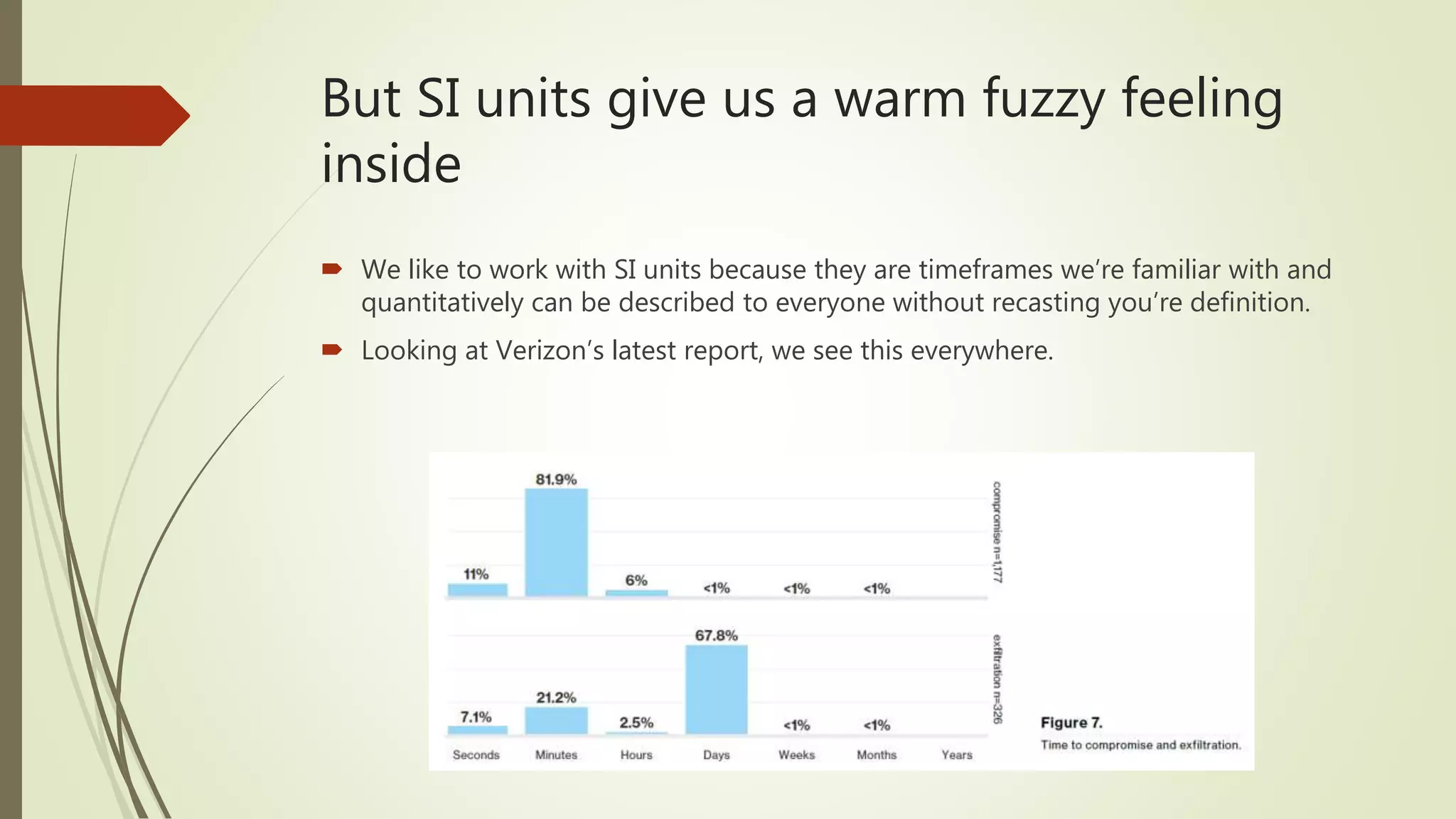
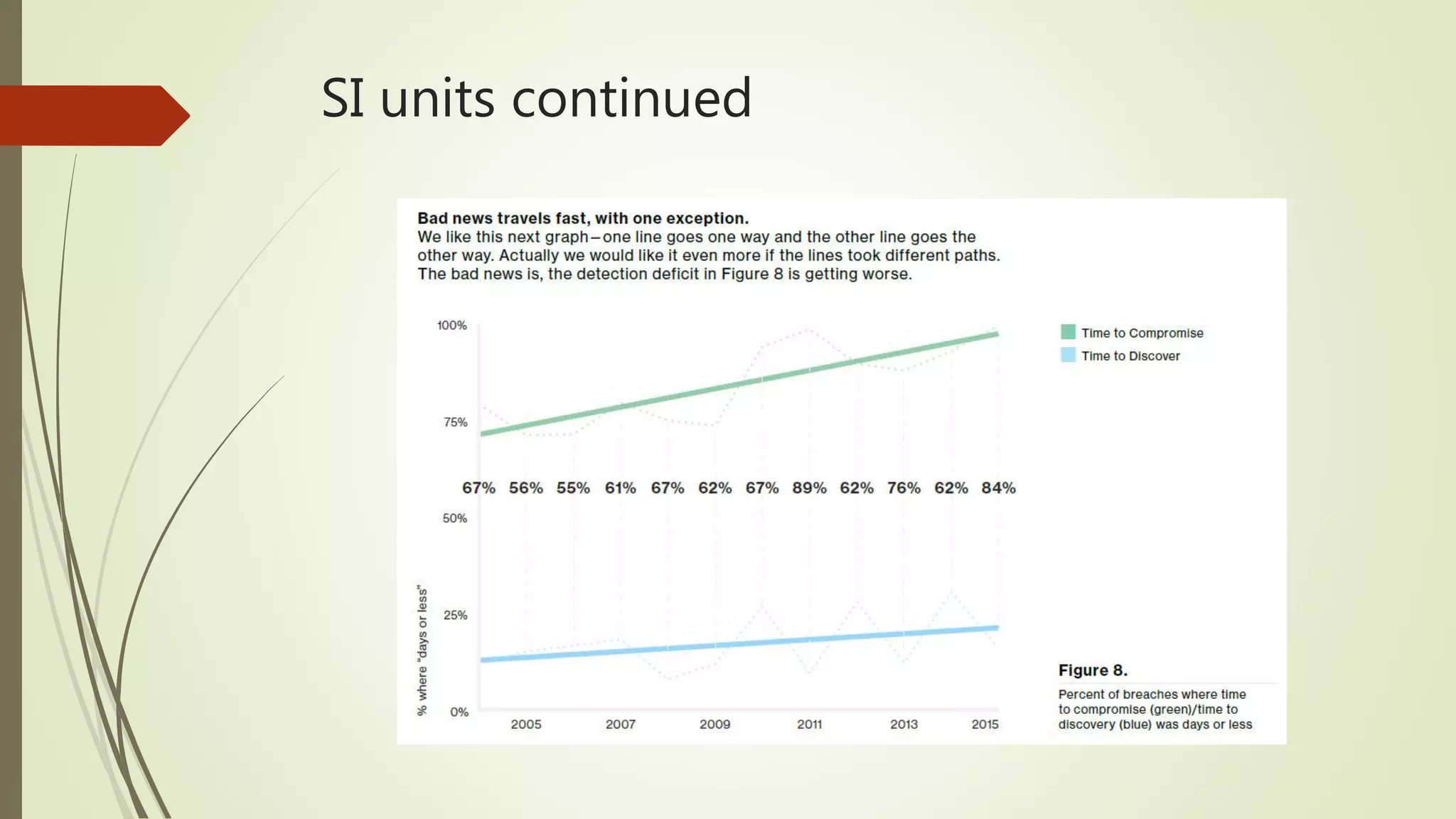
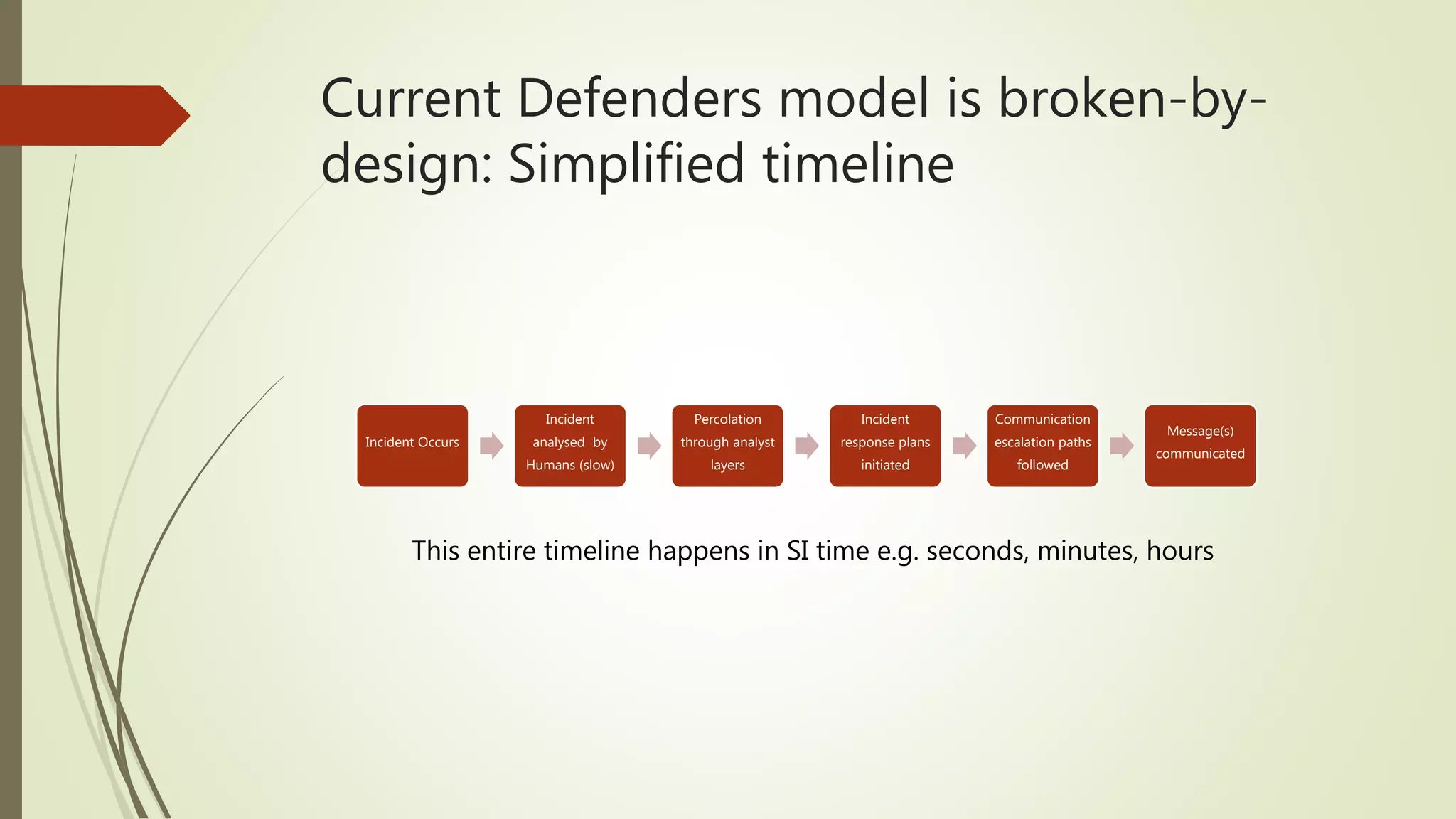
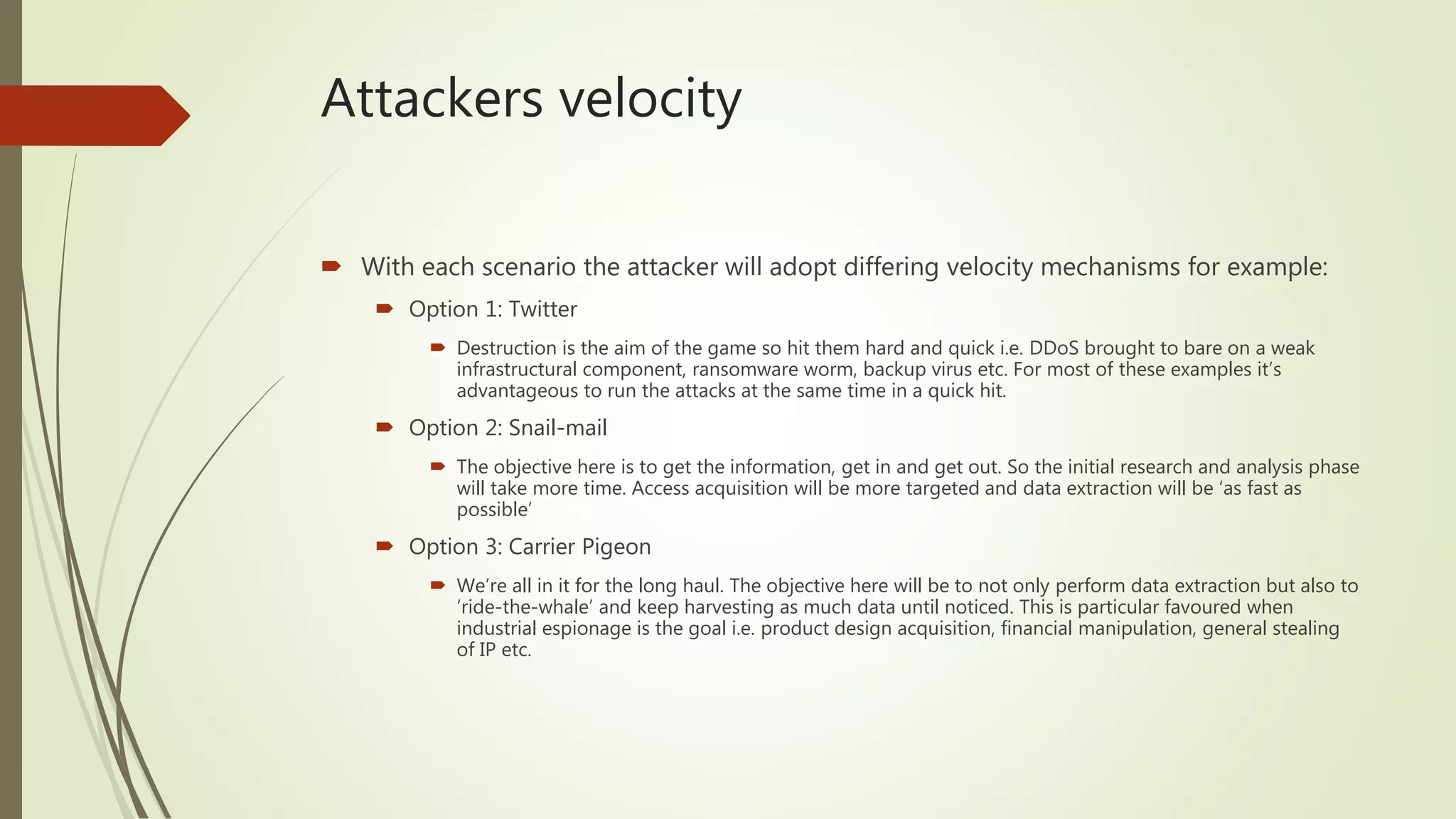
The document discusses the concept of velocity as it relates to cyber crises. It defines key terms like velocity, breach, and social impact. It argues that traditional measures of time like SI units are not meaningful for understanding crisis response, and that the speed of social networks is more important. It suggests defenders need to understand an adversary's speed, lay traps, and remain agile to keep up with the fast pace of cyber attacks in today's digital world. The current defender model is broken because it cannot respond in real-time at the speed information spreads on social platforms.