To create an SAP user and assign roles, one must:
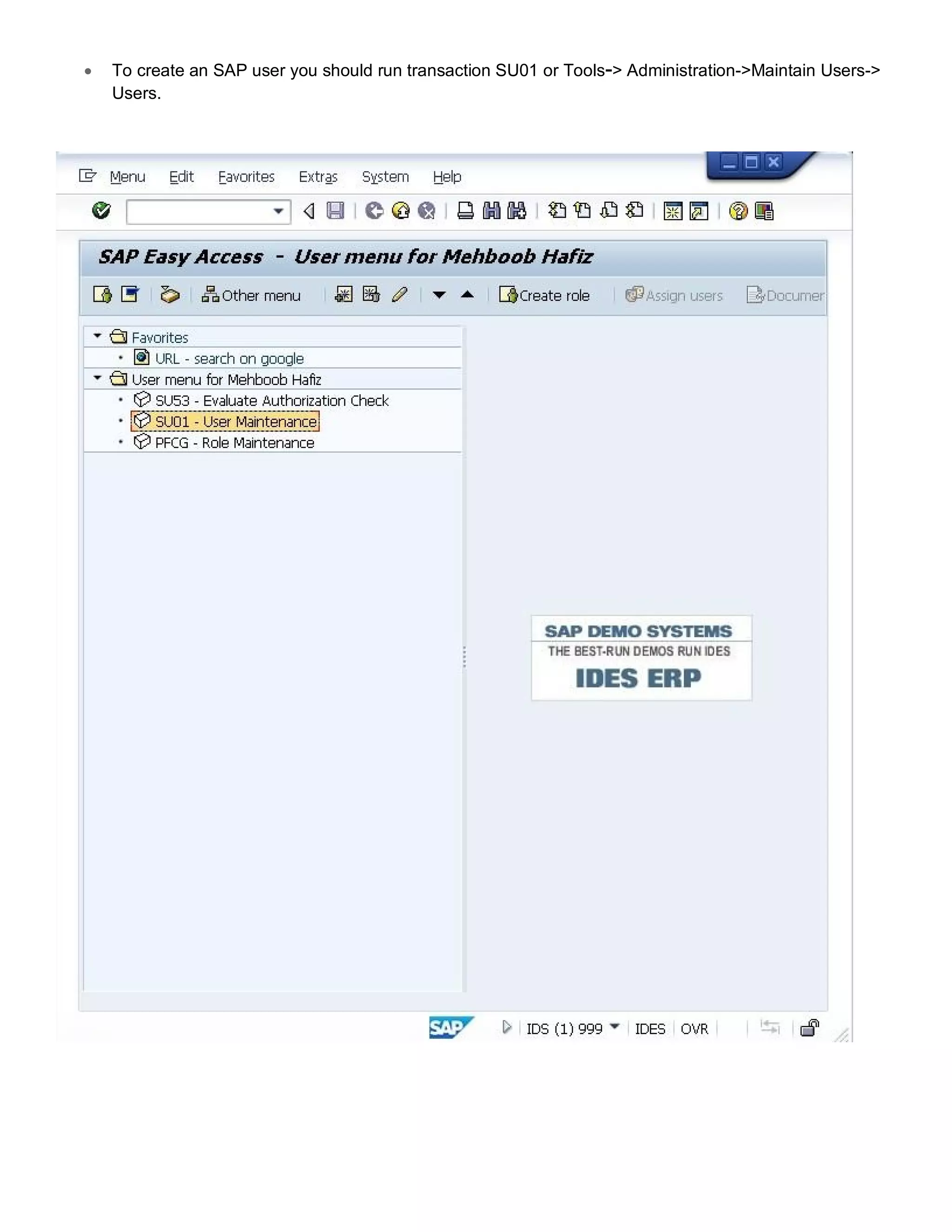
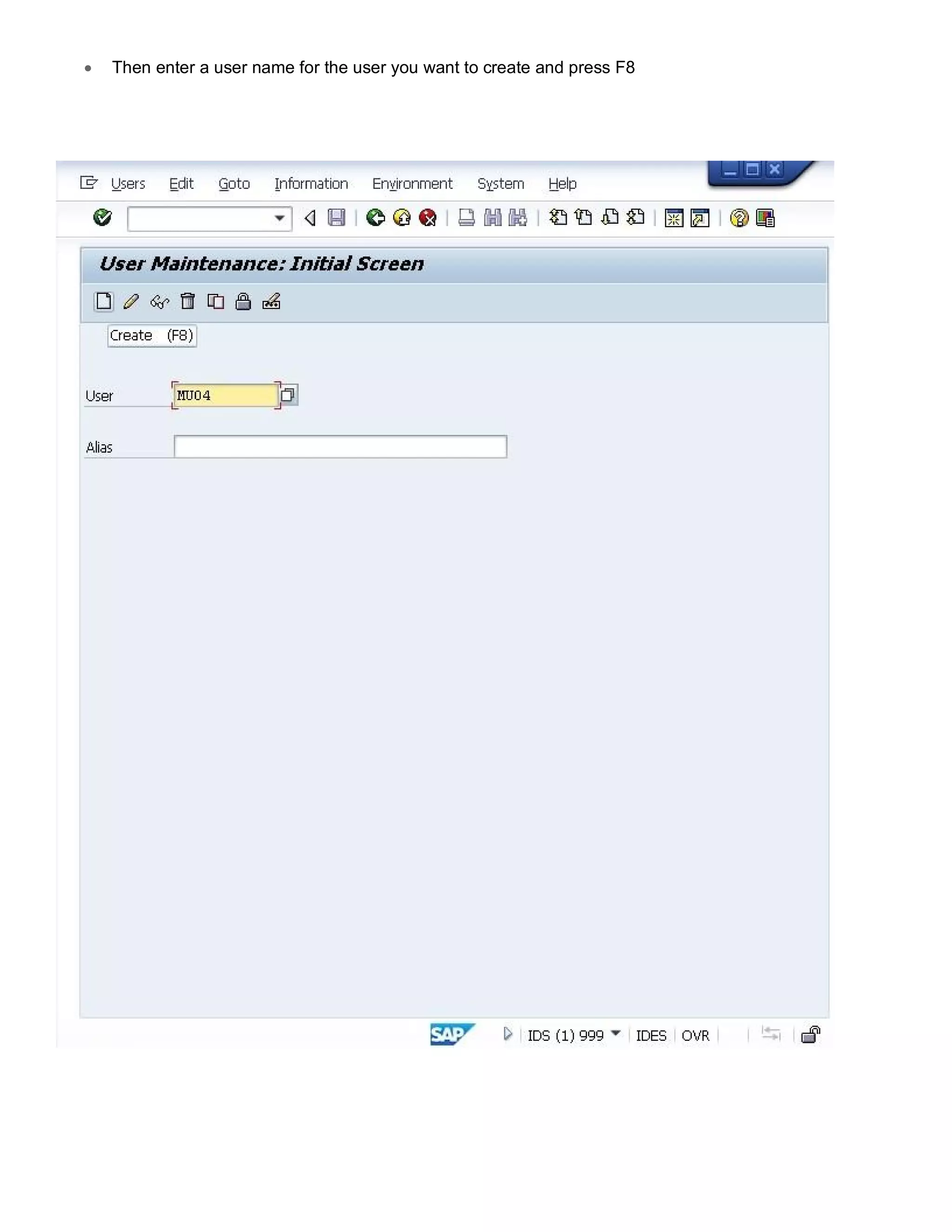
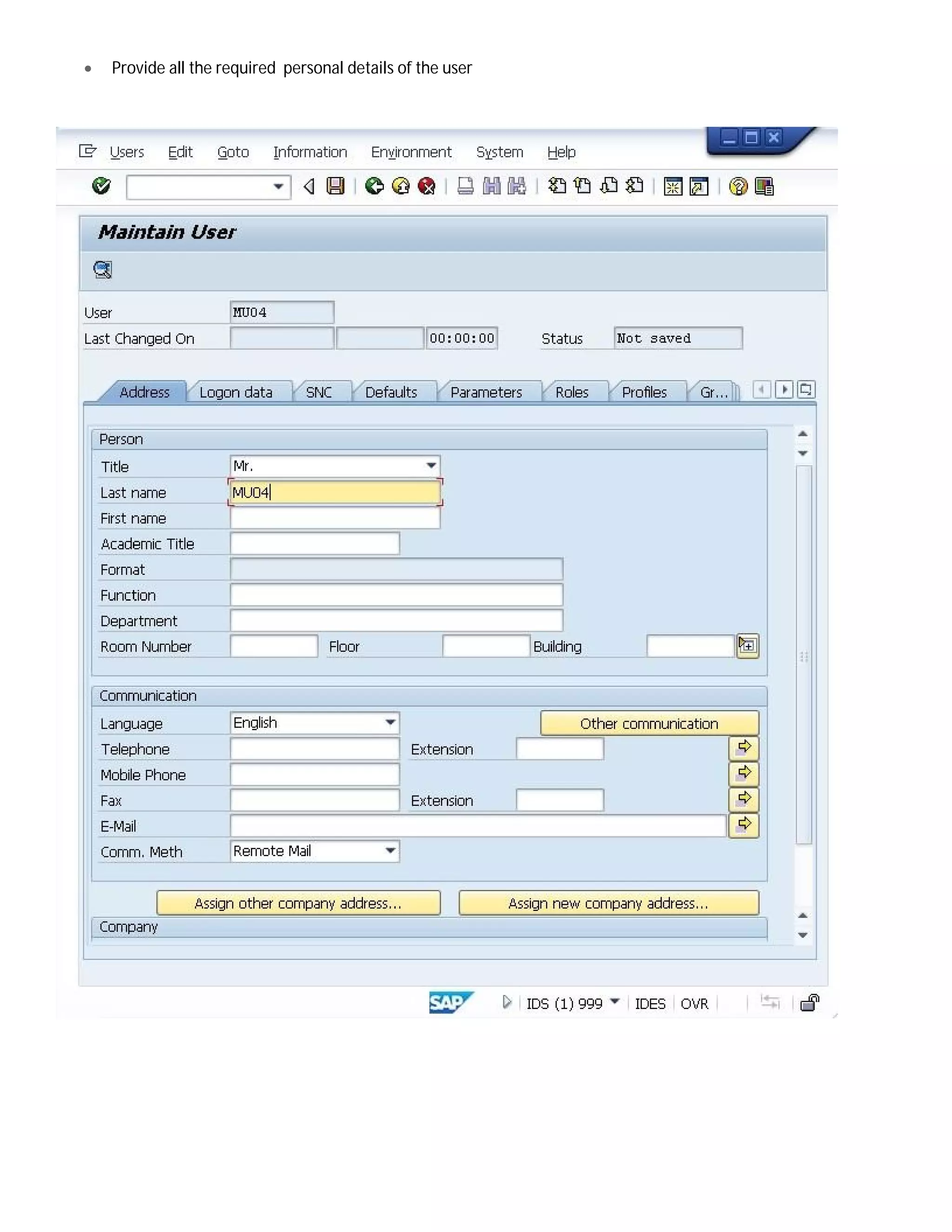
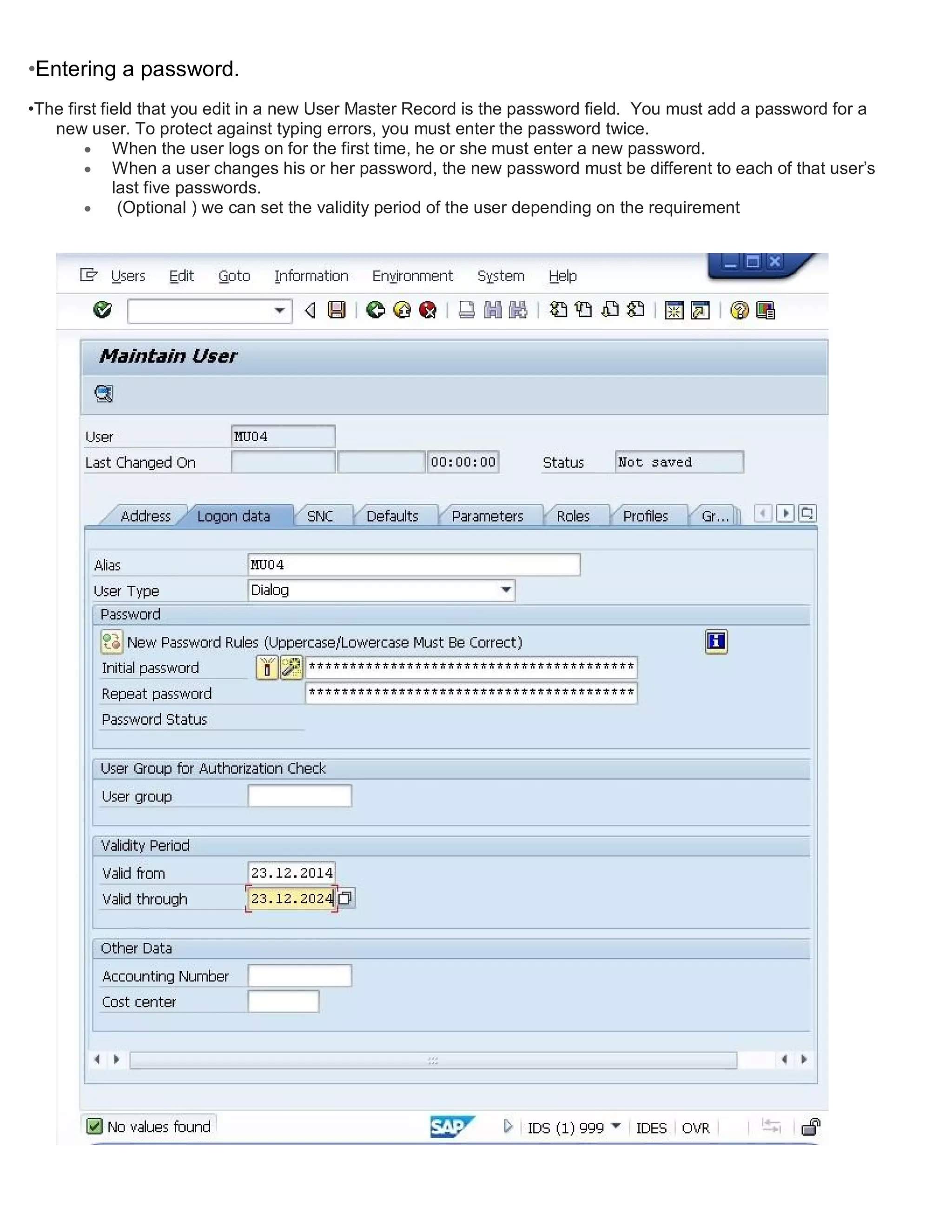
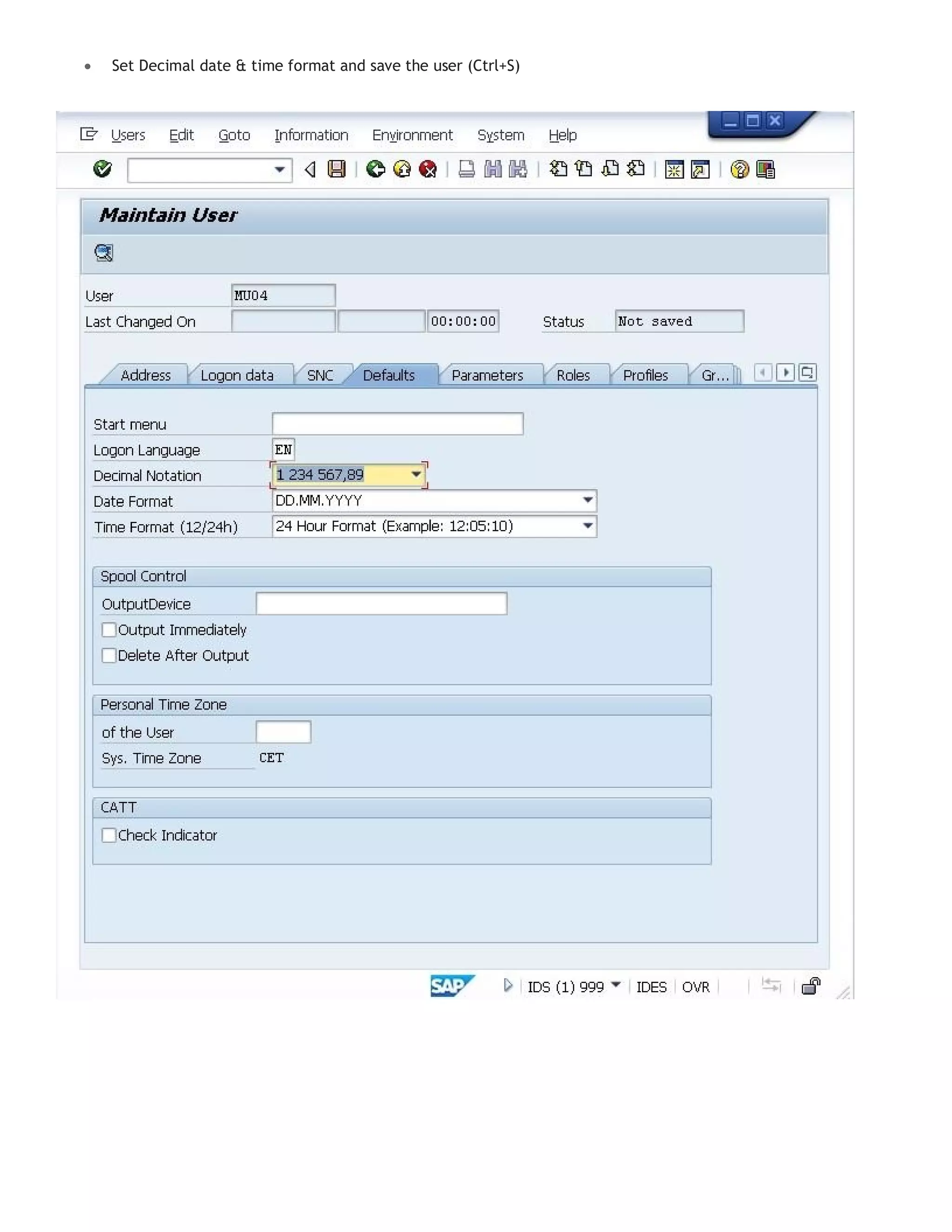
1. Run transaction SU01 and enter a user name, providing personal details and setting a password.
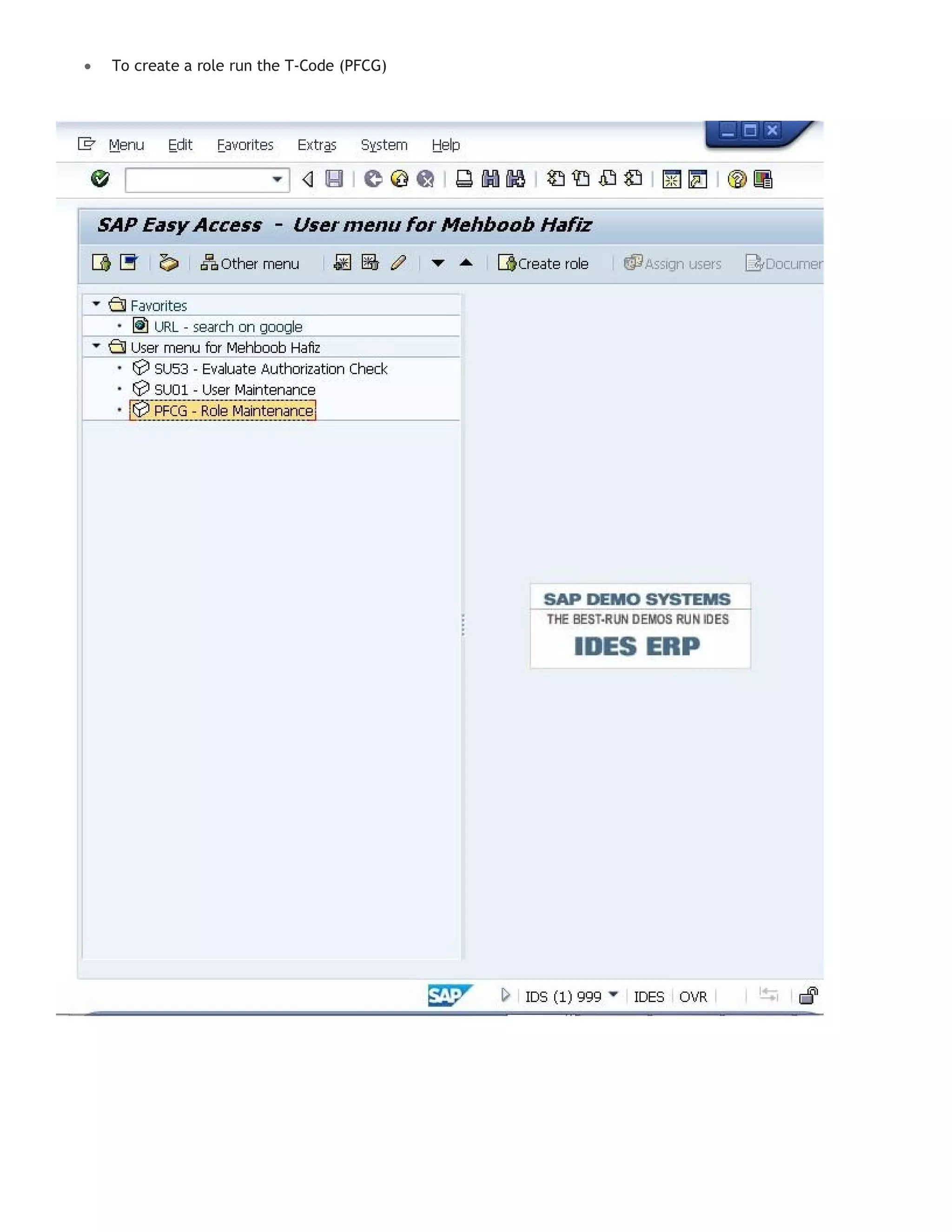
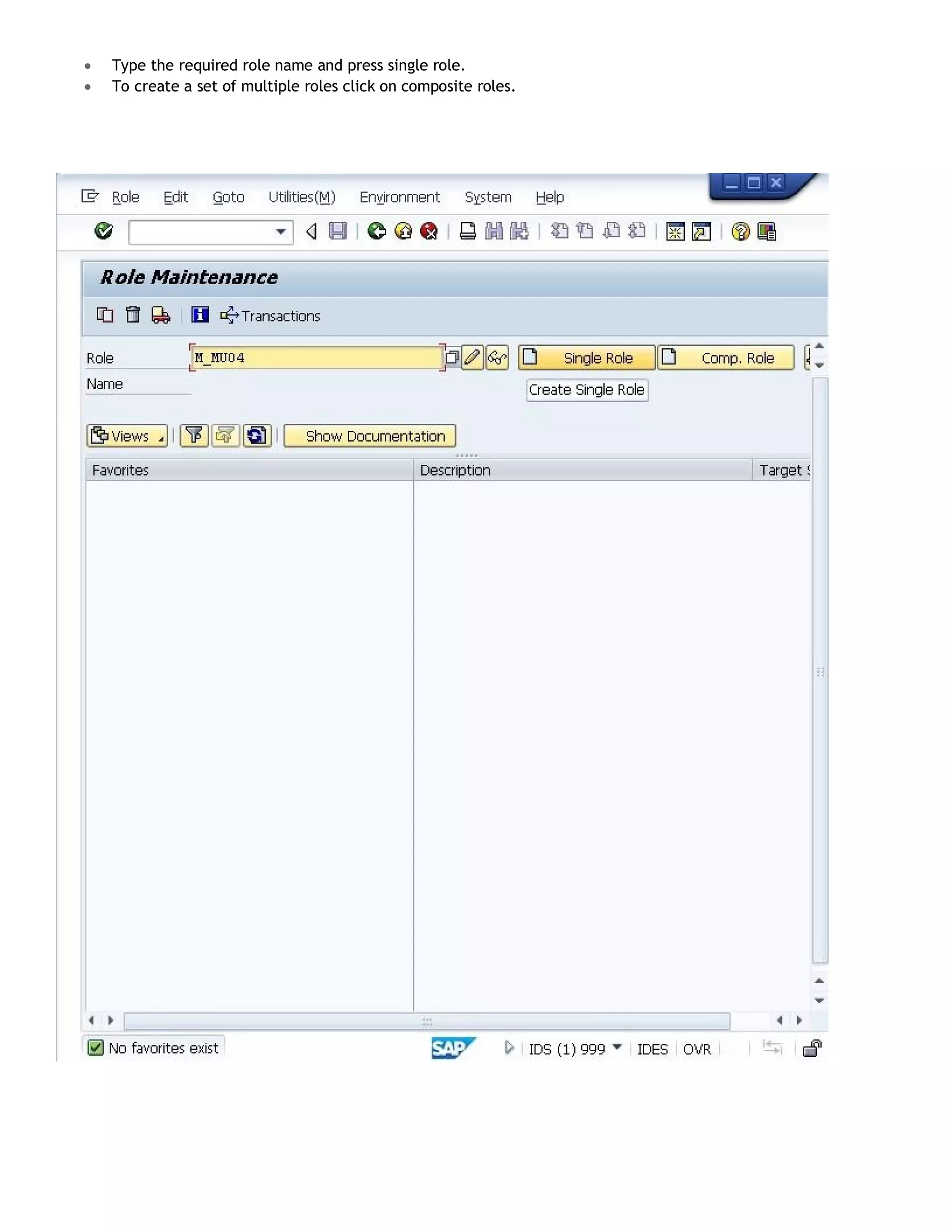
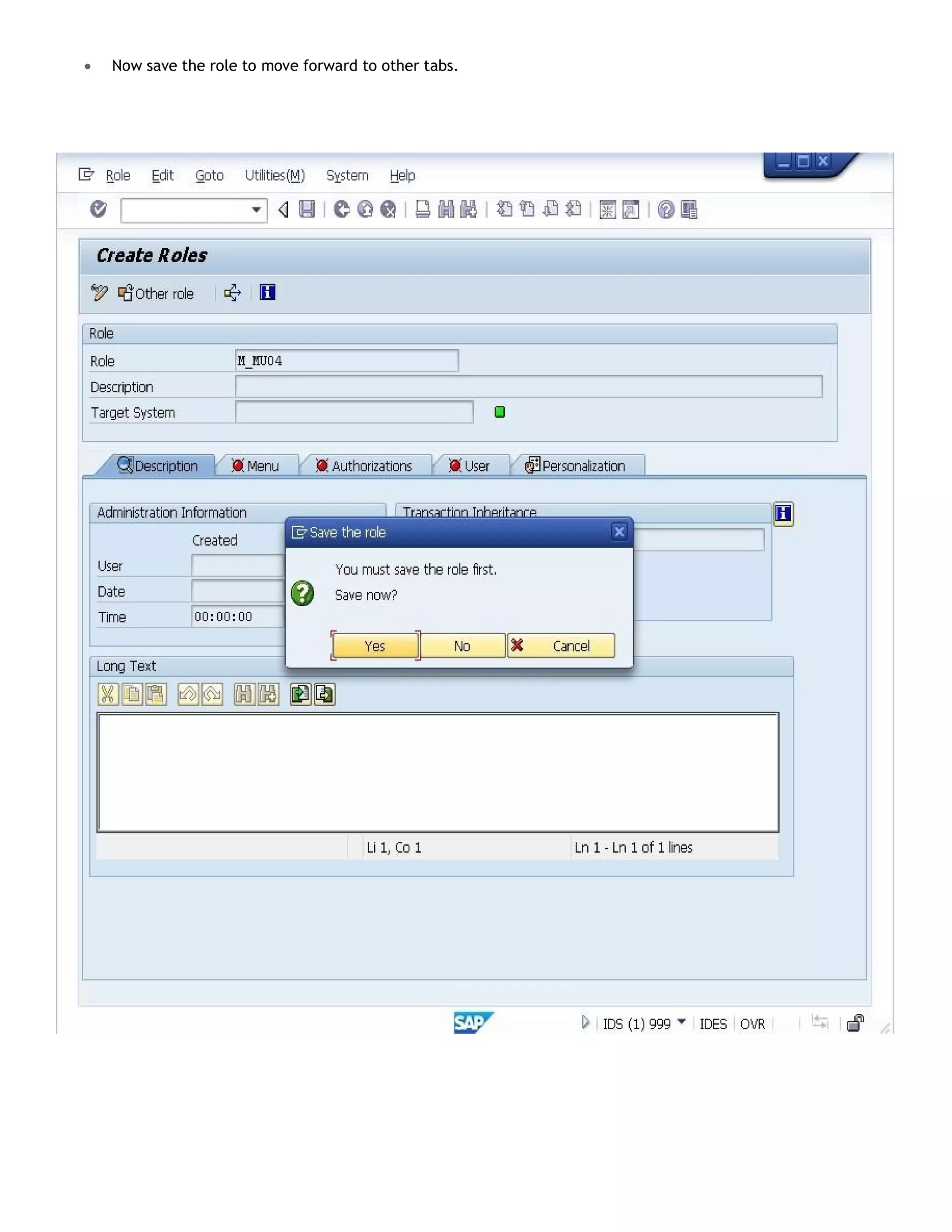
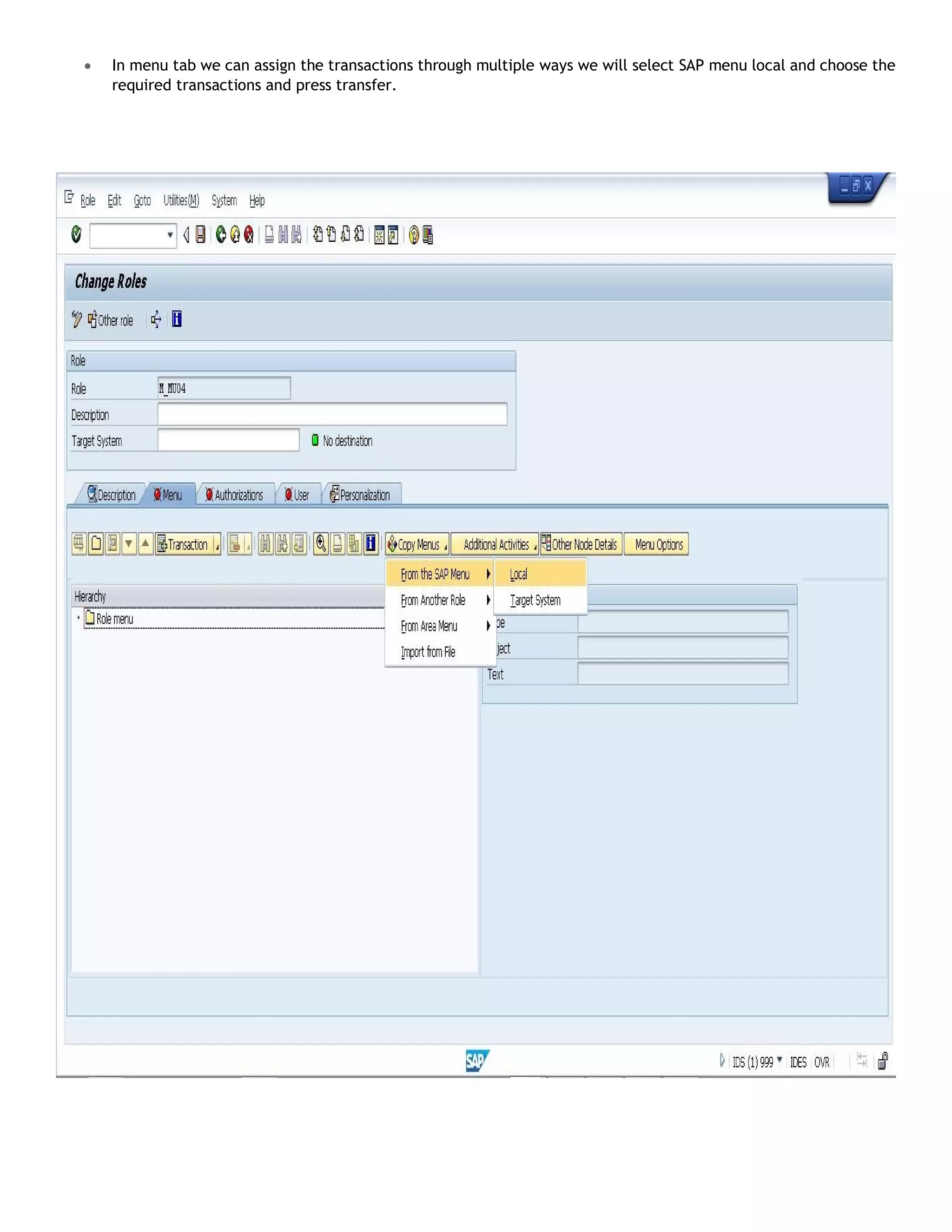
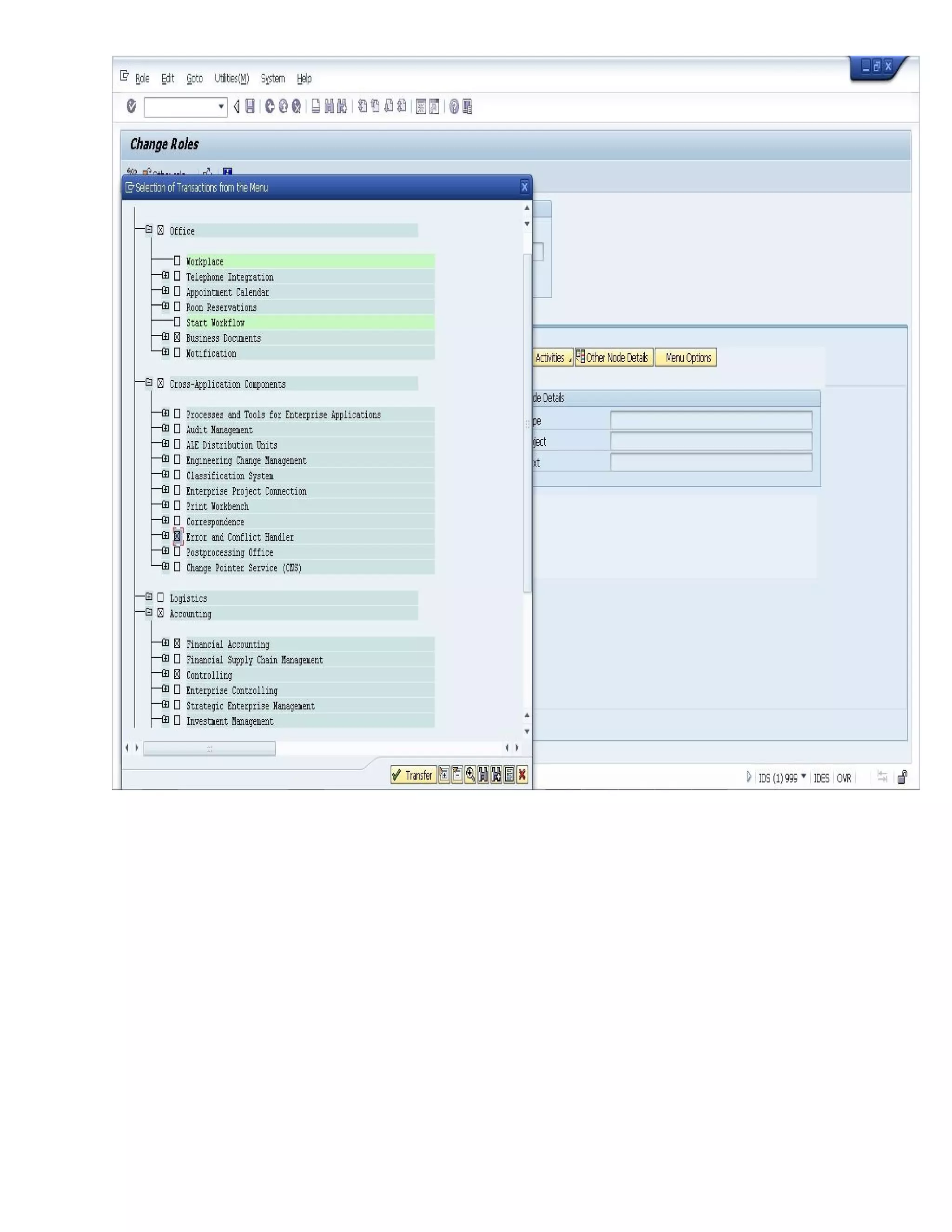
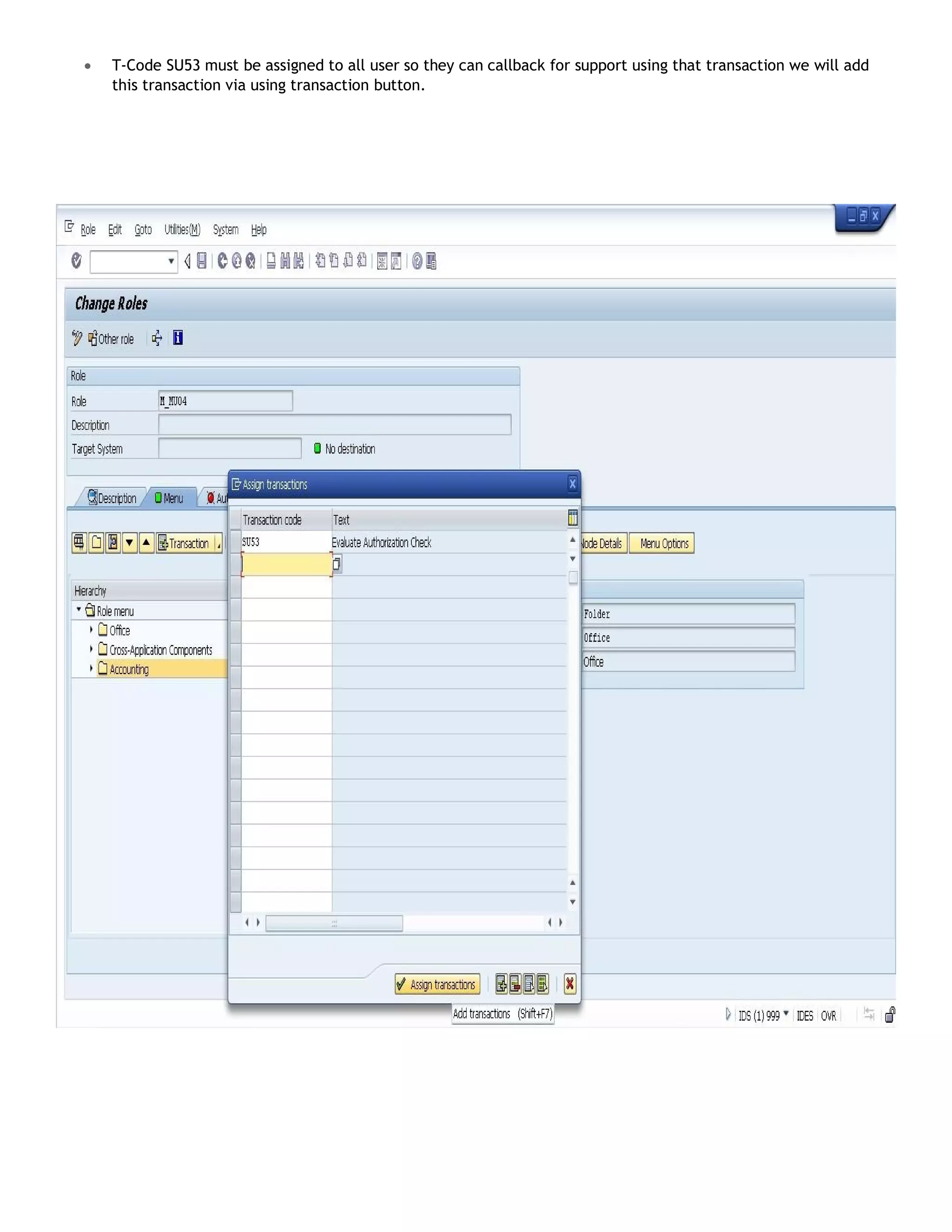
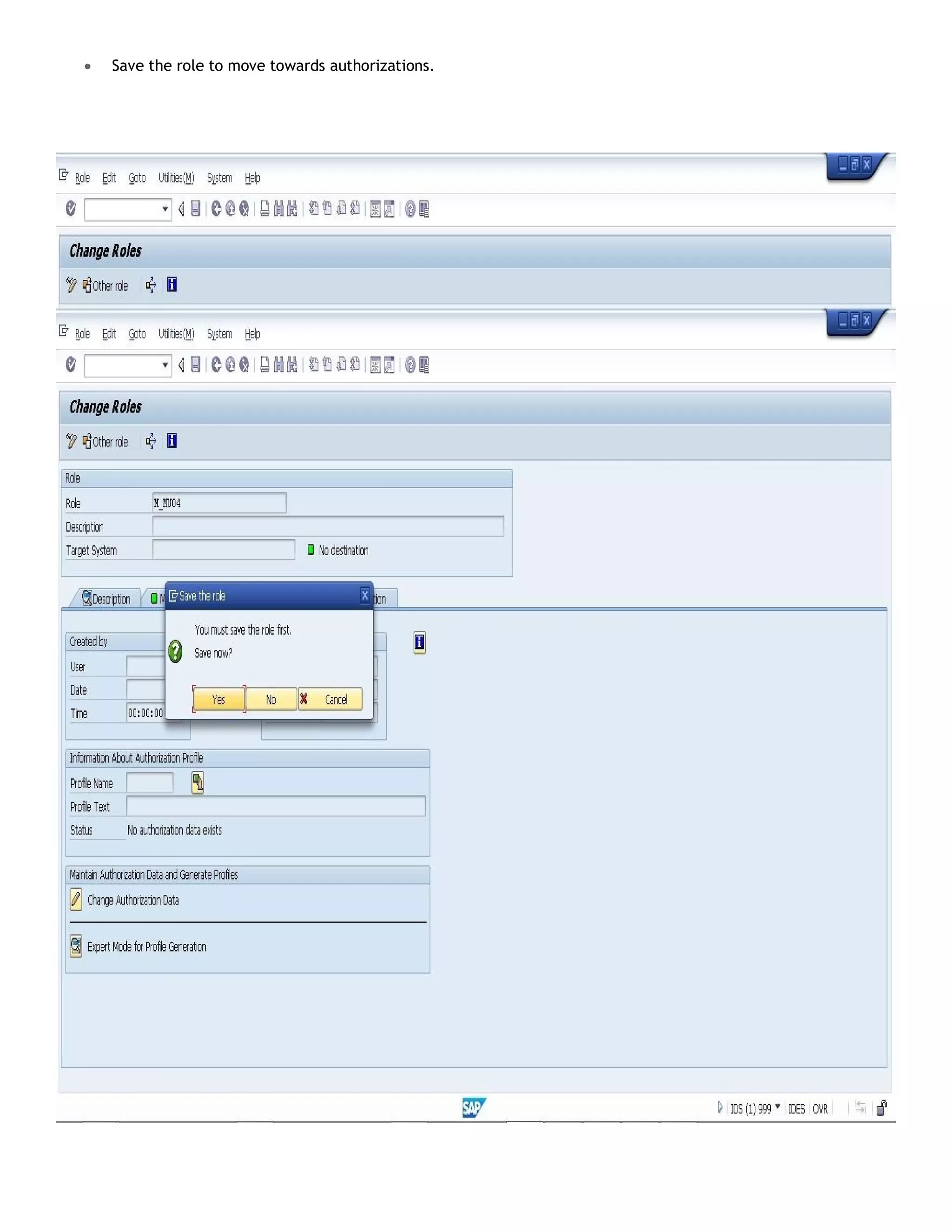
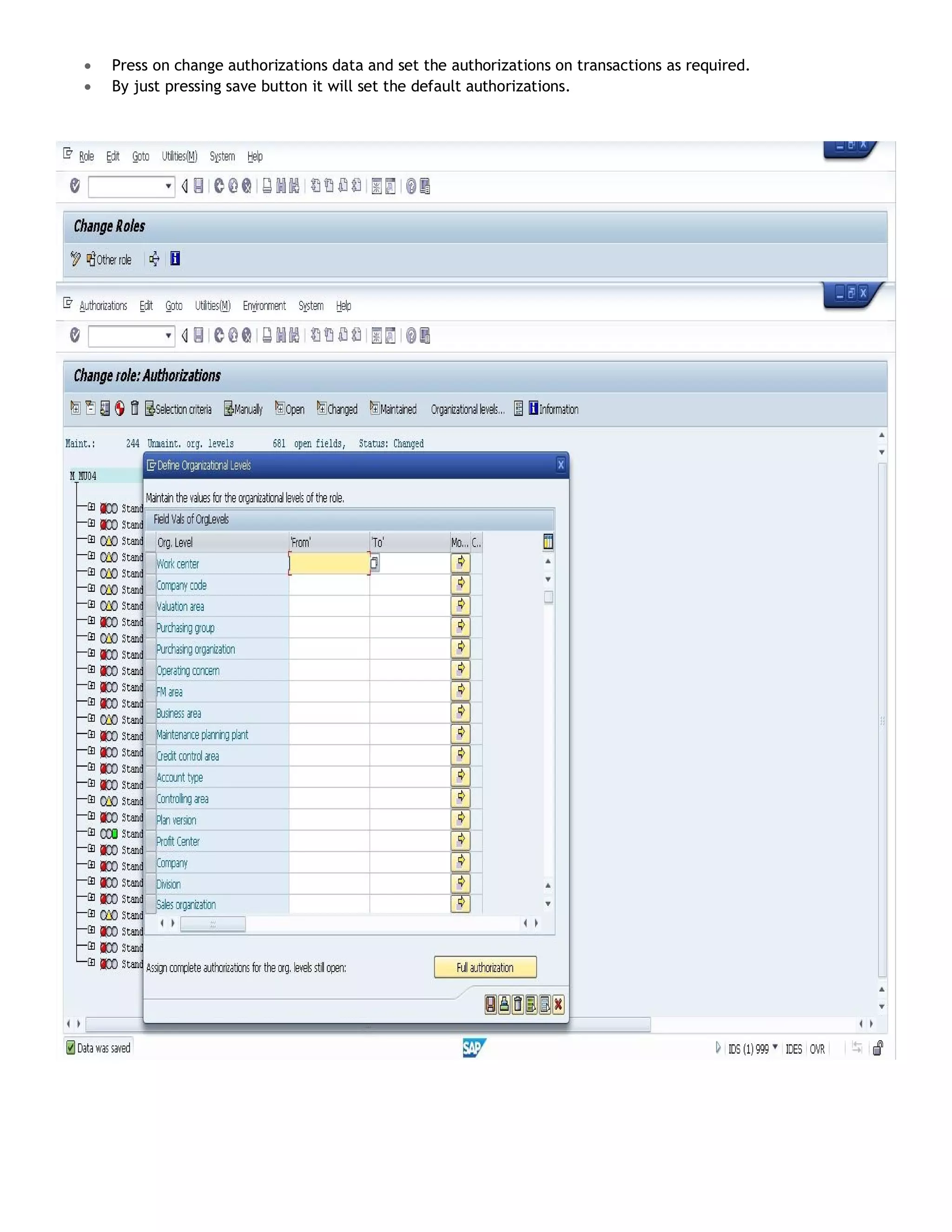
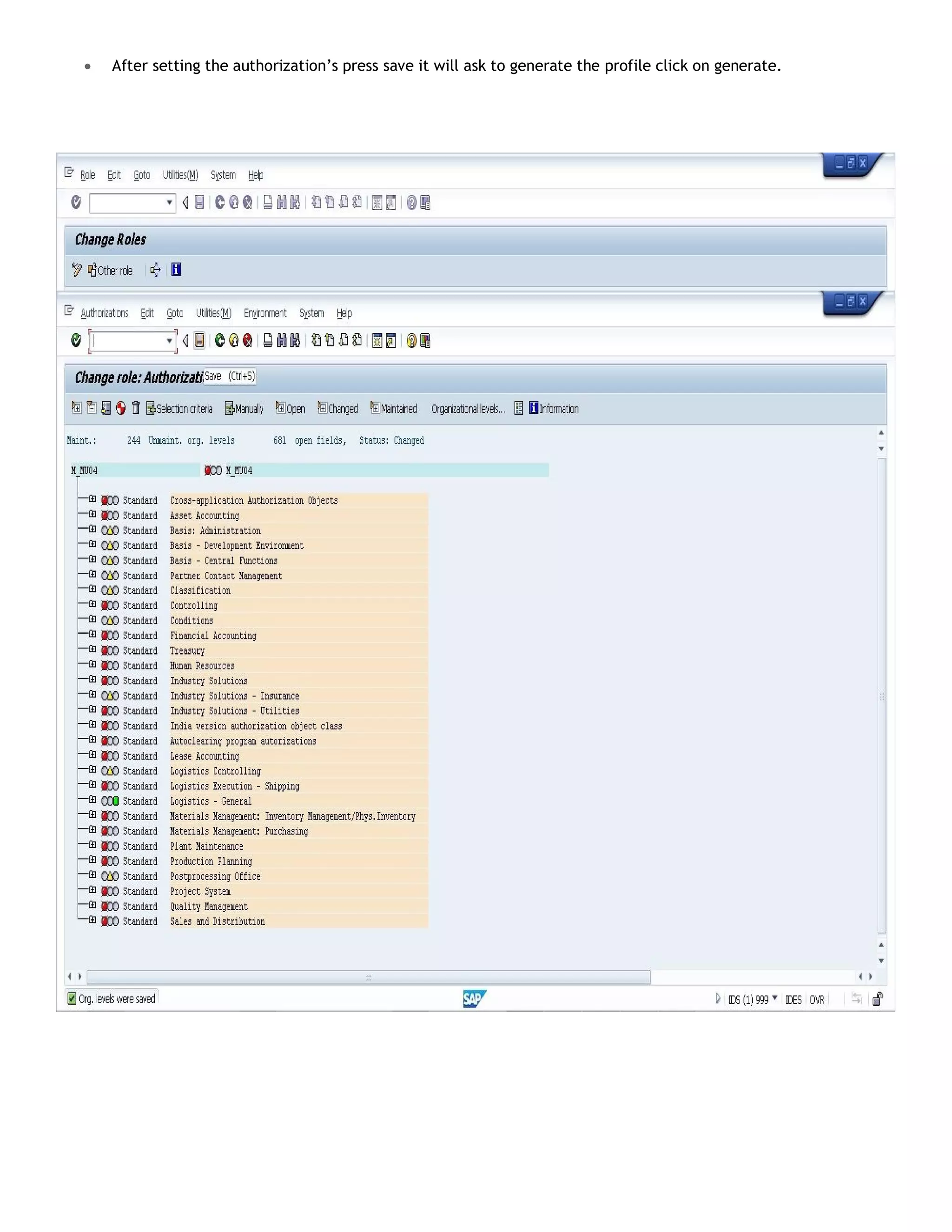
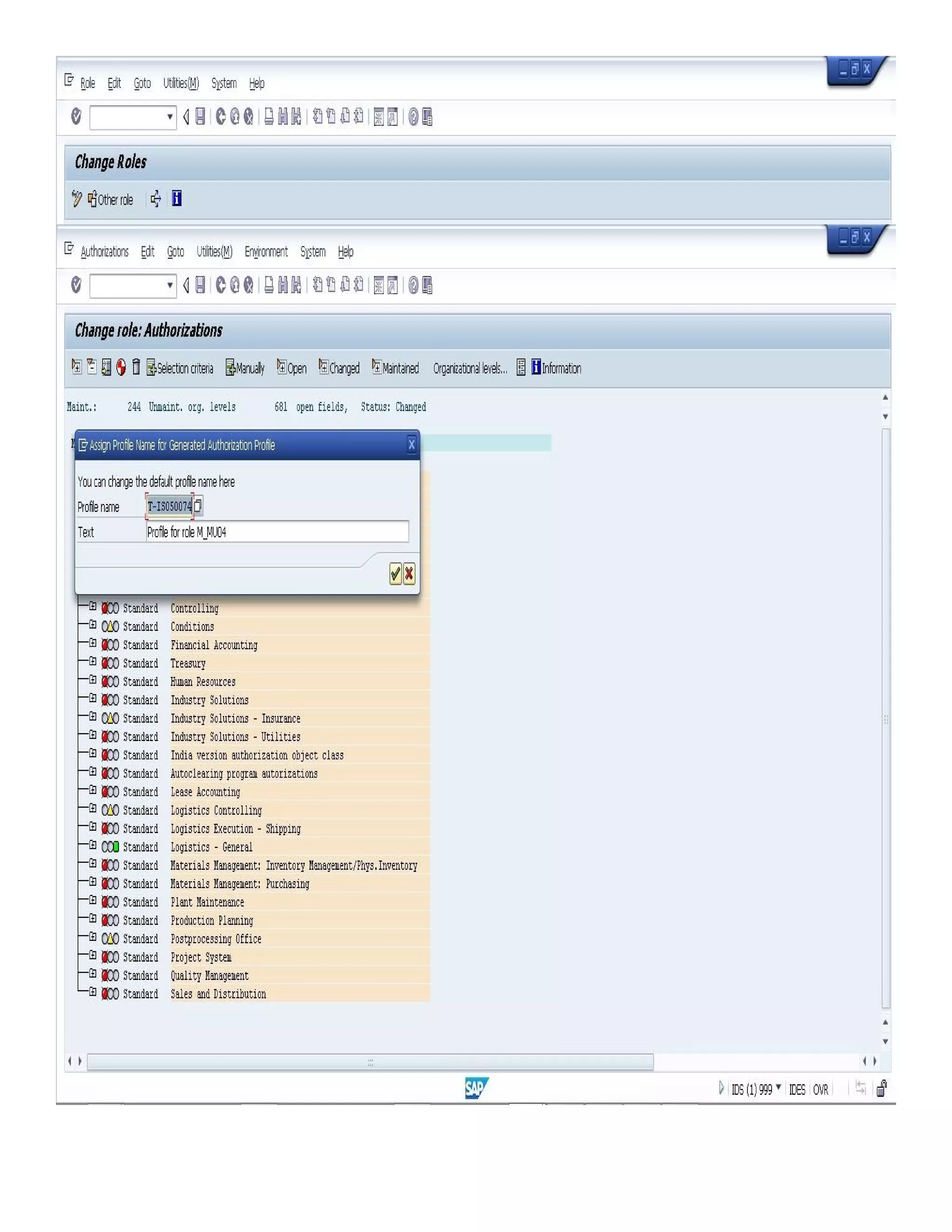
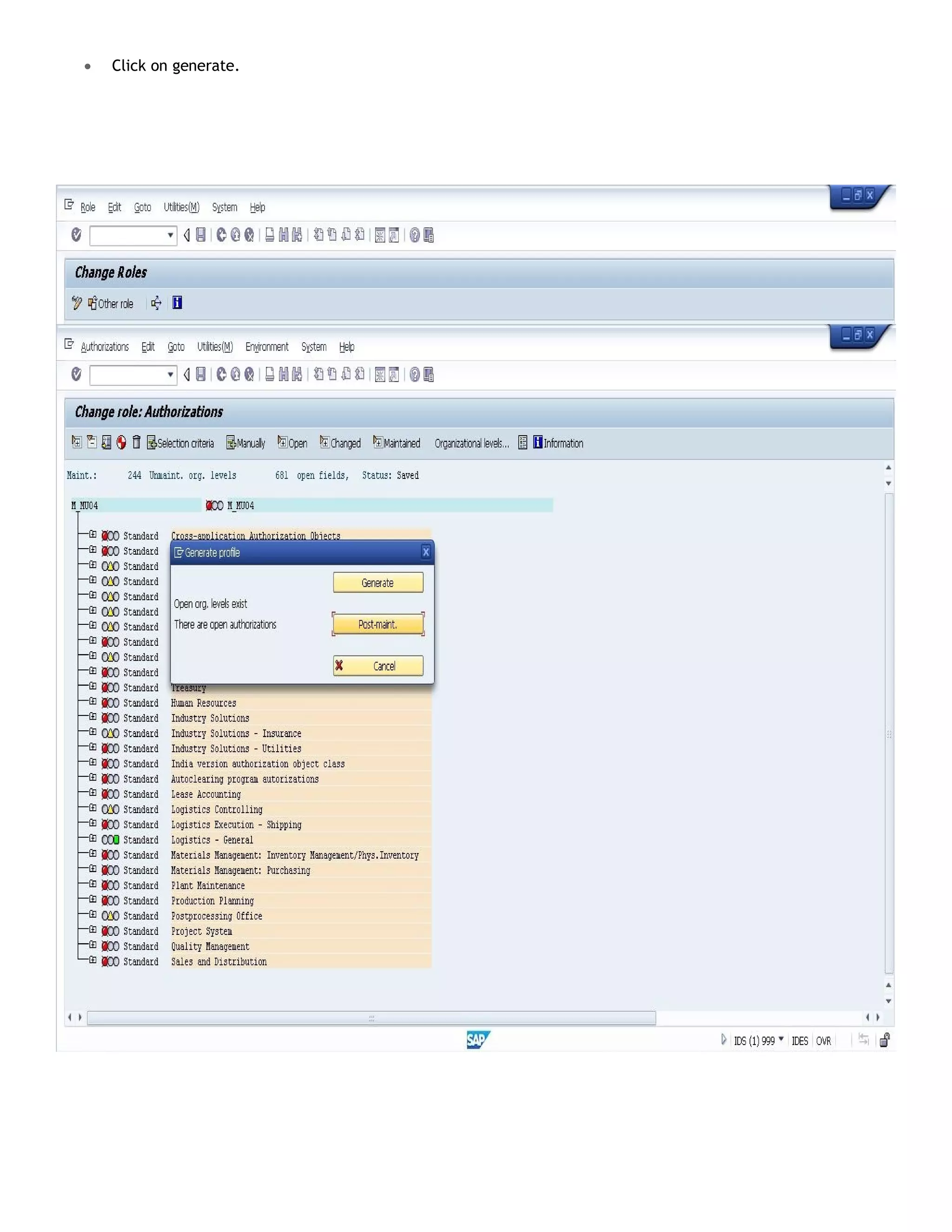
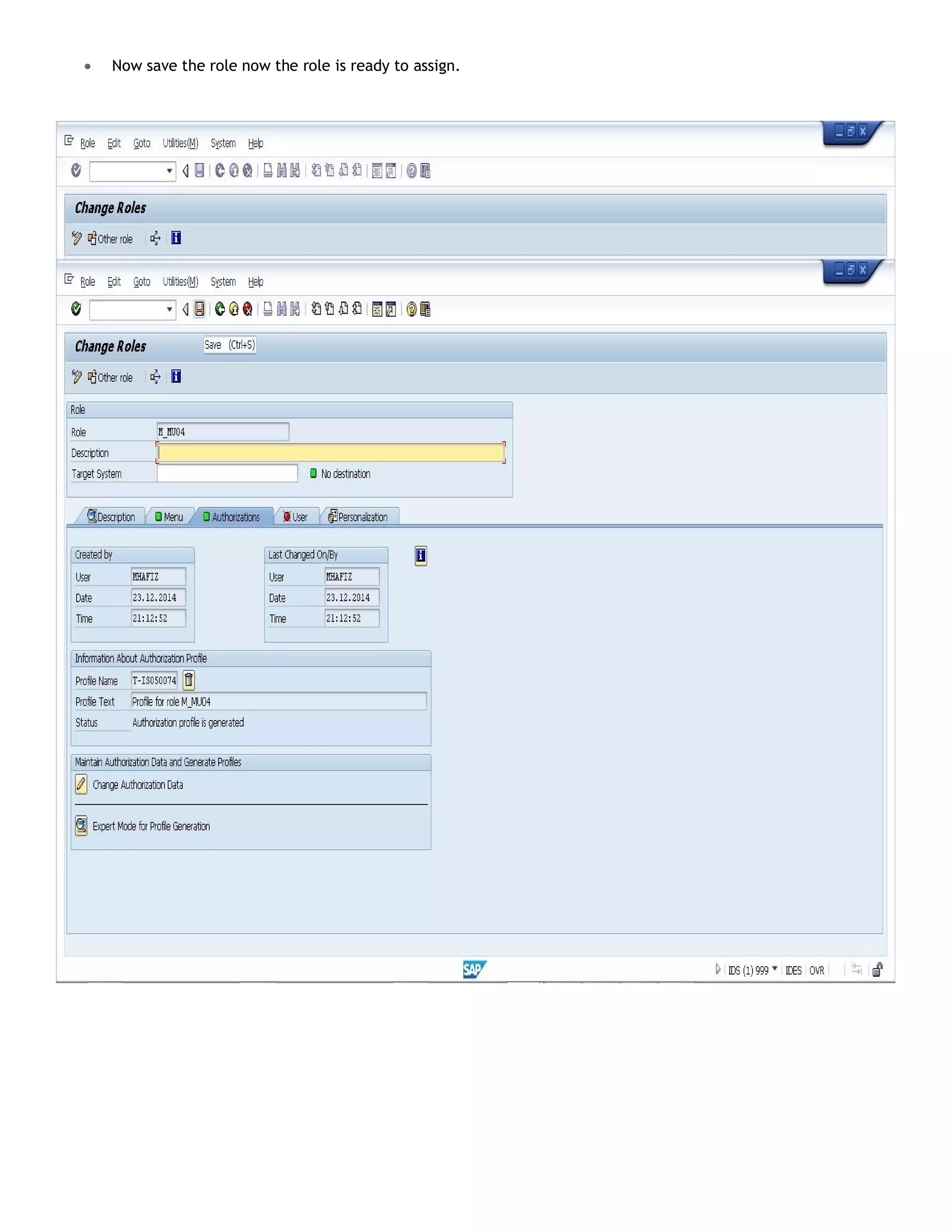
2. Create roles by running transaction PFCG, entering role names, and assigning authorizations and transactions.
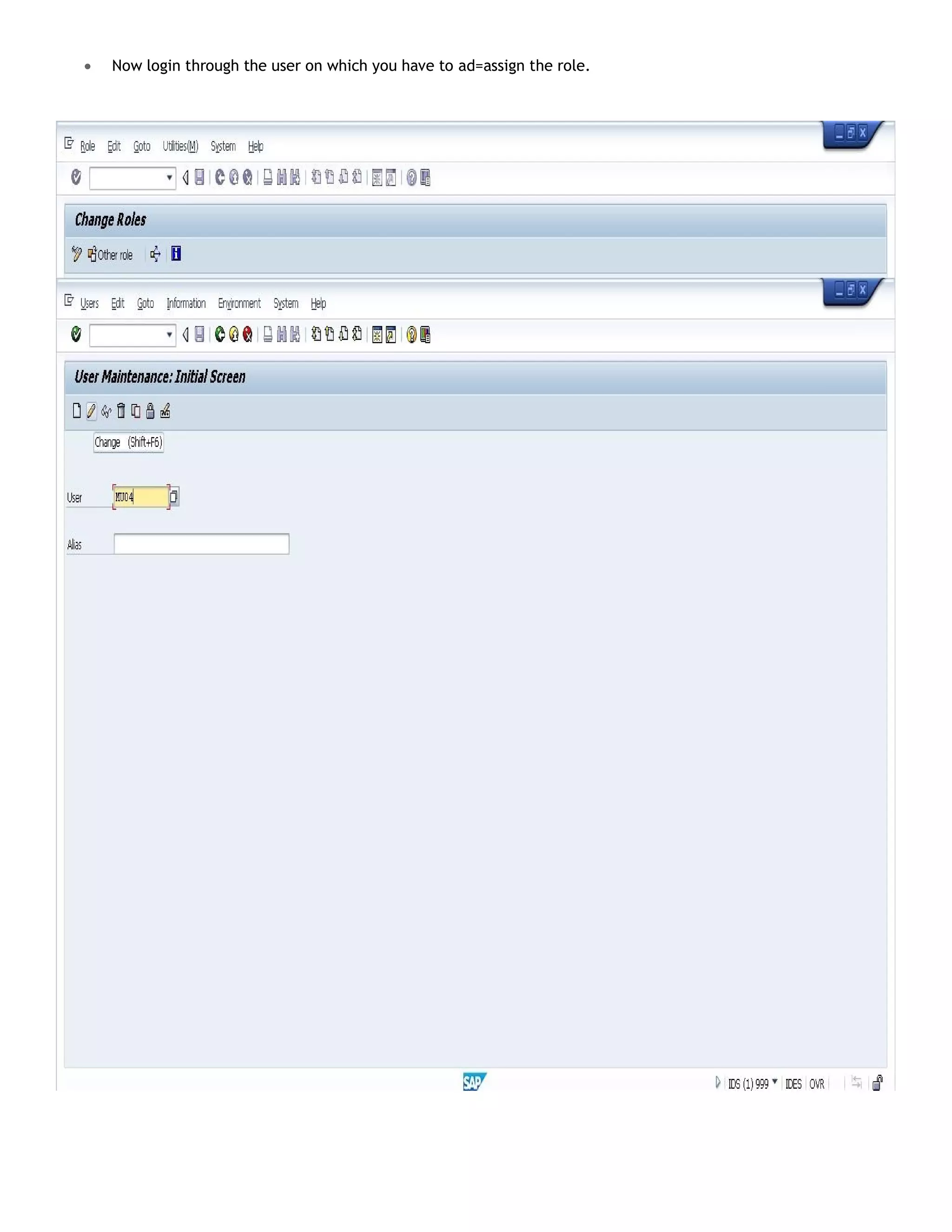
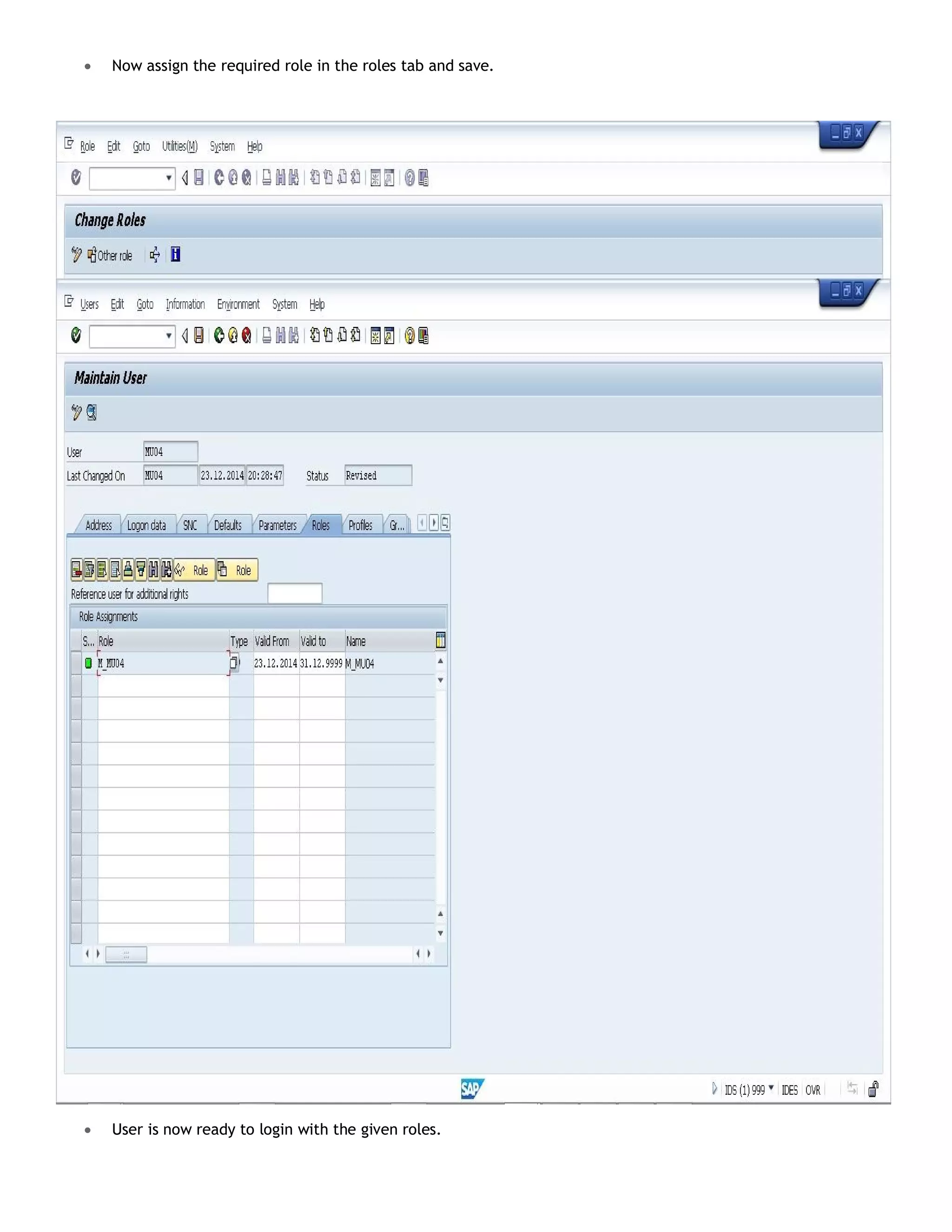
3. Assign the roles to users through transaction SU01.