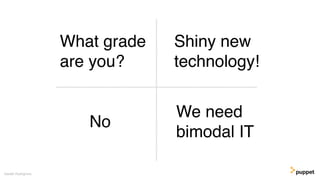
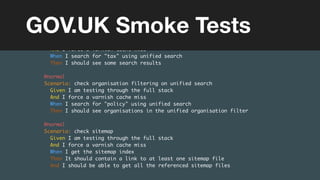
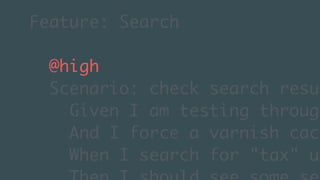
The document discusses the importance of communication and shared language in breaking down silos within government and technical organizations. It highlights that different teams often use jargon that can create barriers to collaboration and understanding. The author emphasizes the need for effective communication to improve relationships, enhance collaboration, and manage perceptions in a diverse environment.