Embed presentation
Download to read offline

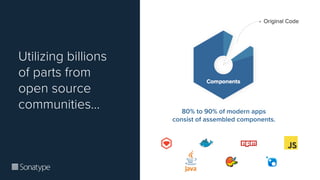


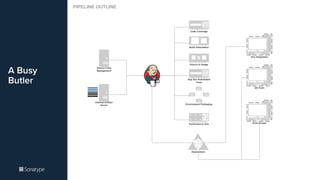
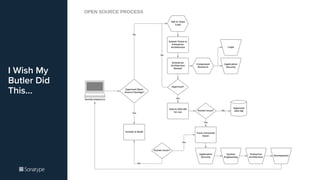

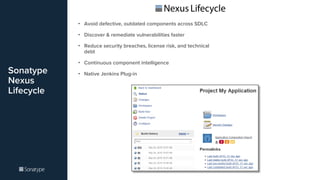


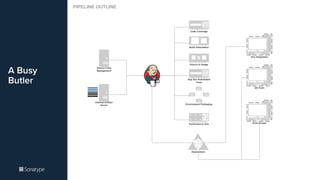
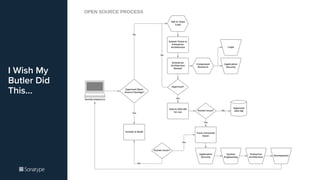
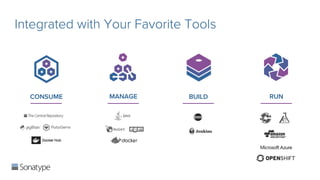
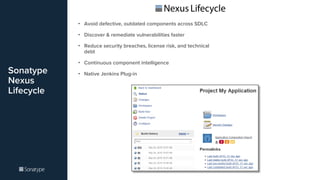
The document discusses the importance of managing open source components in software development, emphasizing that 80% to 90% of modern applications consist of these parts. It highlights the need for automated governance to ensure the integrity of these components throughout the software supply chain. The integration of tools like Sonatype Nexus Lifecycle is presented as a solution for reducing vulnerabilities, security breaches, and technical debt.