Embed presentation
Downloaded 14 times

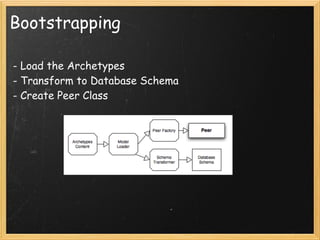
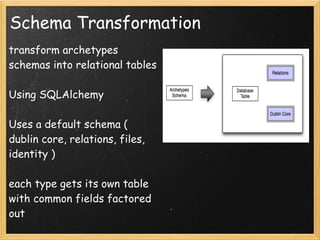
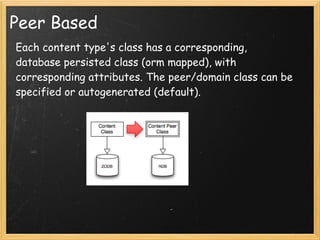
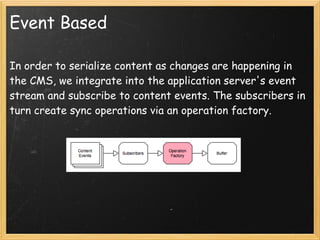
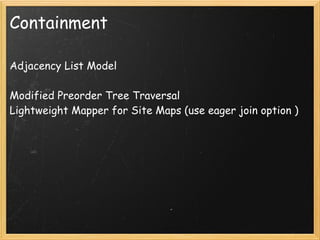
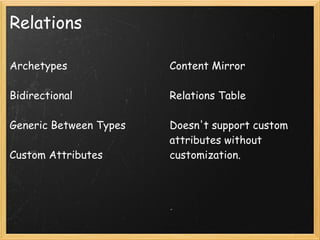
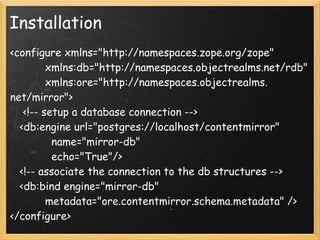
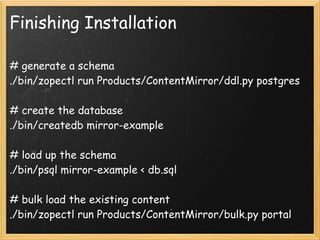

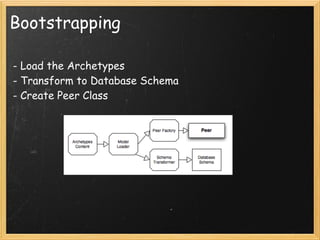
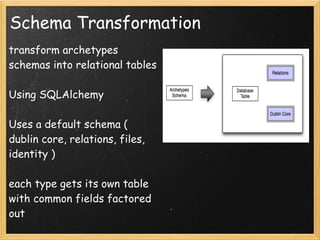
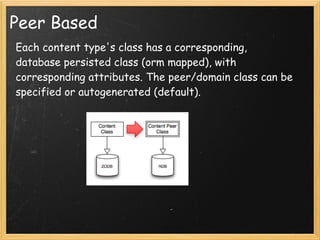
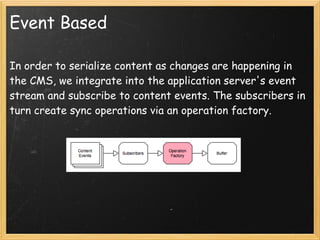
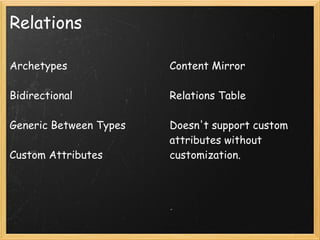
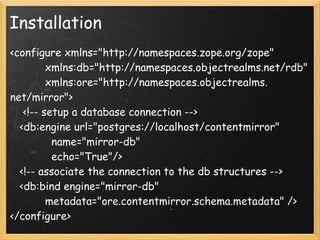
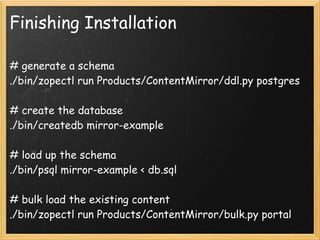
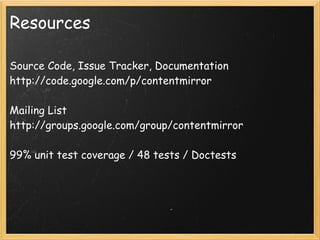
This document discusses Content Mirror, a tool that mirrors Plone content into a structured database. It serializes Plone content as it changes and stores it in a relational database for improved developer productivity and simpler deployment. It transforms Archetypes schemas into database tables, uses events to synchronize changes, and has options for installation, bulk loading content, and interacting with the mirrored data.