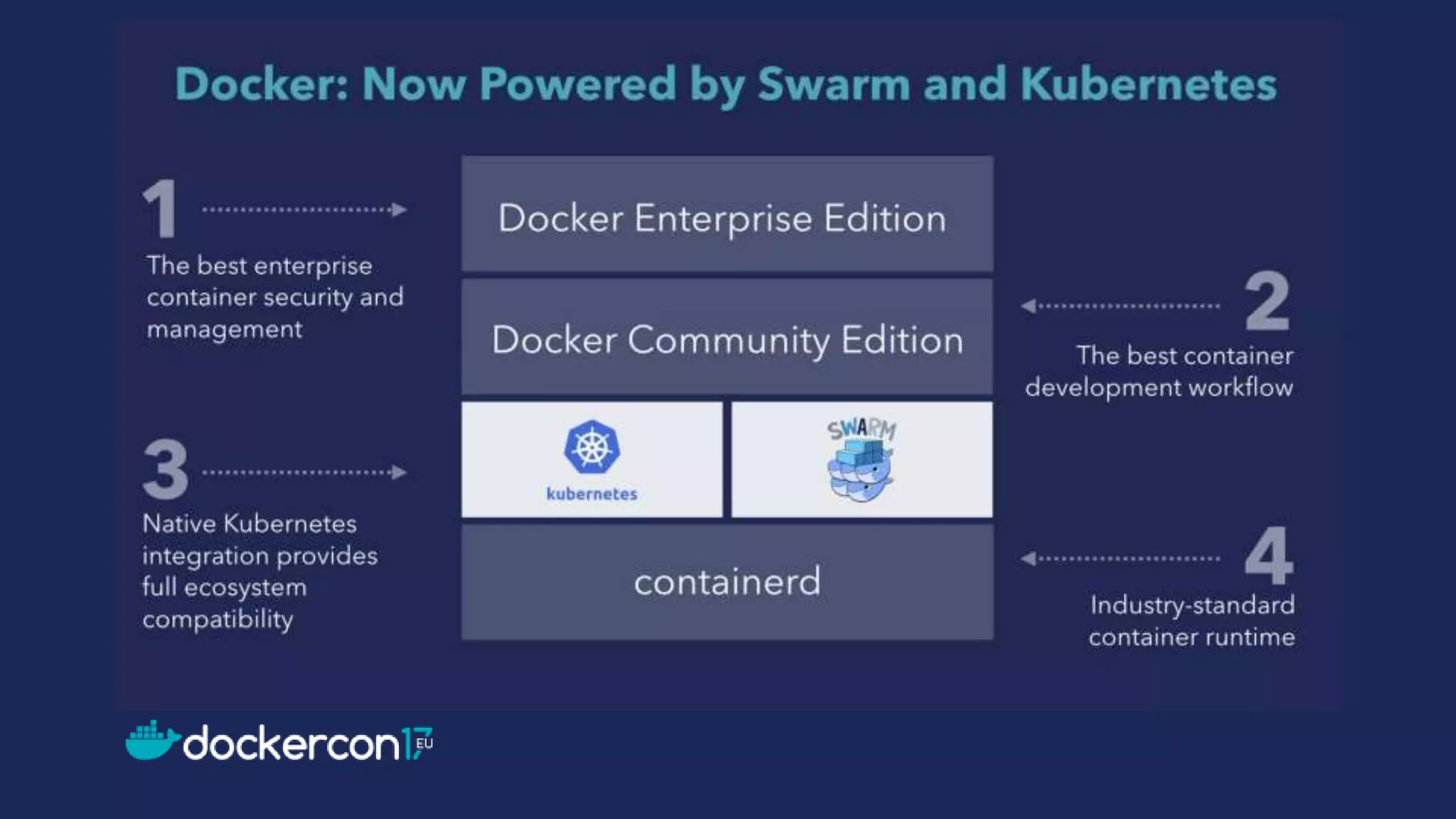
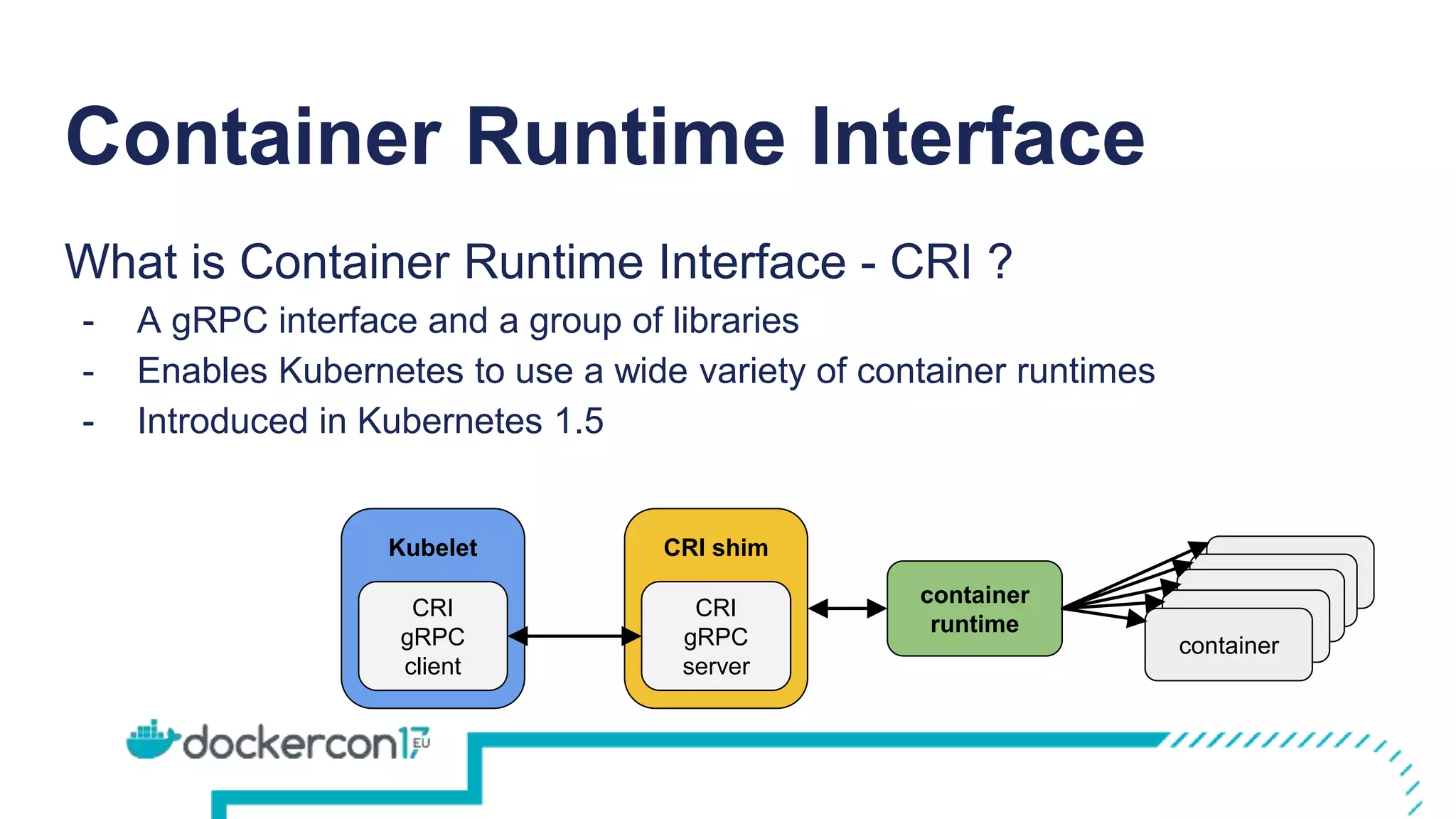
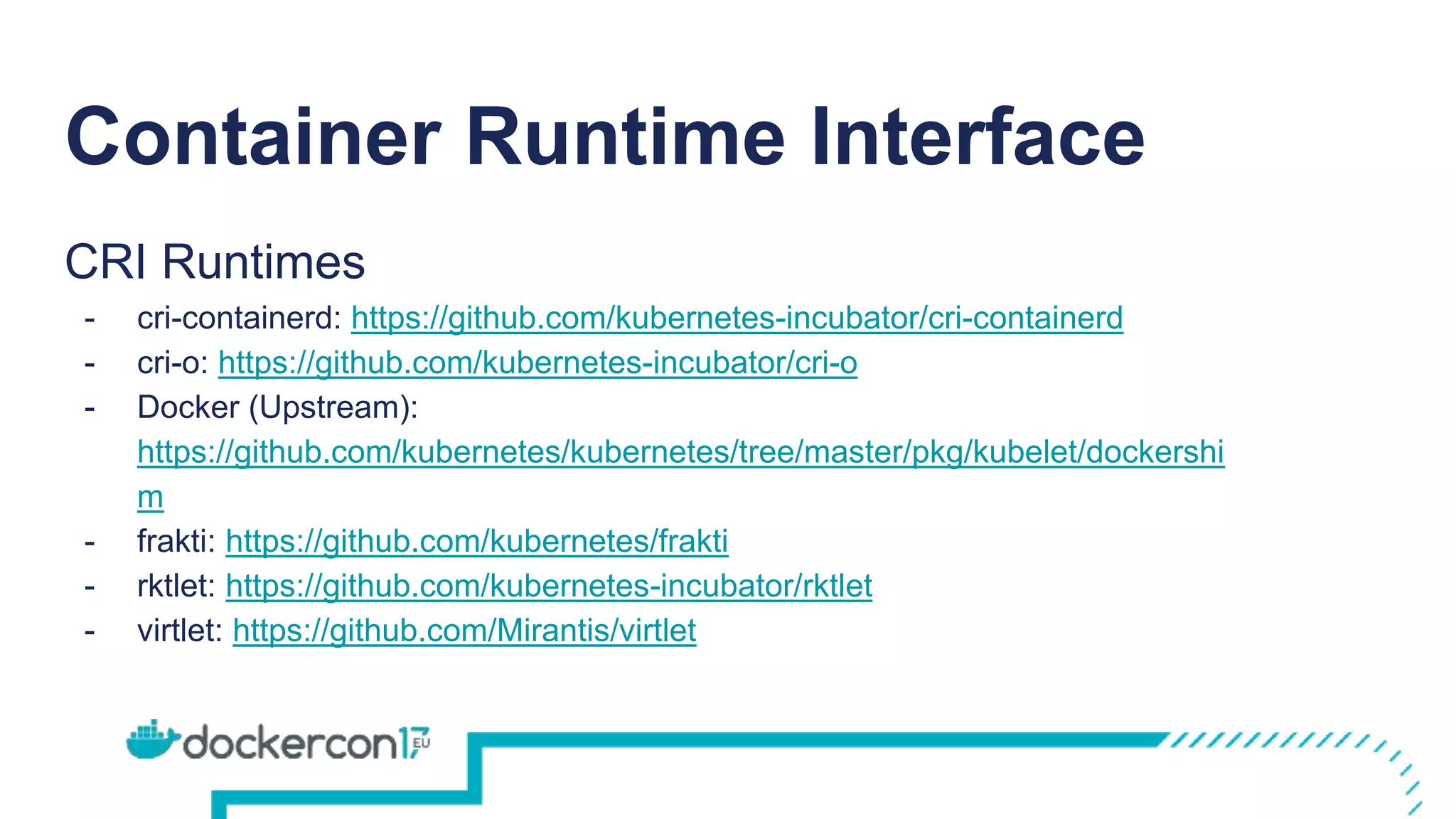
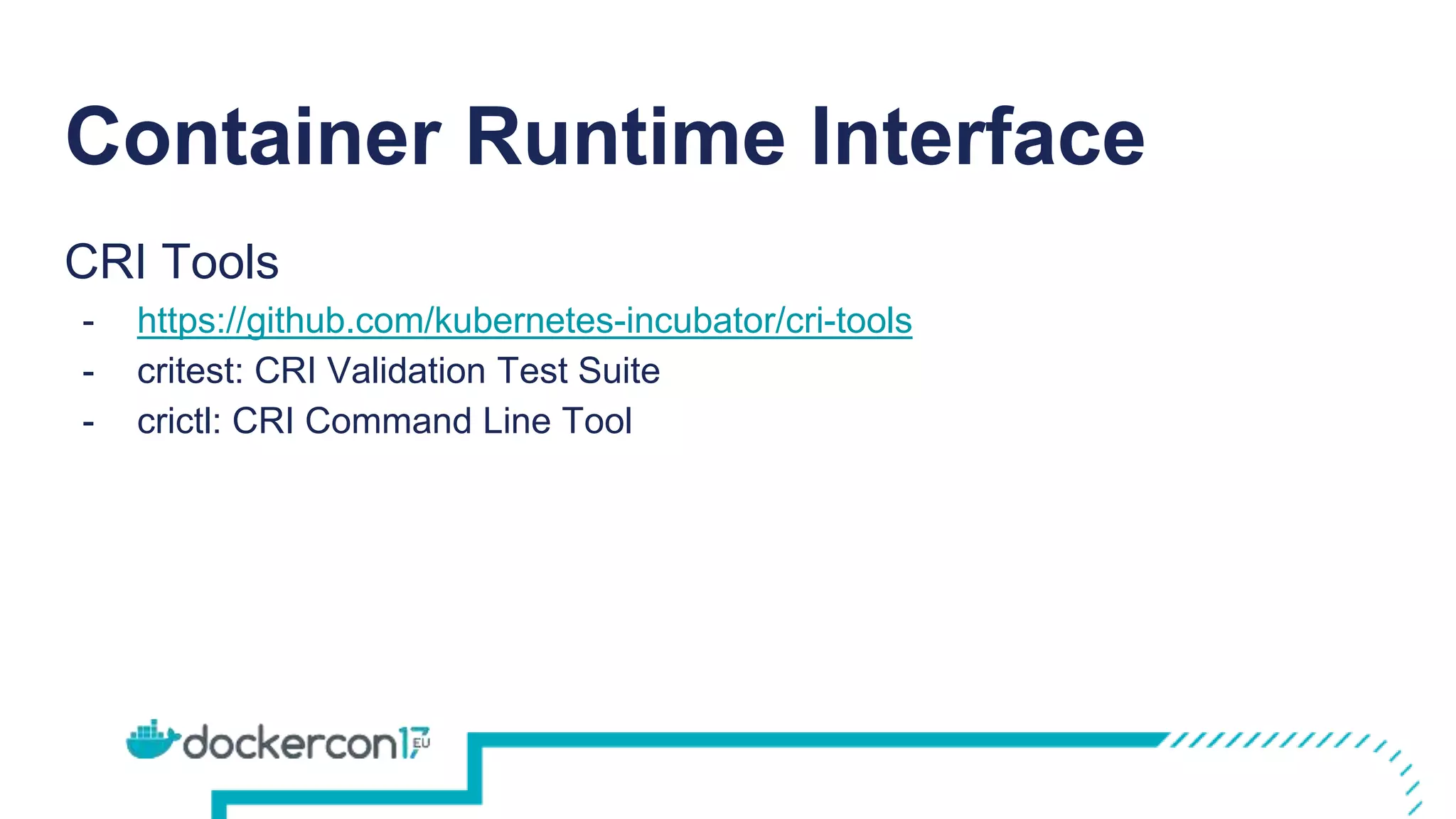
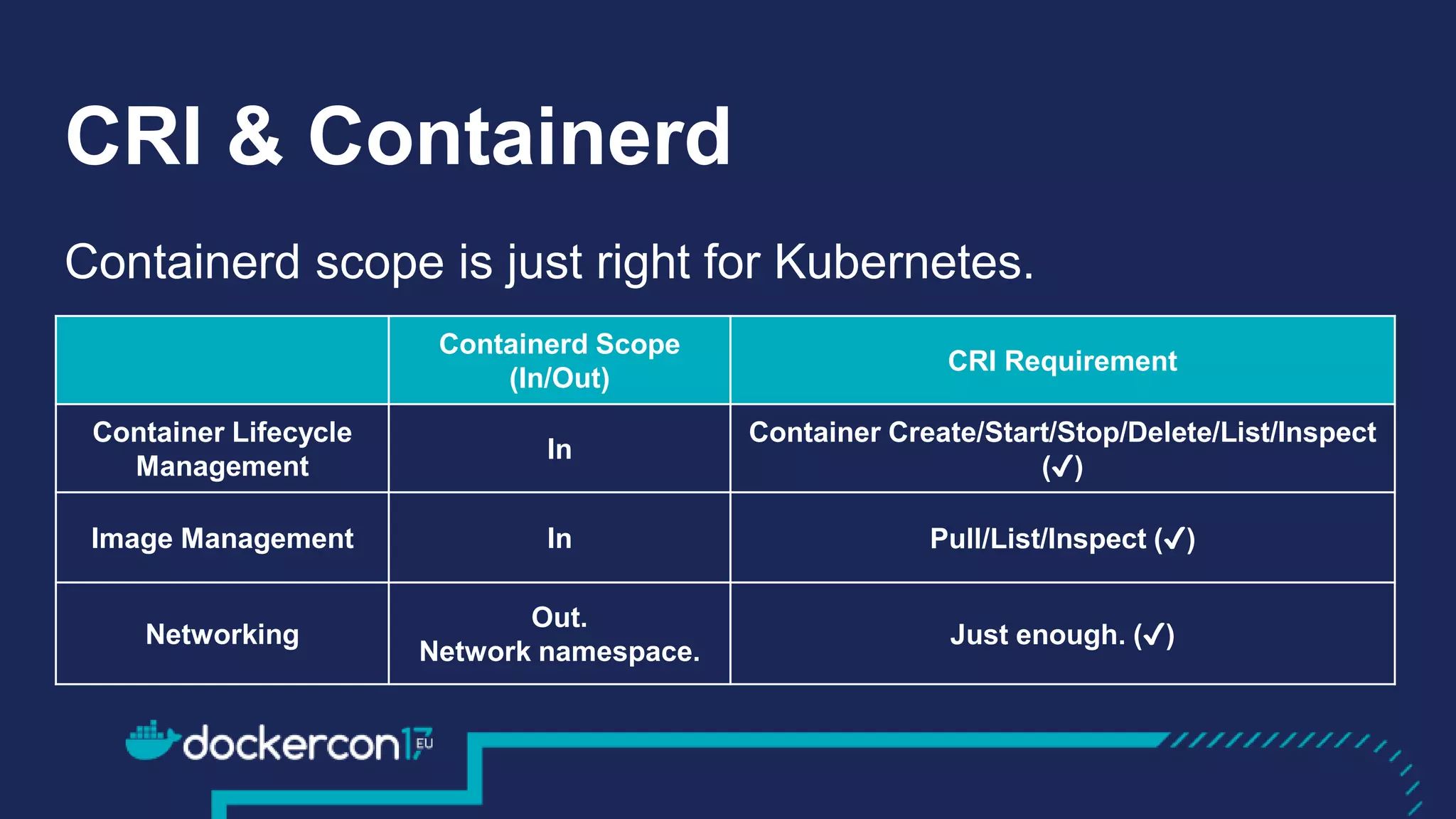
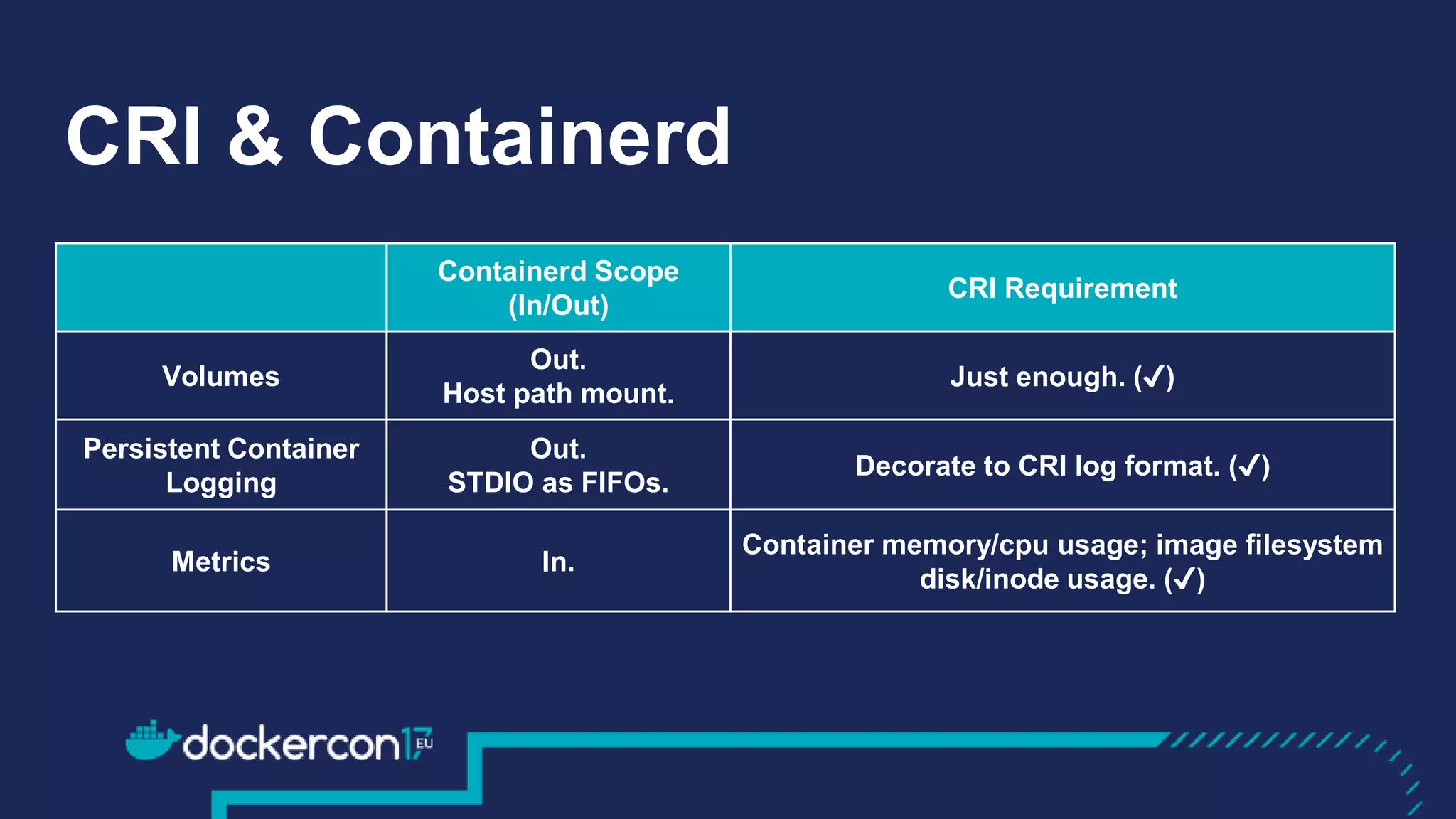
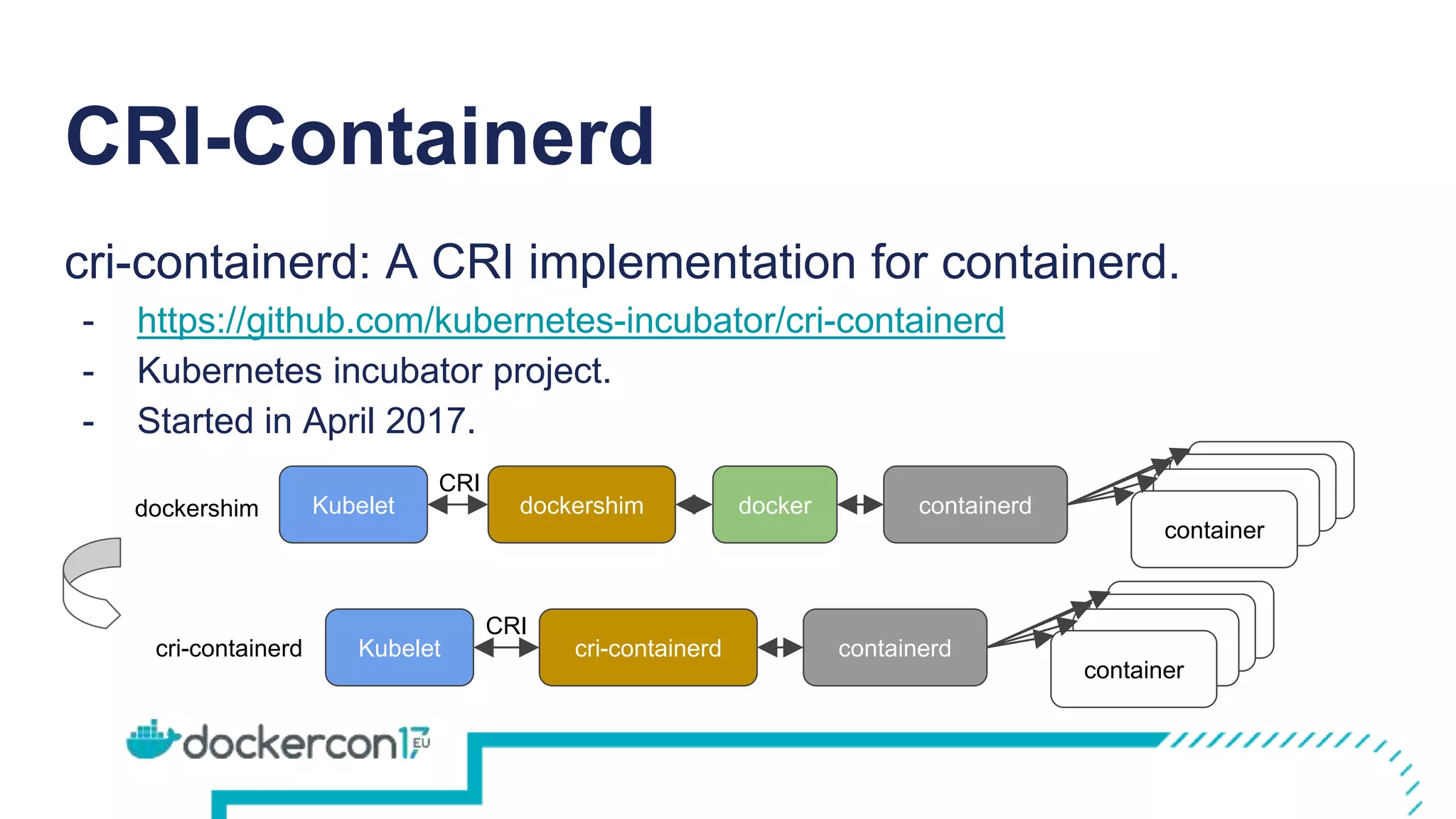
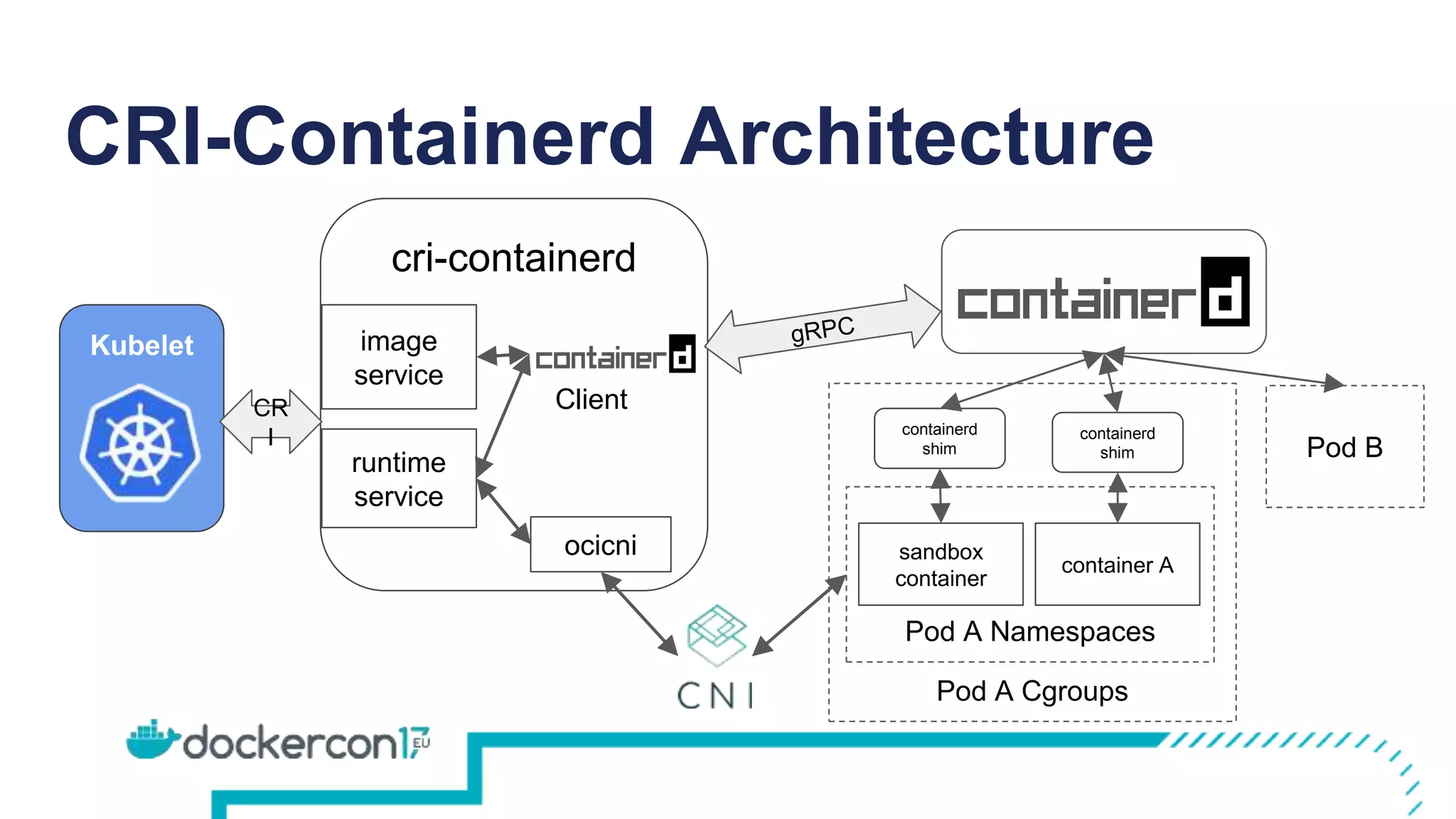
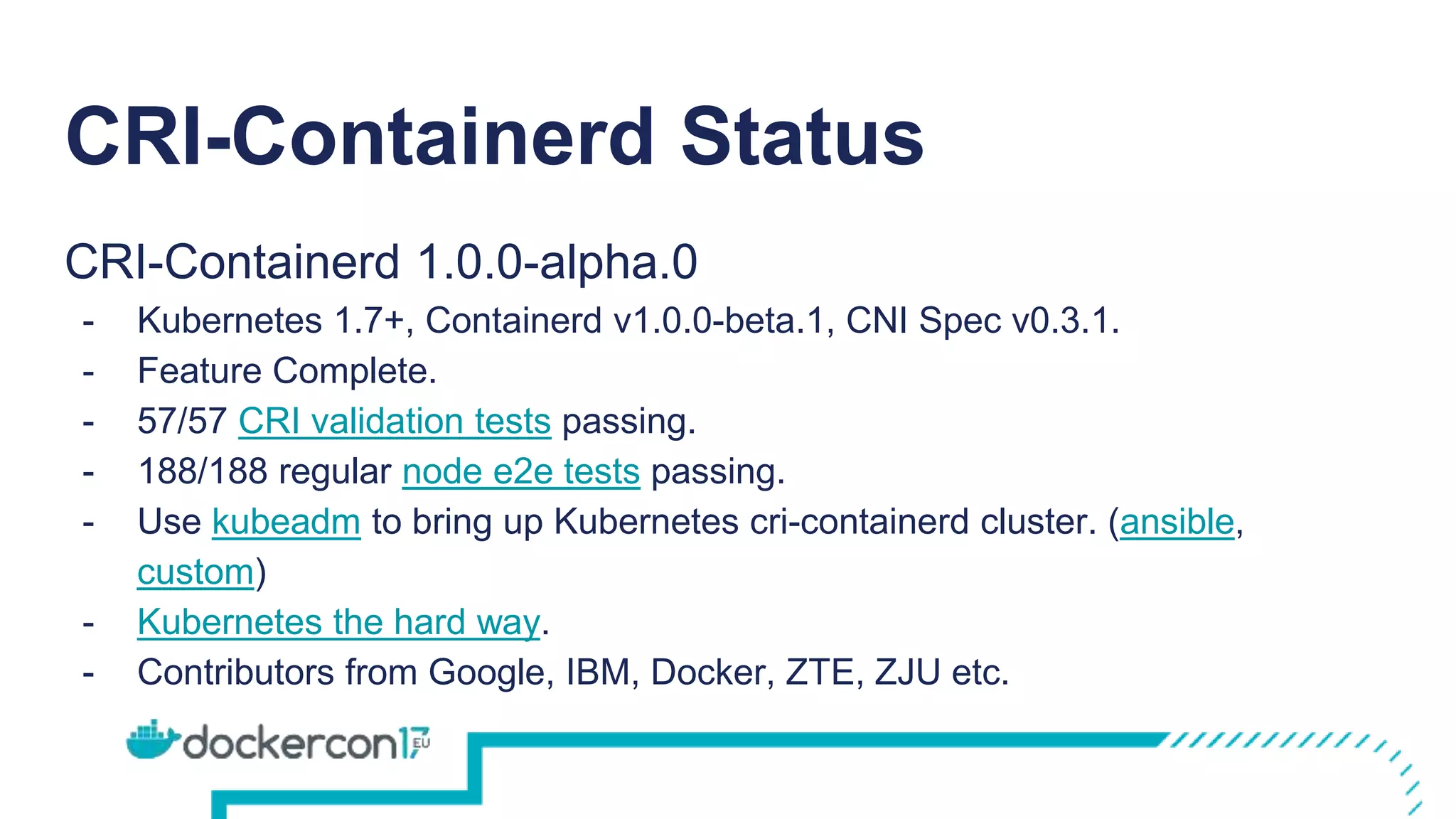
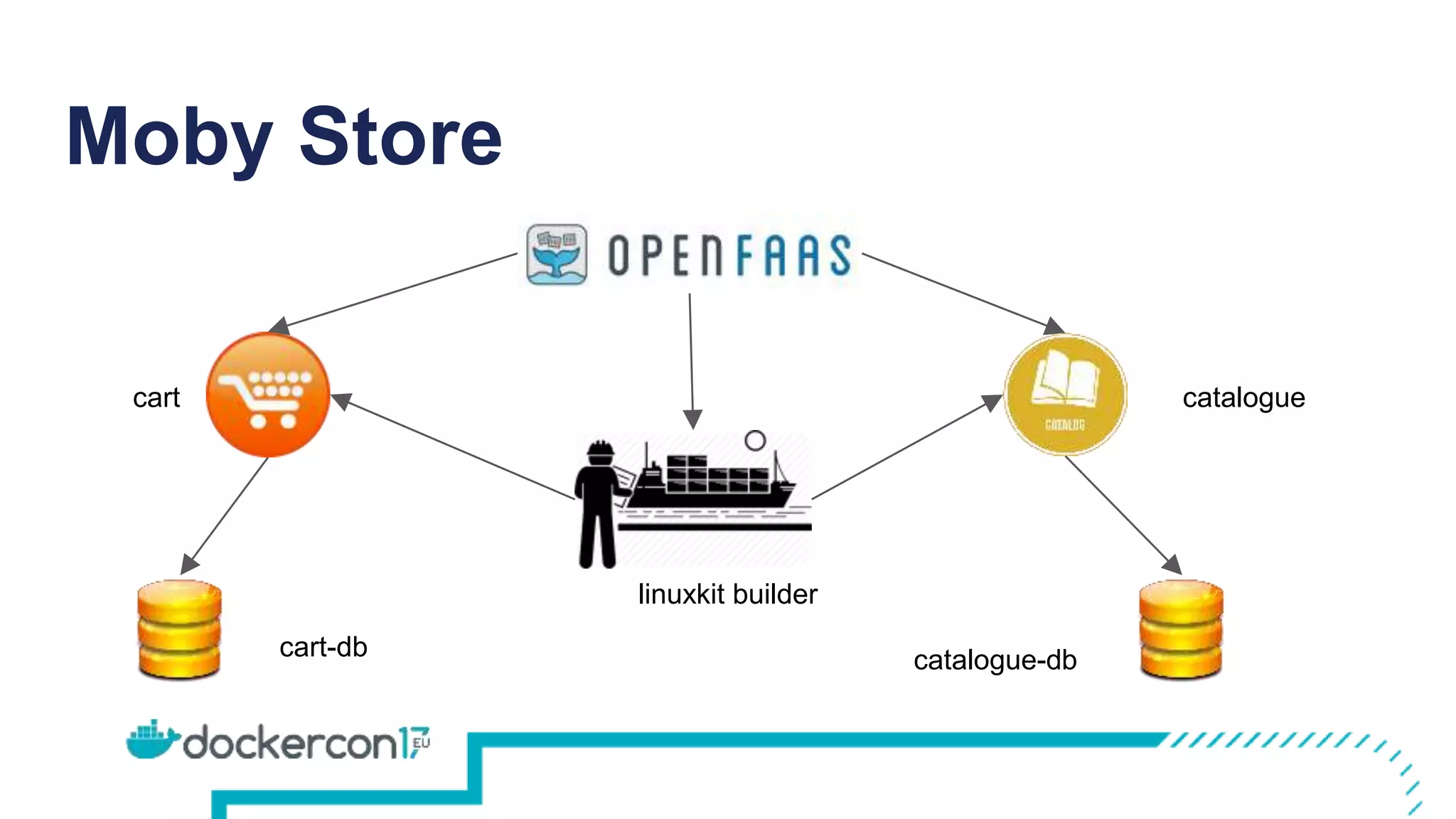
This document discusses CRI-Containerd, which is a CRI implementation that allows Kubernetes to use Containerd as its container runtime. It provides an overview of CRI and how it enables Kubernetes to work with different runtimes. It then discusses how Containerd's scope aligns well with CRI's requirements. It introduces CRI-Containerd and its architecture, and notes that it is now feature complete and passing all CRI and Kubernetes tests. Upcoming work includes additional testing, integration with kube-up.sh, and a 1.0.0-beta.0 release by the end of 2017. It concludes with a demo of CRI-Containerd in action.