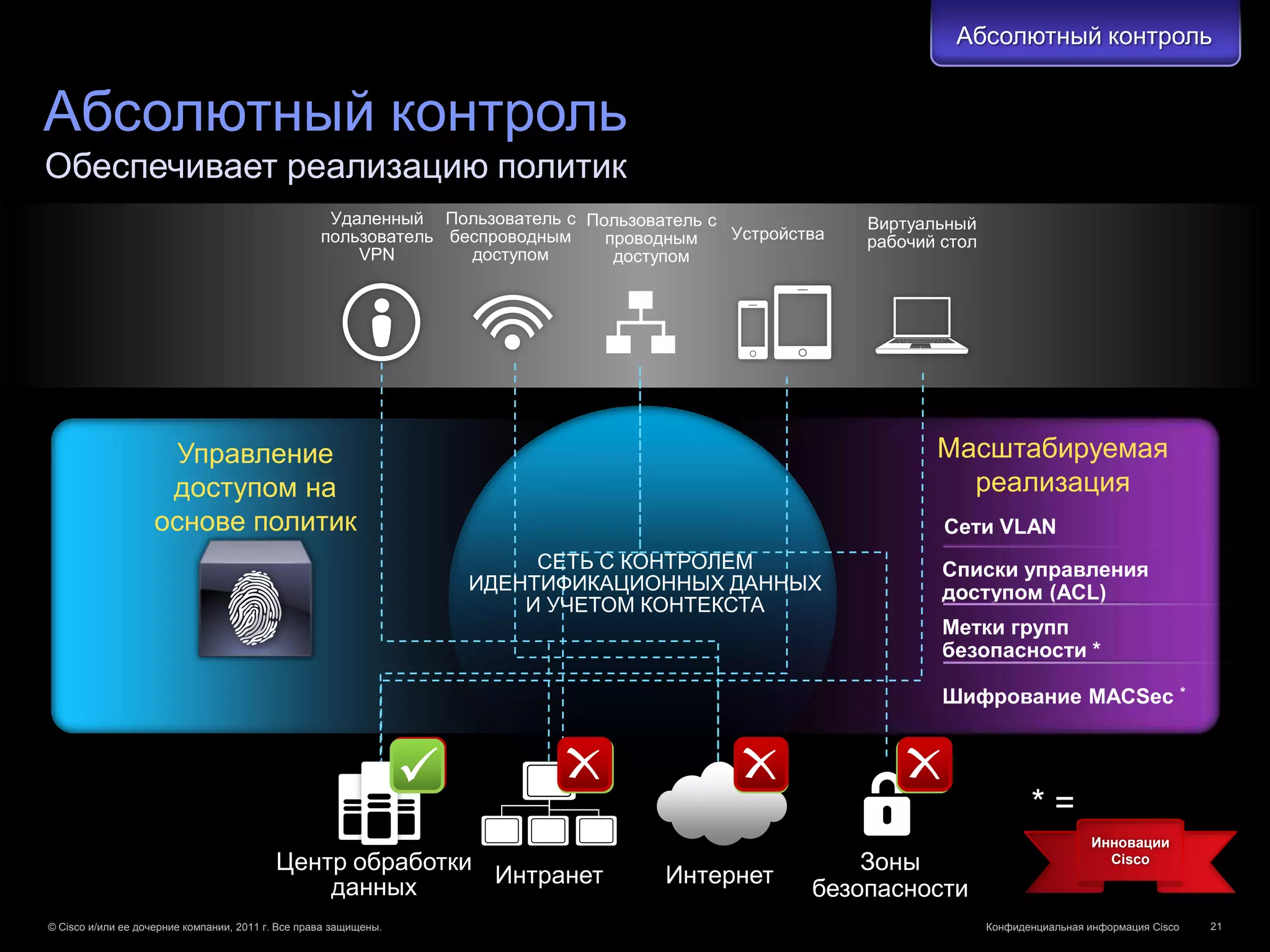
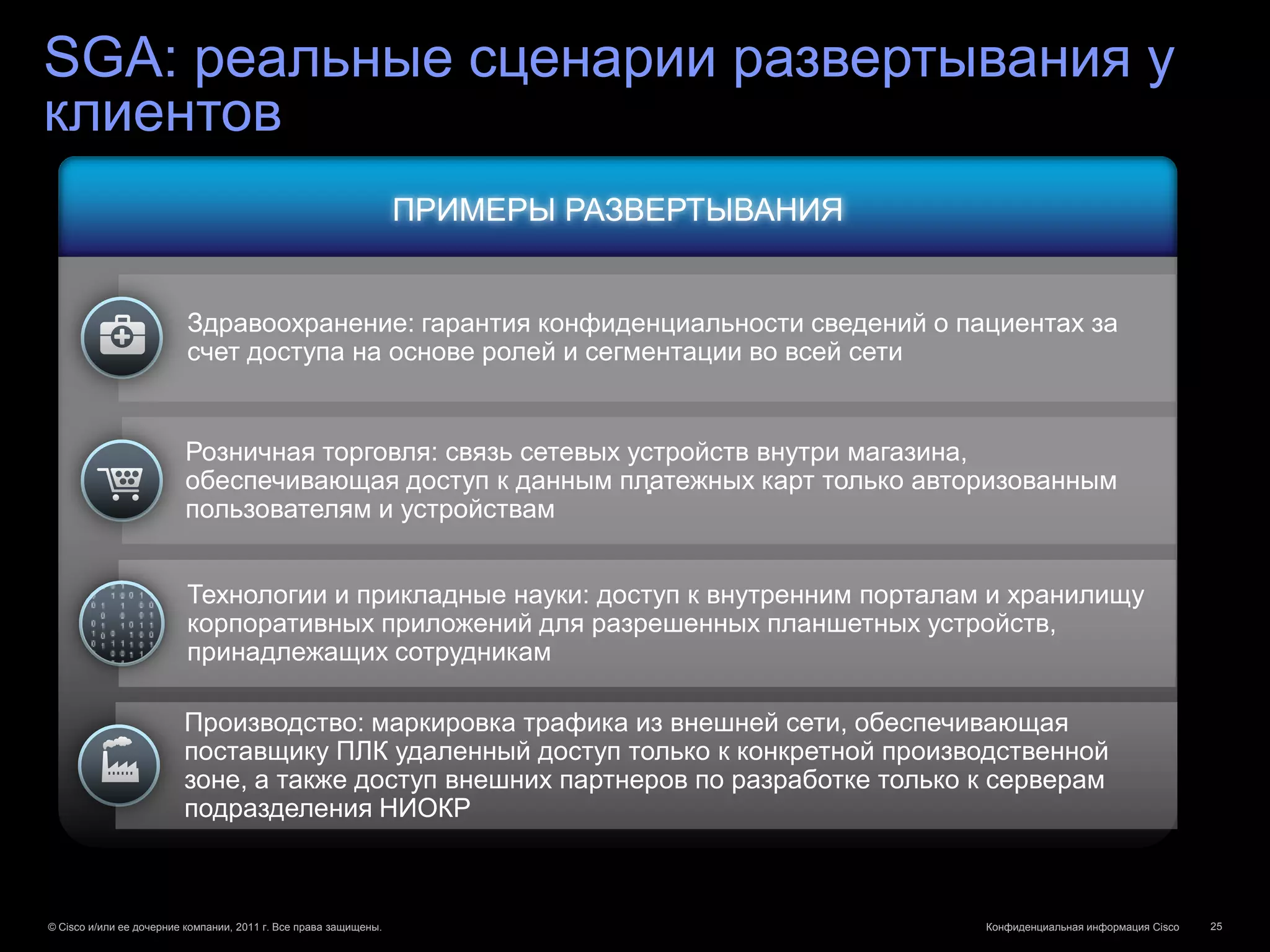
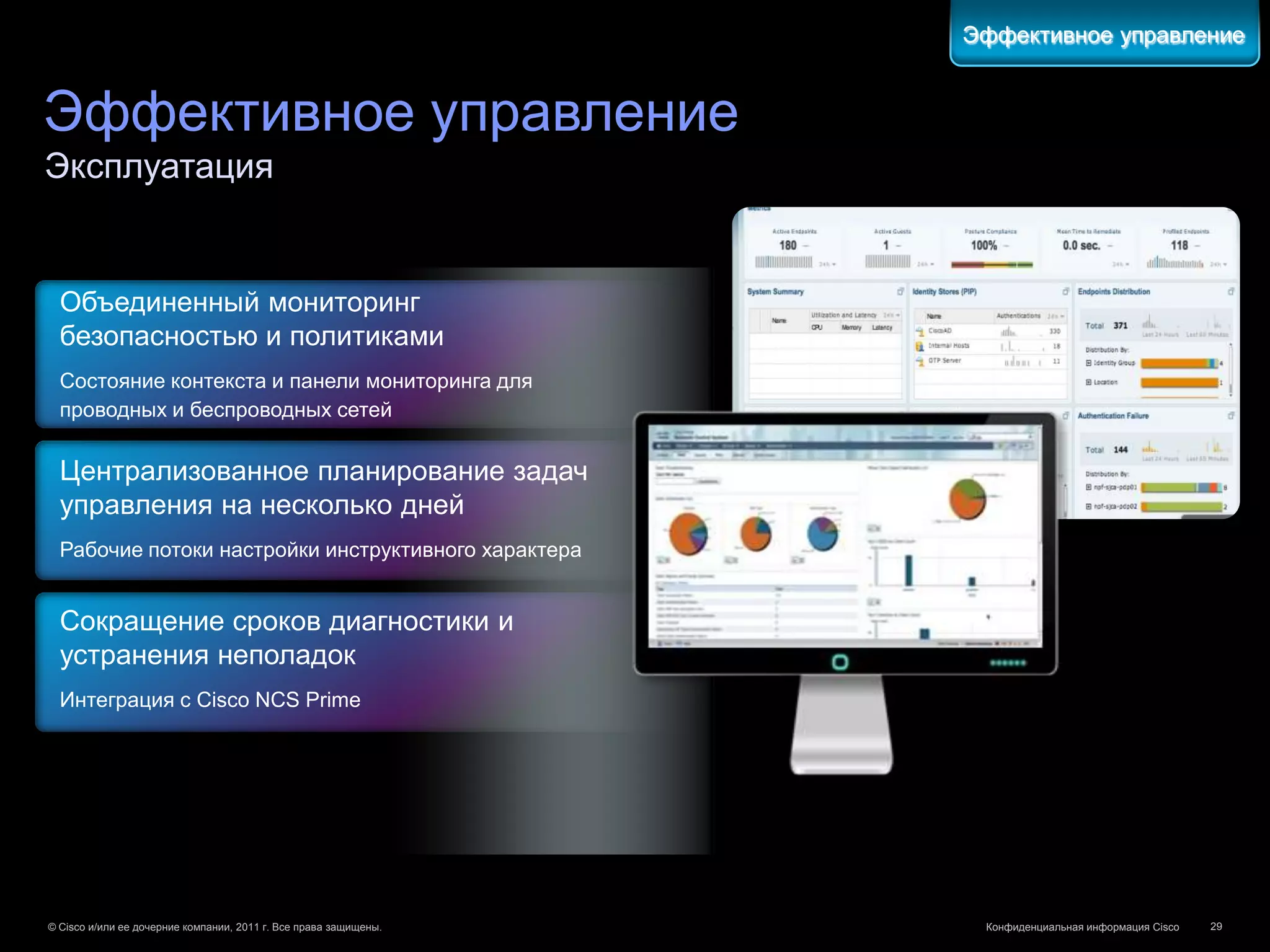
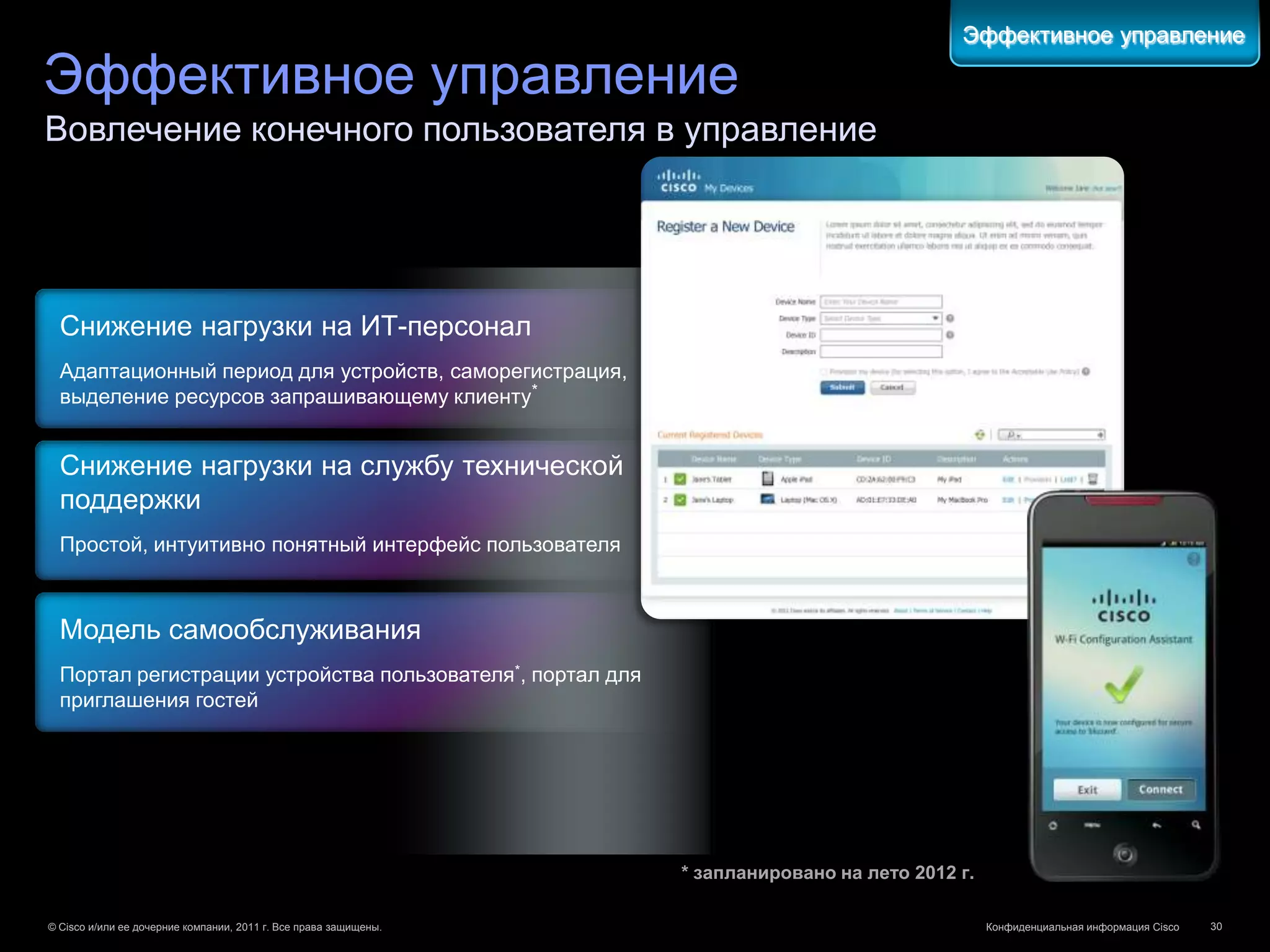
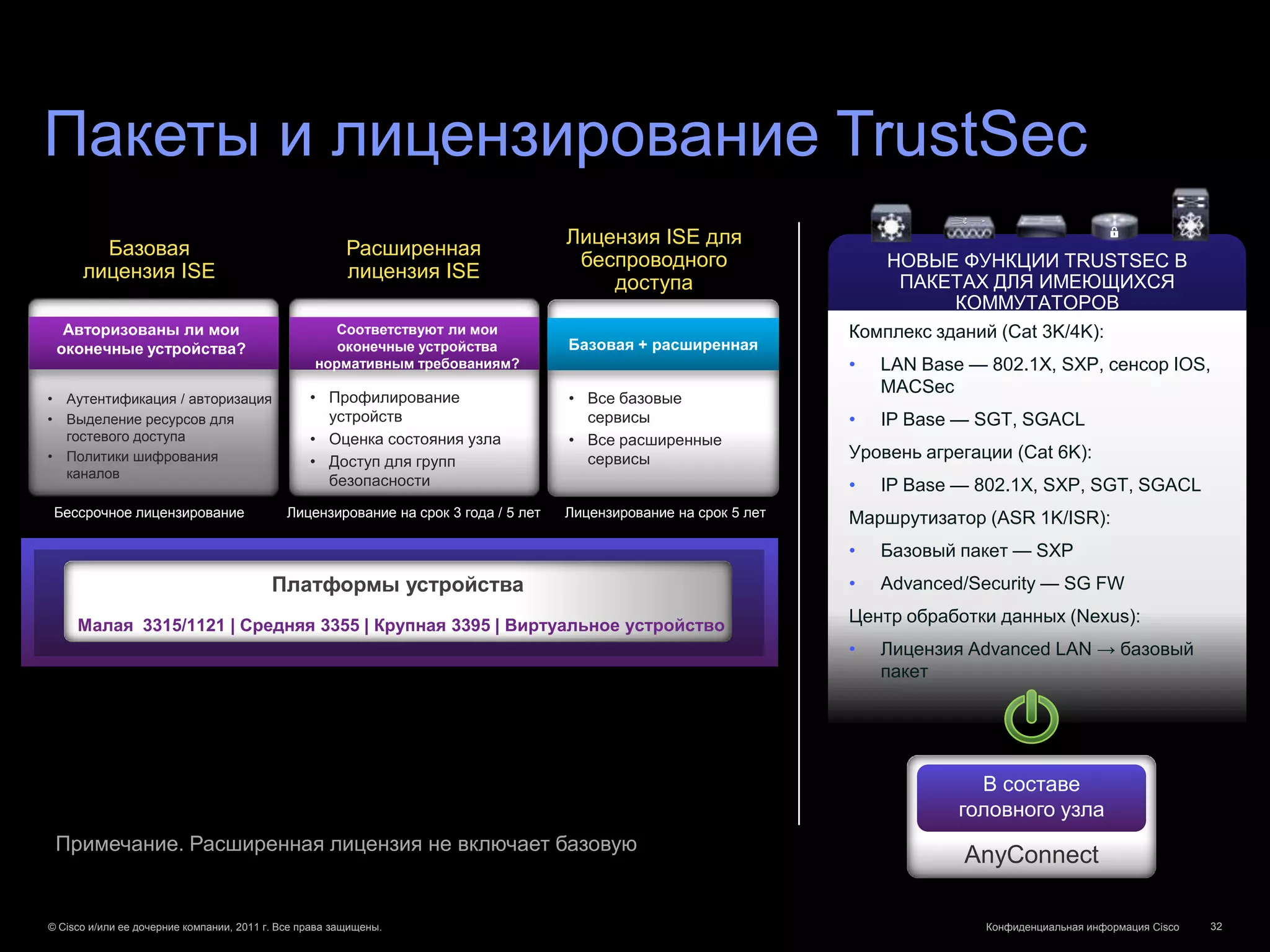
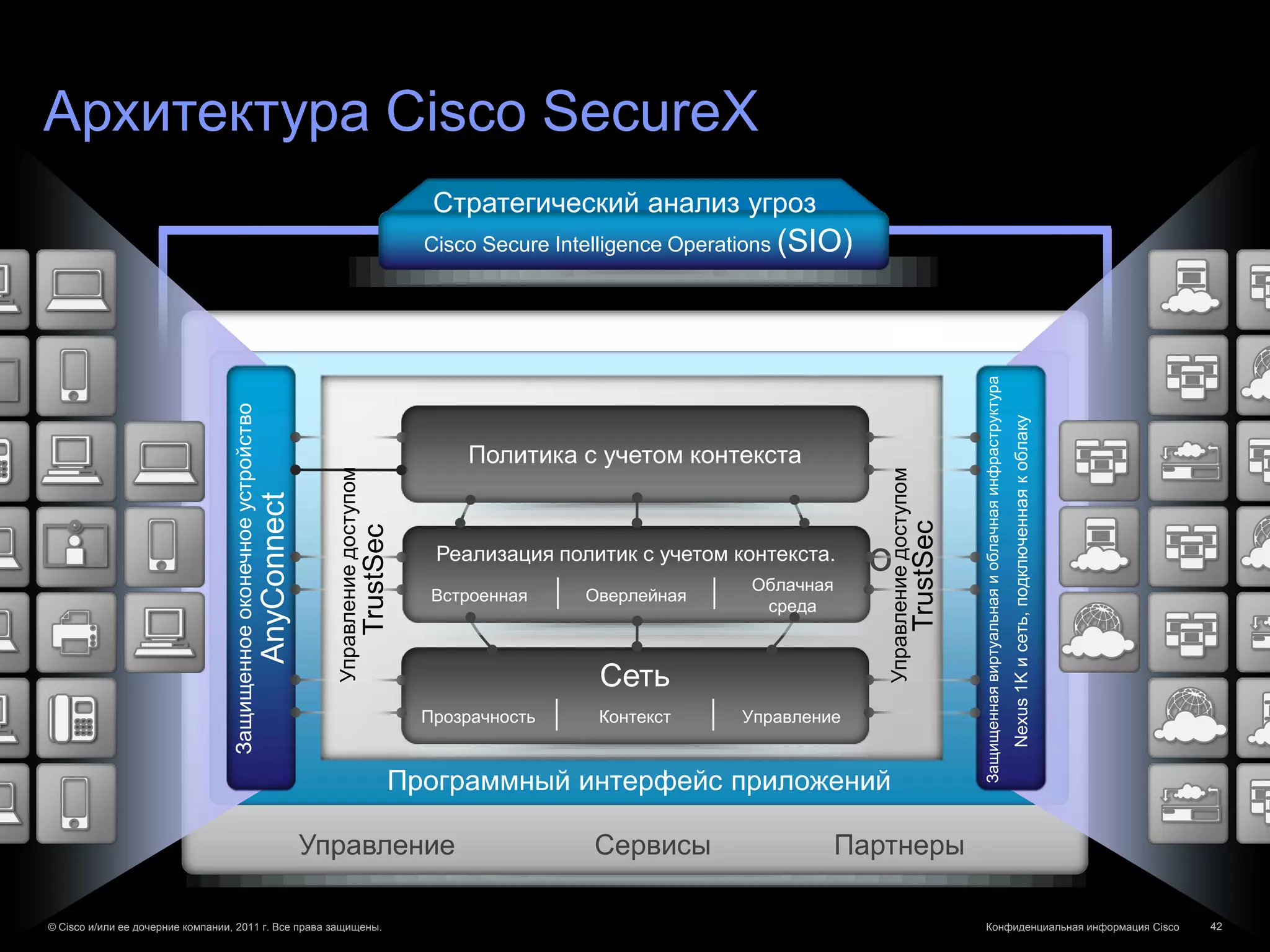
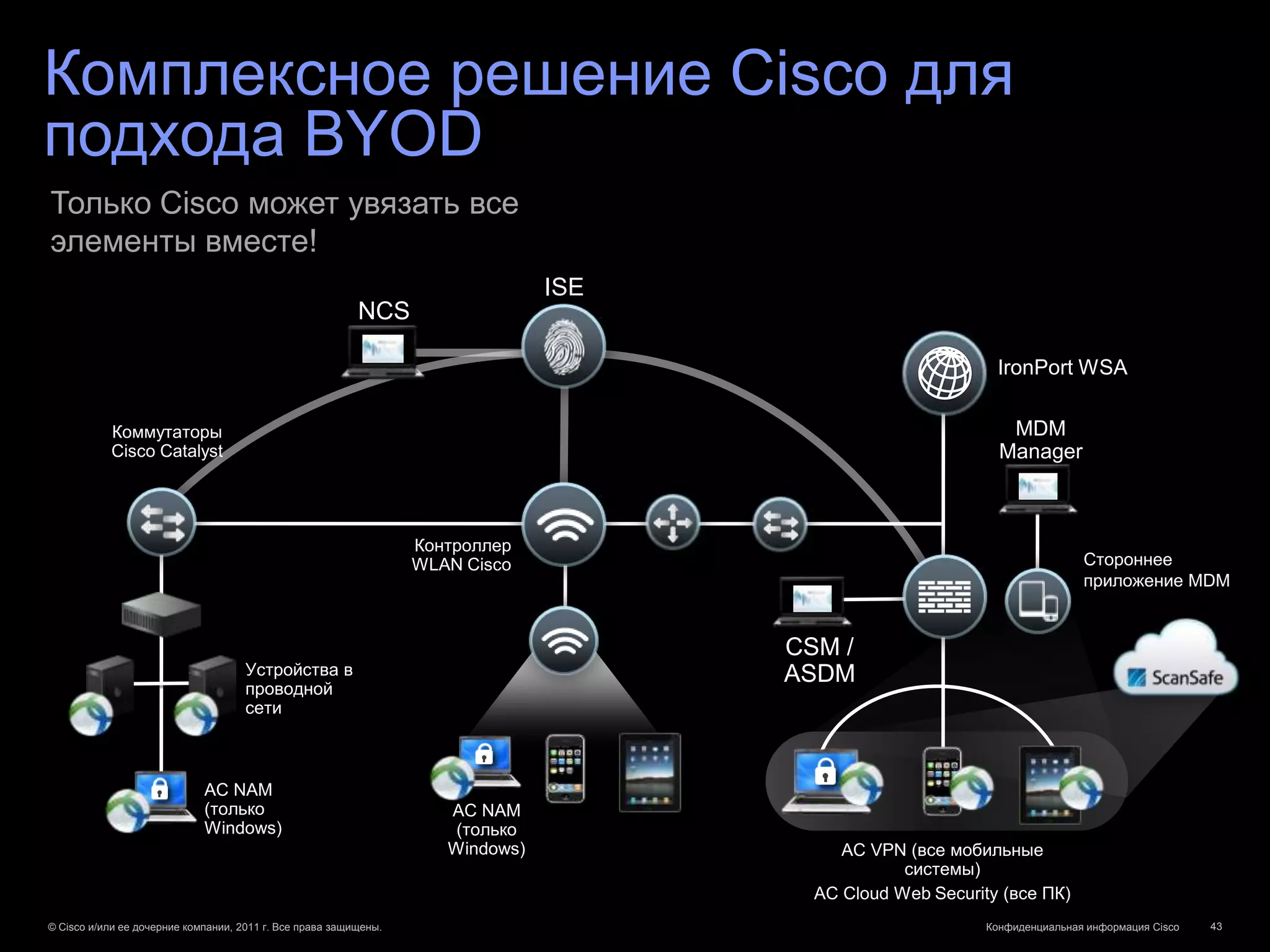
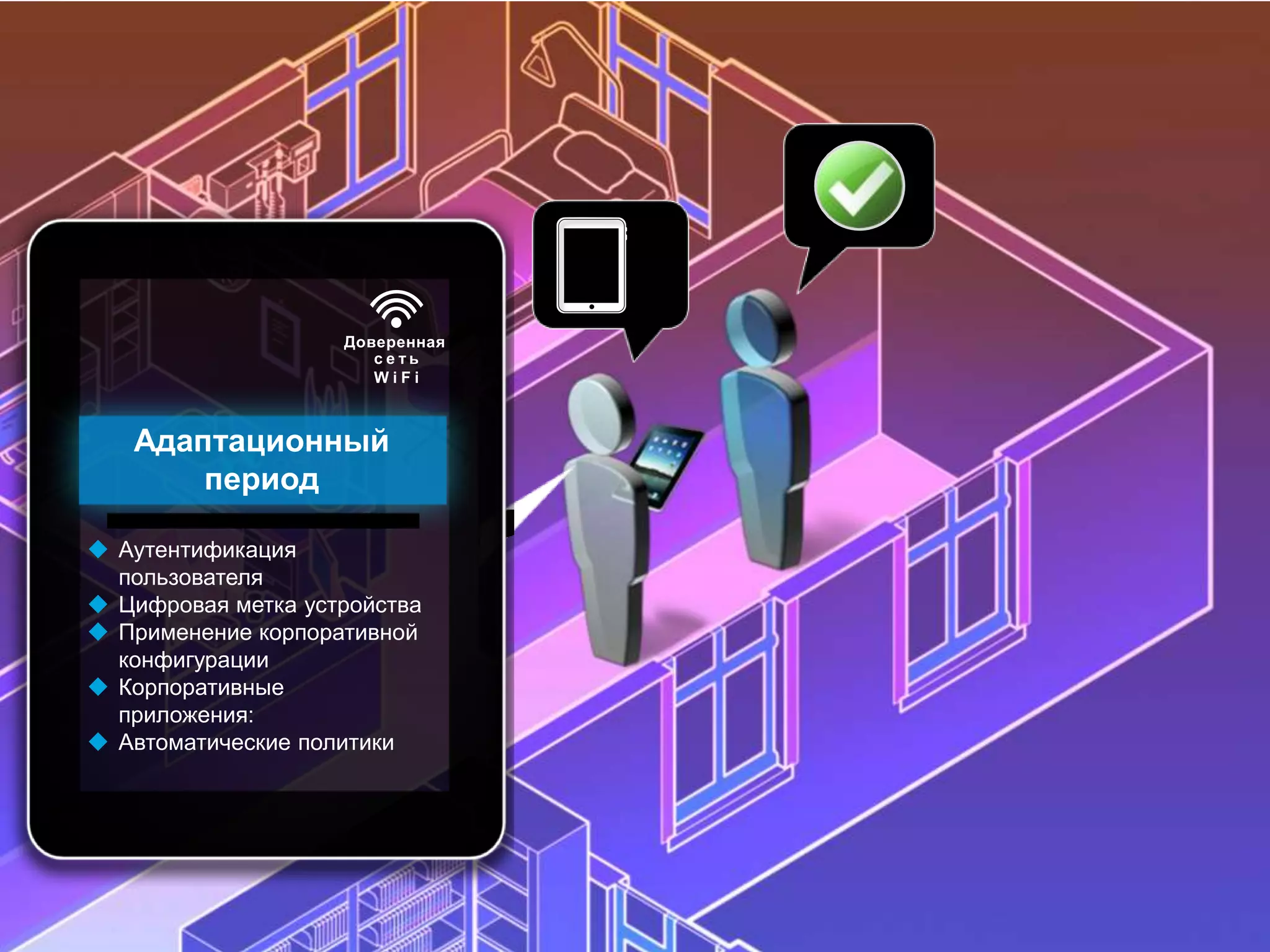
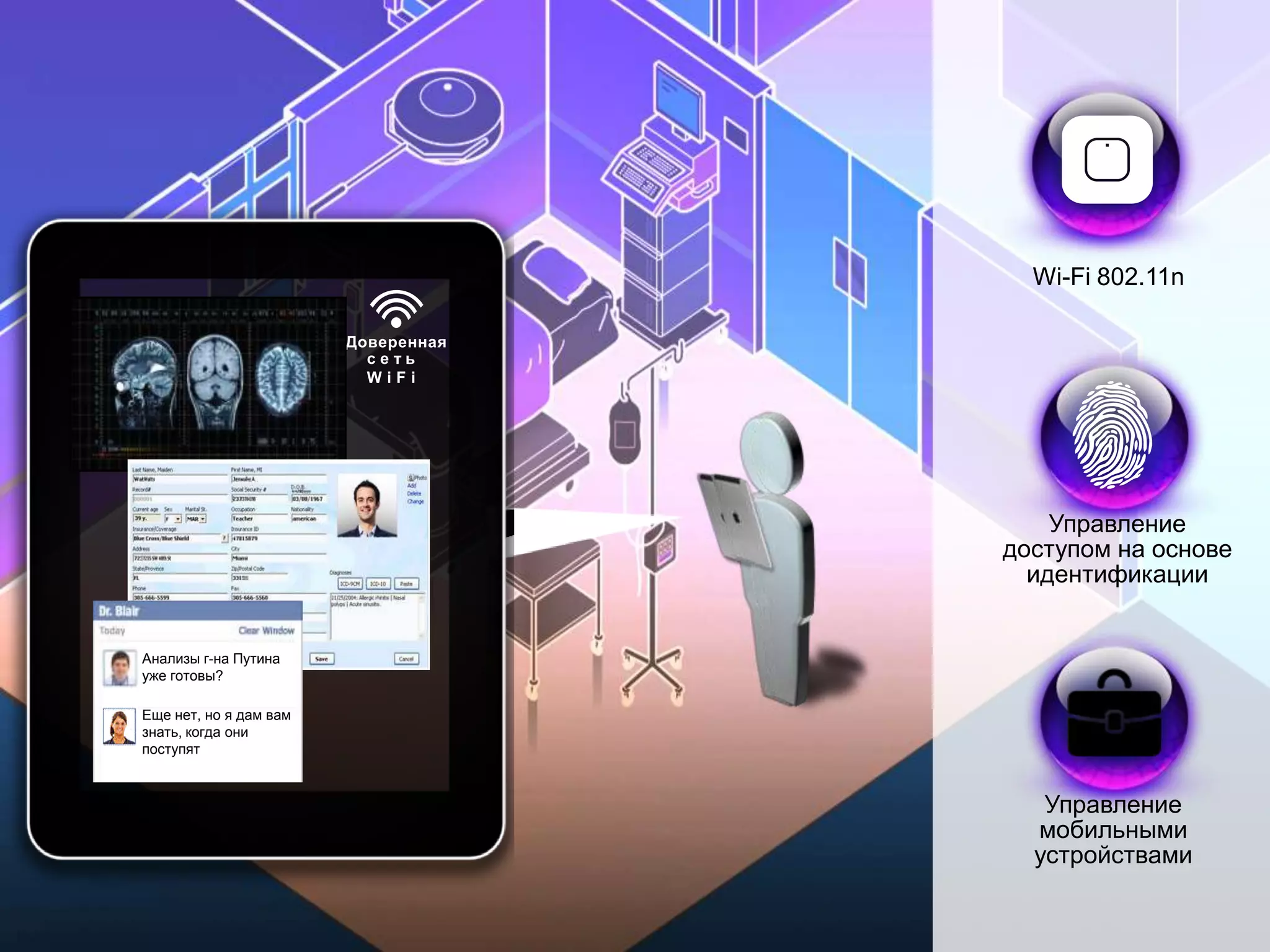
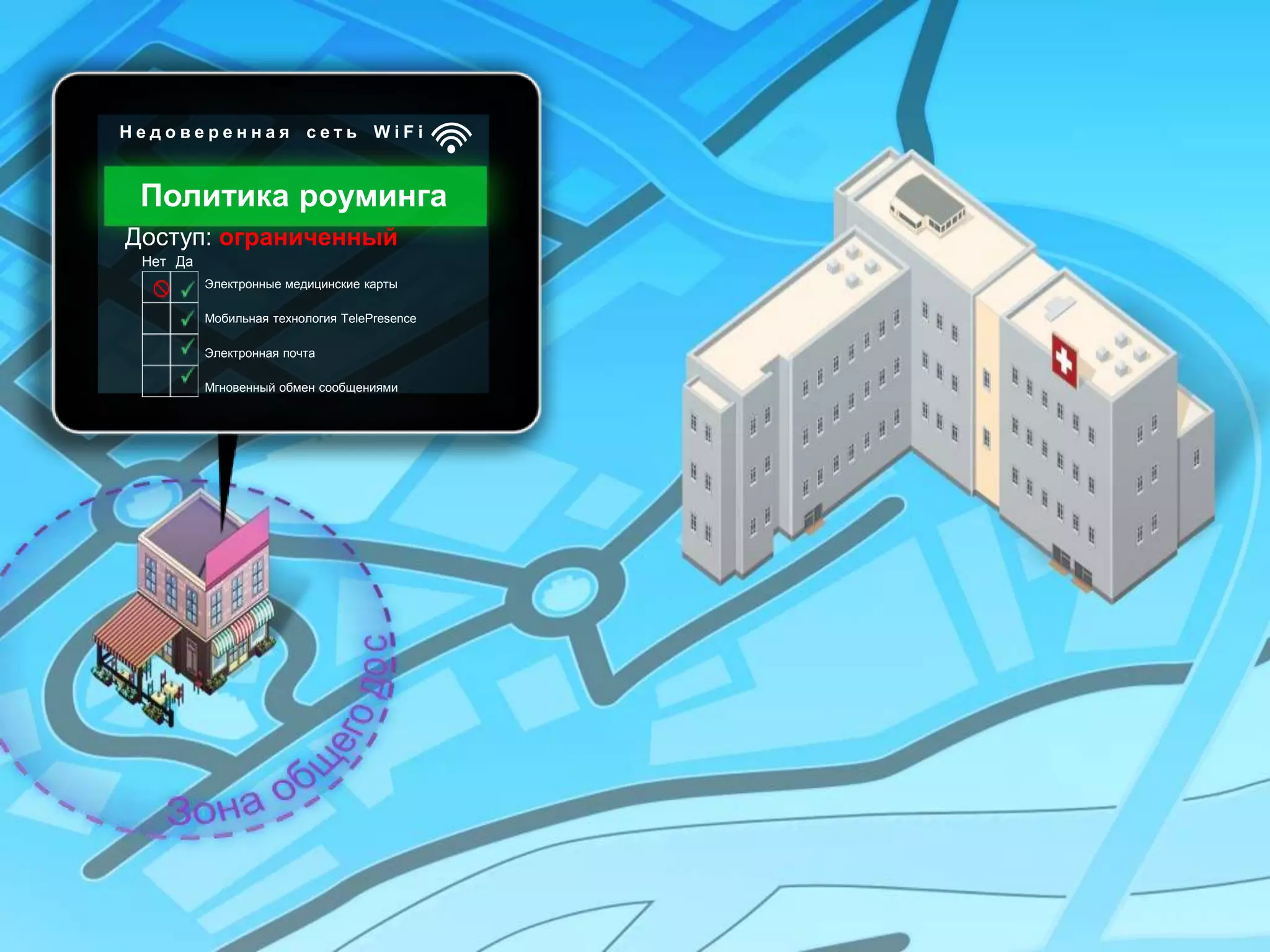
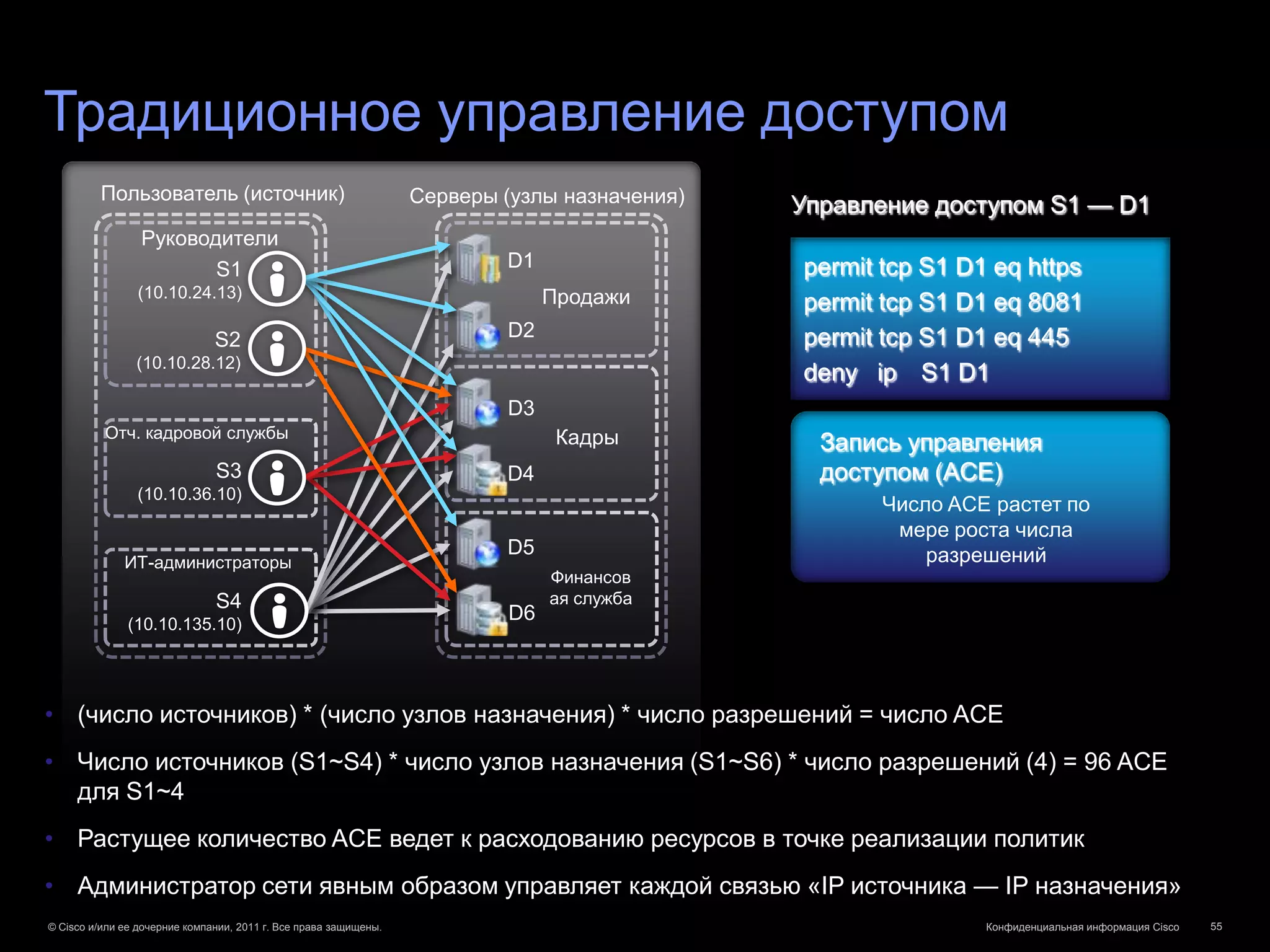
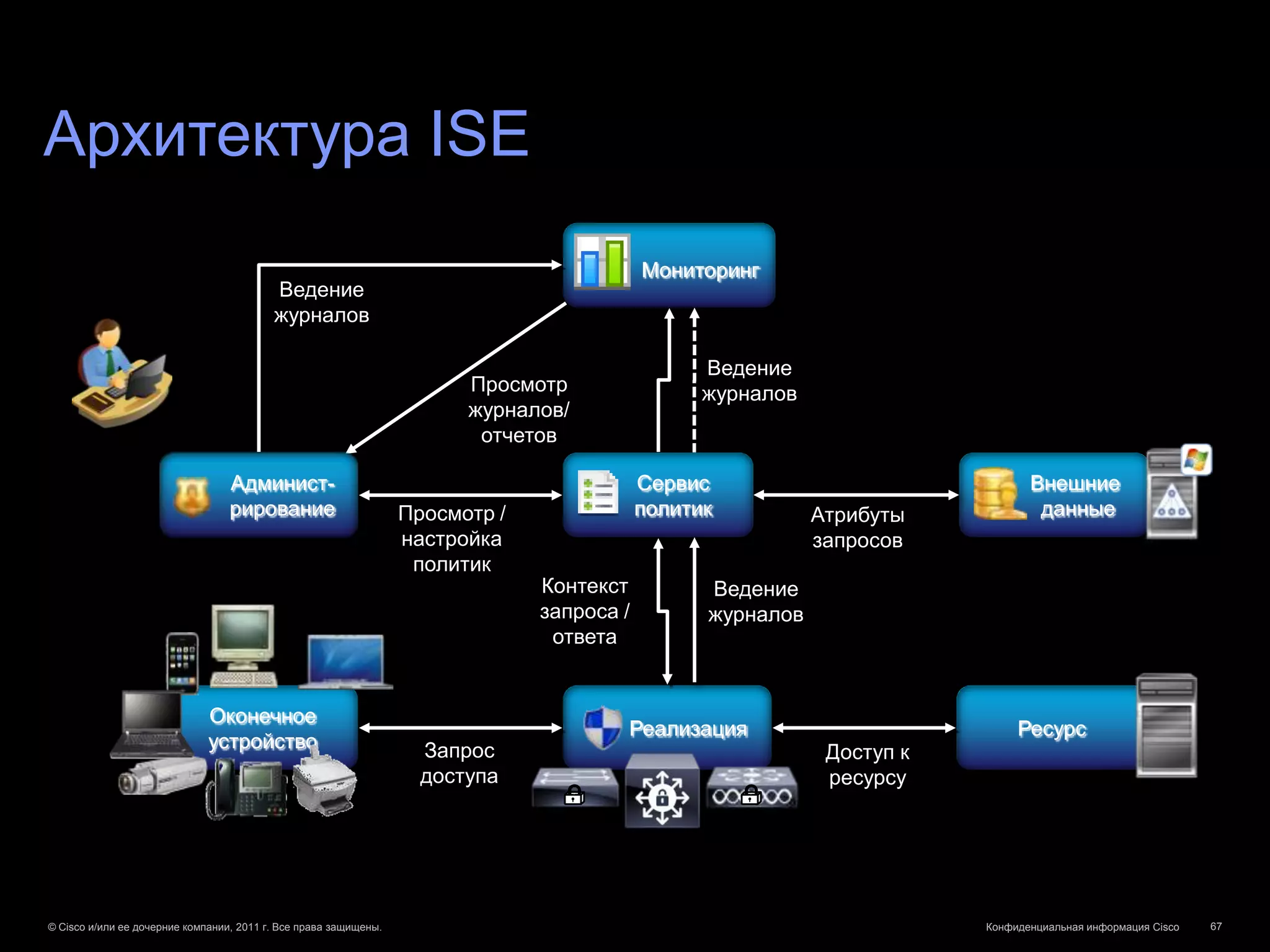
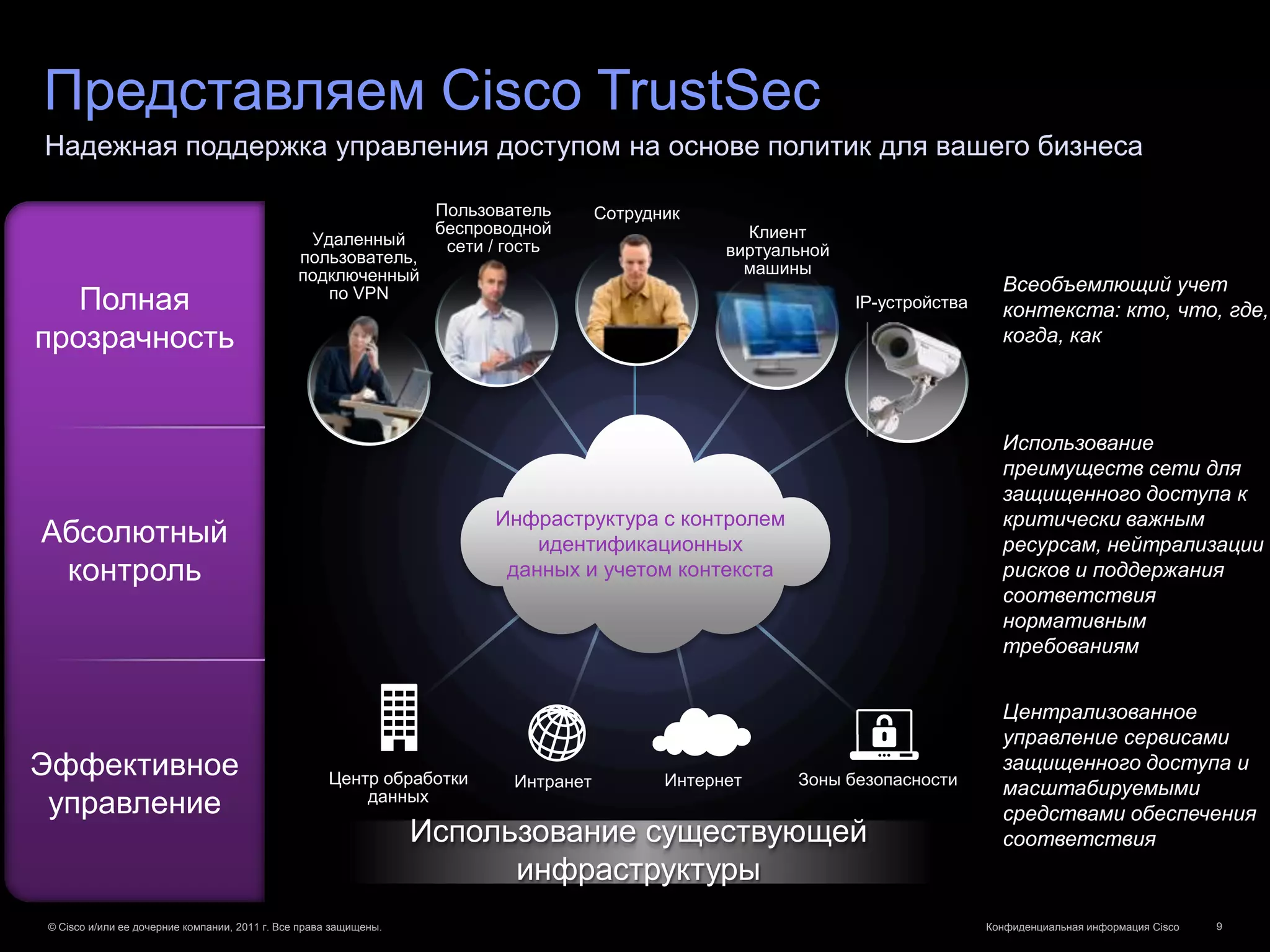
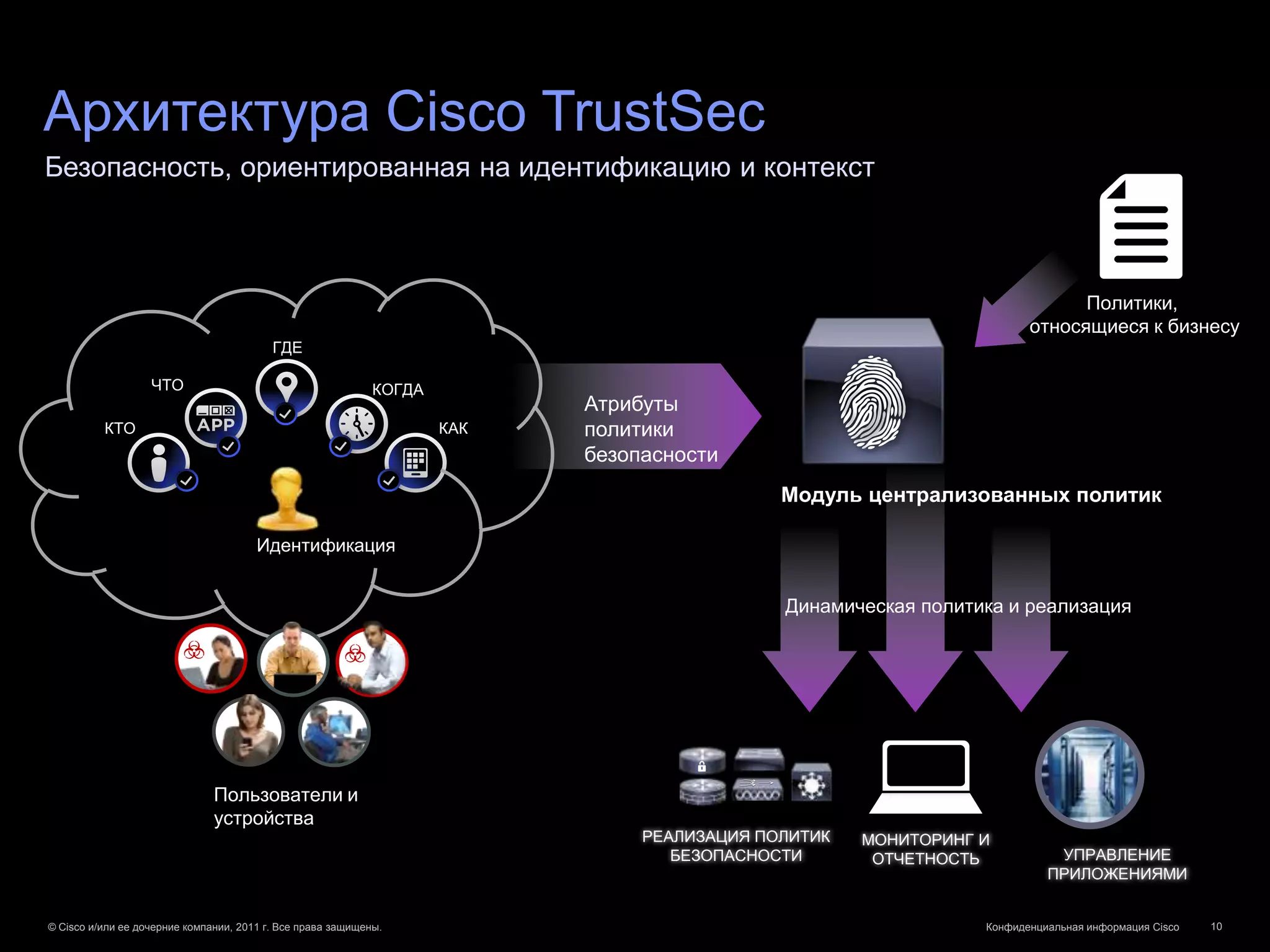
Документ описывает решения Cisco для управления доступом на основе политик с использованием TrustSec и Identity Services Engine, что позволяет предприятиям адаптироваться к растущему числу устройств и сотрудникам, использующим собственные гаджеты. Он подчеркивает важность безопасности, соответствия нормативам и управления сетевыми ресурсами через многоуровневую идентификацию и динамическое управление доступом. В документе также рассмотрены практические сценарии применения технологий в различных отраслях, таких как здравоохранение и розничная торговля.





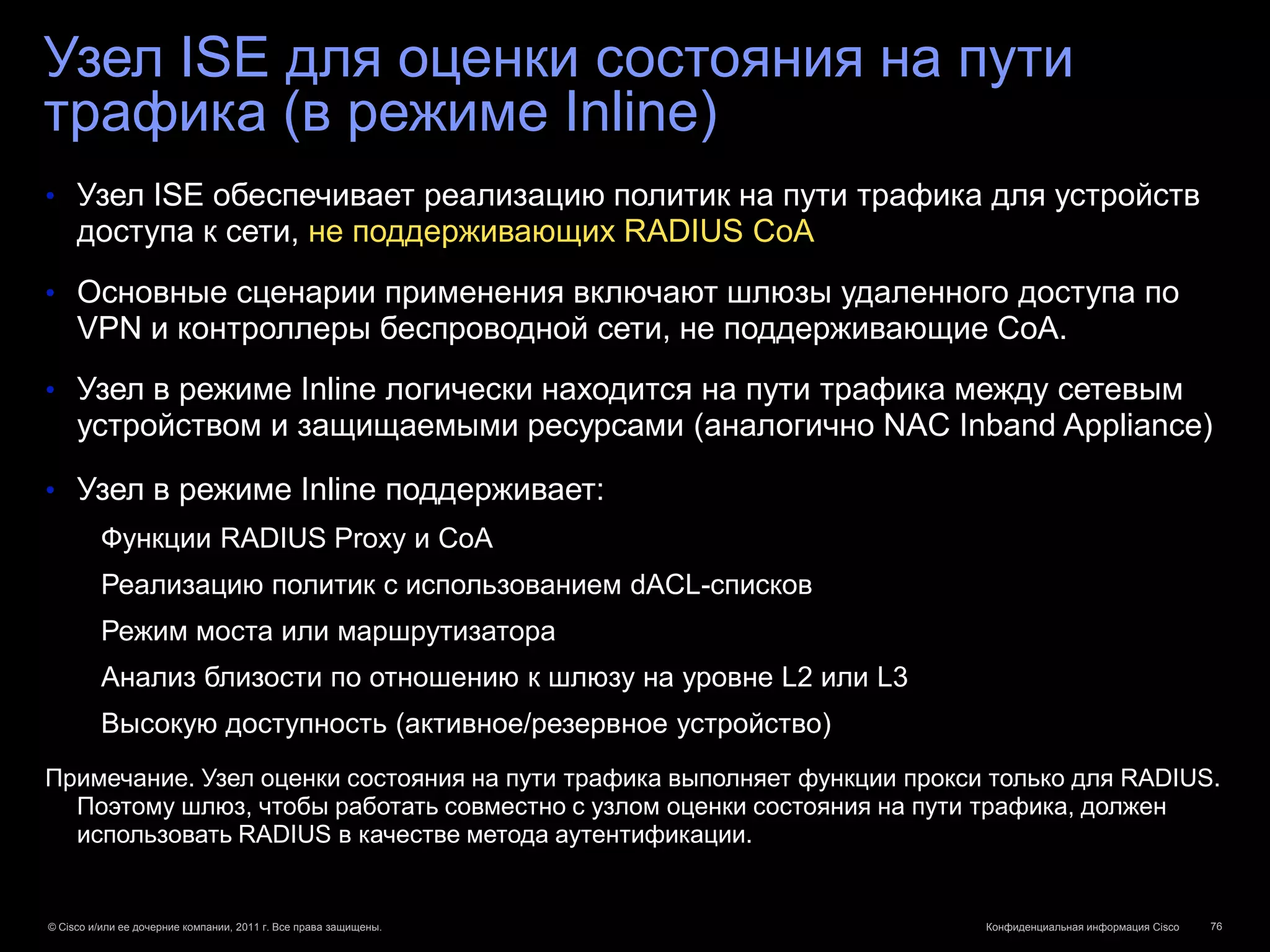
![Полная прозрачность
Идентификация устройств Компоненты
Новаторство
Автоматическая классификация устройств с использованием инфраструктуры Cisco
ПРОФИЛИРОВАНИЕ УСТРОЙСТВ
Для проводных и беспроводных сетей
ПОЛИТИКА
Принтер Личный iPad
ISE
Точка доступа
Политика для Политика для
CDP CDP
принтера LLDP LLDP личного iPad
DHCP DHCP
MAC-адрес MAC-адрес
[поместить в VLAN X] [ограниченный доступ]
Точка
доступа
Решение СЦЕНАРИЙ РАЗВЕРТЫВАНИЯ С СЕНСОРАМИ УСТРОЙСТВ CISCO
Эффективная СБОР ДАННЫХ КЛАССИФИКАЦИЯ АВТОРИЗАЦИЯ
классификация устройств Коммутатор собирает данные, ISE производит классификацию ISE реализует доступ на основе
с использованием относящиеся к устройству, и устройства, сбор данных о политик для данного
передает отчет в ISE трафике и формирует отчет об пользователя и устройства
инфраструктуры использовании устройства
© Cisco и/или ее дочерние компании, 2011 г. Все права защищены. Конфиденциальная информация Cisco 17](https://image.slidesharecdn.com/trustsec-ebc02102012-120311063504-phpapp01/75/Cisco-TrustSec-Cisco-ISE-17-2048.jpg)