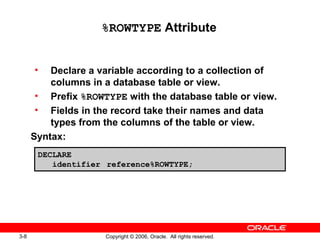
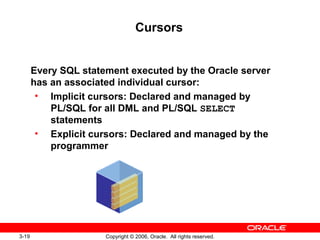
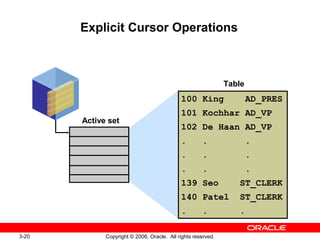
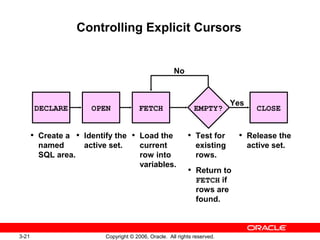
This document discusses composite data types in PL/SQL including records, collections like index by tables and nested tables, and using explicit cursors. It provides examples of declaring different composite data types like records and index by tables, using %ROWTYPE attribute, and controlling explicit cursors through open, fetch, close operations and cursor attributes. It also discusses using cursors with parameters and FOR UPDATE/WHERE CURRENT OF clauses for locking and updating rows.
![3-6 Copyright © 2006, Oracle. All rights reserved.
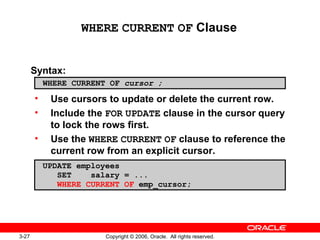
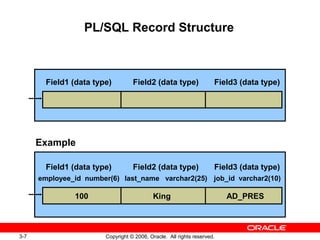
Creating a PL/SQL Record
Syntax:
TYPE type_name IS RECORD
(field_declaration[, field_declaration]…);
field_name {field_type | variable%TYPE
| table.column%TYPE | table%ROWTYPE}
[[NOT NULL] {:= | DEFAULT} expr]
identifier type_name;
1
2
field_declaration:](https://image.slidesharecdn.com/class03-130704014340-phpapp01/85/03-Writing-Control-Structures-Writing-with-Compatible-Data-Types-Using-Explicit-Cursors-6-320.jpg)
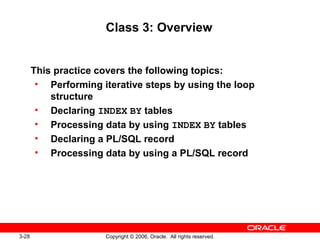
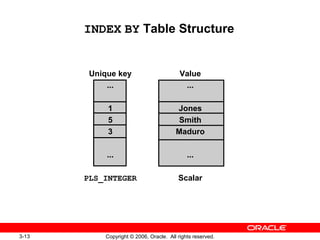
![3-12 Copyright © 2006, Oracle. All rights reserved.
Creating an INDEX BY Table
Syntax:
Declare an INDEX BY table to store the last names of
employees:
TYPE type_name IS TABLE OF
{column_type | variable%TYPE
| table.column%TYPE} [NOT NULL]
| table%ROWTYPE
[INDEX BY PLS_INTEGER | BINARY_INTEGER
| VARCHAR2(<size>)];
identifier type_name;
...
TYPE ename_table_type IS TABLE OF
employees.last_name%TYPE
INDEX BY PLS_INTEGER;
...
ename_table ename_table_type;](https://image.slidesharecdn.com/class03-130704014340-phpapp01/85/03-Writing-Control-Structures-Writing-with-Compatible-Data-Types-Using-Explicit-Cursors-11-320.jpg)


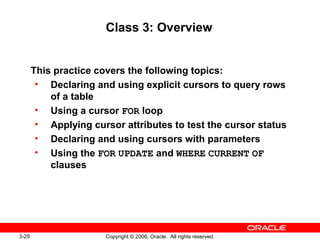
![3-25 Copyright © 2006, Oracle. All rights reserved.
Cursors with Parameters
Syntax:
• Pass parameter values to a cursor when the
cursor is opened and the query is executed.
• Open an explicit cursor several times with a
different active set each time.
CURSOR cursor_name
[(parameter_name datatype, ...)]
IS
select_statement;
OPEN cursor_name(parameter_value,.....) ;](https://image.slidesharecdn.com/class03-130704014340-phpapp01/85/03-Writing-Control-Structures-Writing-with-Compatible-Data-Types-Using-Explicit-Cursors-24-320.jpg)
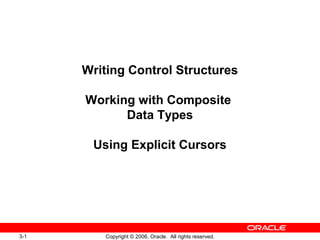
![3-26 Copyright © 2006, Oracle. All rights reserved.
FOR UPDATE Clause
Syntax:
• Use explicit locking to deny access to other
sessions for the duration of a transaction.
• Lock the rows before the update or delete.
SELECT ...
FROM ...
FOR UPDATE [OF column_reference][NOWAIT | WAIT n];](https://image.slidesharecdn.com/class03-130704014340-phpapp01/85/03-Writing-Control-Structures-Writing-with-Compatible-Data-Types-Using-Explicit-Cursors-25-320.jpg)