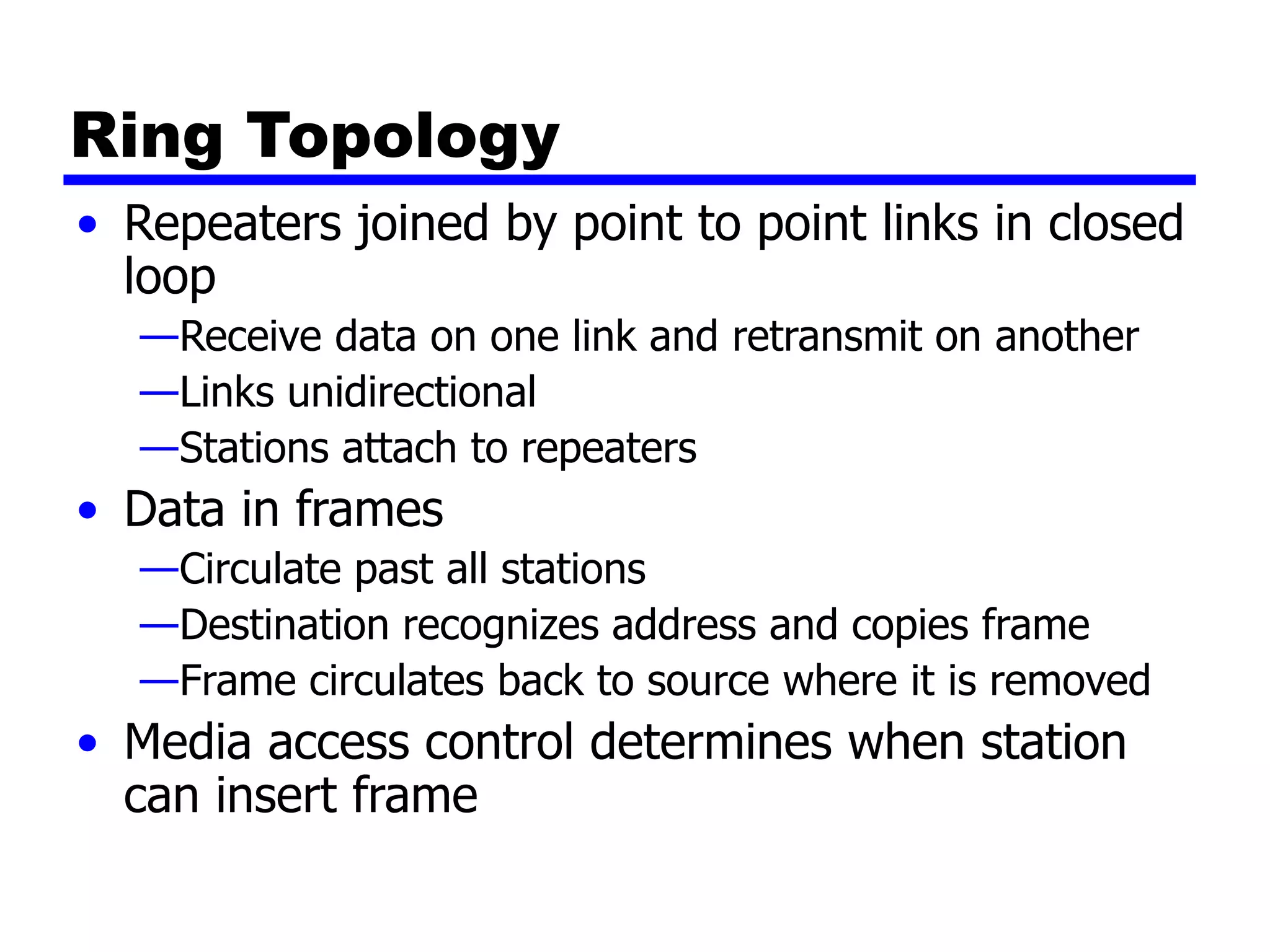
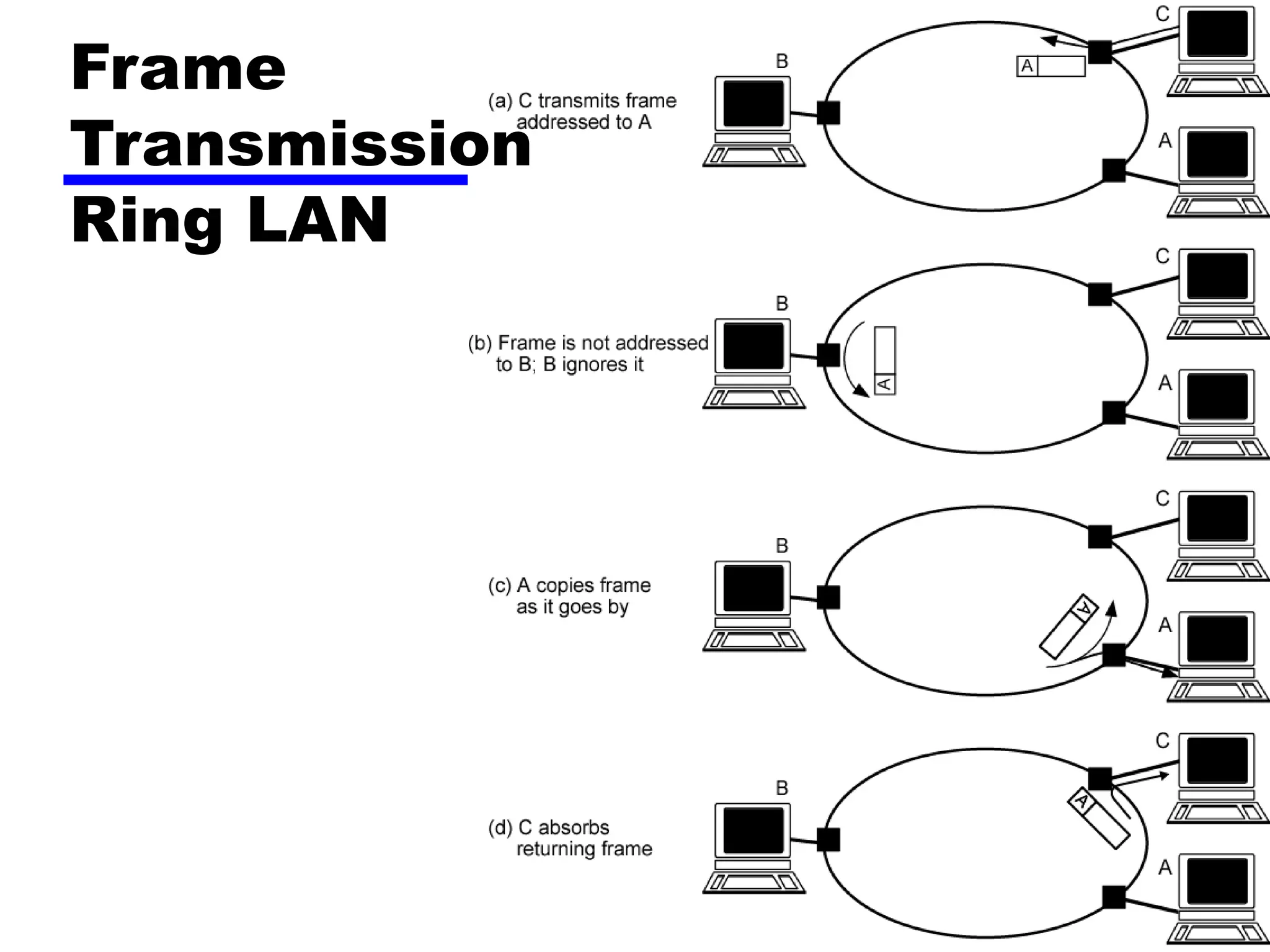
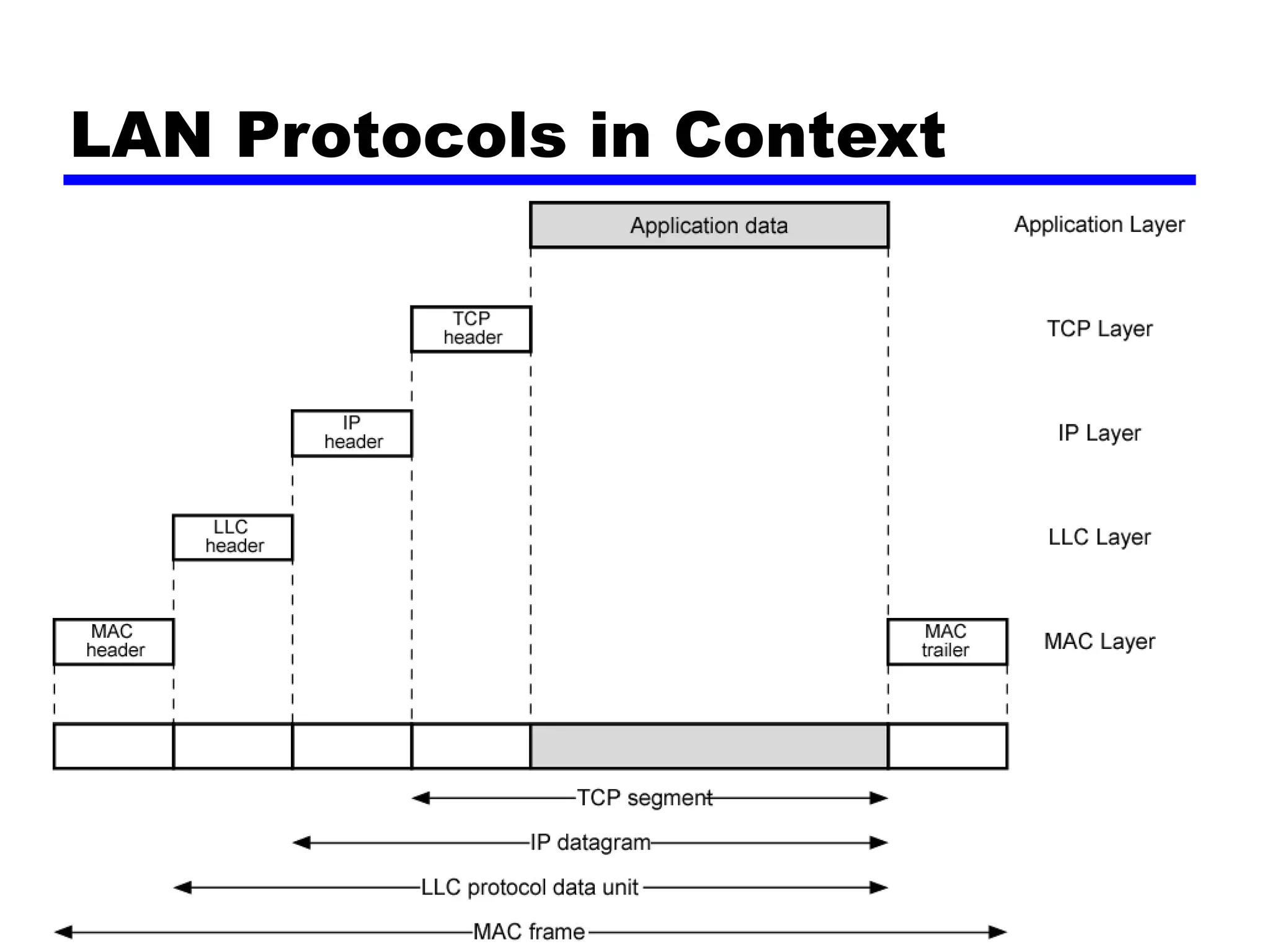
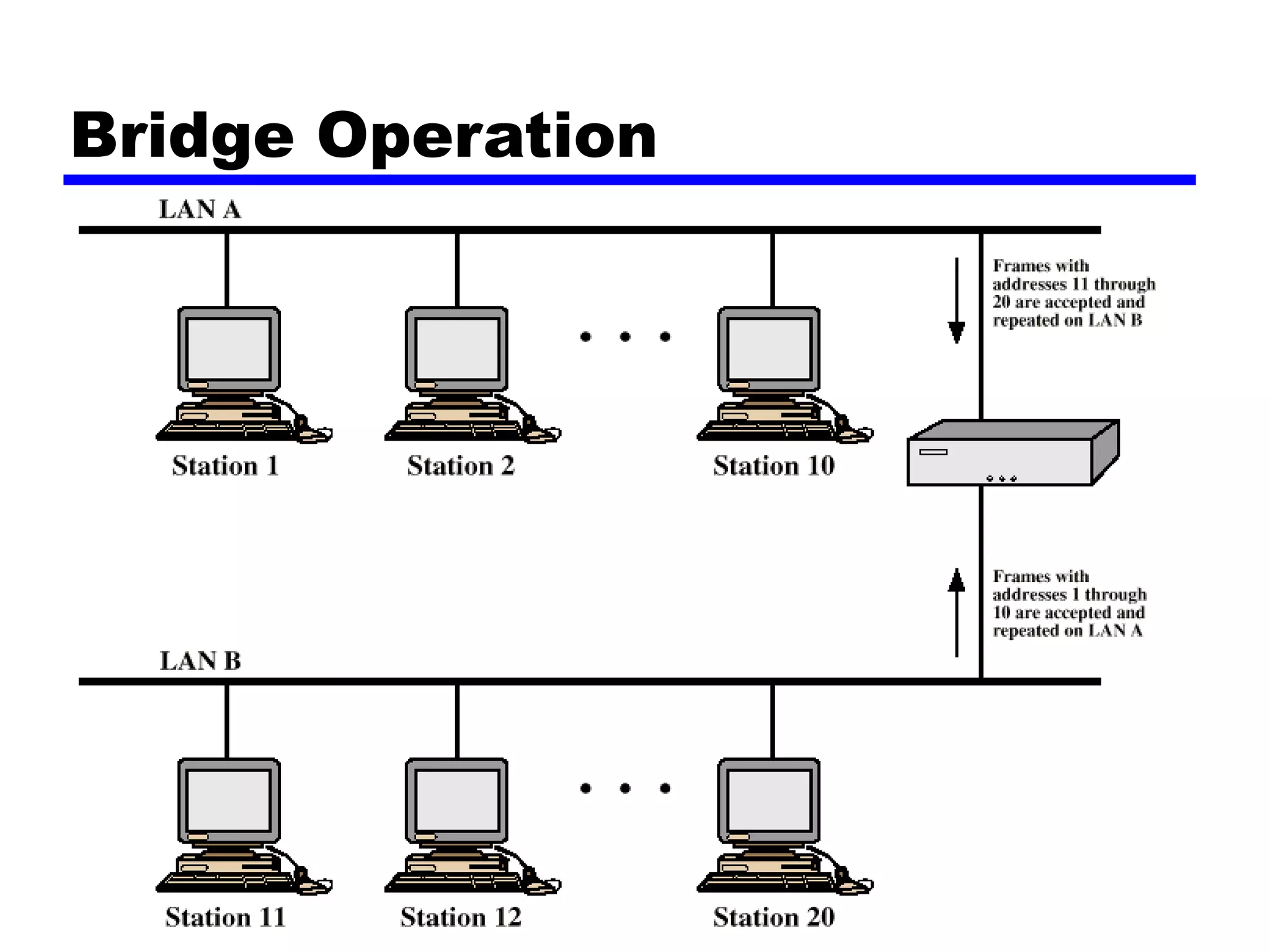
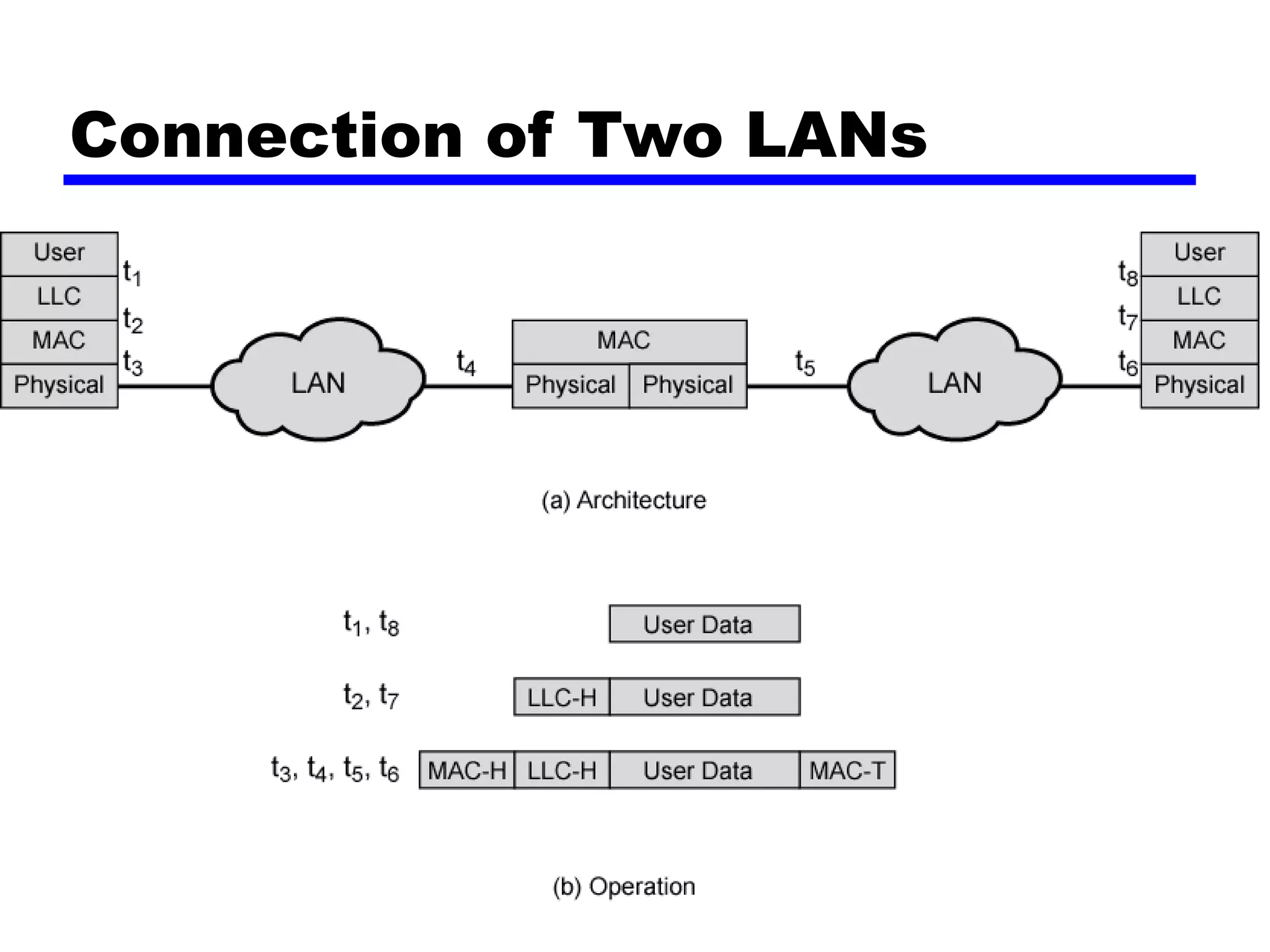
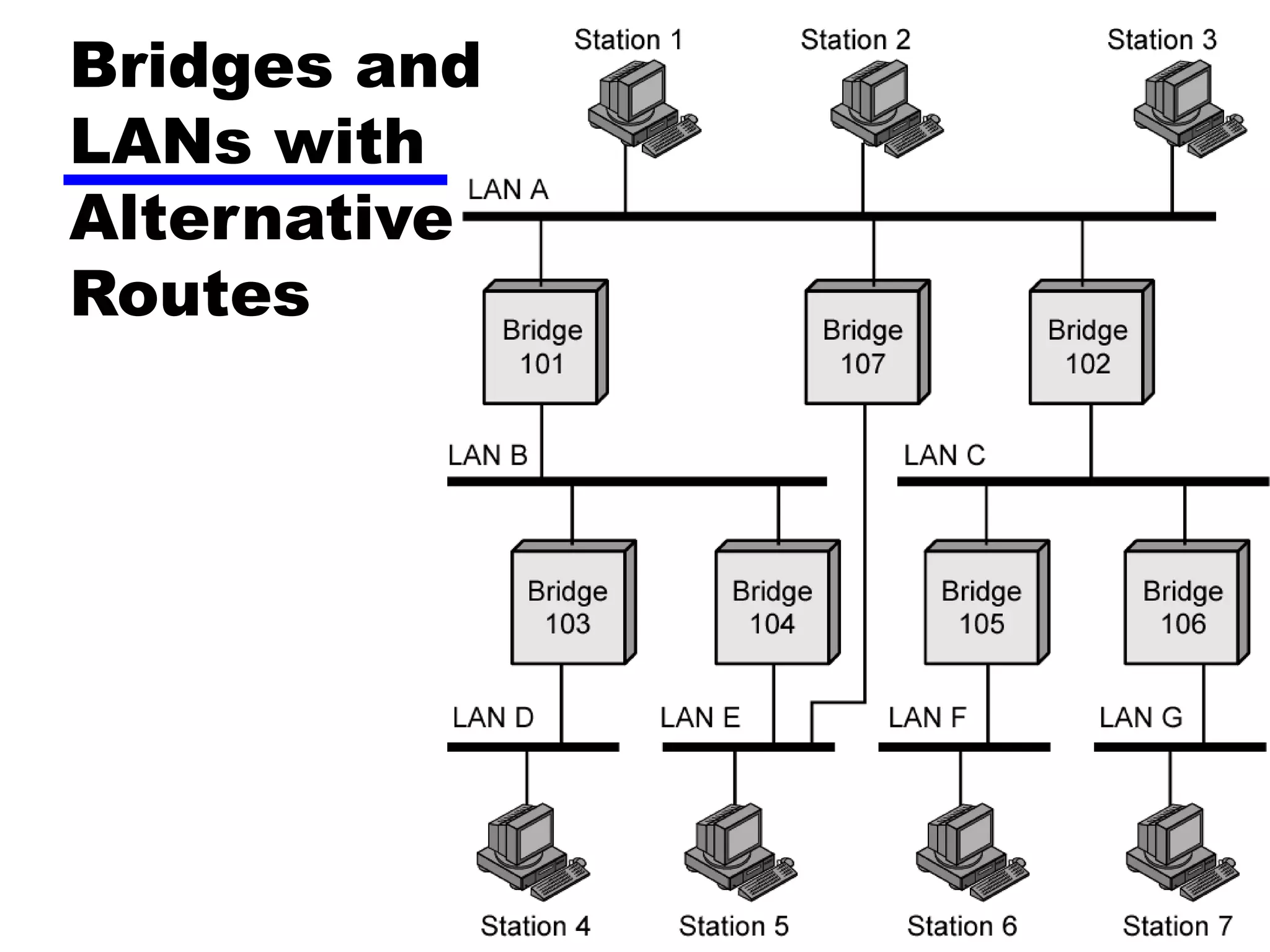
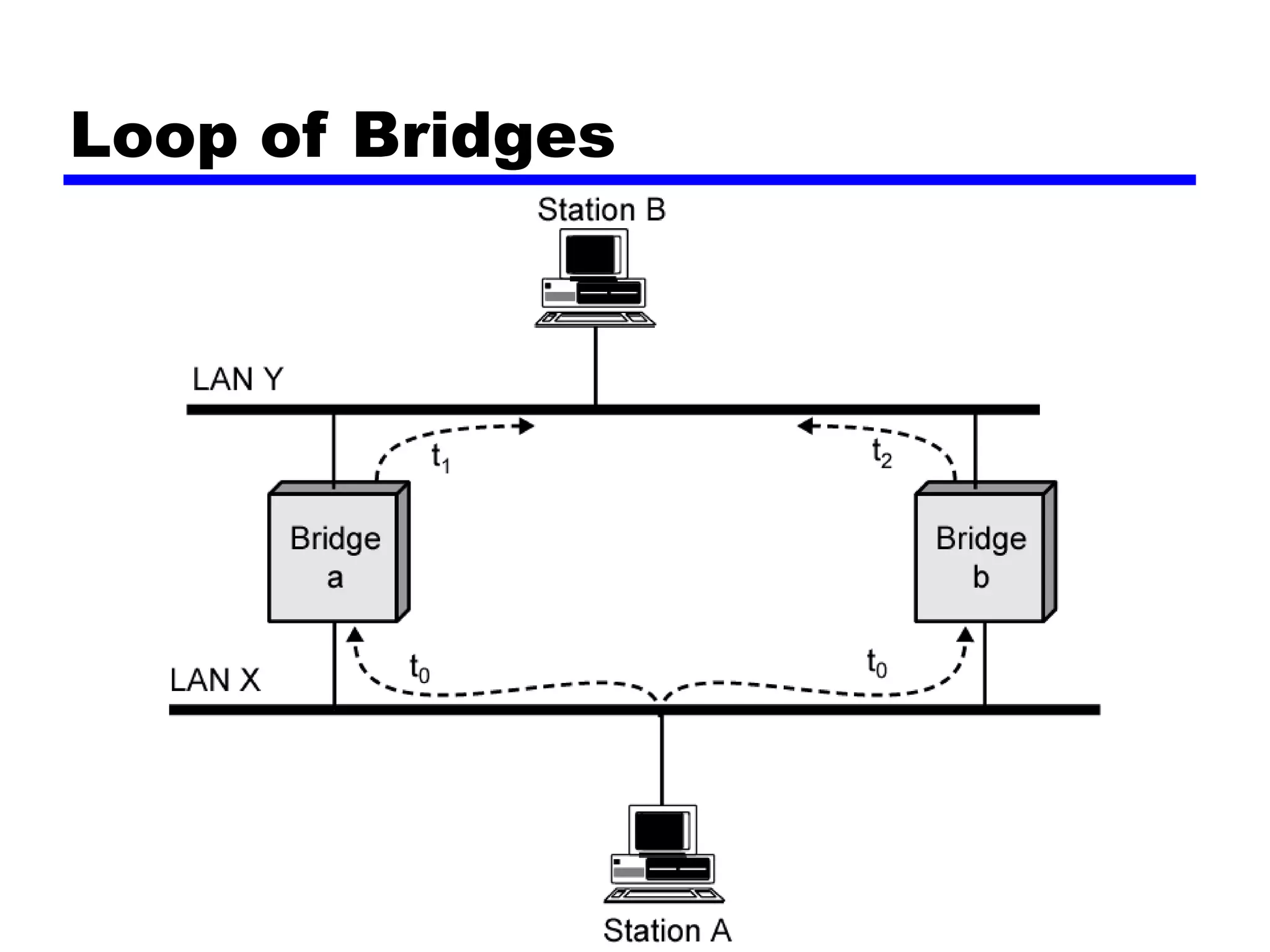
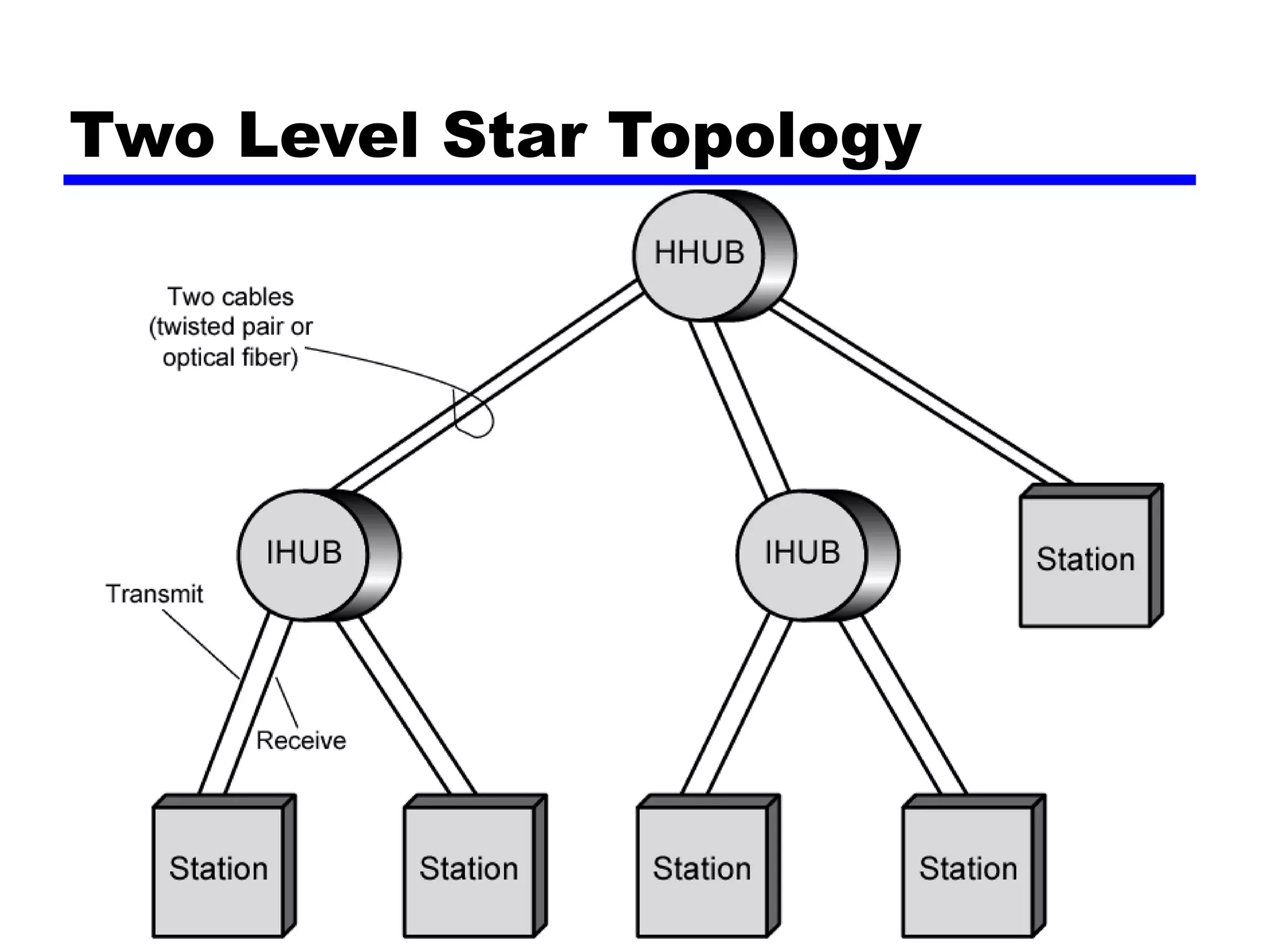
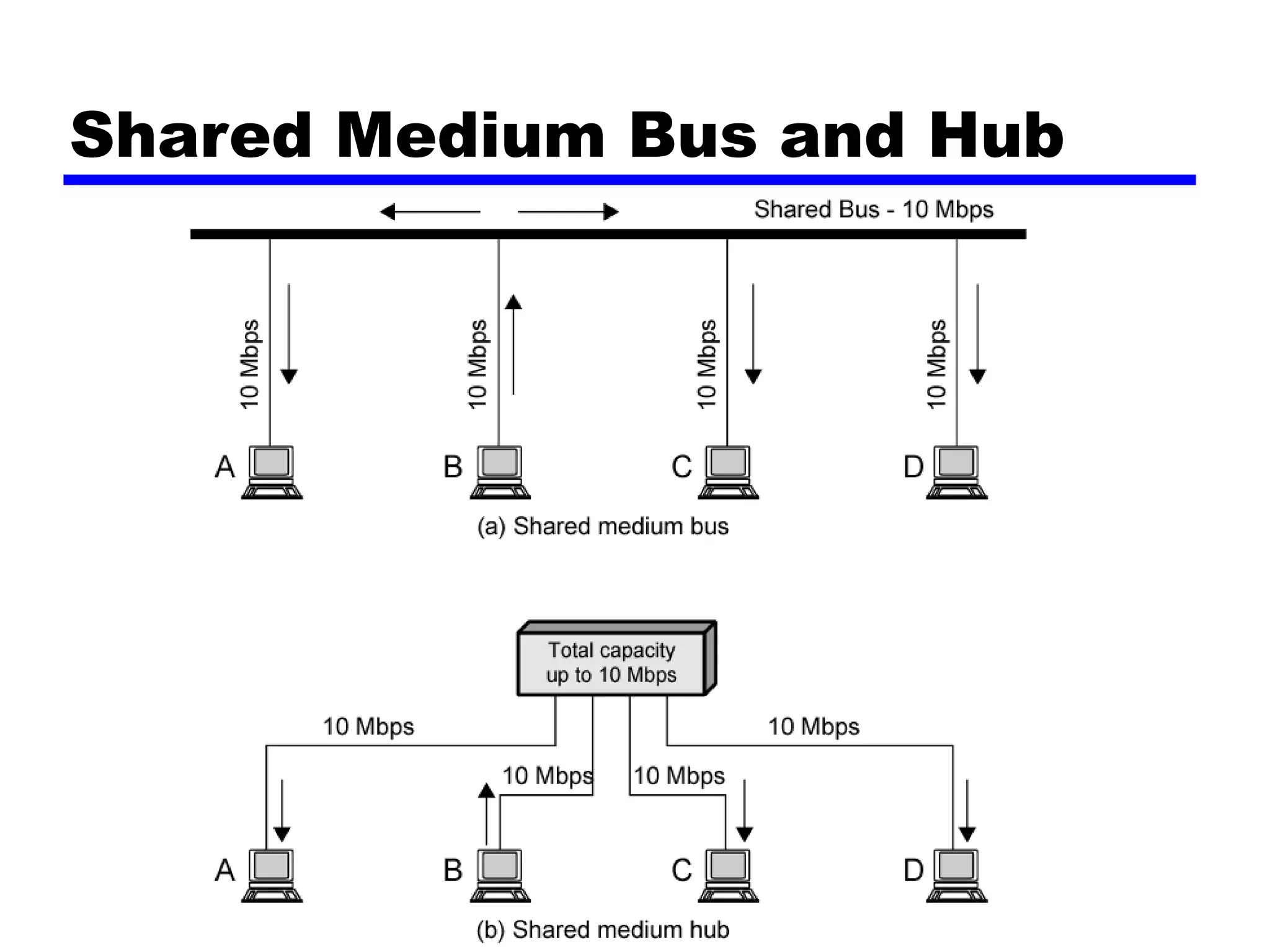
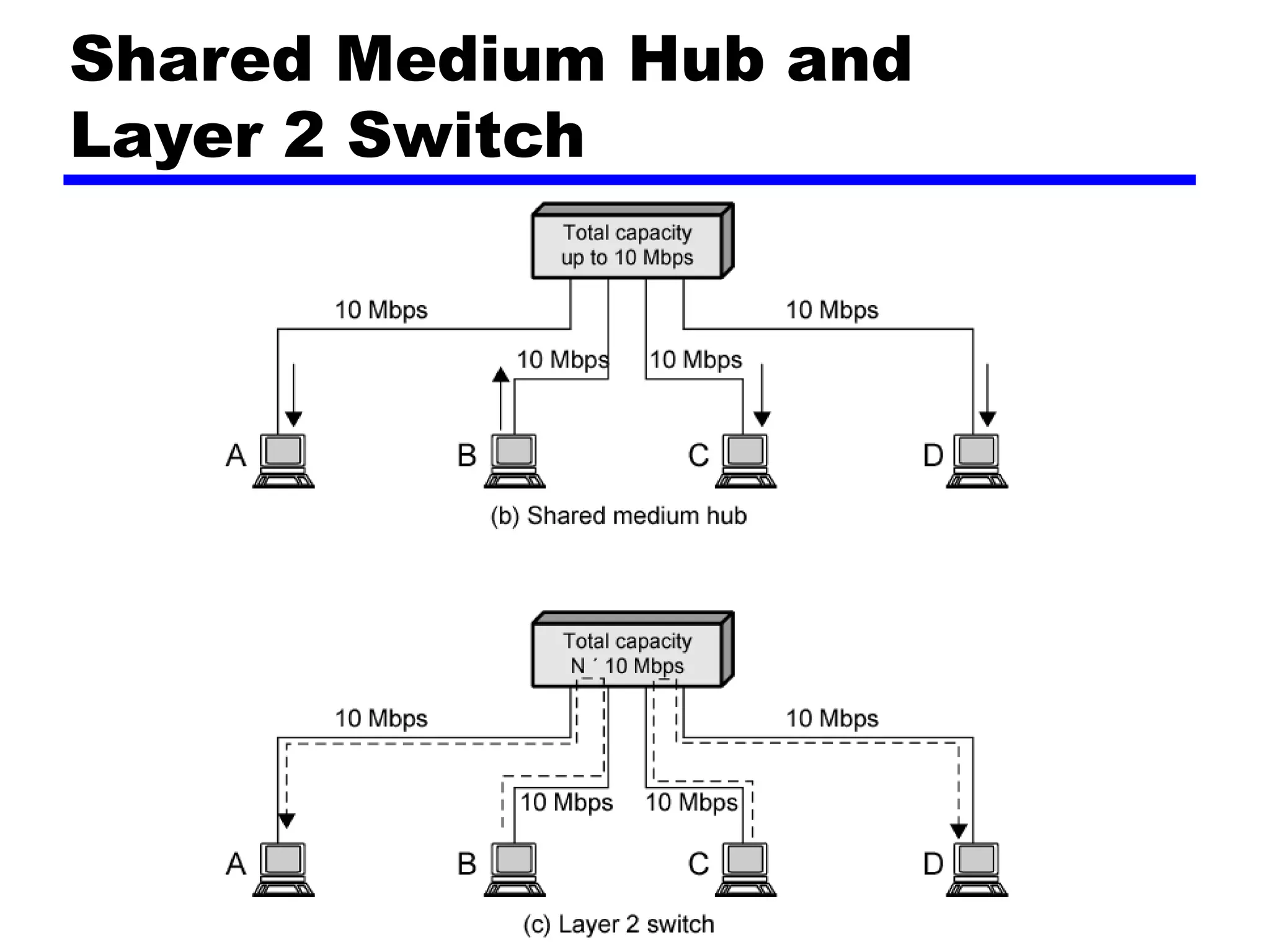
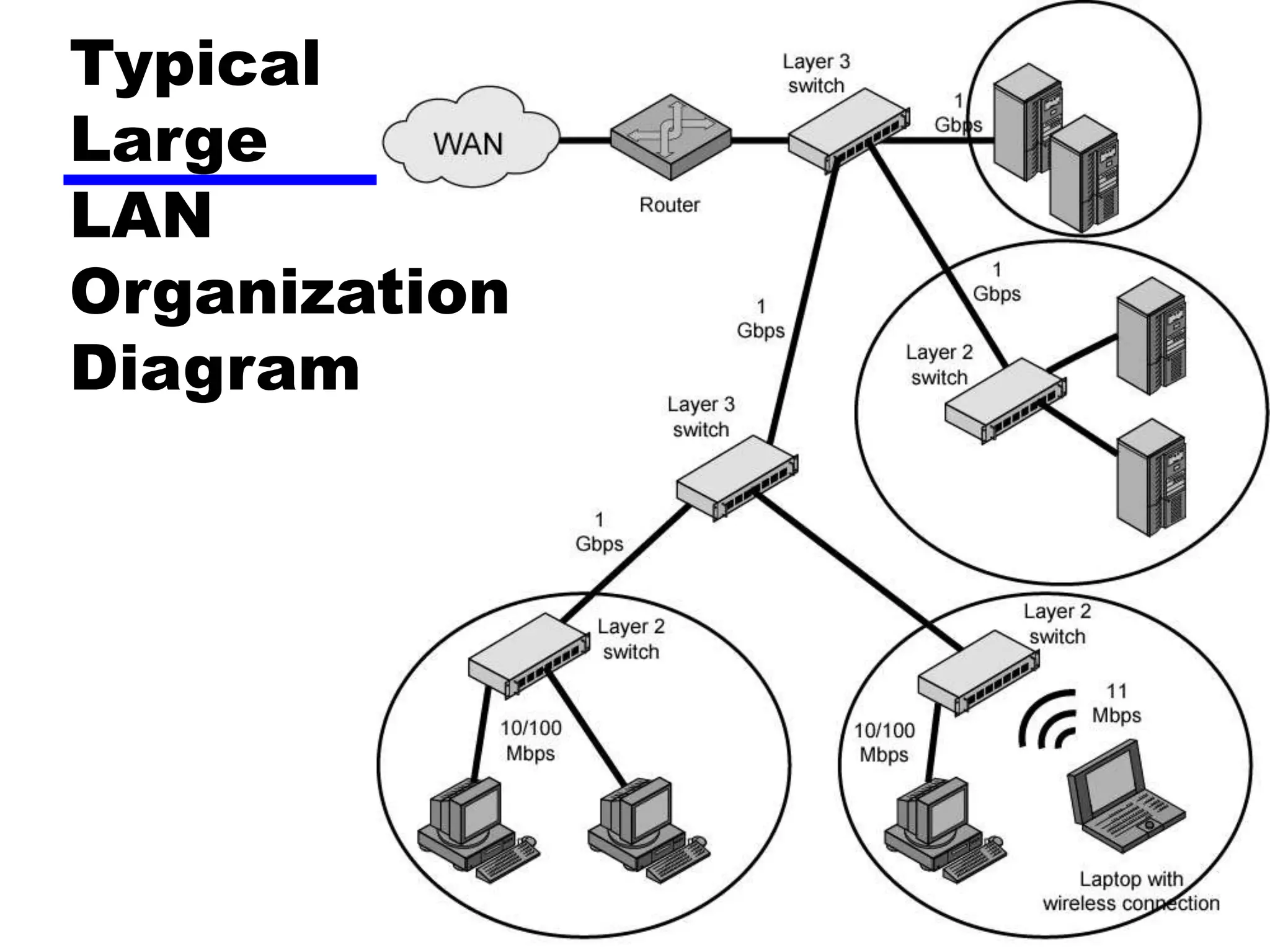
This document summarizes key points from Chapter 15 of William Stallings' book "Data and Computer Communications", 7th Edition. It discusses the applications and architectures of local area networks (LANs). The main applications covered are personal computer LANs, back-end networks, storage area networks, and high-speed office networks. Common LAN topologies like bus, ring, star and their characteristics are explained. Issues around transmission media, protocols, and network devices like bridges, hubs and switches are also summarized at a high level.