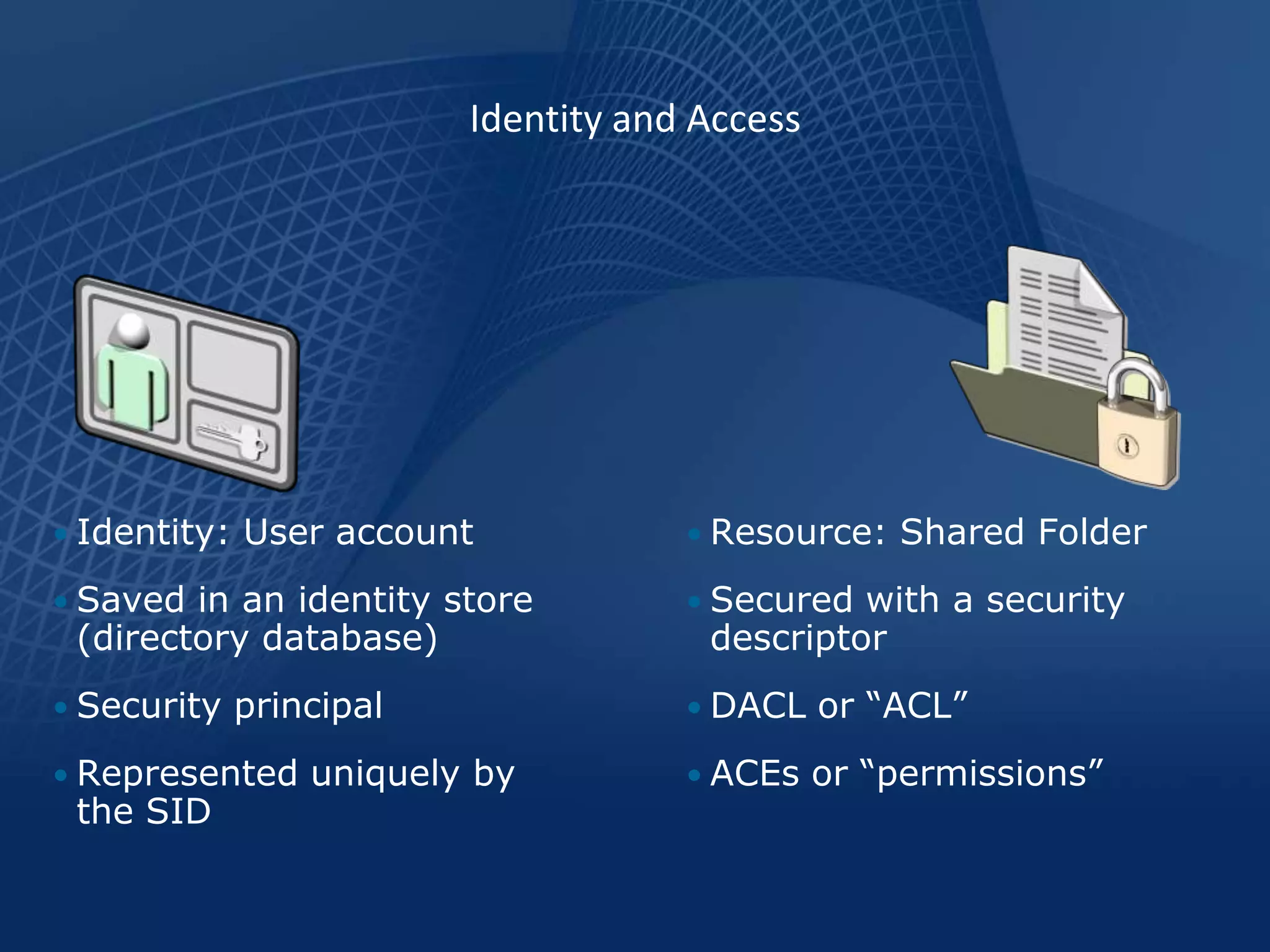
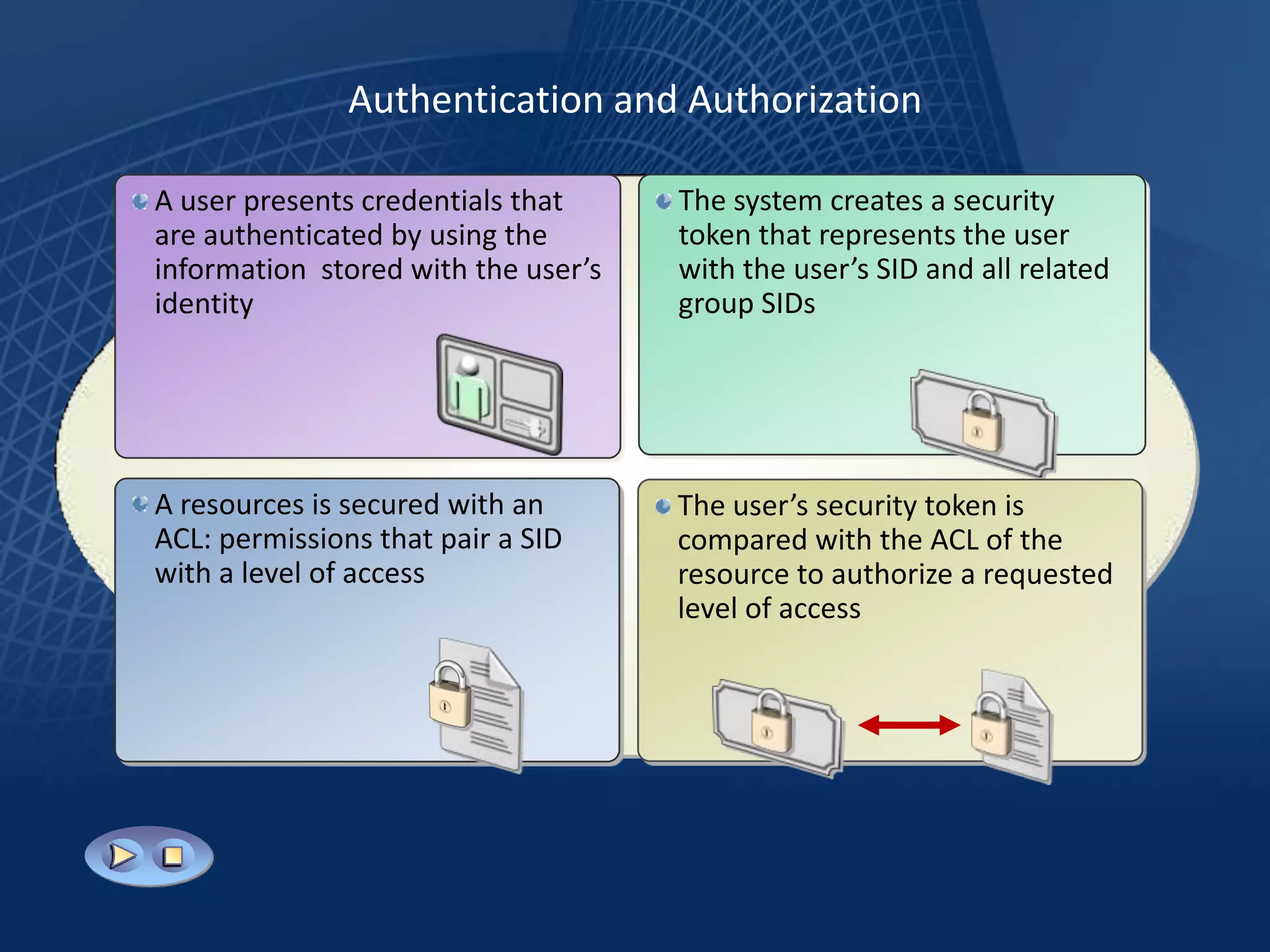
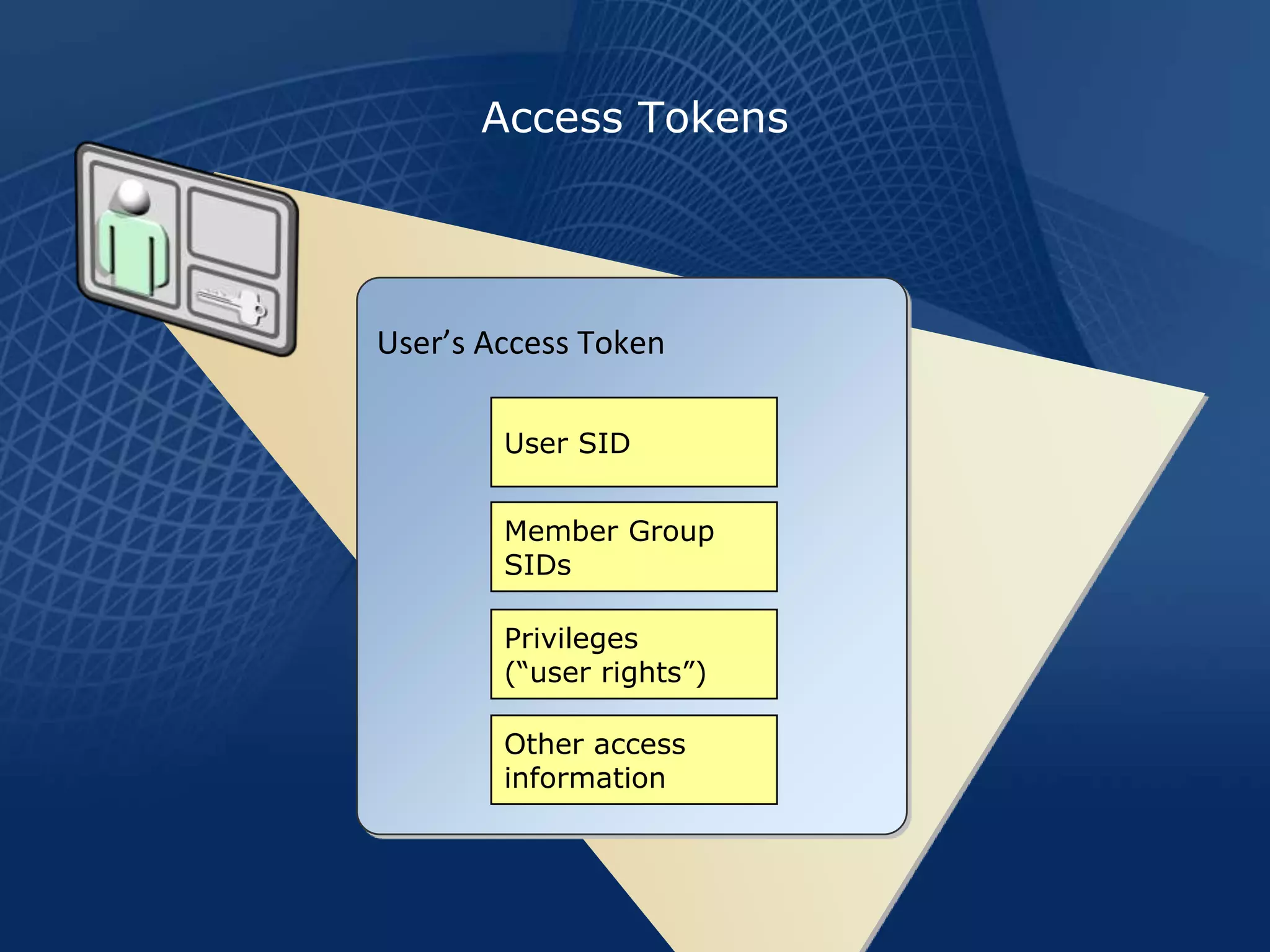
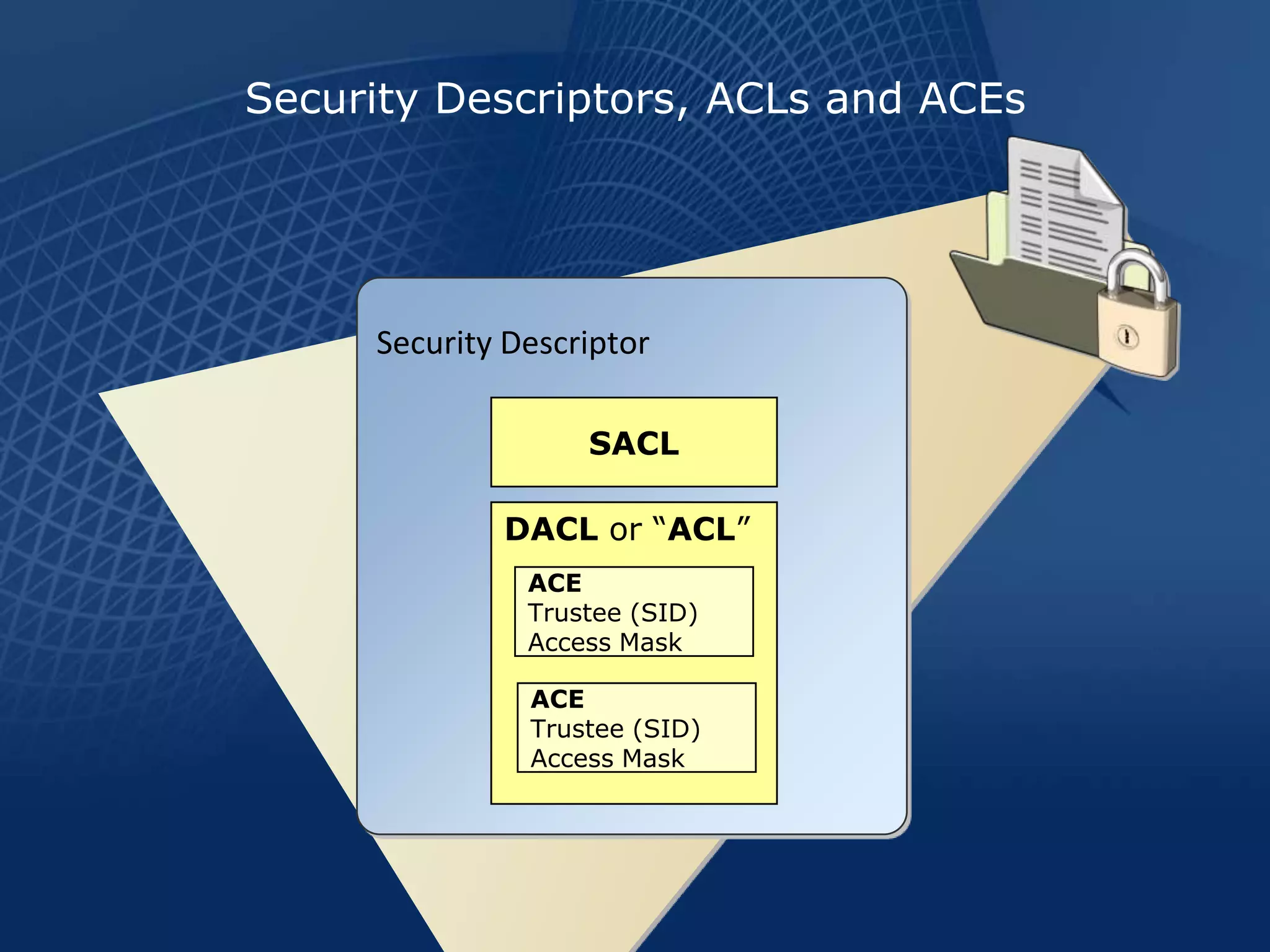
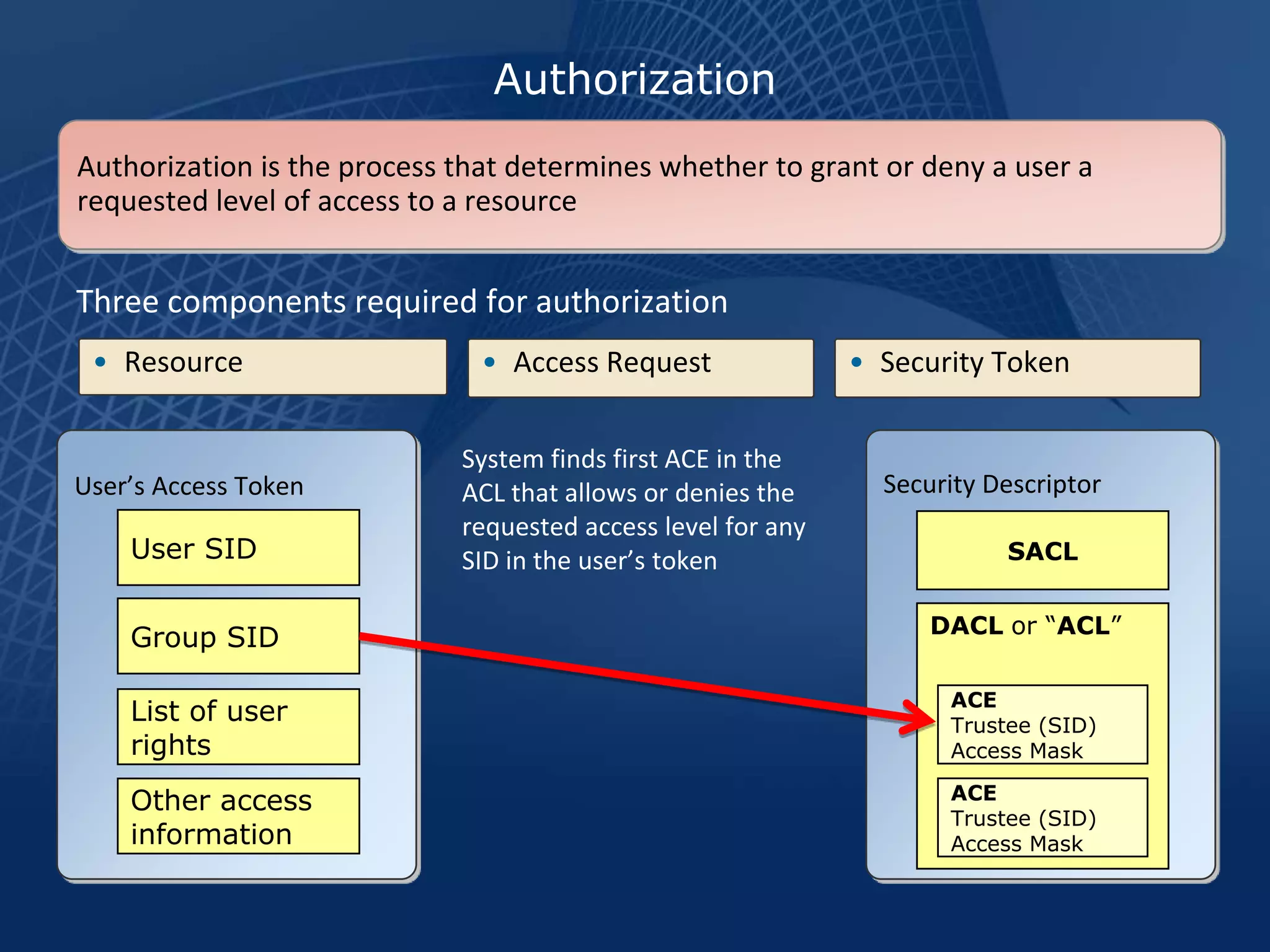
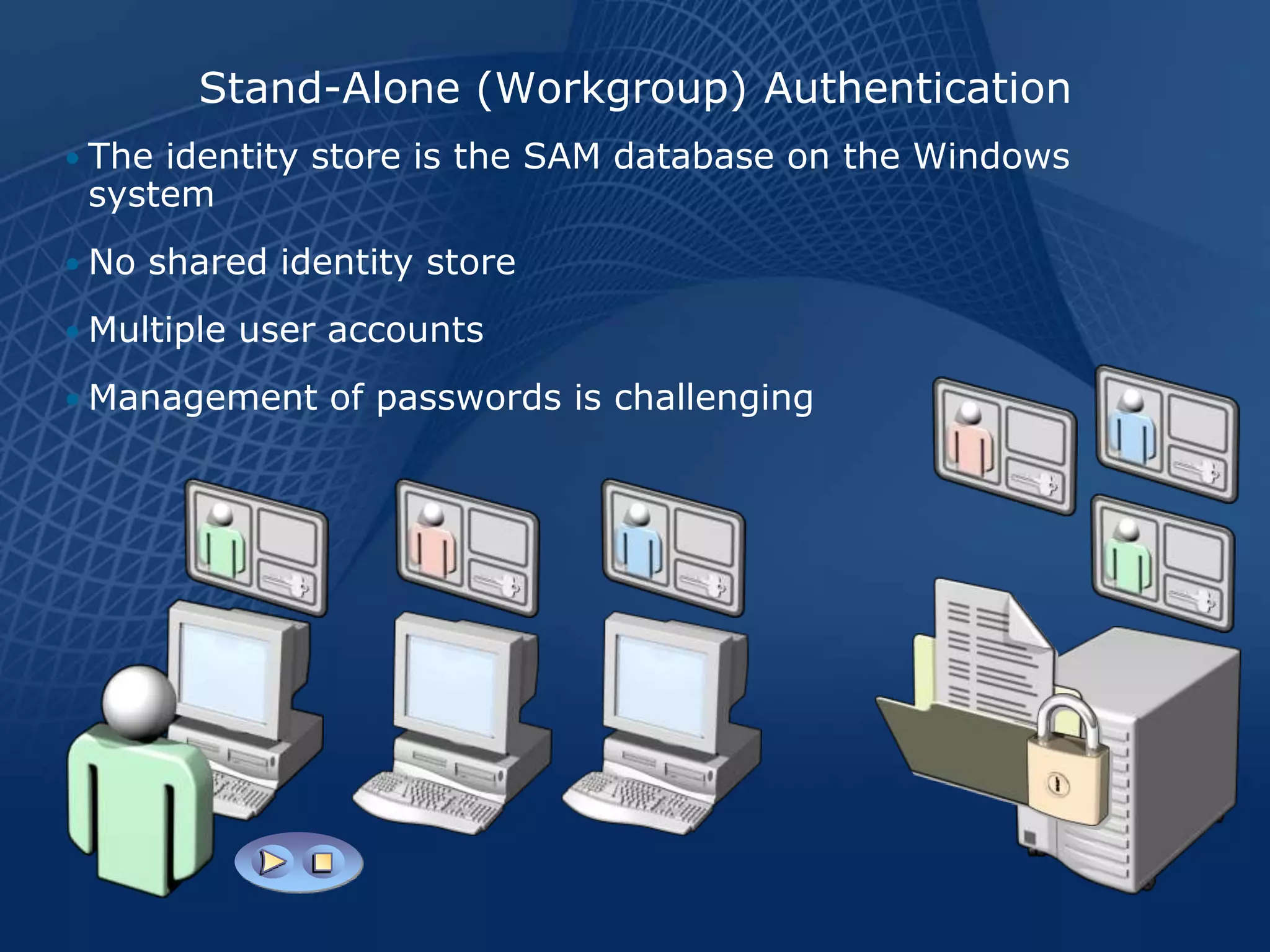
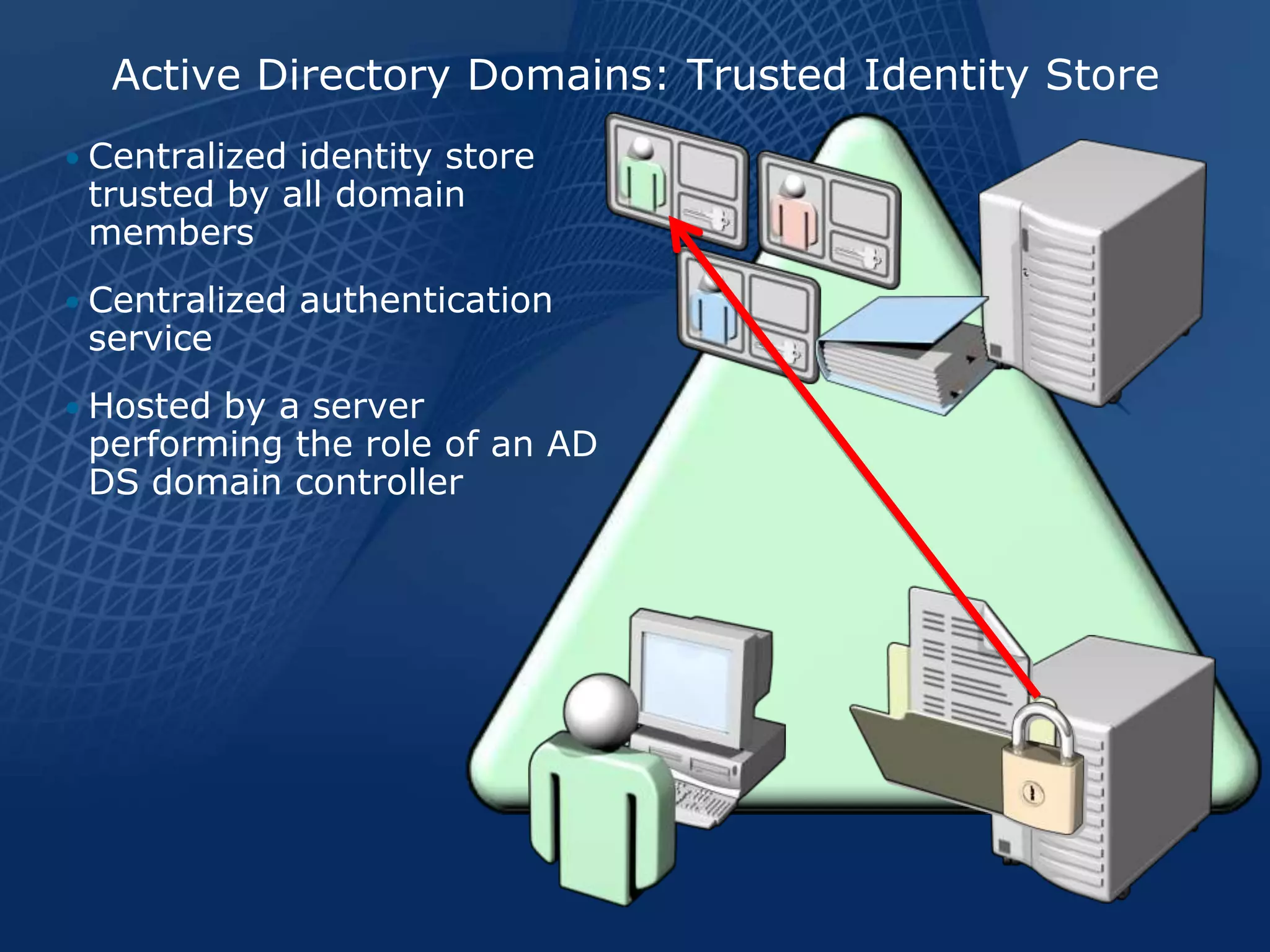
This document provides an overview of Active Directory, identity, and access management. It describes key Active Directory concepts such as domains, authentication, authorization, and security descriptors. It explains how Active Directory stores user and group identities in a centralized directory and uses authentication and authorization to control access to resources. Active Directory provides identity and access management services that help securely connect users to the information they need.