Embed presentation
Downloaded 305 times

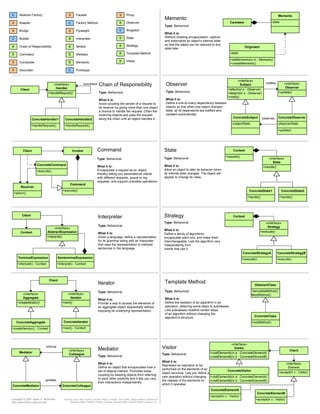
The document summarizes 23 design patterns organized into three categories: Creational patterns, Structural patterns, and Behavioral patterns. Each pattern lists the pattern name, intent, participants, and collaborations in 1-2 sentences. For example, the Singleton pattern ensures a class only has one instance and provides a global point of access to it.