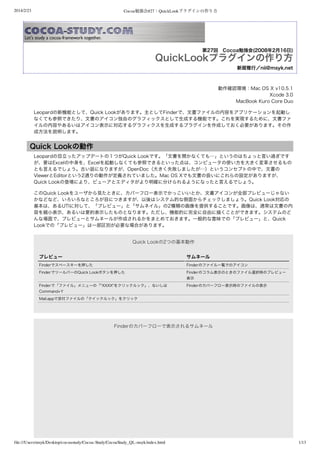
Cocoa勉強会#27-QuickLookプラグインの作り方
•
0 likes•434 views
The document is a log containing repeated entries of a date, topic headings for "Cocoa", "QuickLook", and a file path and page number. It does not contain any other substantive information in the entries or overall.
Report
Share
Report
Share
Download to read offline
Recommended
Cocoa勉強会#23-カスタムシートとModality

The document discusses code for creating and managing a custom sheet window in a Cocoa application. It defines an NSDocument subclass with methods for opening and closing the sheet, as well as handling termination events. The open method uses beginSheet:modalForWindow:modalDelegate:didEndSelector:contextInfo: to display the sheet, while close uses endSheet:. The terminate method closes any open sheets before quitting the application.
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including:
1. Websites related to e-learning projects, course design, and learning management systems
2. Links to blogs and websites about word processors, physics equations, and astronomy
3. Links to pages about holograms, laser interference patterns, and shopping applications using barcodes.
Design Against ATM Crime

The document describes a project between Design Against Crime Camden Council and MA Communication Design students to address overcrowding on certain London Underground stations. The students used statistical information to map out walking routes between targeted congested stations and nearby less congested stations to encourage commuters to walk between stations to relieve tube congestion and improve health. The students designed maps showing the quickest and most pleasant walking routes to help commuters choose walking over taking the tube.
Shark breaching in Cape Town

Great white sharks are apex predators that can breach out of the water at speeds up to 40 mph to attack seals. Seal Island near Cape Town is home to over 60,000 seals and is frequented by a dozen great whites, making it a place where shark breaching occurs commonly as the sharks hunt the seals. Witnessing shark breaching in their natural habitat from the safety of a shark cage is an opportunity offered by tour companies like Extreme Scene, with trips available to Seal Island in False Bay or to Gansbaai, known as the Shark Capital of the World.
32 Ways a Digital Marketing Consultant Can Help Grow Your Business

How can a digital marketing consultant help your business? In this resource we'll count the ways. 24 additional marketing resources are bundled for free.
Cocoa勉強会#28-OpenSSLで暗号化したファイルを復号する

This document discusses OpenSSL and encryption/decryption using the Blowfish cipher. It shows examples of encrypting a plaintext string using OpenSSL's bf utility with different keys and initialization vectors. It also shows decrypting an encrypted file back to plaintext. Finally, it includes Objective-C code to decrypt data from a file encrypted with Blowfish using the OpenSSL EVP API.
Recommended
Cocoa勉強会#23-カスタムシートとModality

The document discusses code for creating and managing a custom sheet window in a Cocoa application. It defines an NSDocument subclass with methods for opening and closing the sheet, as well as handling termination events. The open method uses beginSheet:modalForWindow:modalDelegate:didEndSelector:contextInfo: to display the sheet, while close uses endSheet:. The terminate method closes any open sheets before quitting the application.
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including:
1. Websites related to e-learning projects, course design, and learning management systems
2. Links to blogs and websites about word processors, physics equations, and astronomy
3. Links to pages about holograms, laser interference patterns, and shopping applications using barcodes.
Design Against ATM Crime

The document describes a project between Design Against Crime Camden Council and MA Communication Design students to address overcrowding on certain London Underground stations. The students used statistical information to map out walking routes between targeted congested stations and nearby less congested stations to encourage commuters to walk between stations to relieve tube congestion and improve health. The students designed maps showing the quickest and most pleasant walking routes to help commuters choose walking over taking the tube.
Shark breaching in Cape Town

Great white sharks are apex predators that can breach out of the water at speeds up to 40 mph to attack seals. Seal Island near Cape Town is home to over 60,000 seals and is frequented by a dozen great whites, making it a place where shark breaching occurs commonly as the sharks hunt the seals. Witnessing shark breaching in their natural habitat from the safety of a shark cage is an opportunity offered by tour companies like Extreme Scene, with trips available to Seal Island in False Bay or to Gansbaai, known as the Shark Capital of the World.
32 Ways a Digital Marketing Consultant Can Help Grow Your Business

How can a digital marketing consultant help your business? In this resource we'll count the ways. 24 additional marketing resources are bundled for free.
Cocoa勉強会#28-OpenSSLで暗号化したファイルを復号する

This document discusses OpenSSL and encryption/decryption using the Blowfish cipher. It shows examples of encrypting a plaintext string using OpenSSL's bf utility with different keys and initialization vectors. It also shows decrypting an encrypted file back to plaintext. Finally, it includes Objective-C code to decrypt data from a file encrypted with Blowfish using the OpenSSL EVP API.
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including: e-learning, online courses, Linux, word processors, physics formulas, astronomy, computer science, shopping applications, barcode scanning, robotics, and game development. Many of the links are broken or outdated. The document seems to be collecting various online references but lacks context or overall organization.
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including: project approaches, e-learning, Linux, word processors, physics equations, astronomy, computer science topics like computer generated holograms, shopping applications using barcodes, robotic locomotion, mobile applications, electronics connectors, and game development. Many of the links are broken and no longer function or the websites no longer exist. The document seems to be collecting various online references and resources but without much organization or context around the various topics.
Jalt2015

This document summarizes an action research project on using audio-enabled weblogs (blogs) in university EFL writing classes in Japan. It discusses using blogs and text-to-speech technology in writing projects from 2006 to 2008. It also analyzes student feedback on the blog and online quiz projects, and explores the feasibility of different tasks and class sizes with blogcasting. The document concludes that combining blogs with RSS mixing and text-to-speech can enhance language learning, but class size and task complexity must be considered.
Why is my build times so long?

How do you deal with ever increasing build times and collaborate more without sacrificing on collaborating? That is what this talk is about.
Konvensyen Webmaster Negeri Sabah 2013

This document contains the slides from a presentation on web development with open source technologies given by Edham Arief Dawillah. It introduces Edham and his background in web development using various open source tools. The presentation covered current popular programming languages, frameworks, content management systems and front-end technologies. It emphasized that open source allows for freedom, community support and lower costs. The slides provided information on tools like PHP, Ruby, Python, Java, CakePHP, Ruby on Rails, WordPress, Drupal and more.
Ryan Jarvinen Open Shift Talk @ Postgres Open 2013

The document discusses writing portable PostgreSQL applications for the open cloud. It covers open cloud platforms like OpenStack that avoid lock-in, and platforms like OpenShift that provide portable PostgreSQL applications using cartridges and scaling hooks. Examples are given of simple applications like a TODO app using Flask, SQLAlchemy and PostgreSQL that can be easily deployed to OpenShift.
SWORD Stories

Slides for my talk on SWORD for learning materials repositories, including live demos (not shown here- will include Jing video captures later). From the 2009 Intrallect Conference, 25-26 March 2009.
再考!スマートフォンサイト定番UI 2015 05-14

The document appears to be a series of slides or pages from a PDF document dated May 14, 2015. Each slide/page is numbered but contains no other discernible text, content or information. Therefore, the document provides no summarizable information in 3 sentences or less.
Docker security - TASK Jan 2016

Ricardo Gerardi and I had the privilege of delivering an introductory talk on Docker & Docker Security to the Toronto Area Security Klatch (TASK) this week. Here are the slides.
IBM Bluemix Hackathon Accelerator

Become an hackathon champion with this useful collection of tutorials and examples with links to source code and videos.
Get ready for the next hackathon with IBM Bluemix.
haven't got enough time for sleep

The document discusses starting something and provides instructions on how to access a local file path on a computer. It contains 8 pages of text but no other discernible information could be summarized from the content.
MySQL Shell : the best DBA tool ?

Presentation about how to extend MySQL Shell for DBA daily tasks and Innotop like processlist overview.
This presentation was delivered during the pre-FOSDEM MySQL Day on Feb 1st 2019
Let fleat2019-0807-2

Web-Enhanced Language Learning in EFL: Web 2.0 technologies for Weblogs, Text to Speech and eBooks and Audiobooks
Let fleat2019-0807-1

Web-Enhanced Language Learning in EFL: Web 2.0 technologies for Weblogs, Text to Speech and eBooks and audiobooks
Android utilities

This document provides a summary of various Android utilities including tools for app debugging, memory leak detection, Javadoc generation, diagram generation, project overview, bug tracking, app demonstration, driver installation, search, POJO generation, quality analysis, semantic versioning, Proguard, project configuration, and logo credits. Each utility includes a brief description and link to its GitHub page or website.
Open Access publikācijas (2010. gada oktobris)

The document summarizes several information sources about open access (OA) publications and news:
1) It provides brief descriptions and web addresses for OA resources from organizations like EIFL, OAD, and news sources on recent developments in the OA movement.
2) It also lists events like Open Access Week from 2009 and 2010, with links to information about the events.
3) Sources of OA bibliographies, journals, and reports on topics like OA models and policies are referenced along with their web addresses.
Techs in draaft 1 5 process

The document lists the various technologies used in the DRAFT 1/2/3/4/5 process, including Mac, QuickTime, YouTube, Sony Handycam, iMovie, Microsoft PowerPoint, USB stick, Freesound.org, Blogger, SlideShare, and Wikipedia.
Java User Group Cologne

Karl Heinz Marbaise gives a presentation on Maven that covers:
1) The history and roadmap of Maven, including versions from 1.X to the current 3.X and planned future versions.
2) The Maven ecosystem, including core Maven, plugins, shared components, and projects from Apache, MojoHaus, and Codehaus-plexus.
3) Ways to optimize Maven build performance such as enabling parallelization.
Kg20160217 2013-1

Action research on
CALL and Web 2.0 technologies:
in WELL (Web Enhanced Language Learning),
and CMT (Computer Managed Testing)
in university EFL classes
Presentation on the retiring year of 2016, from 1975.
KG20160217 2013-1
Framework Enabling End-Users to Maintain Web Applications (ICICWS2015)

The document describes a study evaluating whether end-users can maintain web applications using a declarative web application framework called INTER-Mediator. The framework allows users to describe web pages and database queries using key-value pairs rather than imperative programming. An experiment found that while some subjects failed to learn the framework within 2 hours, others scored 42-93% on an exam after studying for over 45 minutes, indicating they successfully learned to develop with the framework in a short period of time.
More Related Content
Similar to Cocoa勉強会#27-QuickLookプラグインの作り方
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including: e-learning, online courses, Linux, word processors, physics formulas, astronomy, computer science, shopping applications, barcode scanning, robotics, and game development. Many of the links are broken or outdated. The document seems to be collecting various online references but lacks context or overall organization.
โครงงานคอมพิวเตอร์606

This document contains a list of various URLs and web links on different topics including: project approaches, e-learning, Linux, word processors, physics equations, astronomy, computer science topics like computer generated holograms, shopping applications using barcodes, robotic locomotion, mobile applications, electronics connectors, and game development. Many of the links are broken and no longer function or the websites no longer exist. The document seems to be collecting various online references and resources but without much organization or context around the various topics.
Jalt2015

This document summarizes an action research project on using audio-enabled weblogs (blogs) in university EFL writing classes in Japan. It discusses using blogs and text-to-speech technology in writing projects from 2006 to 2008. It also analyzes student feedback on the blog and online quiz projects, and explores the feasibility of different tasks and class sizes with blogcasting. The document concludes that combining blogs with RSS mixing and text-to-speech can enhance language learning, but class size and task complexity must be considered.
Why is my build times so long?

How do you deal with ever increasing build times and collaborate more without sacrificing on collaborating? That is what this talk is about.
Konvensyen Webmaster Negeri Sabah 2013

This document contains the slides from a presentation on web development with open source technologies given by Edham Arief Dawillah. It introduces Edham and his background in web development using various open source tools. The presentation covered current popular programming languages, frameworks, content management systems and front-end technologies. It emphasized that open source allows for freedom, community support and lower costs. The slides provided information on tools like PHP, Ruby, Python, Java, CakePHP, Ruby on Rails, WordPress, Drupal and more.
Ryan Jarvinen Open Shift Talk @ Postgres Open 2013

The document discusses writing portable PostgreSQL applications for the open cloud. It covers open cloud platforms like OpenStack that avoid lock-in, and platforms like OpenShift that provide portable PostgreSQL applications using cartridges and scaling hooks. Examples are given of simple applications like a TODO app using Flask, SQLAlchemy and PostgreSQL that can be easily deployed to OpenShift.
SWORD Stories

Slides for my talk on SWORD for learning materials repositories, including live demos (not shown here- will include Jing video captures later). From the 2009 Intrallect Conference, 25-26 March 2009.
再考!スマートフォンサイト定番UI 2015 05-14

The document appears to be a series of slides or pages from a PDF document dated May 14, 2015. Each slide/page is numbered but contains no other discernible text, content or information. Therefore, the document provides no summarizable information in 3 sentences or less.
Docker security - TASK Jan 2016

Ricardo Gerardi and I had the privilege of delivering an introductory talk on Docker & Docker Security to the Toronto Area Security Klatch (TASK) this week. Here are the slides.
IBM Bluemix Hackathon Accelerator

Become an hackathon champion with this useful collection of tutorials and examples with links to source code and videos.
Get ready for the next hackathon with IBM Bluemix.
haven't got enough time for sleep

The document discusses starting something and provides instructions on how to access a local file path on a computer. It contains 8 pages of text but no other discernible information could be summarized from the content.
MySQL Shell : the best DBA tool ?

Presentation about how to extend MySQL Shell for DBA daily tasks and Innotop like processlist overview.
This presentation was delivered during the pre-FOSDEM MySQL Day on Feb 1st 2019
Let fleat2019-0807-2

Web-Enhanced Language Learning in EFL: Web 2.0 technologies for Weblogs, Text to Speech and eBooks and Audiobooks
Let fleat2019-0807-1

Web-Enhanced Language Learning in EFL: Web 2.0 technologies for Weblogs, Text to Speech and eBooks and audiobooks
Android utilities

This document provides a summary of various Android utilities including tools for app debugging, memory leak detection, Javadoc generation, diagram generation, project overview, bug tracking, app demonstration, driver installation, search, POJO generation, quality analysis, semantic versioning, Proguard, project configuration, and logo credits. Each utility includes a brief description and link to its GitHub page or website.
Open Access publikācijas (2010. gada oktobris)

The document summarizes several information sources about open access (OA) publications and news:
1) It provides brief descriptions and web addresses for OA resources from organizations like EIFL, OAD, and news sources on recent developments in the OA movement.
2) It also lists events like Open Access Week from 2009 and 2010, with links to information about the events.
3) Sources of OA bibliographies, journals, and reports on topics like OA models and policies are referenced along with their web addresses.
Techs in draaft 1 5 process

The document lists the various technologies used in the DRAFT 1/2/3/4/5 process, including Mac, QuickTime, YouTube, Sony Handycam, iMovie, Microsoft PowerPoint, USB stick, Freesound.org, Blogger, SlideShare, and Wikipedia.
Java User Group Cologne

Karl Heinz Marbaise gives a presentation on Maven that covers:
1) The history and roadmap of Maven, including versions from 1.X to the current 3.X and planned future versions.
2) The Maven ecosystem, including core Maven, plugins, shared components, and projects from Apache, MojoHaus, and Codehaus-plexus.
3) Ways to optimize Maven build performance such as enabling parallelization.
Kg20160217 2013-1

Action research on
CALL and Web 2.0 technologies:
in WELL (Web Enhanced Language Learning),
and CMT (Computer Managed Testing)
in university EFL classes
Presentation on the retiring year of 2016, from 1975.
KG20160217 2013-1
Similar to Cocoa勉強会#27-QuickLookプラグインの作り方 (19)
Ryan Jarvinen Open Shift Talk @ Postgres Open 2013

Ryan Jarvinen Open Shift Talk @ Postgres Open 2013
More from Masayuki Nii
Framework Enabling End-Users to Maintain Web Applications (ICICWS2015)

The document describes a study evaluating whether end-users can maintain web applications using a declarative web application framework called INTER-Mediator. The framework allows users to describe web pages and database queries using key-value pairs rather than imperative programming. An experiment found that while some subjects failed to learn the framework within 2 hours, others scored 42-93% on an exam after studying for over 45 minutes, indicating they successfully learned to develop with the framework in a short period of time.
Cocoa勉強会23-識別情報の変換〜文字エンコードとデータタイプ

The document discusses methods for getting the preferred MIME type for a file from its extension or path. It defines a category on NSString to initialize a string from NSData using an IANA character set name. It also shows code for getting the preferred MIME type by calling UTTypeCopyPreferredTagWithClass on the file's UTI, determined from its extension using UTTypeCreatePreferredIdentifierForTag, or from its path using LSCopyItemAttributes.
Cocoa勉強会#47-NSURLConnectionのデリゲートメソッドと認証

NSURLConnectionのデリゲートメソッドと認証
This document discusses NSURLConnection delegate methods and authentication. It describes the order that delegate methods are called for different connection states, including before, during and after communication. It also covers all delegate methods, including those related to authentication and handling different error conditions. Code examples are provided to demonstrate how to implement delegate methods to handle normal connections as well as errors, redirects, SSL connections and authentication.
More from Masayuki Nii (20)
Framework Enabling End-Users to Maintain Web Applications (ICICWS2015)

Framework Enabling End-Users to Maintain Web Applications (ICICWS2015)
Recently uploaded
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Infrastructure Challenges in Scaling RAG with Custom AI models

Building Retrieval-Augmented Generation (RAG) systems with open-source and custom AI models is a complex task. This talk explores the challenges in productionizing RAG systems, including retrieval performance, response synthesis, and evaluation. We’ll discuss how to leverage open-source models like text embeddings, language models, and custom fine-tuned models to enhance RAG performance. Additionally, we’ll cover how BentoML can help orchestrate and scale these AI components efficiently, ensuring seamless deployment and management of RAG systems in the cloud.
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf

In this blog post, we'll delve into the intersection of AI and app development in Saudi Arabia, focusing on the food delivery sector. We'll explore how AI is revolutionizing the way Saudi consumers order food, how restaurants manage their operations, and how delivery partners navigate the bustling streets of cities like Riyadh, Jeddah, and Dammam. Through real-world case studies, we'll showcase how leading Saudi food delivery apps are leveraging AI to redefine convenience, personalization, and efficiency.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Recently uploaded (20)
Infrastructure Challenges in Scaling RAG with Custom AI models

Infrastructure Challenges in Scaling RAG with Custom AI models
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf

AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
