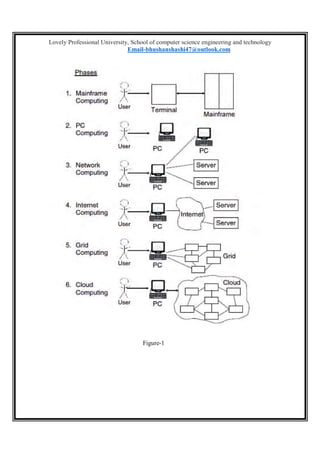
This document discusses cloud computing, including its definition, key features, service layers, deployment models, and challenges. It defines cloud computing as dynamically scalable and virtualized resources provided over the internet. The main service layers are software as a service (SaaS), platform as a service (PaaS), and infrastructure as a service (IaaS). The document also discusses private, public, and hybrid cloud deployment models and features like scalability, quality of service, and pricing models. Finally, it outlines challenges around performance, security, control, bandwidth costs, and reliability.




![Lovely Professional University, School of computer science engineering and technology
Email-bhushanshashi47@outlook.com
d. Bandwidth Costs
Cloud computing, companies can
save money on hardware and
software; however, they could incur
higher network bandwidth charges.
Bandwidth cost may be low for
smaller Internet-based applications,
which are not data intensive, but
could significantly grow for data-
intensive applications.
e. Reliability
Cloud computing still does not
always offer round the clock
reliability. There were cases where
cloud computing services suffered
few hours’ outages. In the present and
future days to expect more cloud
computing providers, richer services,
established standards and best
practices.
Conclusion
Cloud computing is recently new
technological development that has the
potential to have a great impact on the world.
It has many benefits that it provides to it users
and businesses. For example, some of the
benefits that it provides to businesses, is that
it reduces operating cost by spending less on
maintenance and software upgrades and
focus more on the businesses itself. But there
are other challenges the cloud computing
must overcome. People are very skeptical
about whether their data is secure and private.
There are no standards or regulations
worldwide provided data through cloud
computing. Europe has data protection laws
but the US, being one of the most
technological advance nation, does not have
any data protection laws. Users also worry
about who can disclose their data and have
ownership of their data. But once, there are
standards and regulation worldwide, cloud
computing will revolutionize the future.
References
http://en.wikipedia.org/wiki/Cloud
computing
Voas, J., & Zhang, J. (March/April
2009). Cloud computing: New wine
or just a new bottle? IEEE ITPro, 15–
17
http://salesforce.com/cloudcomputin
g/ [accessed on 19 July 2018]
M. Ali, “Green Cloud on the
Horizon,” in Proceedings of the 1st
International Conference on Cloud
Computing (CloudMo), pp. 451- 459,
December 2009.
Journal of Information Engineering
and Applications ISSN 2224-5782
(print) ISSN 2225-0506 (online) Vol
2, No.7, 2012](https://image.slidesharecdn.com/11604333cloud-190402092548/85/cloud-computing-based-its-solutions-term-paper-7-320.jpg)