Common Areas of Data Breach
•
0 likes•109 views
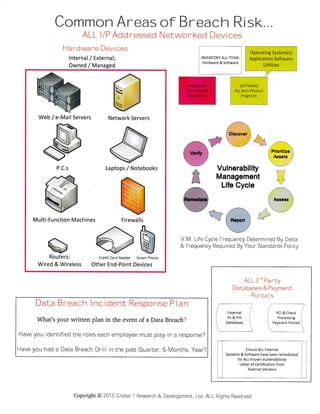
This document provides guidance on assessing cybersecurity risks and inventorying all hardware, software, and networked devices. It recommends identifying internal and external devices as well as owned and managed systems. Further, it suggests inventorying all items including operating systems, applications, utilities and their lifecycles. The document also stresses having a written data breach response plan that identifies employee roles and conducting regular breach drills. External systems should also be assessed for vulnerabilities and certified by vendors.
Report
Share
Report
Share
Download to read offline
Recommended
2016_Brochure_Book

The document introduces the SafeEx software solution for more efficient inspections and maintenance. SafeEx uses RFID technology and handheld devices to document inspections electronically, creating an audit trail and proving inspectors' presence on site. It saves at least 30% of man-hours through automated processes and uploads. SafeEx provides full transparency and traceability of inspection and maintenance data for both offshore and onshore management.
Understanding Safety Level Integrity Levels (SIL)

Safety is an important consideration in process design. Safety integrity level (or SIL) is often used to describe process safety requirements. However, there are often misconceptions or misunder- standings surrounding SIL. While the general subject, functional safety and SIL, can be highly technical, the general ideas can be distilled down to a few readily understandable concepts. In this paper, we will discuss what SIL is, why it is important, what certification means, and the implications and benefits of that certification to the end user.
Safety system

The document discusses safety systems used in industrial plants, including emergency shutdown systems (ESD), process shutdown systems (PSD), and fire and gas control systems (F&G). It defines these terms and describes their objectives, typical components, and functions. Safety is measured by factors like average probability of failure on demand (PFDavg) and risk reduction factor (RRF). The document also covers related topics like hazard analysis, risk, reliability, availability, and definitions of key safety terminology.
Complying with New Functional Safety Standards

The document is a presentation on complying with new functional safety standards. It discusses what functional safety is, what is happening in the functional safety market, what standards should be used for machines, and how to determine safety levels and perform calculations according to standards like ISO 13849-1 and IEC 62061. It provides an example of applying the standards to a dual channel emergency stop application and calculating the resulting safety integrity level.
Understanding sil

This document discusses Safety Integrity Level (SIL) and how it is used to quantify safety in industrial processes. It provides background on the development of international safety standards and defines key terms like SIL, Safety Instrumented Functions (SIF), Probability of Failure on Demand (PFD), and Safe Failure Fraction (SFF). The document explains how hazards analysis is used to determine target SIL levels for safety systems and instrumentation. It also outlines methods for evaluating SIL, including Failure Modes and Effects Analysis (FMEDA) and proven in use testing. Overall, the document provides a comprehensive overview of applying SIL standards to ensure safety in industrial control systems.
Applying IEC 62304 Risk Management in Aligned Elements - the medical device ALM

A concrete example of linking risk management using a preliminary hazard analysis approach with the software architecture when applying IEC 62304 in a medical device ALM.
Critical Steps in Software Development: Enhance Your Chances for a Successful...

Critical Steps in Software Development: Enhance Your Chances for a Successful...Sterling Medical Devices
What if my Software is a Medical Device?
Impacts Design/Development
Impacts Maintenance
PMA or 510K?
If PMA, Clinical Data is NeededSafety Integrity Levels

Safety-critical systems are computer systems whose failure could result in injury, death, or environmental damage. Examples include aircraft control systems, nuclear power plant controls, medical devices like pacemakers, and railway signaling systems. These systems require high integrity to avoid hazards and ensure safety. Techniques like developing diverse redundant systems can improve safety by detecting and tolerating a wider range of faults.
Recommended
2016_Brochure_Book

The document introduces the SafeEx software solution for more efficient inspections and maintenance. SafeEx uses RFID technology and handheld devices to document inspections electronically, creating an audit trail and proving inspectors' presence on site. It saves at least 30% of man-hours through automated processes and uploads. SafeEx provides full transparency and traceability of inspection and maintenance data for both offshore and onshore management.
Understanding Safety Level Integrity Levels (SIL)

Safety is an important consideration in process design. Safety integrity level (or SIL) is often used to describe process safety requirements. However, there are often misconceptions or misunder- standings surrounding SIL. While the general subject, functional safety and SIL, can be highly technical, the general ideas can be distilled down to a few readily understandable concepts. In this paper, we will discuss what SIL is, why it is important, what certification means, and the implications and benefits of that certification to the end user.
Safety system

The document discusses safety systems used in industrial plants, including emergency shutdown systems (ESD), process shutdown systems (PSD), and fire and gas control systems (F&G). It defines these terms and describes their objectives, typical components, and functions. Safety is measured by factors like average probability of failure on demand (PFDavg) and risk reduction factor (RRF). The document also covers related topics like hazard analysis, risk, reliability, availability, and definitions of key safety terminology.
Complying with New Functional Safety Standards

The document is a presentation on complying with new functional safety standards. It discusses what functional safety is, what is happening in the functional safety market, what standards should be used for machines, and how to determine safety levels and perform calculations according to standards like ISO 13849-1 and IEC 62061. It provides an example of applying the standards to a dual channel emergency stop application and calculating the resulting safety integrity level.
Understanding sil

This document discusses Safety Integrity Level (SIL) and how it is used to quantify safety in industrial processes. It provides background on the development of international safety standards and defines key terms like SIL, Safety Instrumented Functions (SIF), Probability of Failure on Demand (PFD), and Safe Failure Fraction (SFF). The document explains how hazards analysis is used to determine target SIL levels for safety systems and instrumentation. It also outlines methods for evaluating SIL, including Failure Modes and Effects Analysis (FMEDA) and proven in use testing. Overall, the document provides a comprehensive overview of applying SIL standards to ensure safety in industrial control systems.
Applying IEC 62304 Risk Management in Aligned Elements - the medical device ALM

A concrete example of linking risk management using a preliminary hazard analysis approach with the software architecture when applying IEC 62304 in a medical device ALM.
Critical Steps in Software Development: Enhance Your Chances for a Successful...

Critical Steps in Software Development: Enhance Your Chances for a Successful...Sterling Medical Devices
What if my Software is a Medical Device?
Impacts Design/Development
Impacts Maintenance
PMA or 510K?
If PMA, Clinical Data is NeededSafety Integrity Levels

Safety-critical systems are computer systems whose failure could result in injury, death, or environmental damage. Examples include aircraft control systems, nuclear power plant controls, medical devices like pacemakers, and railway signaling systems. These systems require high integrity to avoid hazards and ensure safety. Techniques like developing diverse redundant systems can improve safety by detecting and tolerating a wider range of faults.
Shahzad Khan

This document summarizes an individual's experience and qualifications providing machine condition monitoring and preventative maintenance services. They have 1.5 years experience collecting and analyzing vibration and operational data using various online and offline monitoring systems and software. Their responsibilities include routine condition monitoring of rotating equipment using vibration analysis, thermography, and ultrasound inspection. They also support troubleshooting, failure investigations, field balancing, and laser alignment activities.
Medical Device Software

Morgunfundur um markaðskröfur og staðla fyrir lækningavöru og stoðkerfi á heilbrigðissviði 8. mars 2012 - Garðar Þorvarðsson
V&V Considerations In Implementing IEC61508-3

This document discusses verification and validation considerations for implementing IEC 61508-3. It begins with an overview of Oak Systems, a specialist in software verification and validation services. It then provides an overview of IEC 61508-3 and verification and validation (V&V). The rest of the document discusses the IEC 61508 safety lifecycle, key terms and definitions, safety integrity levels, development activities and tools to support V&V, software verification techniques, functional safety assessment, and tables relating technique rigor to safety integrity levels. It concludes that IEC 61508 alone may not be sufficient for all applications and other standards like UL1998 may also need to be considered.
QAdvis - software risk management based on IEC/ISO 62304

This document provides an overview of risk management for medical device software as outlined in IEC 62304. It discusses:
1) IEC 62304 calls for risk management activities throughout the entire software development lifecycle. This includes identification, analysis, evaluation, control and monitoring of risks.
2) Both quantitative and qualitative techniques can be used for risk analysis, such as FMECA, FTA, HAZOP. Requirement-based and risk-based verification strategies are also expected.
3) Effective risk management relies on good software engineering practices and processes. It aims to regulate verification efforts to balance productivity and compliance.
8. operational risk management

This document discusses operational risk management and system safety. It defines key terms like system safety, hazard probability, and hazard severity. It describes the system safety process which involves defining objectives, hazard identification, analysis, risk evaluation, and hazard controls. It also discusses failure modes and effects analysis. Overall, the document provides an overview of operational risk management processes like identifying hazards, assessing and analyzing risks, making control decisions, and supervising risk controls. It discusses how to make risk management decisions and defines terms like identified risk and acceptable risk.
Hardware review rubrics

This rubric evaluates a student's performance on a computer repair and troubleshooting assessment with 5 stations: 1) identifying computer components, 2) identifying tools, 3) more component identification, 4) assembling a computer, and 5) troubleshooting hardware issues on 4 computers. The student can earn up to 125 points total by correctly completing tasks at each station and demonstrating appropriate workplace behavior and safety. Their score will be assessed in categories like below average, average, good, or excellent.
Reliability Instrumented System | Arrelic Insights 

An approach that strays from the conventional, coupled with
consistency, enables us to contribute to the company's overall
growth and success.
This Insights talks about RIS Process and applications
Malewareanalysis 

This document discusses malware analysis. It covers types of malware like viruses, worms, and trojans. It describes how malware can infect hosts by overwriting, prepending, appending, or using packers. Methods of malware detection like signatures, heuristics, checksums, and sandboxes are presented. The goals, types, and tools of malware analysis are outlined along with simulation steps and conclusions.
DeviceDriverNov18.ppt

This document provides an overview of device drivers. It defines a device driver as a program that allows a system to interface with hardware devices. It discusses how device drivers act as translators between operating systems, applications, and hardware devices. The document also describes the purpose of device drivers, how they operate in privileged mode, and how file abstraction is used for devices. It provides examples of shift and logic operators that are commonly used when writing low-level code like device drivers.
Smart phone application

This document describes a proposed smart phone application for home automation. The application would allow users to remotely control home appliances and monitor the home environment using an Android smart phone. The proposed system uses an embedded microcontroller, sensors, relays, a GSM modem and serial communication to interface with the smart phone application. The application would provide a user-friendly GUI to allow monitoring and control of devices from the phone. The system aims to provide mobility, accessibility and remote control capabilities compared to existing PC-based home automation systems.
BASIC COMPUTER PERIPHERALS/DEVICES/SYSTEMS

Computer malfunctions can range from a minor setting that is incorrect, to spyware, viruses, and as far as replacing hardware and an entire operating system.
While computer hardware configurations vary widely, a "Computer OEM & Repair" technician will work with five general categories of hardware; desktop computers, laptops, servers, computer clusters and smartphones / mobile computing. Technicians also work with and occasionally repair a range of peripherals, including input devices (like keyboards, mice, and scanners), output devices (like displays, printers, and speakers), and data storage devices such as internal and external hard drives and disk arrays. Technicians involved in system administration might also work with networking hardware, including routers, switches, fiber optics, and wireless networks. OEM= Original Equipment Manufacturer.
6 profiling tools

The document provides information on performance monitoring and analysis tools from Intel, including the Intel VTune Amplifier XE, Intel Performance Counter Monitor (PCM), and guidance on using them. It outlines a process for identifying performance bottlenecks including finding hotspots, determining efficiency, and identifying the underlying architectural issues. Potential issues discussed include cache misses, data access problems, allocation stalls, and branch mispredictions. The document also provides usage examples and resources for further information.
Mw training slide

This document discusses troubleshooting of OptiX RTN 600 equipment. It covers objectives of troubleshooting preparation, ideas and methods, and examples of classified troubleshooting situations. Common troubleshooting methods discussed include alarm and performance analysis, loopback, replacement, configuration data analysis, configuration modification, using testing instruments, and experience-based rules of thumb. Typical troubleshooting sequences are also presented, beginning with excluding external issues and locating faults to a single network element or board. Finally, examples of traffic interruptions, wrong configurations, and bit errors are analyzed.
Troubleshooting & Tools

The document discusses various computer hardware troubleshooting tools, including in-circuit emulators, logic state/timing analyzers, digital multimeters, and cathode-ray oscilloscopes. It provides details on what each tool is used for and how it functions. In-circuit emulators are used to debug software on embedded systems by allowing observation and alteration of the system. Logic analyzers capture and display digital signals and can trigger on patterns. Digital multimeters combine voltage, current and resistance measurements. Cathode-ray oscilloscopes provide time and amplitude measurements of voltage signals.
UserManual43.pdf

The document is the user manual for version 4.3 of the Hydrologic Modeling System (HEC-HMS), a hydrologic modeling application developed by the Hydrologic Engineering Center (HEC). HEC-HMS is designed to simulate precipitation-runoff processes in dendritic watershed systems. The 640-page manual describes the program's capabilities, components, data requirements, and procedures for constructing and running hydrologic models.
PLUG : Presentation Layer Universal Generator

PLUG is a presentation layer universal generator that provides automatic code generation from specifications. It uses object-oriented design and handles heterogeneous programming languages and hardware. PLUG can generate stubs for API usage and message coders for object message passing between distributed applications.
Peripheral devices2.pptx

- A peripheral device is an internal or external device that connects directly to a computer but is not essential to its primary function of computing. Peripherals can be input devices, output devices, or storage devices.
- Peripheral devices include items like mice, keyboards, monitors, printers, scanners, webcams, and more. They can be either external devices that connect to the outside of a computer or internal devices installed inside the computer case.
- Peripheral devices help users access and utilize a computer's functionality. Some devices like modems can serve as both input and output peripherals.
511718784-maintain-inventory-of-equipment-software-and-documentation.pptx

The document provides information on maintaining inventories of equipment, software, and documentation at Mary Help College. It discusses maintaining accurate hardware and software inventories, including defining inventory, the purposes of inventory, best practices for inventory management, and examples of inventory forms for hardware like computers, monitors, keyboards and mice. Maintaining proper inventories is important for tracking assets, replacing equipment, and ensuring software licensing compliance.
BRKDCT-3144 - Advanced - Troubleshooting Cisco Nexus 7000 Series Switches (20...

The document describes a Cisco Live 2014 presentation on advanced troubleshooting of Cisco Nexus 7000 series switches. It includes an agenda that covers system, data plane, and control plane troubleshooting over 120 minutes. It also discusses strategies, tools, and techniques for troubleshooting these different areas. Some key tools highlighted include show commands, scripts like SystemCheck, packet capture with ELAME, and analyzing logs. The presentation provides guidance on approaches for each troubleshooting area and highlights the extensive logging capabilities of NX-OS.
Process

The document discusses processes and operating systems. It defines a process as a program under execution and describes the different states a process can be in such as ready, running, waiting, and terminated. It explains that there are two types of processes - active processes that are under execution and passive processes that are not currently running. The summary also mentions that a process control block contains information about each process like its identifier, state, priority and memory pointers.
Simens plc training. simatic working-with-step-7

This document provides an introduction to using STEP 7 software to program SIMATIC S7 programmable logic controllers. It outlines the basic procedure for creating a program using STEP 7, which involves combining hardware configuration with software programming. Practical exercises in subsequent chapters will demonstrate programming in Ladder Logic, Statement List, and Function Block Diagram to address inputs and outputs using basic binary logic operations.
V center operations enterprise standalone technical presentation

Download & Share Technology
Presentations http://ouo.io/XKLUj
Student Guide & Best http://ouo.io/8u1RP
More Related Content
What's hot
Shahzad Khan

This document summarizes an individual's experience and qualifications providing machine condition monitoring and preventative maintenance services. They have 1.5 years experience collecting and analyzing vibration and operational data using various online and offline monitoring systems and software. Their responsibilities include routine condition monitoring of rotating equipment using vibration analysis, thermography, and ultrasound inspection. They also support troubleshooting, failure investigations, field balancing, and laser alignment activities.
Medical Device Software

Morgunfundur um markaðskröfur og staðla fyrir lækningavöru og stoðkerfi á heilbrigðissviði 8. mars 2012 - Garðar Þorvarðsson
V&V Considerations In Implementing IEC61508-3

This document discusses verification and validation considerations for implementing IEC 61508-3. It begins with an overview of Oak Systems, a specialist in software verification and validation services. It then provides an overview of IEC 61508-3 and verification and validation (V&V). The rest of the document discusses the IEC 61508 safety lifecycle, key terms and definitions, safety integrity levels, development activities and tools to support V&V, software verification techniques, functional safety assessment, and tables relating technique rigor to safety integrity levels. It concludes that IEC 61508 alone may not be sufficient for all applications and other standards like UL1998 may also need to be considered.
QAdvis - software risk management based on IEC/ISO 62304

This document provides an overview of risk management for medical device software as outlined in IEC 62304. It discusses:
1) IEC 62304 calls for risk management activities throughout the entire software development lifecycle. This includes identification, analysis, evaluation, control and monitoring of risks.
2) Both quantitative and qualitative techniques can be used for risk analysis, such as FMECA, FTA, HAZOP. Requirement-based and risk-based verification strategies are also expected.
3) Effective risk management relies on good software engineering practices and processes. It aims to regulate verification efforts to balance productivity and compliance.
8. operational risk management

This document discusses operational risk management and system safety. It defines key terms like system safety, hazard probability, and hazard severity. It describes the system safety process which involves defining objectives, hazard identification, analysis, risk evaluation, and hazard controls. It also discusses failure modes and effects analysis. Overall, the document provides an overview of operational risk management processes like identifying hazards, assessing and analyzing risks, making control decisions, and supervising risk controls. It discusses how to make risk management decisions and defines terms like identified risk and acceptable risk.
Hardware review rubrics

This rubric evaluates a student's performance on a computer repair and troubleshooting assessment with 5 stations: 1) identifying computer components, 2) identifying tools, 3) more component identification, 4) assembling a computer, and 5) troubleshooting hardware issues on 4 computers. The student can earn up to 125 points total by correctly completing tasks at each station and demonstrating appropriate workplace behavior and safety. Their score will be assessed in categories like below average, average, good, or excellent.
Reliability Instrumented System | Arrelic Insights 

An approach that strays from the conventional, coupled with
consistency, enables us to contribute to the company's overall
growth and success.
This Insights talks about RIS Process and applications
Malewareanalysis 

This document discusses malware analysis. It covers types of malware like viruses, worms, and trojans. It describes how malware can infect hosts by overwriting, prepending, appending, or using packers. Methods of malware detection like signatures, heuristics, checksums, and sandboxes are presented. The goals, types, and tools of malware analysis are outlined along with simulation steps and conclusions.
What's hot (8)
QAdvis - software risk management based on IEC/ISO 62304

QAdvis - software risk management based on IEC/ISO 62304
Reliability Instrumented System | Arrelic Insights 

Reliability Instrumented System | Arrelic Insights
Similar to Common Areas of Data Breach
DeviceDriverNov18.ppt

This document provides an overview of device drivers. It defines a device driver as a program that allows a system to interface with hardware devices. It discusses how device drivers act as translators between operating systems, applications, and hardware devices. The document also describes the purpose of device drivers, how they operate in privileged mode, and how file abstraction is used for devices. It provides examples of shift and logic operators that are commonly used when writing low-level code like device drivers.
Smart phone application

This document describes a proposed smart phone application for home automation. The application would allow users to remotely control home appliances and monitor the home environment using an Android smart phone. The proposed system uses an embedded microcontroller, sensors, relays, a GSM modem and serial communication to interface with the smart phone application. The application would provide a user-friendly GUI to allow monitoring and control of devices from the phone. The system aims to provide mobility, accessibility and remote control capabilities compared to existing PC-based home automation systems.
BASIC COMPUTER PERIPHERALS/DEVICES/SYSTEMS

Computer malfunctions can range from a minor setting that is incorrect, to spyware, viruses, and as far as replacing hardware and an entire operating system.
While computer hardware configurations vary widely, a "Computer OEM & Repair" technician will work with five general categories of hardware; desktop computers, laptops, servers, computer clusters and smartphones / mobile computing. Technicians also work with and occasionally repair a range of peripherals, including input devices (like keyboards, mice, and scanners), output devices (like displays, printers, and speakers), and data storage devices such as internal and external hard drives and disk arrays. Technicians involved in system administration might also work with networking hardware, including routers, switches, fiber optics, and wireless networks. OEM= Original Equipment Manufacturer.
6 profiling tools

The document provides information on performance monitoring and analysis tools from Intel, including the Intel VTune Amplifier XE, Intel Performance Counter Monitor (PCM), and guidance on using them. It outlines a process for identifying performance bottlenecks including finding hotspots, determining efficiency, and identifying the underlying architectural issues. Potential issues discussed include cache misses, data access problems, allocation stalls, and branch mispredictions. The document also provides usage examples and resources for further information.
Mw training slide

This document discusses troubleshooting of OptiX RTN 600 equipment. It covers objectives of troubleshooting preparation, ideas and methods, and examples of classified troubleshooting situations. Common troubleshooting methods discussed include alarm and performance analysis, loopback, replacement, configuration data analysis, configuration modification, using testing instruments, and experience-based rules of thumb. Typical troubleshooting sequences are also presented, beginning with excluding external issues and locating faults to a single network element or board. Finally, examples of traffic interruptions, wrong configurations, and bit errors are analyzed.
Troubleshooting & Tools

The document discusses various computer hardware troubleshooting tools, including in-circuit emulators, logic state/timing analyzers, digital multimeters, and cathode-ray oscilloscopes. It provides details on what each tool is used for and how it functions. In-circuit emulators are used to debug software on embedded systems by allowing observation and alteration of the system. Logic analyzers capture and display digital signals and can trigger on patterns. Digital multimeters combine voltage, current and resistance measurements. Cathode-ray oscilloscopes provide time and amplitude measurements of voltage signals.
UserManual43.pdf

The document is the user manual for version 4.3 of the Hydrologic Modeling System (HEC-HMS), a hydrologic modeling application developed by the Hydrologic Engineering Center (HEC). HEC-HMS is designed to simulate precipitation-runoff processes in dendritic watershed systems. The 640-page manual describes the program's capabilities, components, data requirements, and procedures for constructing and running hydrologic models.
PLUG : Presentation Layer Universal Generator

PLUG is a presentation layer universal generator that provides automatic code generation from specifications. It uses object-oriented design and handles heterogeneous programming languages and hardware. PLUG can generate stubs for API usage and message coders for object message passing between distributed applications.
Peripheral devices2.pptx

- A peripheral device is an internal or external device that connects directly to a computer but is not essential to its primary function of computing. Peripherals can be input devices, output devices, or storage devices.
- Peripheral devices include items like mice, keyboards, monitors, printers, scanners, webcams, and more. They can be either external devices that connect to the outside of a computer or internal devices installed inside the computer case.
- Peripheral devices help users access and utilize a computer's functionality. Some devices like modems can serve as both input and output peripherals.
511718784-maintain-inventory-of-equipment-software-and-documentation.pptx

The document provides information on maintaining inventories of equipment, software, and documentation at Mary Help College. It discusses maintaining accurate hardware and software inventories, including defining inventory, the purposes of inventory, best practices for inventory management, and examples of inventory forms for hardware like computers, monitors, keyboards and mice. Maintaining proper inventories is important for tracking assets, replacing equipment, and ensuring software licensing compliance.
BRKDCT-3144 - Advanced - Troubleshooting Cisco Nexus 7000 Series Switches (20...

The document describes a Cisco Live 2014 presentation on advanced troubleshooting of Cisco Nexus 7000 series switches. It includes an agenda that covers system, data plane, and control plane troubleshooting over 120 minutes. It also discusses strategies, tools, and techniques for troubleshooting these different areas. Some key tools highlighted include show commands, scripts like SystemCheck, packet capture with ELAME, and analyzing logs. The presentation provides guidance on approaches for each troubleshooting area and highlights the extensive logging capabilities of NX-OS.
Process

The document discusses processes and operating systems. It defines a process as a program under execution and describes the different states a process can be in such as ready, running, waiting, and terminated. It explains that there are two types of processes - active processes that are under execution and passive processes that are not currently running. The summary also mentions that a process control block contains information about each process like its identifier, state, priority and memory pointers.
Simens plc training. simatic working-with-step-7

This document provides an introduction to using STEP 7 software to program SIMATIC S7 programmable logic controllers. It outlines the basic procedure for creating a program using STEP 7, which involves combining hardware configuration with software programming. Practical exercises in subsequent chapters will demonstrate programming in Ladder Logic, Statement List, and Function Block Diagram to address inputs and outputs using basic binary logic operations.
V center operations enterprise standalone technical presentation

Download & Share Technology
Presentations http://ouo.io/XKLUj
Student Guide & Best http://ouo.io/8u1RP
.conf2011: Web Analytics Throwdown: with NPR and Intuit

Splunk for Web Intelligence? Why not! This session provides a plain-english tour that shows how NPR uses Splunk to track audio and video traffic across our web sites and digital apps (Android, iPhone, etc.). Then Intuit will share how they capture greater insight into visitor sessions and answer questions traditional web analytics tools can’t provide. Intuit will cover a variety of use cases, taking each from the raw data through Splunk “under-the-hood” to the strategic questions and answers.
A Case Study of the Capital One Data Breach

Are existing compliance requirements sufficient to prevent data breaches? This session will provide a technical assessment of the 2019 Capital One data breach, illustrating the technical modus operandi of the attack and identify related compliance requirements based on the NIST Cybersecurity Framework. Attendees will learn the unexpected impact of corporate culture on overall cyber security posture.
This talk was presented at RSA Conference 2021 (Session RMG-T15) on May 18, 2021.
Original paper available for download at SSRN: Novaes Neto, Nelson and Madnick, Stuart E. and Moraes G. de Paula, Anchises and Malara Borges, Natasha, A Case Study of the Capital One Data Breach (28/04/2020). https://ssrn.com/abstract=3570138
Introduction to EMBEDDED SYSTEM.pdf

The document provides an overview of embedded system design, including:
1. The Apollo Guidance Computer was one of the first modern embedded systems and enabled the moon landings by automatically controlling the navigational functions of the Apollo spacecraft.
2. Embedded systems can be classified as small, medium, or sophisticated based on their hardware and software complexity. Common programming tools for each level are also discussed.
3. Major applications of embedded systems include consumer electronics, industrial equipment, automotive systems, networking devices, and medical equipment. Embedded systems typically perform functions like data collection, processing, communication, monitoring and control.
Permission Driven Malware Detection using Machine Learning

This document summarizes research analyzing the correlation between Android application permissions and machine learning algorithms for malware detection. The research collected data on 398 applications and their 331 permission attributes. Various machine learning classification algorithms were analyzed to determine the best for detecting malware based on permissions requested. The algorithms analyzed included Naive Bayes, Ada Boost, Multi-Class Classifier, Random Tree, Random Forest, and J48. Random Forest had the highest accuracy rate of 93.2% for malware detection based on permissions. The research aims to help users identify potentially malicious applications by their requested permissions before installing them.
Marko Gargenta_Remixing android

The document provides instructions for customizing and building a new Android device called Marakana Alpha. It describes generating custom platform signing keys, building the initial device code, and adding optional components like a custom kernel. Key steps include registering the new device in the build system, generating signing keys, compiling the code, and running it on an emulator or device. The goal is to remix Android by building a customized version with new features while maintaining compatibility.
Forti gate troubleshooting_guide_v0.10

The document provides troubleshooting guidance for FortiGate devices. It begins with requirements for opening support tickets, such as clearly describing the problem and network configuration. It then gives initial troubleshooting steps for issues like IPsec VPNs, high availability (HA), and traffic blocking. Debugging commands are suggested to gather key information for issues with interfaces, anti-spam, web filtering, and the FortiAnalyzer Security Appliance Extension (FSAE).
Similar to Common Areas of Data Breach (20)
511718784-maintain-inventory-of-equipment-software-and-documentation.pptx

511718784-maintain-inventory-of-equipment-software-and-documentation.pptx
BRKDCT-3144 - Advanced - Troubleshooting Cisco Nexus 7000 Series Switches (20...

BRKDCT-3144 - Advanced - Troubleshooting Cisco Nexus 7000 Series Switches (20...
V center operations enterprise standalone technical presentation

V center operations enterprise standalone technical presentation
.conf2011: Web Analytics Throwdown: with NPR and Intuit

.conf2011: Web Analytics Throwdown: with NPR and Intuit
Permission Driven Malware Detection using Machine Learning

Permission Driven Malware Detection using Machine Learning
More from William Kiss
North America's Electrical Grid @ Risk v1.3

The document discusses three main attack vectors that could disable the North American electric grid:
1) Kinetic attacks using weapons like AK-47s to destroy transformers at electric substations, preventing power transfer.
2) An electromagnetic pulse attack using a nuclear weapon detonated in the atmosphere.
3) A severe solar storm known as a Carrington event, emitting a coronal mass ejection capable of frying transformers and electronics across the grid. Protecting critical infrastructure like extra high voltage transformers is vital to preventing long-term blackouts from these threats.
The Silver Bullet of Cyber Security v1.1

While there is no single solution to prevent cyber attacks, there are basic steps that companies often overlook that leave them vulnerable. These include failing to identify where sensitive data is stored and located, whether backups exist and have been tested, and what would happen if this data was stolen or encrypted. It is important to retain a cybersecurity consultant to assess strengths, weaknesses, opportunities and threats; be proactive by selecting an incident response team before an attack; and continuously test and revise response plans to help secure an organization's critical data and systems.
Ali

Muhammad Ali met the photographer in Chicago in the 1980s at a hotel they were both staying at. When the photographer told the front desk he wanted to shake "The Champ's" hand, Ali graciously extended his right hand in friendship. The photographer was amazed by the size of Ali's hands, with his index finger alone being over an inch thick and longer than any of the photographer's fingers. Though a giant of a man, Ali gently grasped the photographer's hands with both of his own as the photographer thanked him for the opportunity to meet. The photographer has always remembered this kind meeting and wishes Ali can now rest in peace.
Your Cyber Security Picture - A Starting Point

This document outlines an 8 step process for conducting an initial cyber security assessment of a company: 1) Evaluate the company website and create a computer network diagram, 2) Review existing cyber liability insurance, 3) Provide staff cyber awareness training, 4) Scan for vulnerabilities across all internet connected devices, 5) Generate a vulnerability report and prioritize issues, 6) Test custom software and reports from vendors, 7) Create a vulnerability remediation plan, 8) Develop a cyber security incident response plan including data loss prevention.
One Way Hackers Steal Data From Your Systems

The document outlines the typical steps, known as the "kill chain", that an attacker takes during an Advanced Persistent Threat (APT). The kill chain involves 9 steps: 1) reconnaissance of the target, 2) weaponization of exploits, 3) payload delivery, 4) installation of malware, 5) malware contacting a command and control server, 6) lateral movement within the network, 7) expanding compromise to other areas, 8) completing the intended mission such as data exfiltration, and 9) finishing the attack by destroying data and covering tracks. The goal is to stealthily compromise networks and systems over an extended period to acquire sensitive information.
Cyber Security Weakest Links

This document discusses cyber security and lists several aspects that need protection including personnel, hardware, operating systems, applications, utilities, browsers, user identity validation, interfaces and encryption. It asks the reader to identify their weakest link in cyber security.
Cyber Attack Phase Progression

The document outlines the typical 4 phase progression of a cyber attack: 1) disrupt business and prevent access, 2) access credentials and steal data, 3) embed malware on industrial control systems and devices, and 4) directly damage or destroy infrastructure through computer networks or sell stolen information. It notes how cyber attacks have evolved over the decades to cause greater damage and disruption.
More from William Kiss (8)
Common Areas of Data Breach
- 1. Common Areas ALL l/P Add ressed Hardware Devices lnternal / External; Owned / Managed of Breach Risk,,, Networked Devices a.' Dimver --8 . t l @ , J ,.!::&!-;€g;&. t*;-;.t 1:j -11:: e*:% F' €=*re Prioritize 81re Aasets q:=====7 r€======7 T Vulnerability ,r:: F=q Management *=:g ...: , '-' INVENTORY ALL ITEMS: Hardware & Software Operating System(s) Application Software Utilities Life Cycle -*;., t' I Ate*e l 1i1' I 1.. l---f3h f-::.V i.alw,t,..i llt,.l.. ' ..: .1,, 1 1':r' ::-;i V M. Life Cycle Frequency Determined By Delta & Frequency Required By Your Standards Policy Data Breach I ncident Response P I an What's your written plan in the event of a Data Breach? Have you identified the roles each employee must play in a response? Have you had a Data Breach Drill in the past Quarter, 6-Months, Year? ALL 3'o Pa rty Databases & Payment Porta I s Ensure ALL External Systems & Software have been remediated for ALL Known Vulnerabilities Letter of Certification from External Vendors Web / e-Mail Servers Network Servers Laptops / Notebooks Multi-Function Machines &Routers: Wired & Wireless Credit Card Reader Smart Phone Other End-Point Devices Firewalls Copyright@ 2015 Global 1 Research & Deveiopment, Ltd, ALL Rights Reserved
