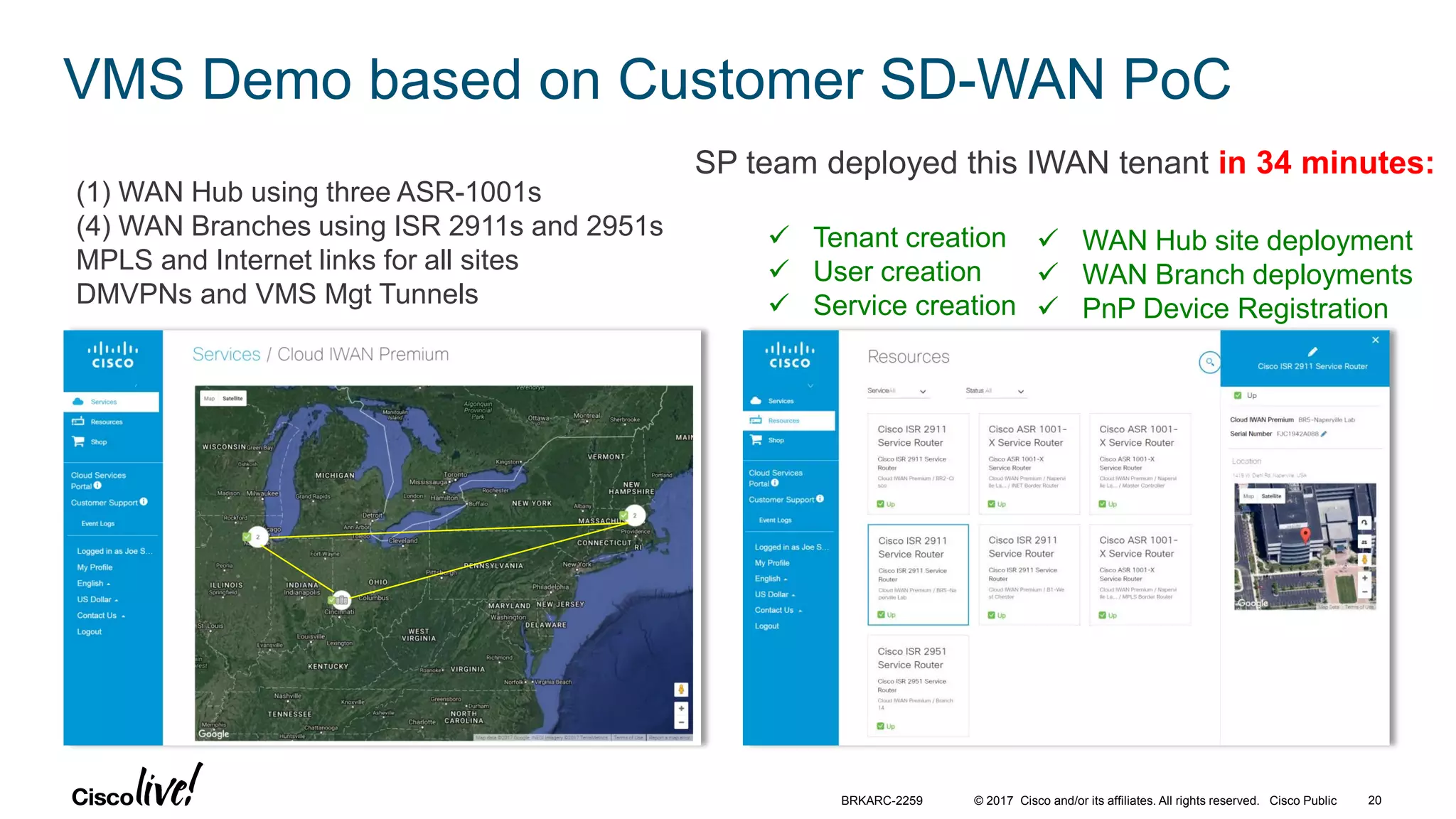
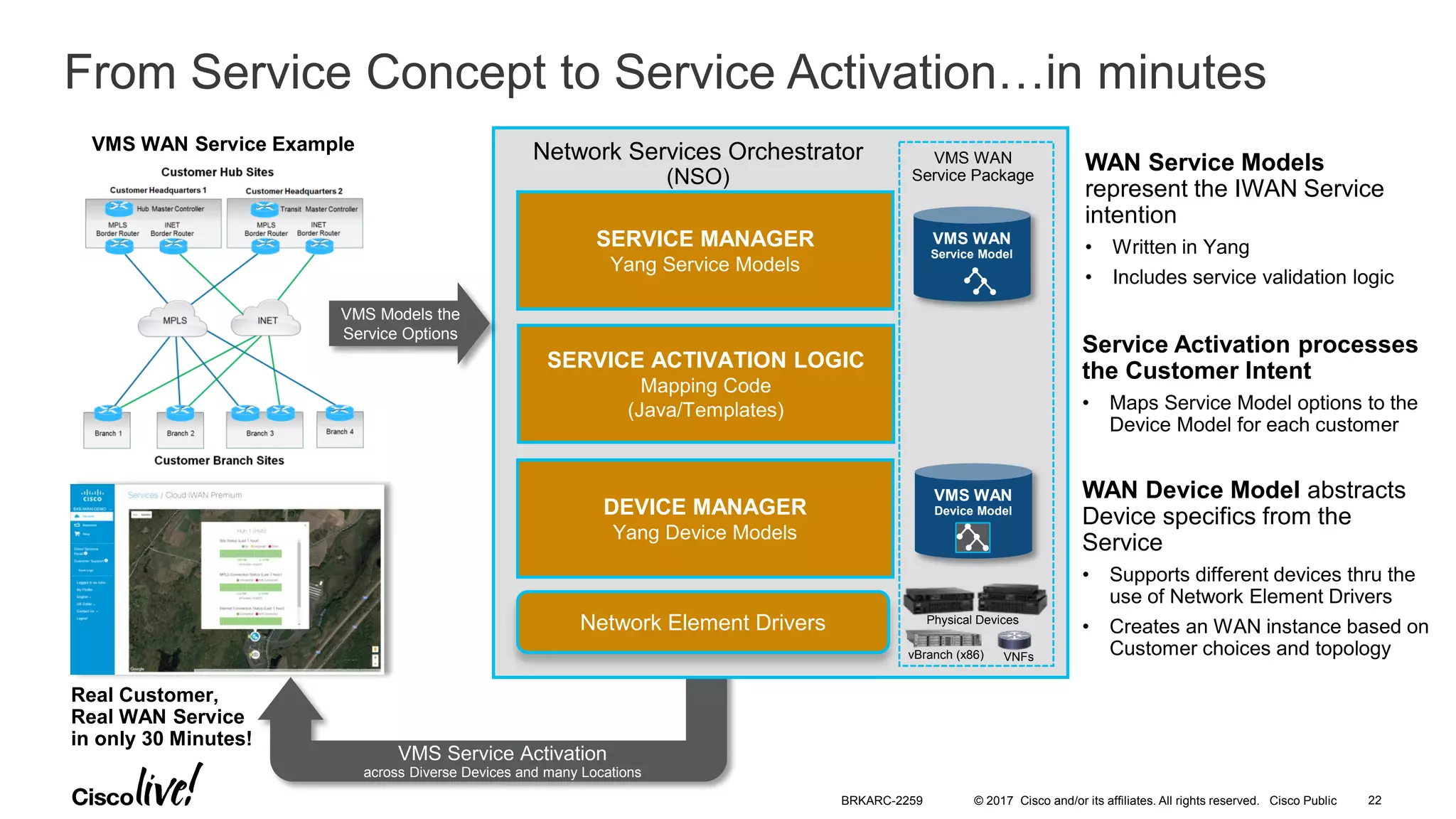
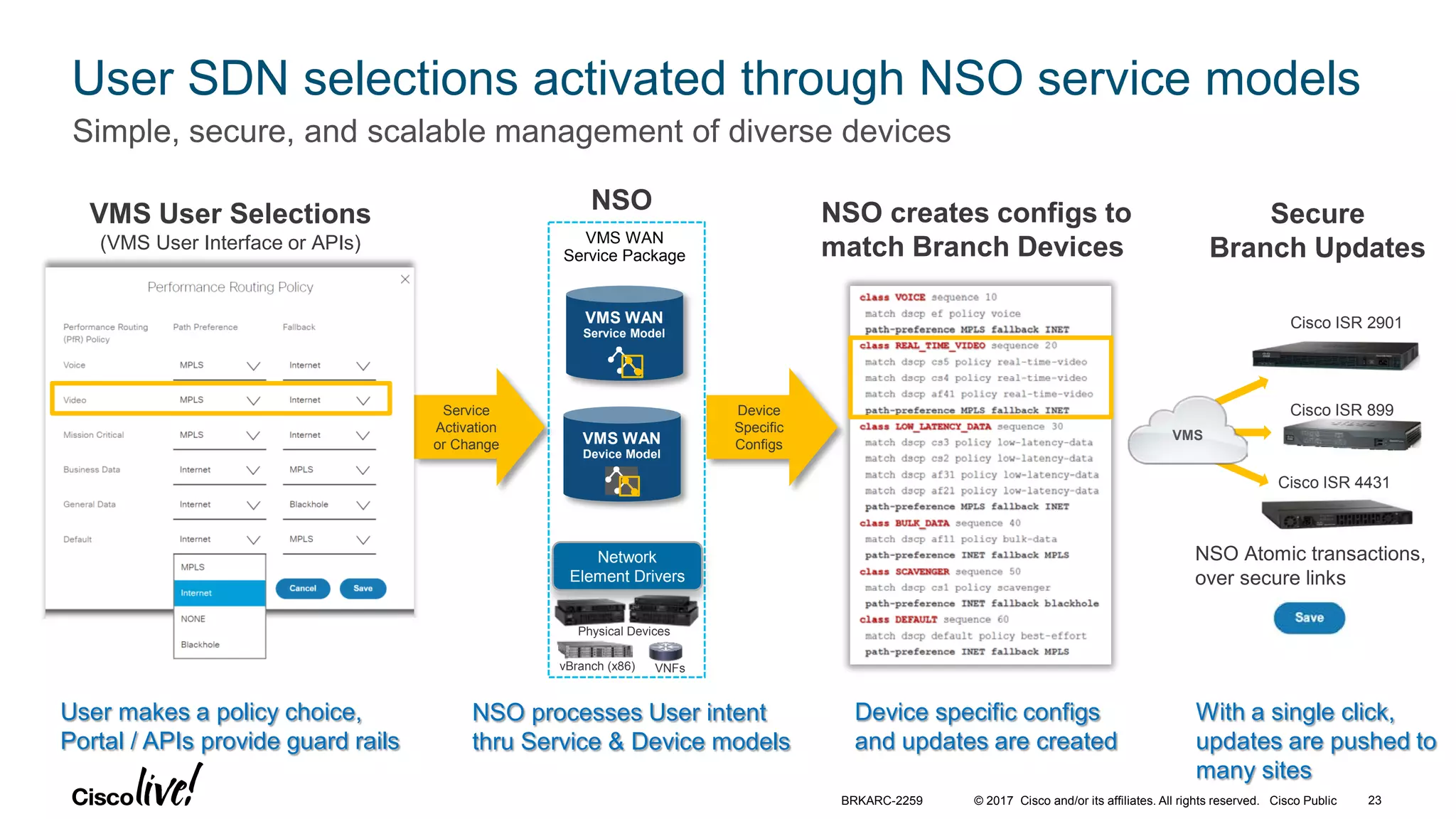
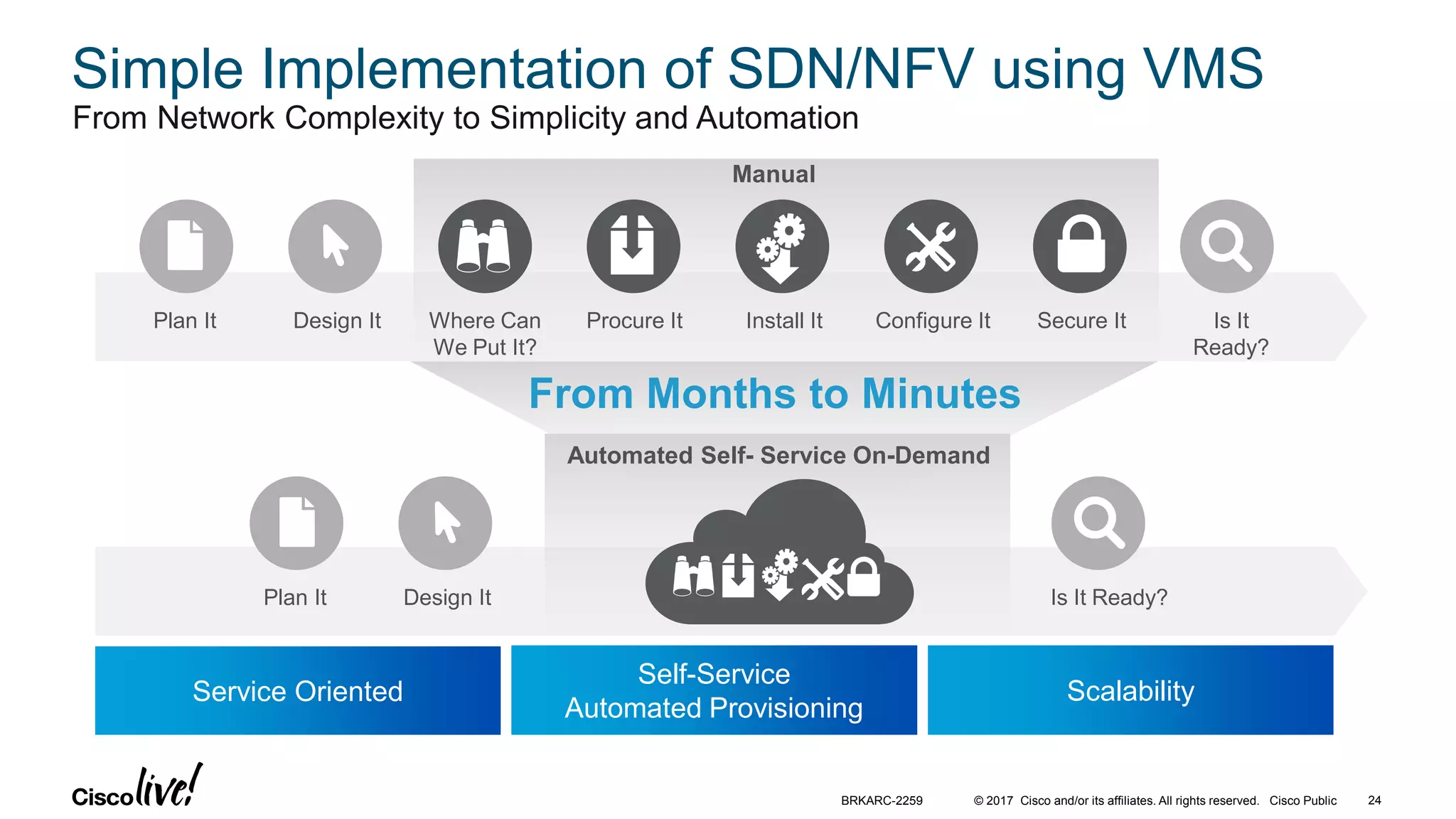
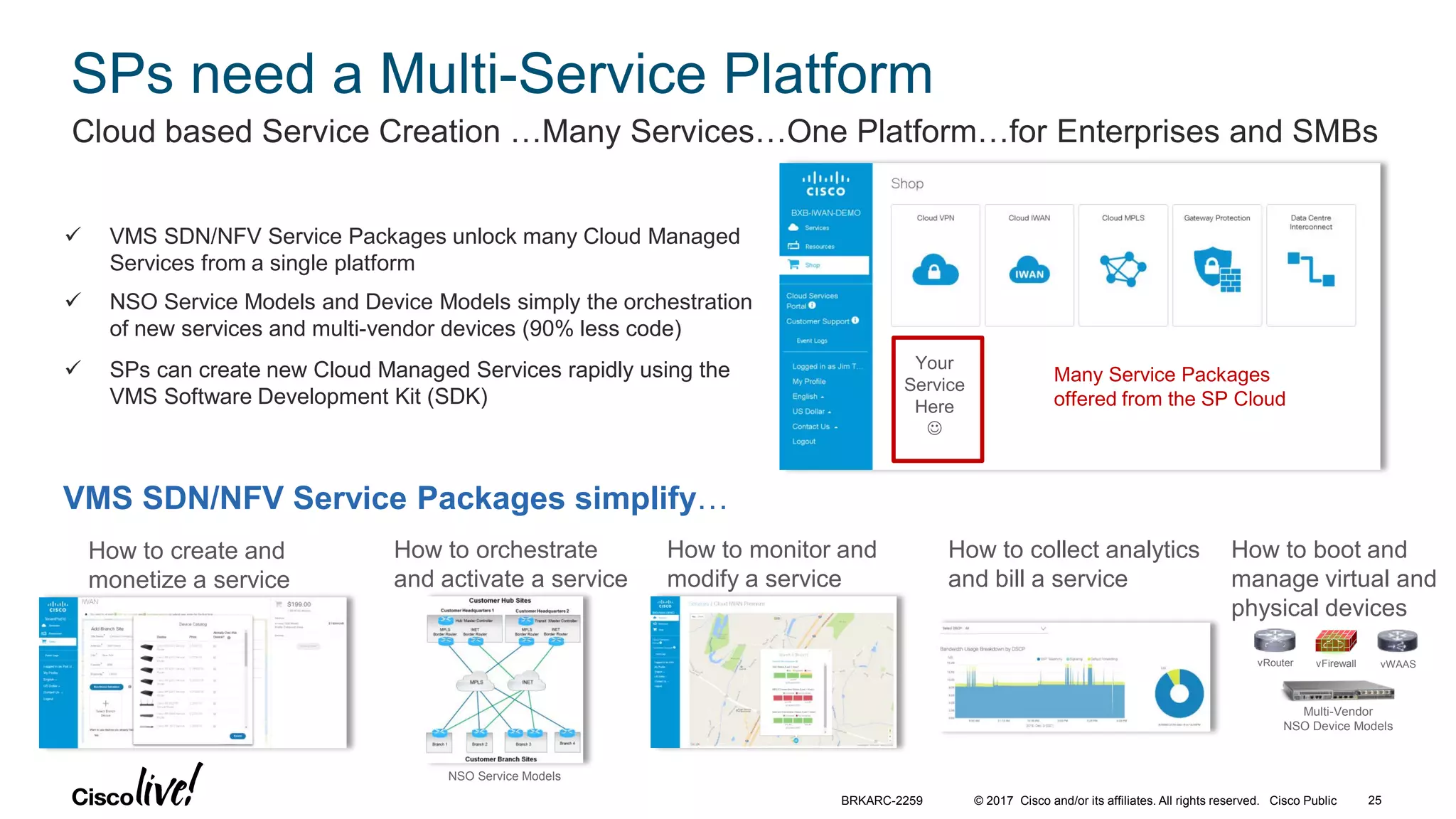
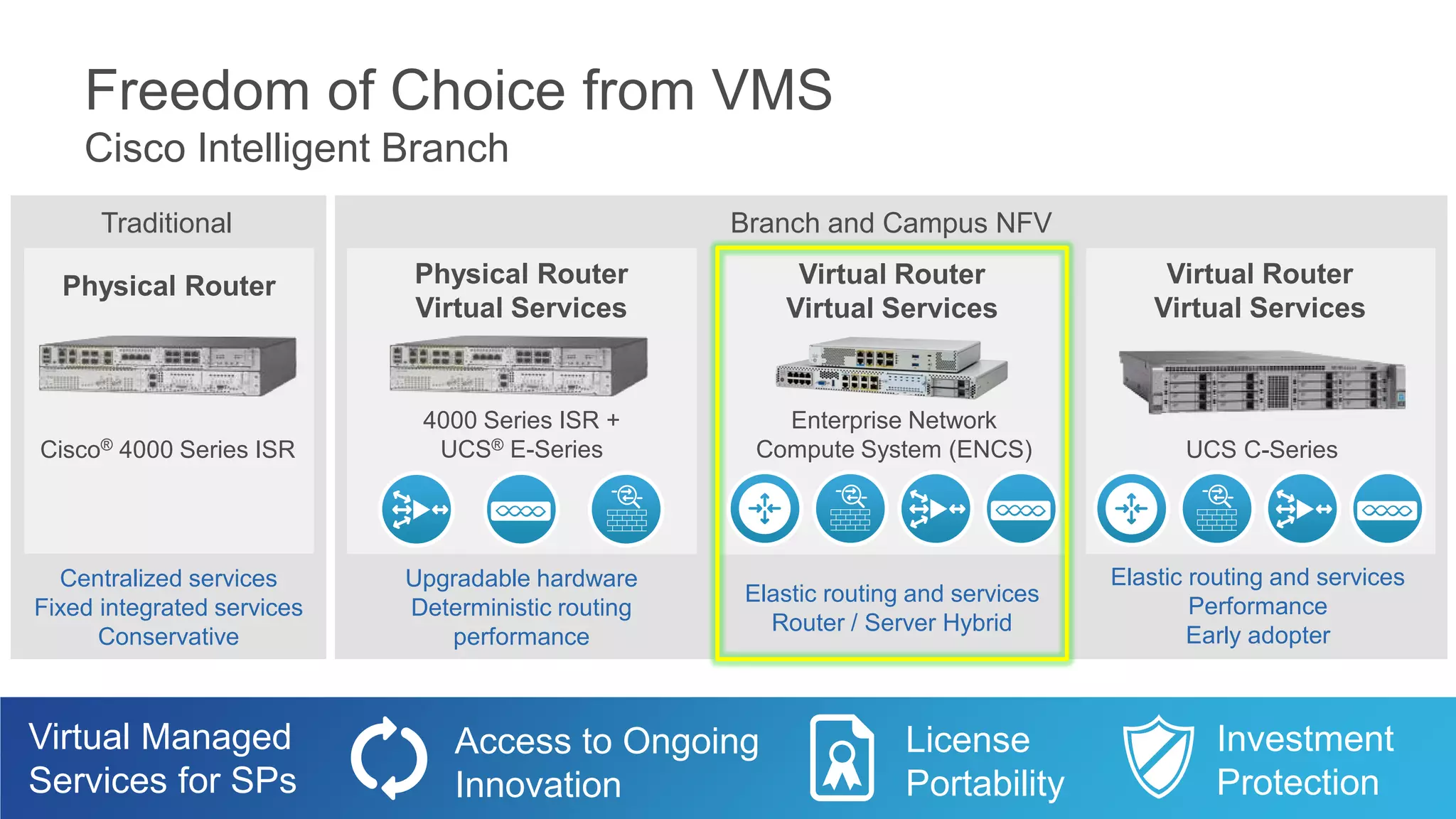
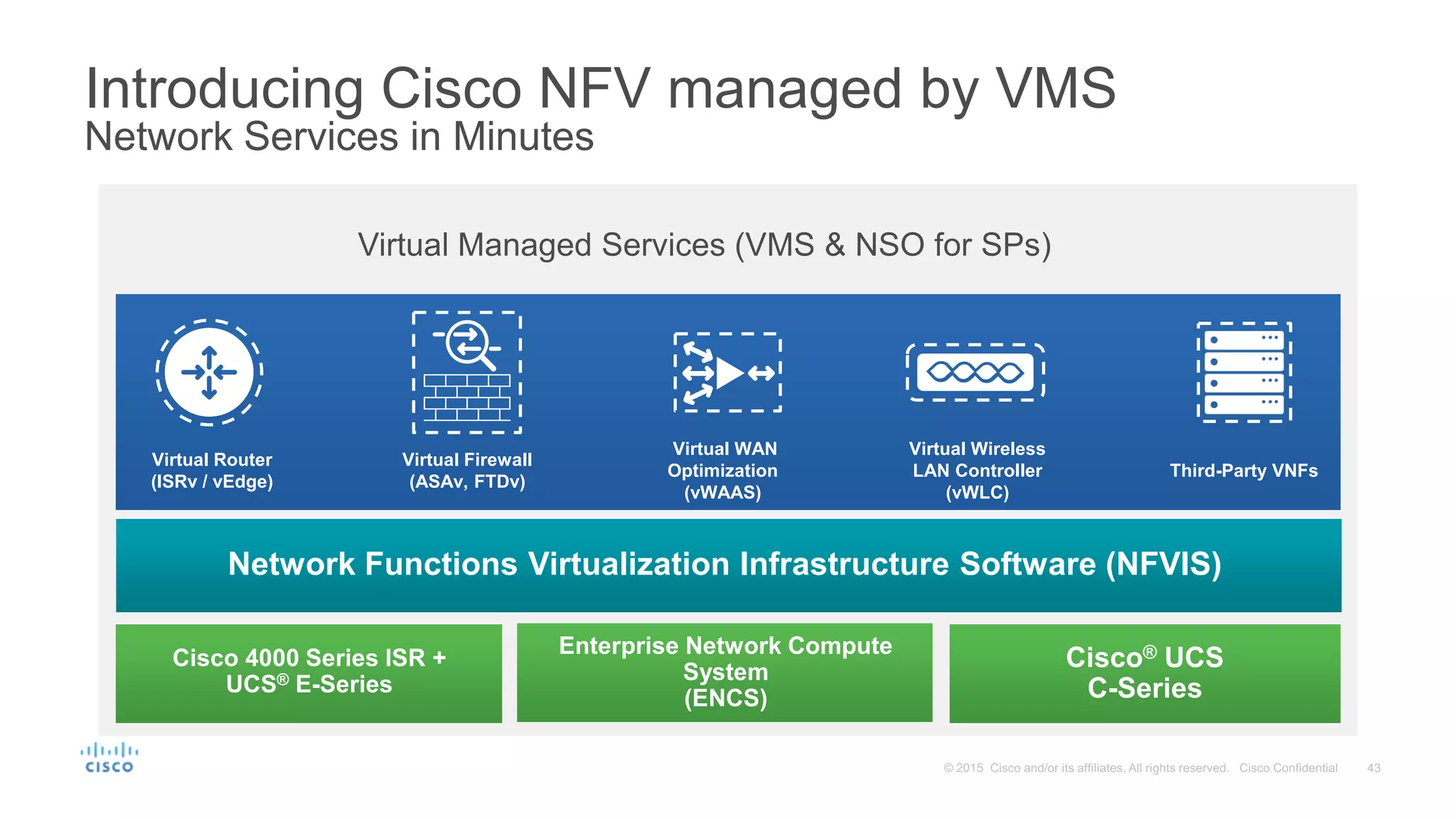
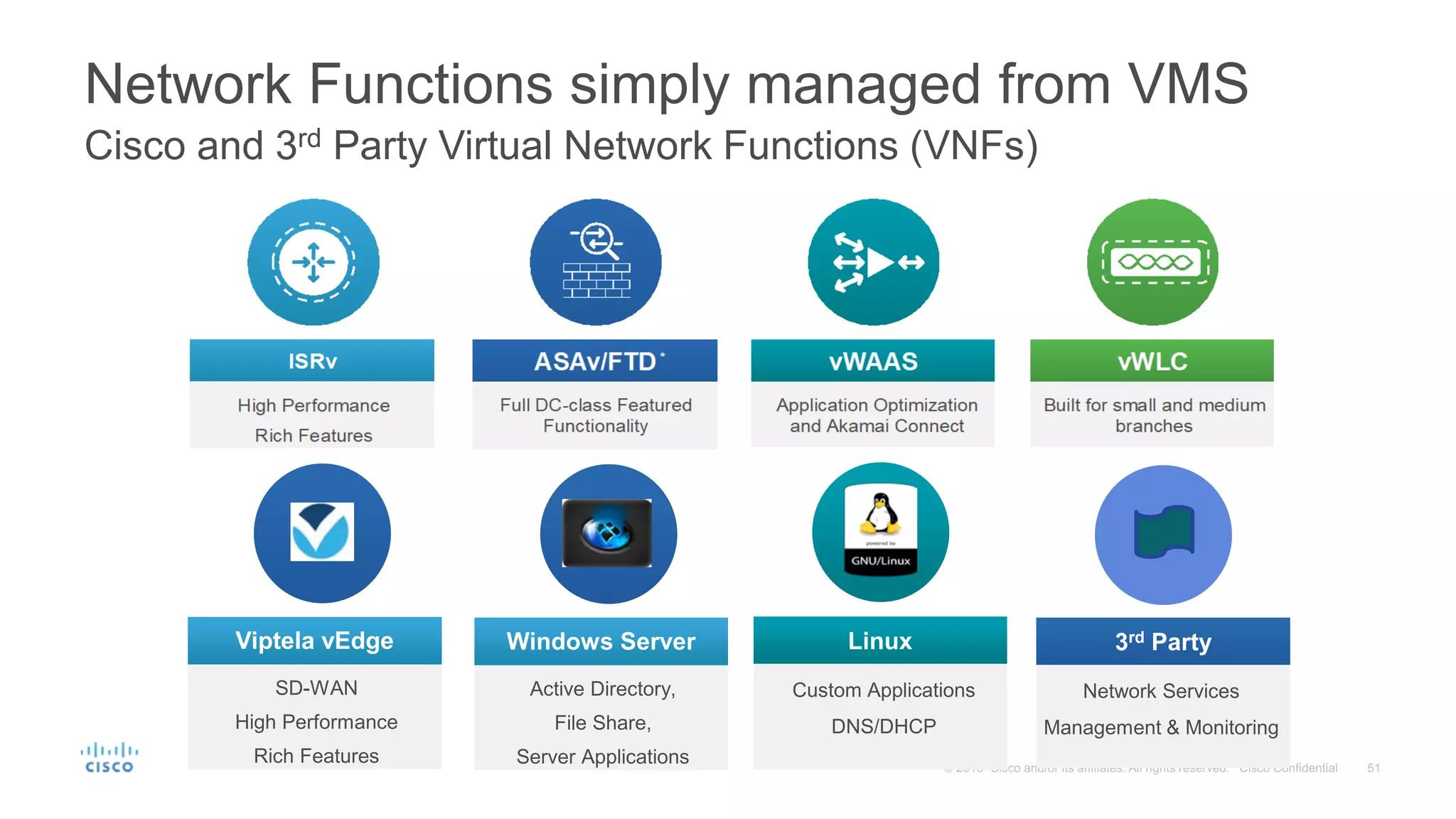
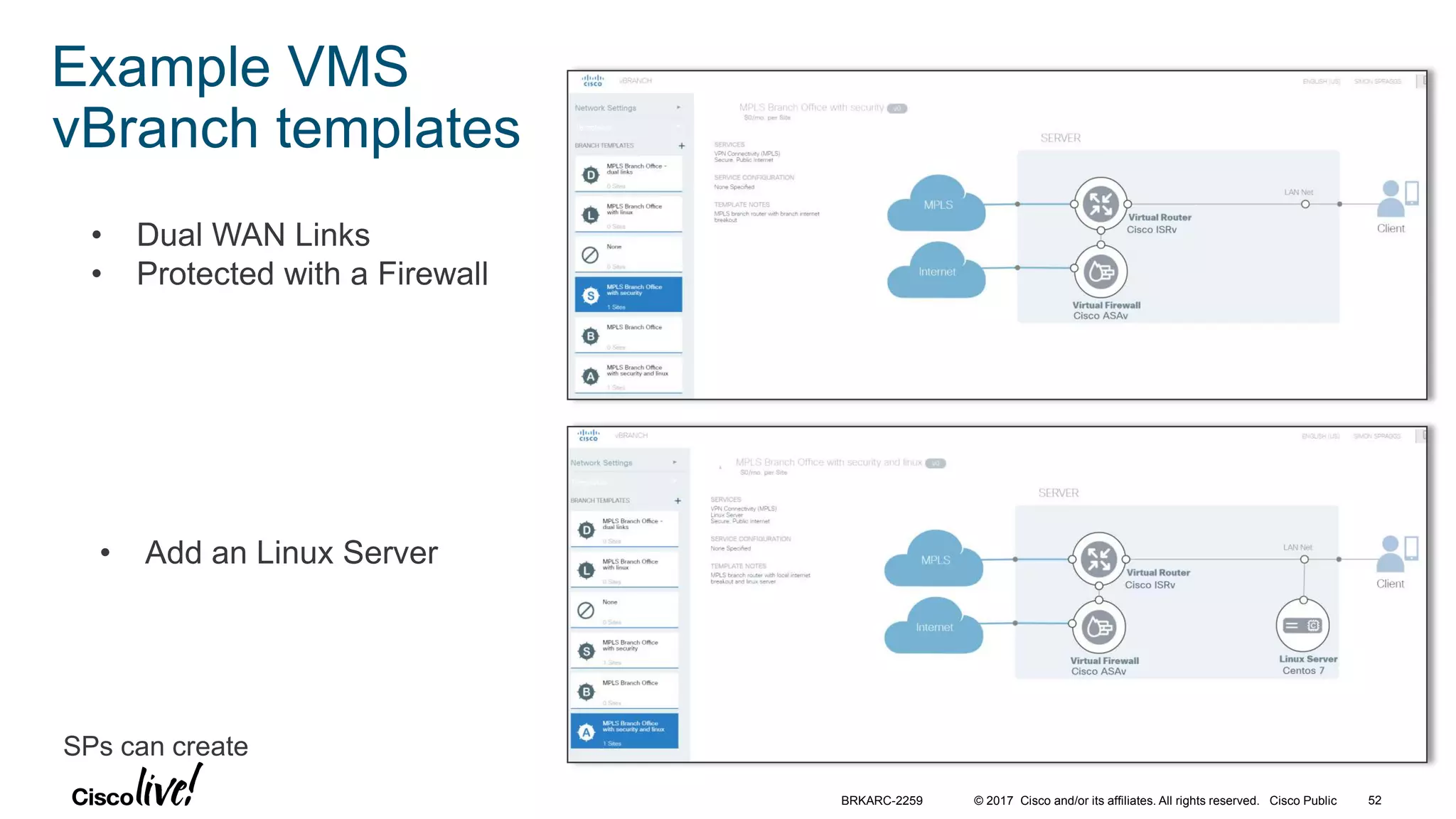
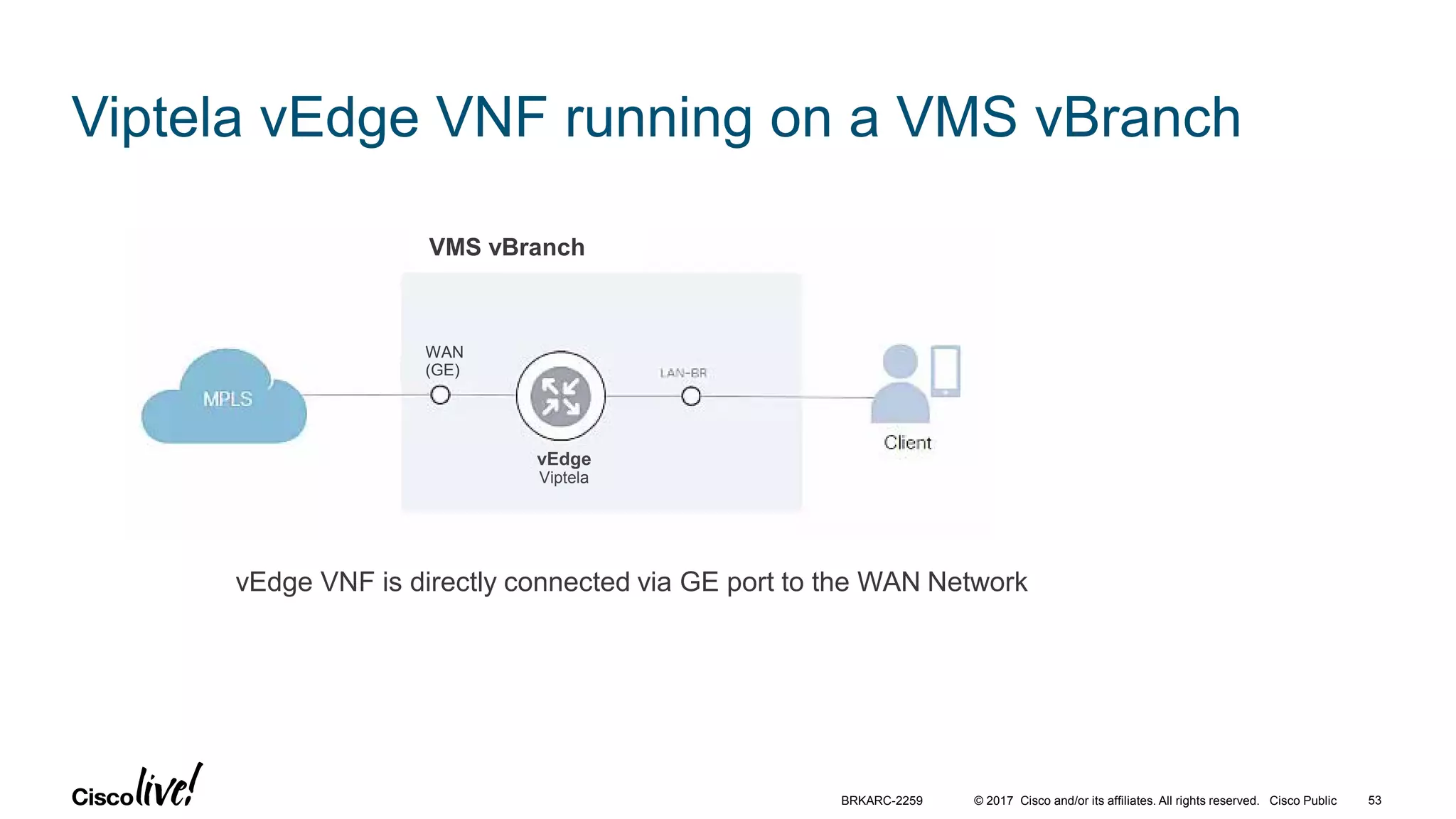
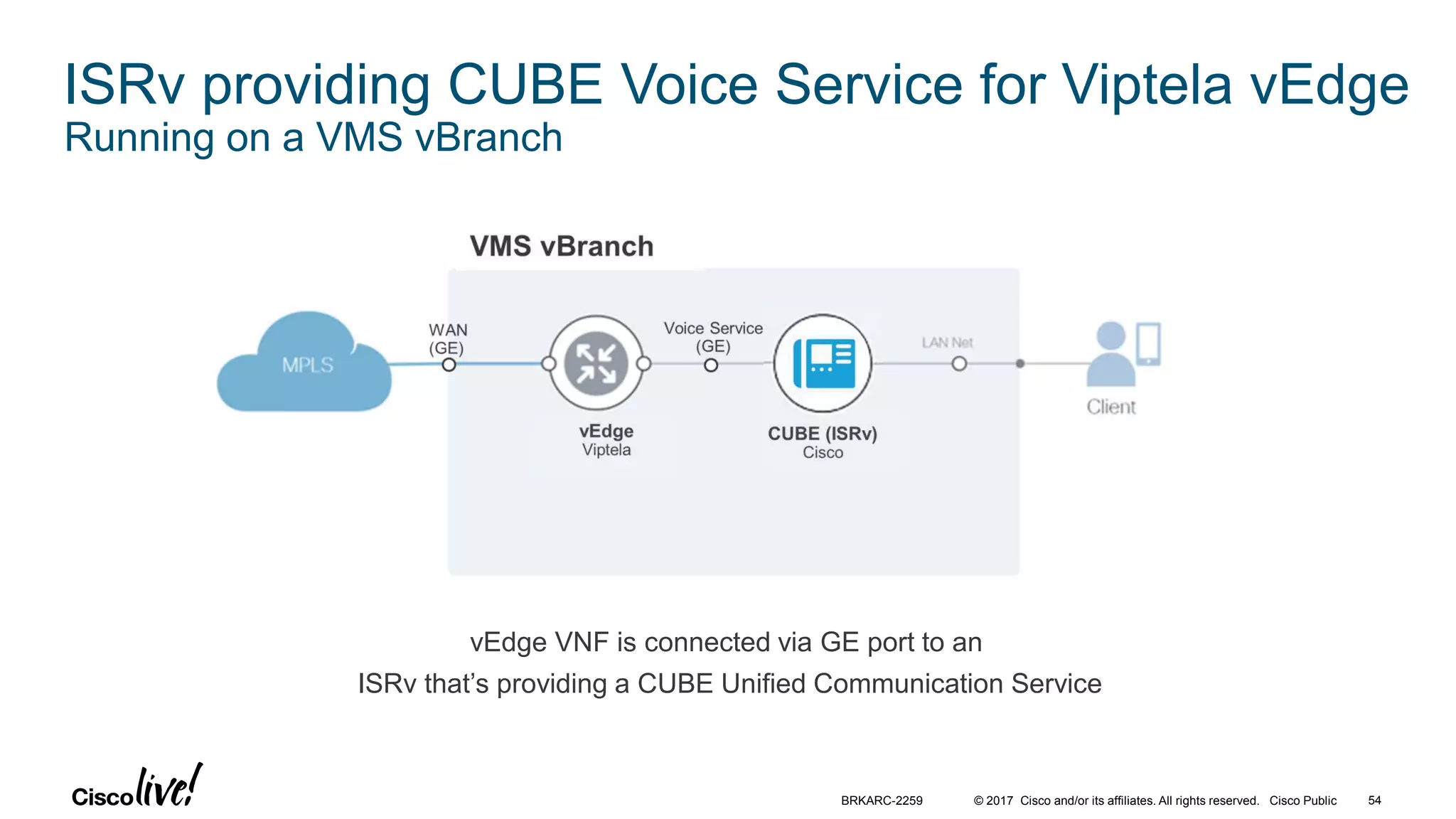
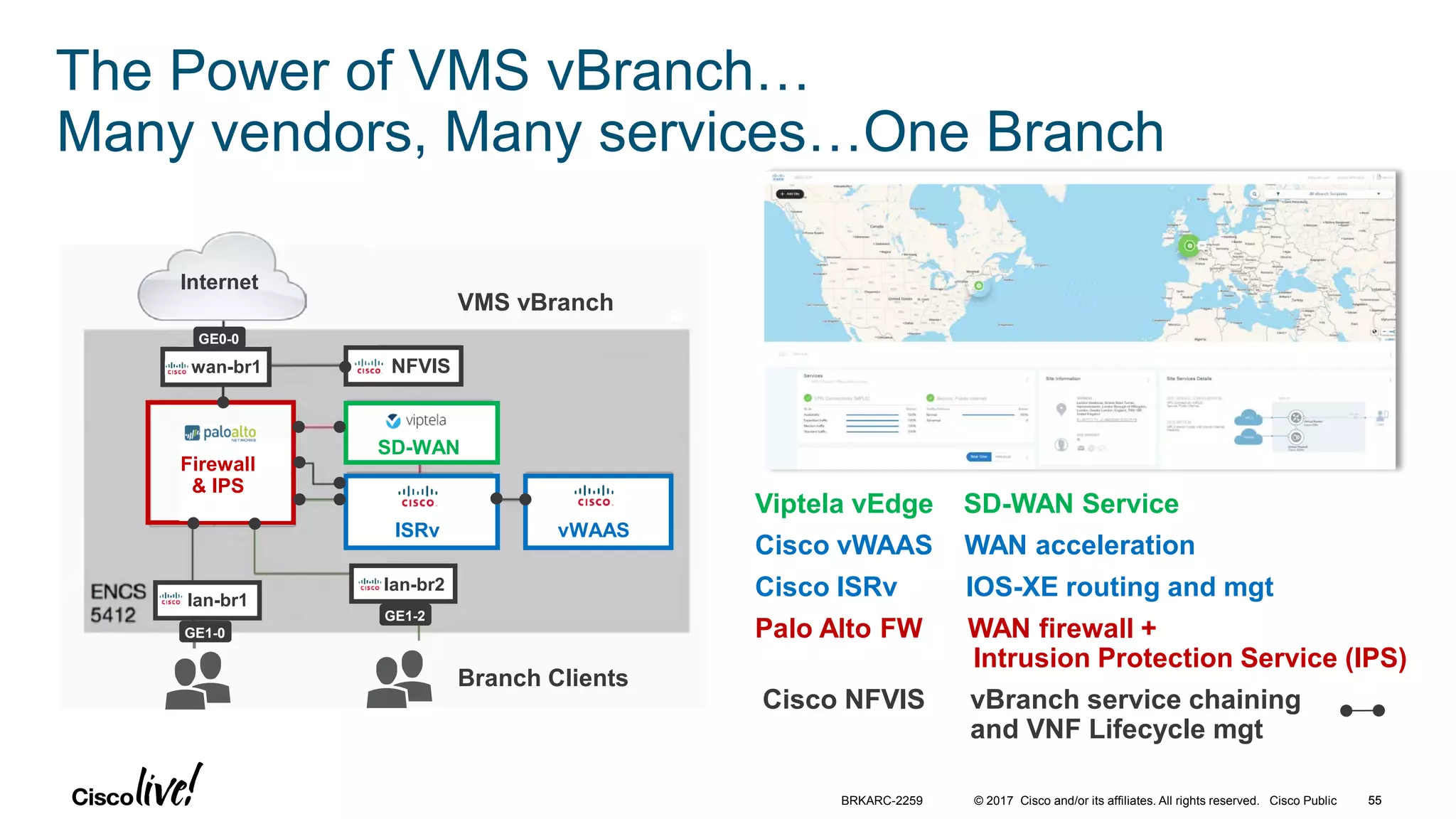
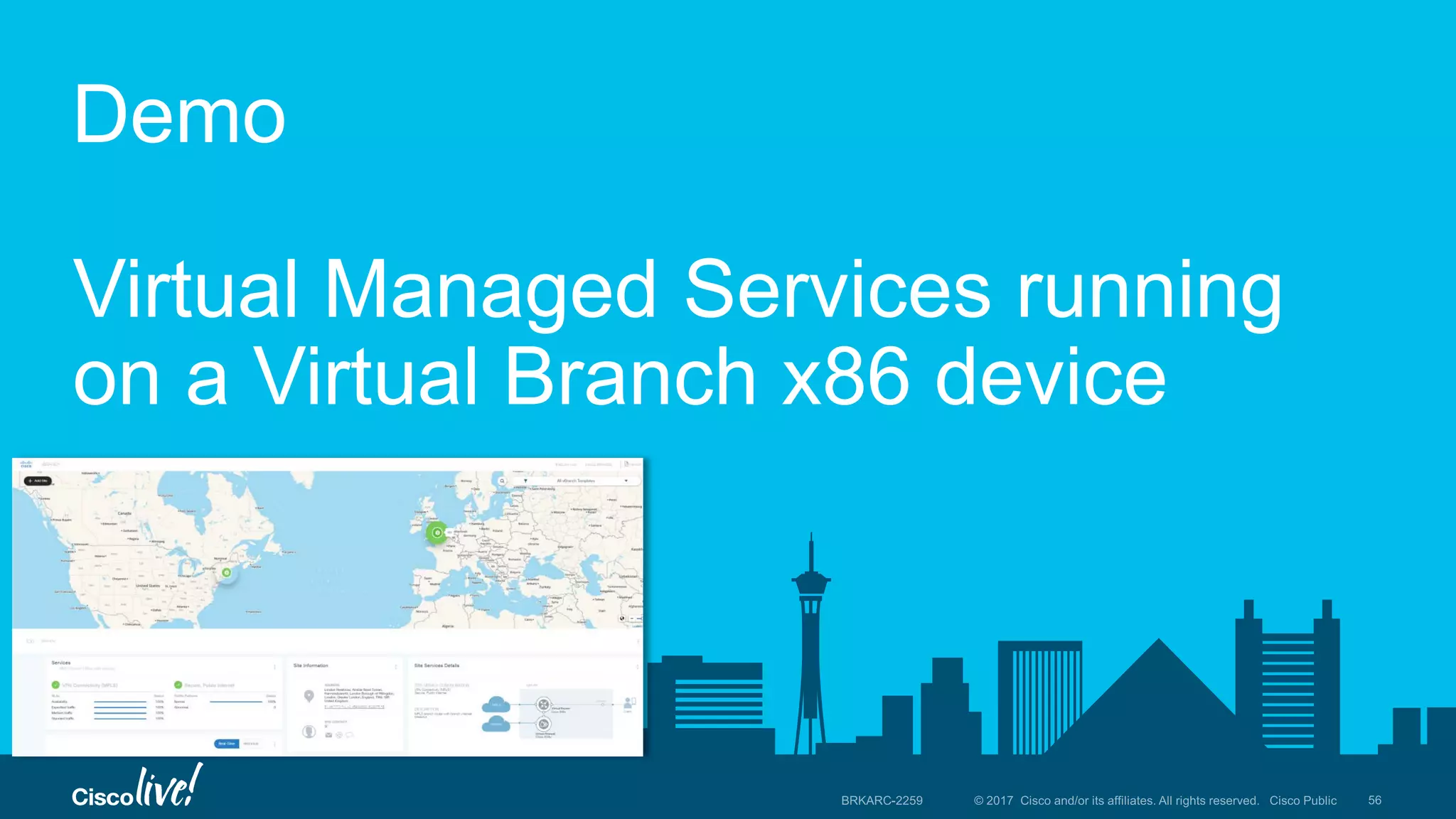
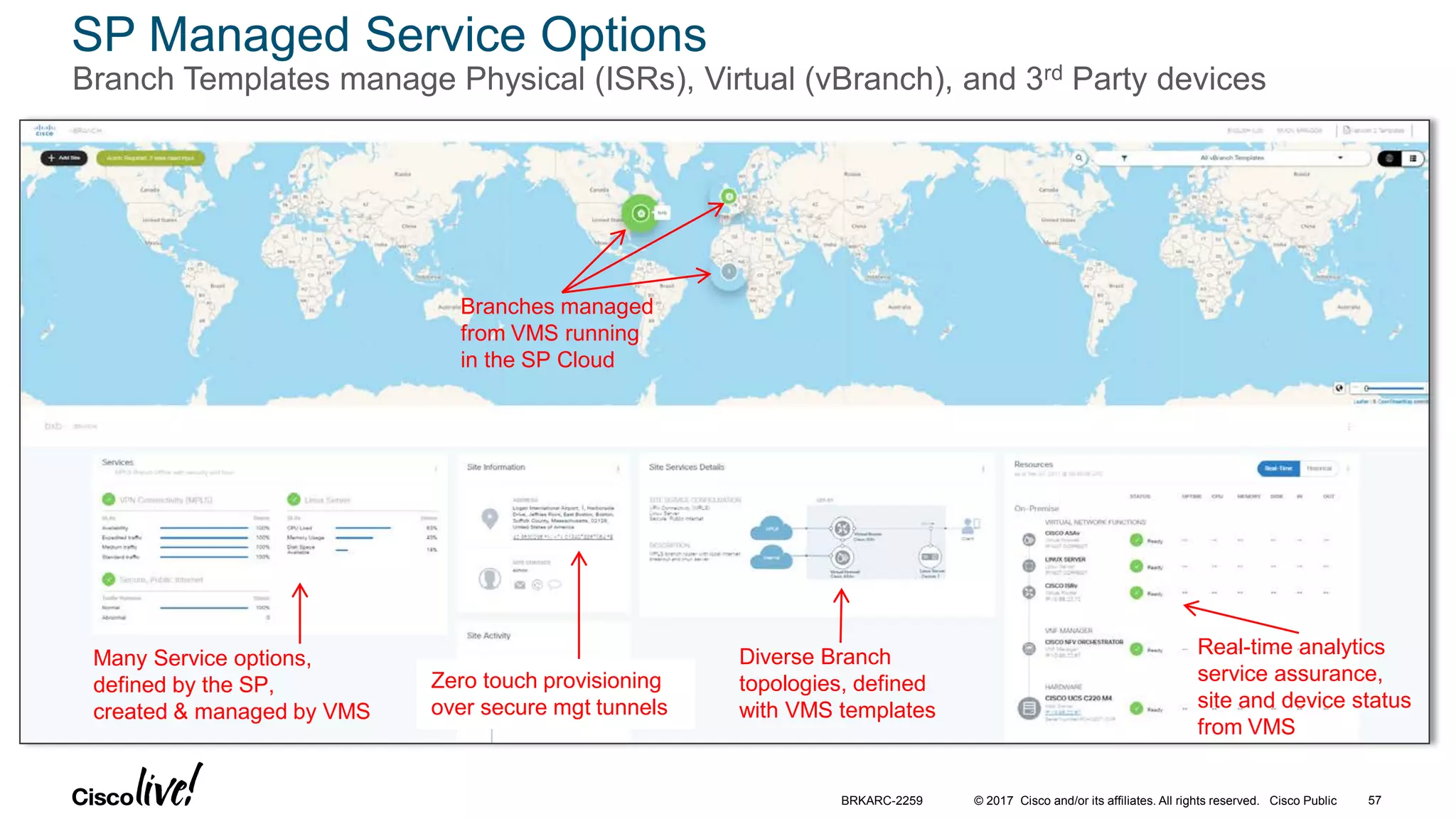
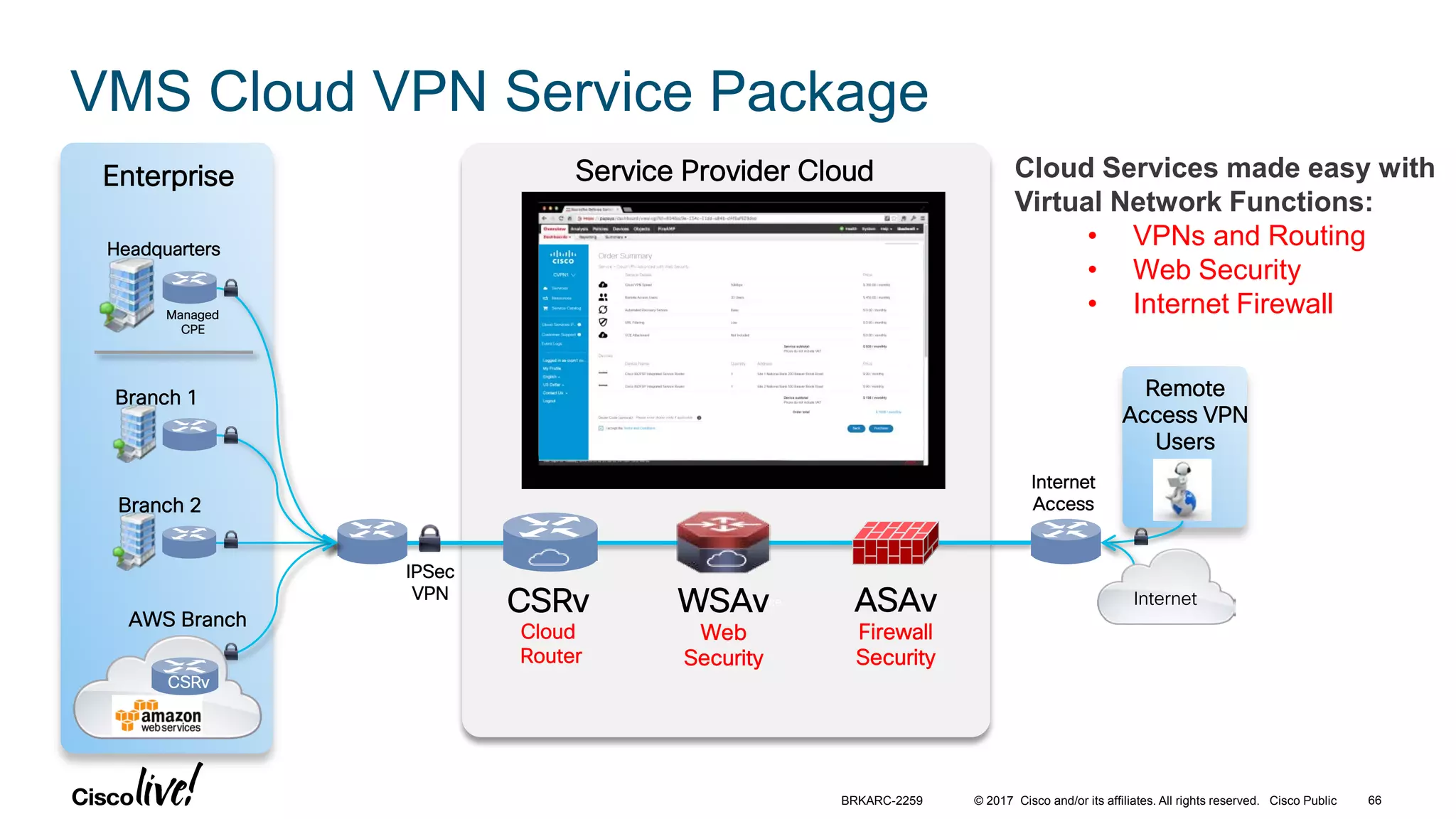
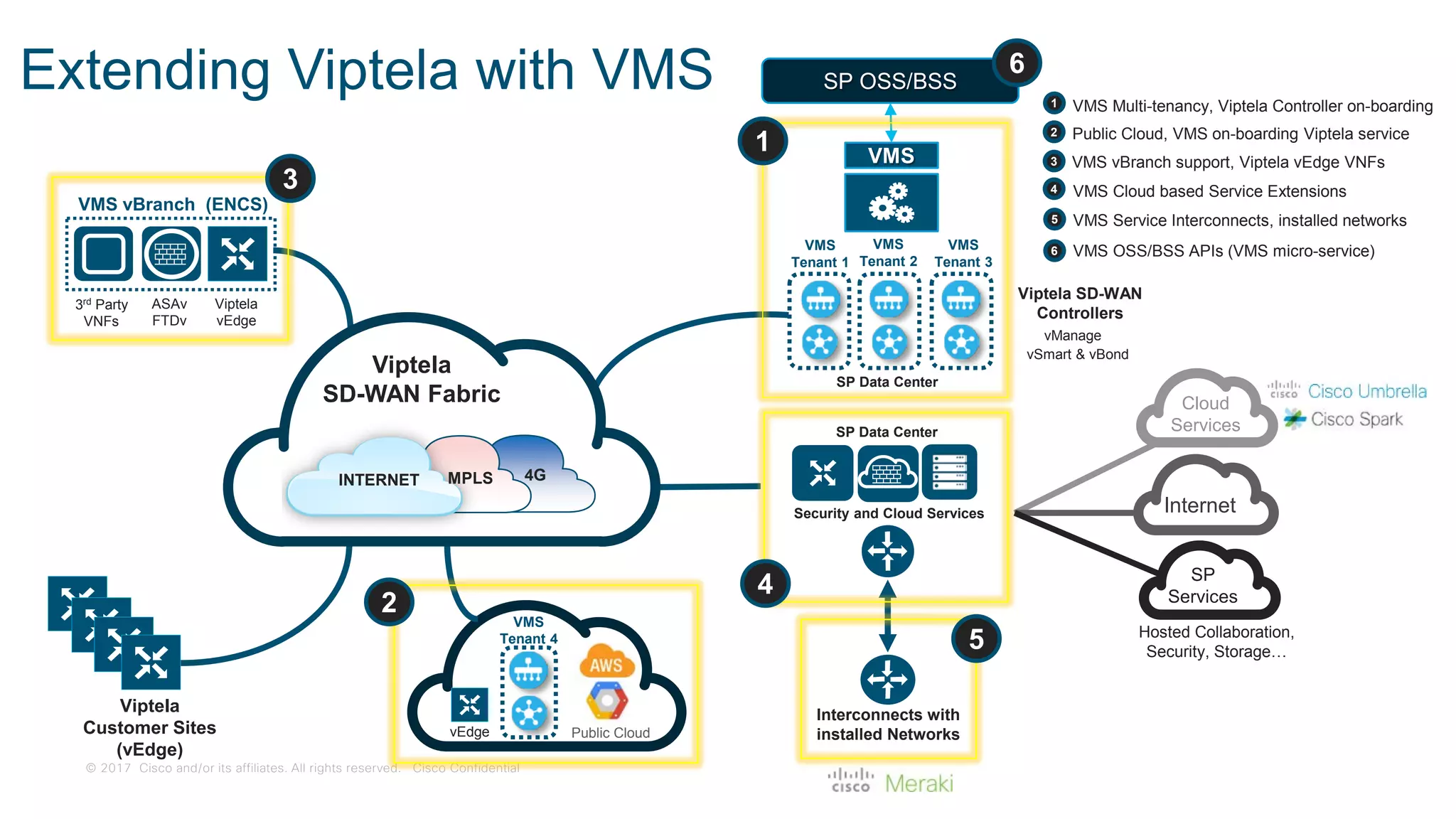
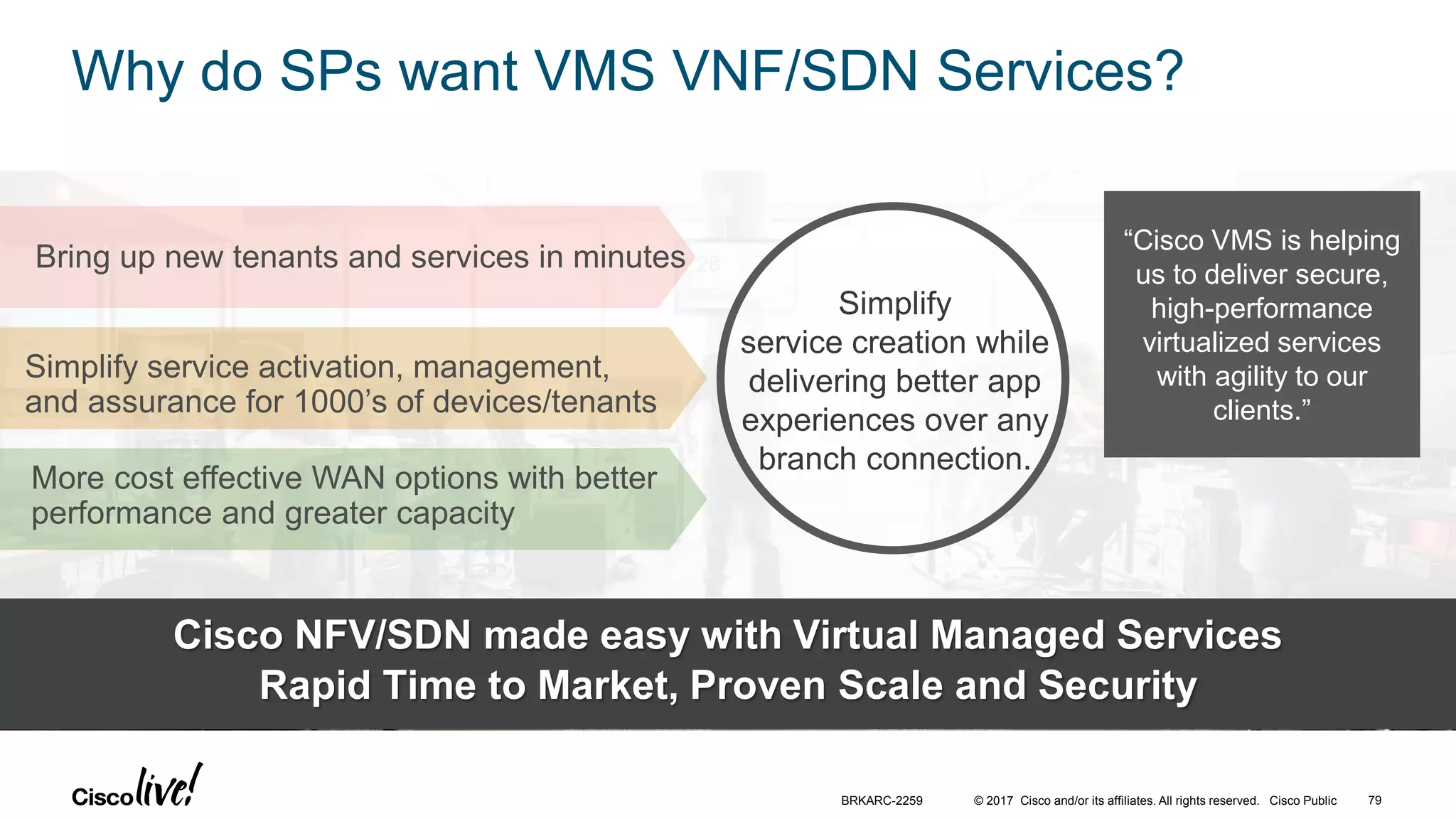
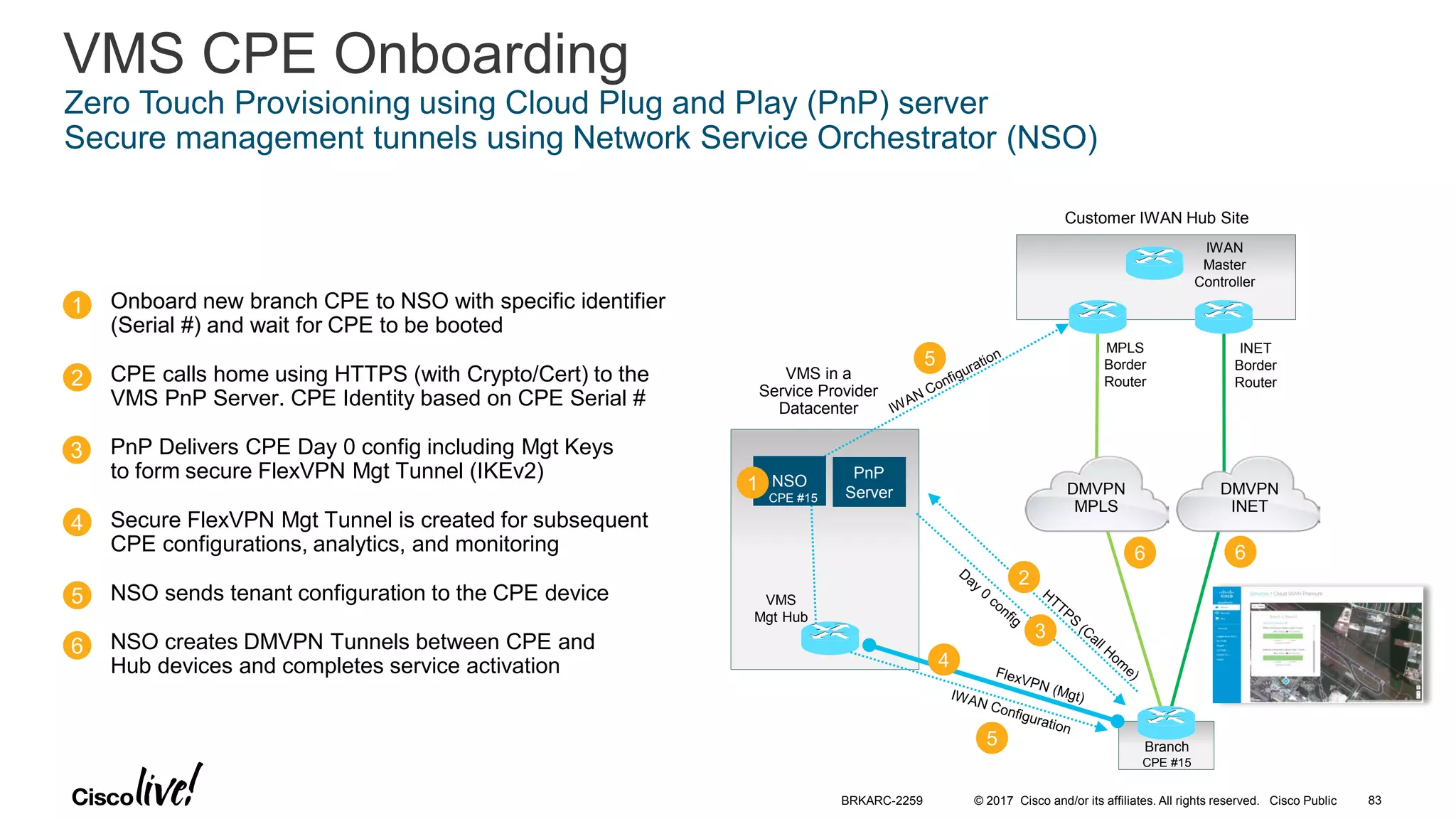
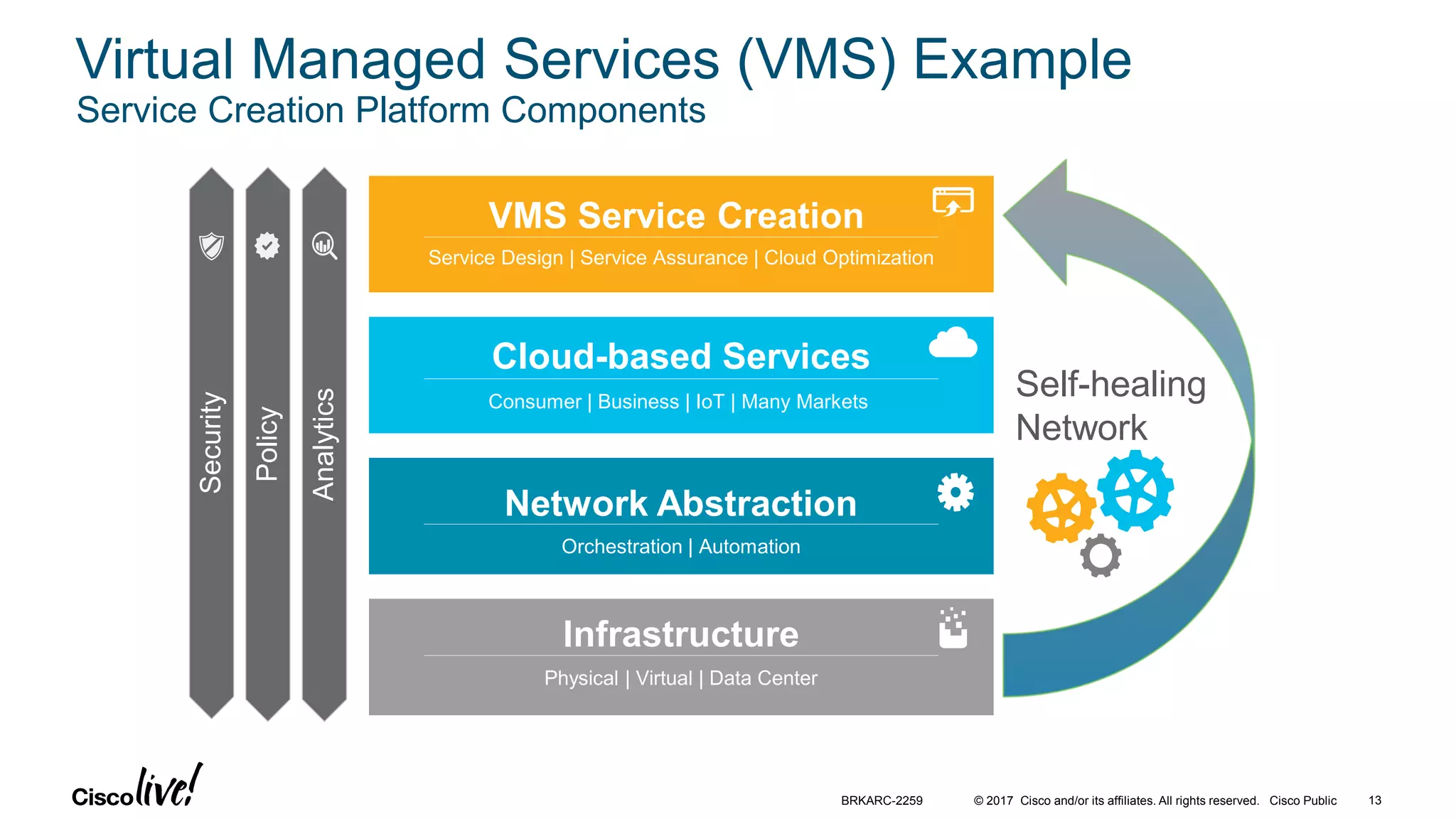
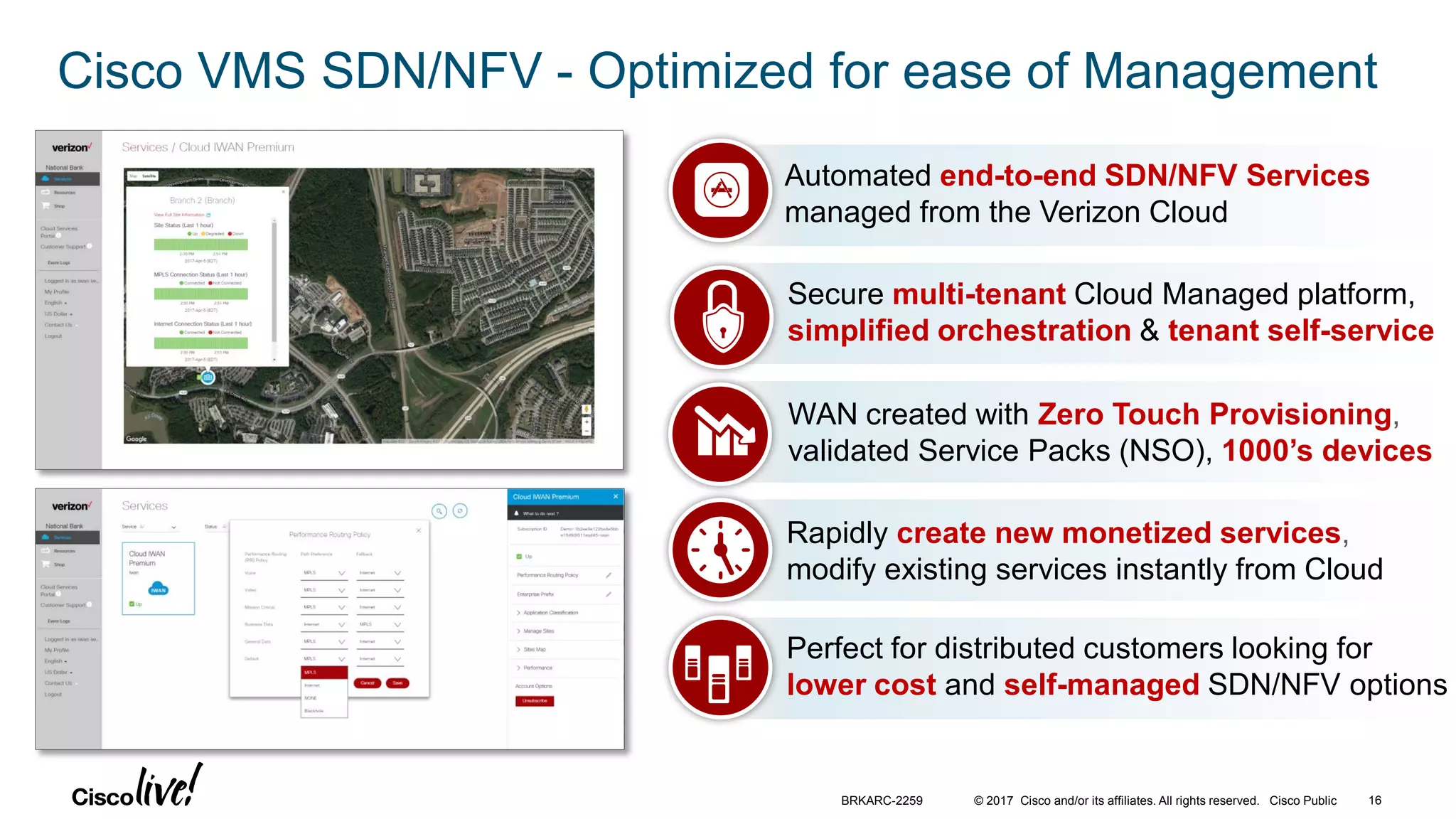
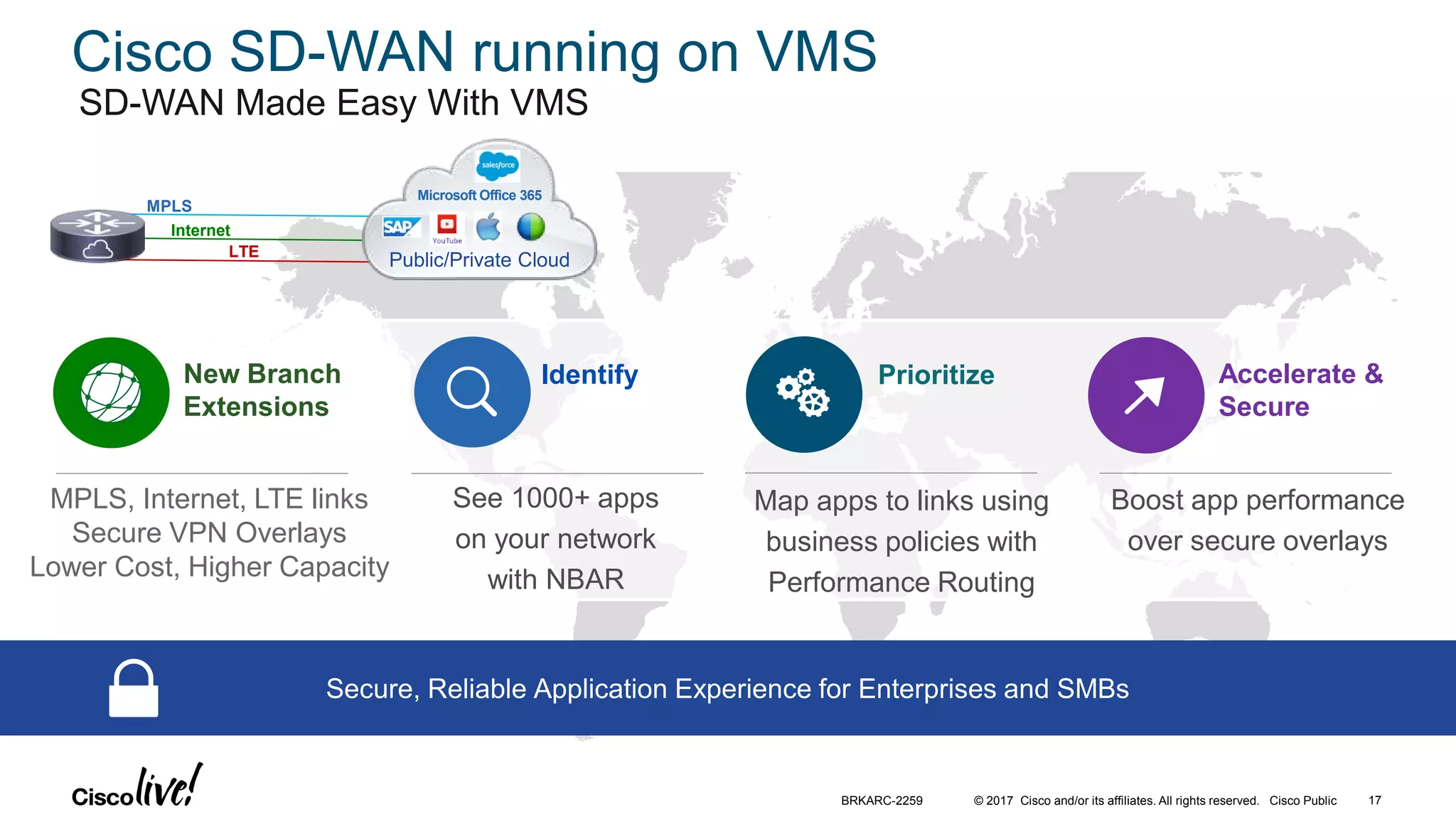
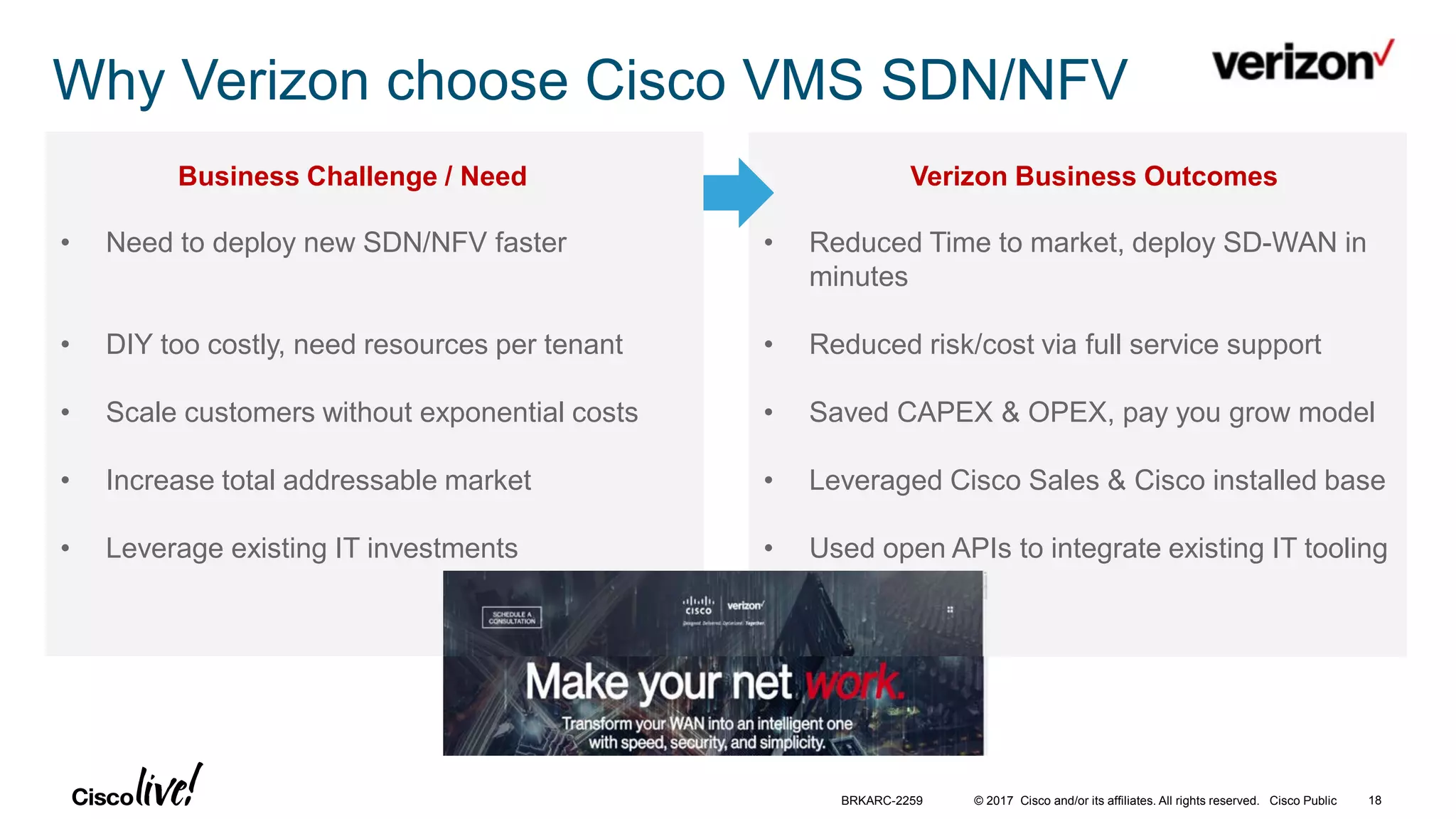
Cisco's Virtual Managed Services (VMS) platform allows service providers to orchestrate and manage SD-WAN and NFV services from the cloud. The demo showed how VMS can rapidly deploy SD-WAN services across multiple sites with MPLS, internet, and LTE links using Cisco routers. VMS provides a multi-tenant cloud management platform that reduces costs and time to market for service providers while improving services for enterprise customers.

![© 2017 Cisco and/or its affiliates. All rights reserved. Cisco Public
VMS Architecture - Simplified Cloud Management
VMS Operator/Admin Service
Secure Multi-tenant Cloud management,
Service creation platform for Enterprises & SMBs
VMS Customer Service
Self-service portal for service selection, device
analytics, traffic usage, and service configuration
[ OPTIONAL ]
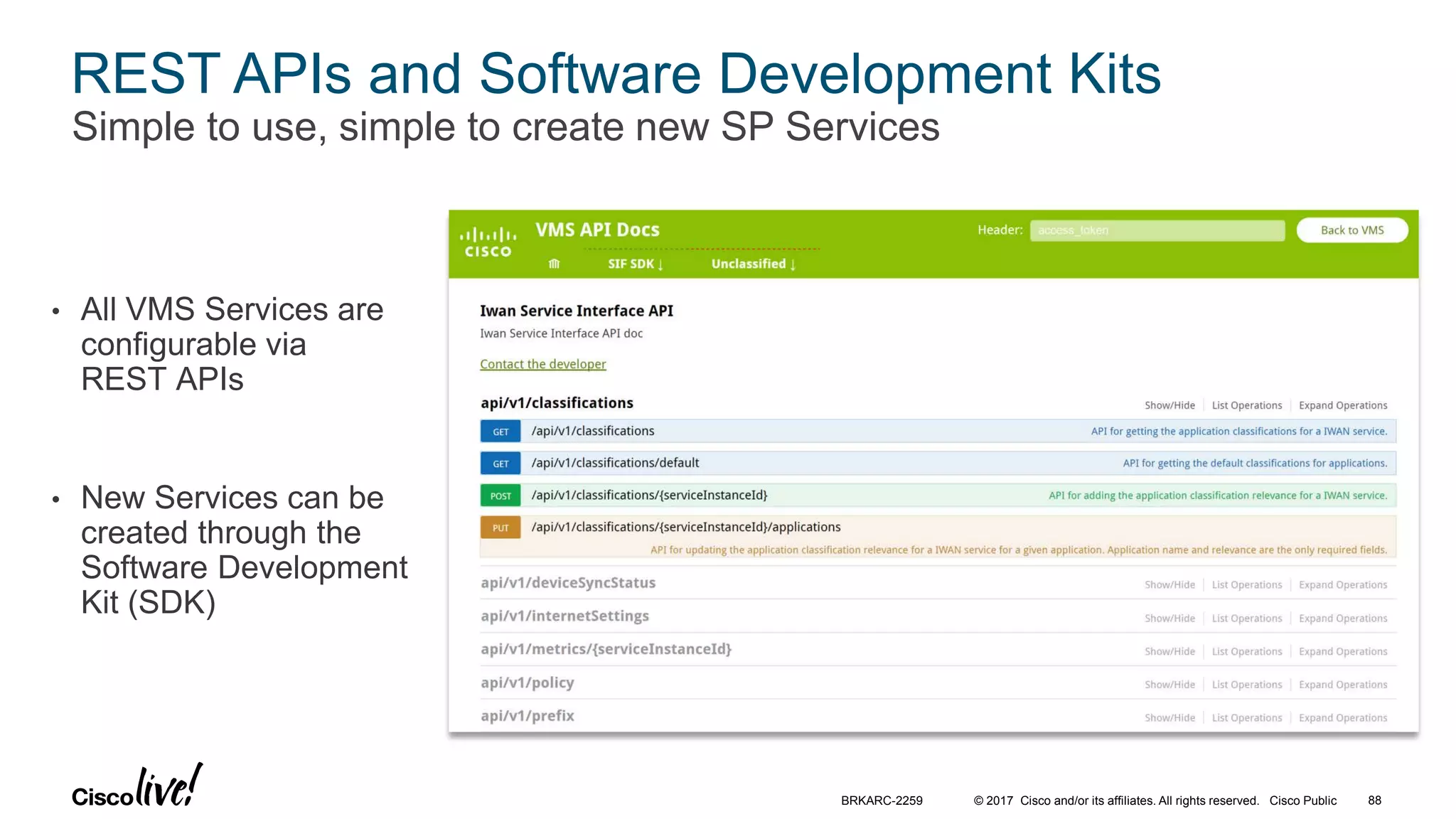
Open REST APIs and SDKs
Develop new Services using rich APIs,
Service SDKs, and world-class NSO
Customer equipment (On-premise and In-cloud)
SERVICE PROVIDER | CUSTOMER
ISRs &
ASRs
vBranch
VNFs
Multi-
VendorSecurity
BRKARC-2259 19](https://image.slidesharecdn.com/sdnnfvarchitectures-ciscoconnectcanada-oct2017-171031154658/75/Cisco-Connect-Toronto-2017-NFV-SDN-Platform-for-Orchestrating-Cloud-and-vBranch-Managed-Services-19-2048.jpg)