CIS2005 Principles of Information Security - Assignment 2 Pract.docx
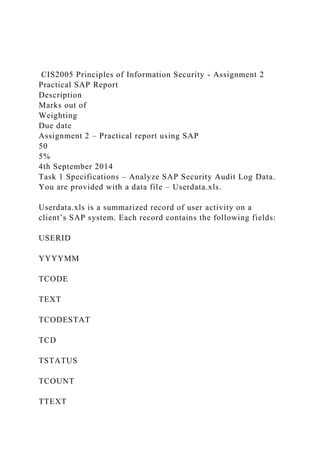
- 1. CIS2005 Principles of Information Security - Assignment 2 Practical SAP Report Description Marks out of Weighting Due date Assignment 2 – Practical report using SAP 50 5% 4th September 2014 Task 1 Specifications – Analyze SAP Security Audit Log Data. You are provided with a data file – Userdata.xls. Userdata.xls is a summarized record of user activity on a client’s SAP system. Each record contains the following fields: USERID YYYYMM TCODE TEXT TCODESTAT TCD TSTATUS TCOUNT TTEXT
- 2. YYYYMM describes when the user action took place. YYYYMM is useful for summarising user activity by month. TCODE refers to the transaction (option on the menu) performed by the user. TEXT describes the outcome of the action, including its success or failure. Some tcodes are blank. Accordingly, TCODESTAT is an invented transaction code for each action indicating whether the action was successful (-0) or failed (-1). TCD is the same as TCODESTAT, except there is no -0 or -1. TSTATUS indicates whether the action was successful or not (0/1). TCOUNT is the number of times the user has performed this action, with this outcome, in the month YYYYMM. TTEXT is the narrative description of the TCODE. Task 1 Requirements You can use software of your choice (spreadsheet, database, statistical package etc) to analyze the provided SAP security audit log data (Userdata.xls), generate appropriate reports and provide an analysis of your findings (hint this assignment 2 task 1 can be done using excel pivot tables or Microsoft Access database SQL queries). Of particular interest are the following reports: 1. Alphabetic list of all actions and their frequency by any selected user, e.g. USER-040. 2. List of users performing unsuccessful activities. 3. List of transaction codes performed, with their frequency by each user. 4. List of users engaging in security-related actions. 5. Top 10 users in terms of frequency of activity. 6. List of users who are dormant – in the range USER-001 to USER-050. 7. You should also produce at least 3 reports/charts/plots based on any of the above previous reports that summarise activity
- 3. over time using YYYYMM. Note: Submission of your assignment report documents (an excel spreadsheet for task 1 if you use a spreadsheet for task1 or an Access database if you use a database for task 1) will be via Ease Assignment 2 submission link PAGE 1 SAP_Security_Loguseridyyyymmftexttcodestattcdtstatustcounttt extUSER-001201403SU10Transaction SU10 StartedSU10- 0SU1001Mass Changes to User Master RecordsUSER- 001201403SESSPassword changed for user USER-001 in client 400pwdc-0pwdc01USER-001201403Logon Successful (Type=A)logn-0logn01USER-001201403SESSLogon Successful (Type=A)logn-0logn01USER-001201403User Logoffloff- 0loff01USER-001201403SESSLogon Failed (Reason = 3, Type = A)logn-1logn13USER-001201403SA38User Logoffloff- 0loff01USER-001201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn19USER-001201403SU03Transaction SU03 StartedSU03-0SU0301Maintain AuthorizationsUSER- 001201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER-001201403SE11Transaction SE11 StartedSE11-0SE1102ABAP/4 Dictionary MaintenanceUSER- 001201403SU01Transaction SU01 StartedSU01-0SU0104User MaintenanceUSER-001201403Start Transaction GL Failed- 111USER-001201403FS00Transaction FS00 StartedFS00- 0FS0005USER-001201403Start Transaction SOOO Failed- 111USER-001201403FB60Transaction FB60 StartedFB60- 0FB6002USER-001201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-001201403Start Transaction S090 Failed-111USER-001201403Start Transaction S009 Failed-111USER-002201403SA38Transaction SA38 StartedSA38-0SA3806ABAP reportingUSER- 002201403FK10Transaction FK10N StartedFK10-
- 4. 0FK1001Vendor Account BalanceUSER- 002201403SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER-002201403SE11Transaction SE11 StartedSE11-0SE1101ABAP/4 Dictionary MaintenanceUSER- 002201403SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER-002201403FS00Transaction FS00 StartedFS00-0FS0002USER-002201403FS00User Logoffloff- 0loff01USER-002201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn12USER-002201403SESSLogon Successful (Type=A)logn-0logn01USER-002201403User Logoffloff- 0loff01USER-002201403Logon Successful (Type=A)logn- 0logn01USER-002201403SESSPassword changed for user USER-002 in client 400pwdc-0pwdc01USER- 003201403SWUITransaction SWUI StartedSWUI- 0SWUI01Start WorkflowUSER-003201403SESSLogon Successful (Type=A)logn-0logn01USER-003201403Password changed for user USER-003 in client 400pwdc-0pwdc01USER- 003201403Logon Successful (Type=A)logn-0logn02USER- 003201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn16USER-003201403User Logoffloff-0loff02USER- 003201403FS00User Logoffloff-0loff01USER- 003201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-003201403SESSLogon Failed (Reason = 3, Type = A)logn-1logn12USER-003201403SESSPassword changed for user USER-003 in client 400pwdc-0pwdc01USER- 003201403FS00Transaction FS00 StartedFS00-0FS0002USER- 003201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-003201403SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER- 003201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 003201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 003201403FB60Transaction FB60 StartedFB60-0FB6002USER- 003201403SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-003201403SE43Transaction SE43N
- 5. StartedSE43-0SE4301Maintain Area MenuUSER- 003201403SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER-003201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER- 005201403SM50Transaction SM50 StartedSM50-0SM5001Work Process OverviewUSER-005201403ME21Transaction ME21N StartedME21-0ME2101Create Purchase OrderUSER- 005201403FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-005201403FV60Transaction FV60 StartedFV60-0FV6001USER-005201403SM30Transaction SM30 StartedSM30-0SM3002Call View MaintenanceUSER- 005201403F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER-005201403SA38Transaction SA38 StartedSA38-0SA3805ABAP reportingUSER- 005201403SE11Transaction SE11 StartedSE11- 0SE1107ABAP/4 Dictionary MaintenanceUSER- 005201403FS10Transaction FS10 StartedFS10-0FS1001G/L Account BalanceUSER-005201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 005201403FB03Transaction FB03 StartedFB03- 0FB0302Display DocumentUSER-005201403PPMDTransaction PPMDT StartedPPMD-0PPMD01Manager's DesktopUSER- 005201403FS00Transaction FS00 StartedFS00-0FS0004USER- 005201403ST22Transaction ST22 StartedST22- 0ST2201ABAP/4 Runtime Error AnalysisUSER- 005201403FB60Transaction FB60 StartedFB60-0FB6002USER- 005201403SSAATransaction SSAA StartedSSAA- 0SSAA01System Administration AssistantUSER- 005201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-005201403FBV3Transaction FBV3 StartedFBV3-0FBV301Display Parked DocumentUSER- 005201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-005201403Logon Successful (Type=A)logn-0logn03USER-005201403FS10User Logoffloff-0loff01USER-005201403SE11User Logoffloff- 0loff01USER-005201403User Logoffloff-0loff01USER-
- 6. 005201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-005201403SESSLogon Successful (Type=A)logn-0logn01USER-005201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER- 005201403SESSPassword changed for user USER-005 in client 400pwdc-0pwdc01USER-005201403FS00User Logoffloff- 0loff01USER-006201403SU3Transaction SU3 StartedSU3 - 0SU301Maintain Users Own DataUSER-006201403Logon Successful (Type=A)logn-0logn02USER-006201403User Logoffloff-0loff03USER-006201403SESSPassword changed for user USER-006 in client 400pwdc-0pwdc01USER- 006201403SU3User Master Record USER-006 ChangedSU03- 0SU0301Maintain AuthorizationsUSER-006201403SESSLogon Successful (Type=A)logn-0logn01USER- 006201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 006201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 006201403FS00Transaction FS00 StartedFS00-0FS0002USER- 006201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER-006201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER- 006201403F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER-006201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 006201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-006201403FB60Transaction FB60 StartedFB60-0FB6003USER-006201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER- 007201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-007201403SE43Transaction SE43N StartedSE43-0SE4302Maintain Area MenuUSER- 007201403SE11Transaction SE11 StartedSE11- 0SE1104ABAP/4 Dictionary MaintenanceUSER- 007201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-007201403FS00Transaction FS00
- 7. StartedFS00-0FS0002USER-007201403Start Transaction USR40 Failed-111USER-007201403FB60Transaction FB60 StartedFB60-0FB6002USER-007201403F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER- 007201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 007201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-007201403SM30Transaction SM30 StartedSM30-0SM3003Call View MaintenanceUSER- 007201403User Logoffloff-0loff02USER-007201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn11USER- 007201403SU3Transaction SU3 StartedSU3 -0SU302Maintain Users Own DataUSER-007201403SESSLogon Successful (Type=A)logn-0logn01USER-007201403SESSPassword changed for user USER-007 in client 400pwdc-0pwdc01USER- 007201403Logon Successful (Type=A)logn-0logn01USER- 007201403User Master Record USER-007 ChangedSU03- 0SU0301Maintain AuthorizationsUSER- 008201403SESSPassword changed for user USER-008 in client 400pwdc-0pwdc01USER-008201403Logon Successful (Type=A)logn-0logn01USER-008201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER- 008201403SE11User Logoffloff-0loff01USER-008201403User Logoffloff-0loff01USER-008201403SU3User Master Record USER-008 ChangedSU03-0SU0301Maintain AuthorizationsUSER-008201403SESSLogon Successful (Type=A)logn-0logn01USER-008201403SE11Transaction SE11 StartedSE11-0SE1101ABAP/4 Dictionary MaintenanceUSER- 008201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-008201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 008201403FS00Transaction FS00 StartedFS00-0FS0004USER- 008201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 008201403FB60Transaction FB60 StartedFB60-0FB6002USER- 009201403SA38Transaction SA38 StartedSA38-0SA3801ABAP
- 8. reportingUSER-009201403SU01Transaction SU01 StartedSU01- 0SU0101User MaintenanceUSER-009201403SE11Transaction SE11 StartedSE11-0SE1106ABAP/4 Dictionary MaintenanceUSER-009201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER- 009201403FS00Transaction FS00 StartedFS00-0FS0002USER- 009201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-009201403SU02Transaction SU02 StartedSU02-0SU0201Maintain Authorization ProfilesUSER- 009201403SESSLogon Failed (Reason = 3, Type = A)logn- 1logn11USER-009201403Logon Successful (Type=A)logn- 0logn02USER-009201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn13USER-009201403SU03Transaction SU03 StartedSU03-0SU0301Maintain AuthorizationsUSER- 009201403SESSPassword changed for user USER-009 in client 400pwdc-0pwdc02USER-009201403SE11User Logoffloff- 0loff01USER-009201403User Logoffloff-0loff01USER- 010201403Password changed for user USER-010 in client 400pwdc-0pwdc01USER-010201403SESSLogon Successful (Type=A)logn-0logn01USER-010201403SU3User Master Record USER-010 ChangedSU03-0SU0301Maintain AuthorizationsUSER-010201403User Logoffloff-0loff01USER- 010201403SE11User Logoffloff-0loff01USER-010201403Logon Successful (Type=A)logn-0logn01USER- 010201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-010201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER- 010201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 010201403FB60Transaction FB60 StartedFB60-0FB6005USER- 010201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-010201403FS00Transaction FS00 StartedFS00-0FS0002USER-010201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 010201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-010201403SE11Transaction SE11 StartedSE11-
- 9. 0SE1103ABAP/4 Dictionary MaintenanceUSER- 010201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-010201403Start Transaction ZMENU 10 Failed-111USER-010201403FK03Transaction FK03 StartedFK03-0FK0301Display Vendor (Accounting)USER- 010201403Start Transaction T000 Failed-111USER- 011201403FB60Transaction FB60 StartedFB60-0FB6007USER- 011201403Start Transaction 47611 Failed-111USER- 011201403Start Transaction 0001 Failed-111USER- 011201403FK10Transaction FK10N StartedFK10- 0FK1003Vendor Account BalanceUSER- 011201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-011201403Start Transaction 476111 Failed-111USER-011201403Start Transaction 476100 Failed- 111USER-011201403FS00Transaction FS00 StartedFS00- 0FS0001USER-011201403Logon Successful (Type=A)logn- 0logn01USER-011201403SESSPassword changed for user USER-011 in client 400pwdc-0pwdc01USER- 011201403FK10User Logoffloff-0loff01USER- 012201403SESSPassword changed for user USER-012 in client 400pwdc-0pwdc01USER-012201403SU3Transaction SU3 StartedSU3 -0SU303Maintain Users Own DataUSER- 012201403SU3User Master Record USER-012 ChangedSU03- 0SU0303Maintain AuthorizationsUSER-012201403SESSLogon Successful (Type=A)logn-0logn01USER-012201403User Logoffloff-0loff03USER-012201403Logon Successful (Type=A)logn-0logn02USER-012201403FB60Transaction FB60 StartedFB60-0FB6002USER-012201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 012201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-012201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER- 012201403SA38Transaction SA38 StartedSA38-0SA3801ABAP reportingUSER-012201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 012201403SU01Transaction SU01D StartedSU01-0SU0101User
- 10. MaintenanceUSER-012201403SBWPTransaction SBWP StartedSBWP-0SBWP01USER-012201403SE11Transaction SE11 StartedSE11-0SE1103ABAP/4 Dictionary MaintenanceUSER-012201403FS00Transaction FS00 StartedFS00-0FS0003USER-012201403Start Transaction DISPLAY USERS Failed-111USER-012201403Start Transaction USR04 Failed-111USER-012201403PFCGTransaction PFCG StartedPFCG-0PFCG01Activity Group MaintenanceUSER- 013201403FS00Transaction FS00 StartedFS00-0FS0001USER- 013201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER-013201403SESSPassword changed for user USER-013 in client 400pwdc-0pwdc01USER- 013201403FK01User Logoffloff-0loff01USER-013201403Logon Successful (Type=A)logn-0logn01USER- 014201403SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER-014201403SU01User Logoffloff- 0loff01USER-014201403SU01Transaction SU01 StartedSU01- 0SU0101User MaintenanceUSER-014201403SESSLogon Successful (Type=A)logn-0logn01USER- 014201403SESSPassword changed for user USER-014 in client 400pwdc-0pwdc01USER-014201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER- 014201403FS00Transaction FS00 StartedFS00-0FS0003USER- 014201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 014201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-014201403FB60Transaction FB60 StartedFB60- 0FB6002USER-014201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 014201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 014201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-015201403SE11Transaction SE11 StartedSE11-0SE1102ABAP/4 Dictionary MaintenanceUSER- 015201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-015201403FS00Transaction FS00
- 11. StartedFS00-0FS0002USER-015201403FB60Transaction FB60 StartedFB60-0FB6003USER-015201403SUPCTransaction SUPC StartedSUPC-0SUPC01Profiles for activity groupsUSER- 015201403SESSPassword changed for user USER-015 in client 400pwdc-0pwdc01USER-015201403SESSLogon Successful (Type=A)logn-0logn02USER-015201403User Logoffloff- 0loff01USER-015201403SE11User Logoffloff-0loff01USER- 015201403FB60User Logoffloff-0loff01USER-015201403Logon Successful (Type=A)logn-0logn01USER-017201403SESSLogon Successful (Type=A)logn-0logn01USER-017201403Logon Successful (Type=A)logn-0logn01USER- 017201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-017201403SESSPassword changed for user USER-017 in client 400pwdc-0pwdc01USER- 017201403SE11User Logoffloff-0loff01USER-017201403User Logoffloff-0loff01USER-017201403SE43Transaction SE43N StartedSE43-0SE4303Maintain Area MenuUSER- 017201403FS10Transaction FS10 StartedFS10-0FS1001G/L Account BalanceUSER-017201403FB03Transaction FB03 StartedFB03-0FB0301Display DocumentUSER- 017201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 017201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-017201403FB60Transaction FB60 StartedFB60- 0FB6002USER-017201403FS00Transaction FS00 StartedFS00- 0FS0001USER-017201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER- 017201403SE11Transaction SE11 StartedSE11- 0SE1104ABAP/4 Dictionary MaintenanceUSER- 017201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-017201403F-02Transaction F-02 StartedF-02-0F-0202Enter G/L Account PostingUSER- 018201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-018201403SA38Transaction SA38 StartedSA38-0SA3804ABAP reportingUSER- 018201403FS10Transaction FS10 StartedFS10-0FS1001G/L
- 12. Account BalanceUSER-018201403FB03Transaction FB03 StartedFB03-0FB0301Display DocumentUSER- 018201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-018201403Start Transaction T000 Failed-111USER-018201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 018201403FS00Transaction FS00 StartedFS00-0FS0005USER- 018201403F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER-018201403FB60Transaction FB60 StartedFB60-0FB6004USER-018201403SE11Transaction SE11 StartedSE11-0SE1103ABAP/4 Dictionary MaintenanceUSER- 018201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-018201403SE13Transaction SE13 StartedSE13-0SE1301Maintain Technical Settings (Tables)USER-018201403SU01Transaction SU01 StartedSU01- 0SU0104User MaintenanceUSER-018201403SU02Transaction SU02 StartedSU02-0SU0201Maintain Authorization ProfilesUSER-018201403SESSLogon Successful (Type=A)logn- 0logn01USER-018201403SESSPassword changed for user USER-018 in client 400pwdc-0pwdc01USER-018201403Logon Failed (Reason = 1, Type = A)logn-1logn11USER- 018201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-018201403SE11User Logoffloff-0loff01USER- 018201403Logon Successful (Type=A)logn-0logn01USER- 018201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-018201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-018201403SU3User Master Record USER-018 ChangedSU03-0SU0301Maintain AuthorizationsUSER-018201403User Logoffloff-0loff01USER- 018201403SU03Transaction SU03 StartedSU03- 0SU0301Maintain AuthorizationsUSER-02201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn11USER- 020201403SU02Transaction SU02 StartedSU02- 0SU0201Maintain Authorization ProfilesUSER-020201403User Logoffloff-0loff04USER-020201403SXDAStart Transaction SXDA FailedSXDA-1SXDA11SAPDXfer: Control CenterUSER-
- 13. 020201403Logon Successful (Type=A)logn-0logn02USER- 020201403SESSLogon Successful (Type=A)logn- 0logn02USER-020201403SU01Transaction SU01 StartedSU01- 0SU0103User MaintenanceUSER-020201403SU01Transaction SU01D StartedSU01-0SU0103User MaintenanceUSER- 020201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-020201403SESSPassword changed for user USER-020 in client 400pwdc-0pwdc01USER- 020201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER-020201403FS00Transaction FS00 StartedFS00-0FS0004USER-020201403SBWPTransaction SBWP StartedSBWP-0SBWP01USER- 020201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-020201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 020201403SE43Transaction SE43N StartedSE43- 0SE4303Maintain Area MenuUSER-020201403SA38Transaction SA38 StartedSA38-0SA38016ABAP reportingUSER- 020201403FB60Transaction FB60 StartedFB60-0FB6004USER- 020201403SE11Transaction SE11 StartedSE11- 0SE1106ABAP/4 Dictionary MaintenanceUSER-020201403Start Transaction RSPARAM Failed-111USER-020201403Start Transaction ABAP RSPARAM Failed-111USER- 021201403SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-021201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 021201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-021201403SESSLogon Successful (Type=A)logn-0logn01USER-021201403SE11User Logoffloff- 0loff01USER-021201403Password changed for user USER-021 in client 400pwdc-0pwdc01USER-022201403User Logoffloff- 0loff01USER-022201403SESSPassword changed for user USER-022 in client 400pwdc-0pwdc01USER- 022201403SUGRTransaction SUGR StartedSUGR- 0SUGR01USER-022201403SU3Transaction SU3 StartedSU3 - 0SU301Maintain Users Own DataUSER-022201403SESSLogon
- 14. Successful (Type=A)logn-0logn01USER-022201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn15USER- 022201403FK10User Logoffloff-0loff01USER- 022201403SESSLogon Failed (Reason = 3, Type = A)logn- 1logn11USER-022201403SU3User Master Record USER-022 ChangedSU03-0SU0301Maintain AuthorizationsUSER- 022201403SU01Transaction SU01D StartedSU01-0SU0103User MaintenanceUSER-022201403FS00User Logoffloff- 0loff03USER-022201403SE11User Logoffloff-0loff01USER- 022201403Logon Failed (Reason = 3, Type = A)logn- 1logn11USER-022201403FB60User Logoffloff-0loff01USER- 022201403Logon Successful (Type=A)logn-0logn06USER- 022201403SE11Transaction SE11 StartedSE11- 0SE1105ABAP/4 Dictionary MaintenanceUSER- 022201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-022201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 022201403FS00Transaction FS00 StartedFS00-0FS0006USER- 022201403FK01Transaction FK01 StartedFK01-0FK0105Create Vendor (Accounting)USER-022201403SA38Transaction SA38 StartedSA38-0SA3804ABAP reportingUSER- 022201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 022201403FB60Transaction FB60 StartedFB60-0FB6005USER- 024201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-024201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-024201403Start Transaction SOOO Failed-111USER- 024201403SBWPTransaction SBWP StartedSBWP- 0SBWP03USER-024201403SE11Transaction SE11 StartedSE11-0SE1105ABAP/4 Dictionary MaintenanceUSER- 024201403FB60Transaction FB60 StartedFB60-0FB6003USER- 024201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-024201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 024201403F-02Transaction F-02 StartedF-02-0F-0202Enter G/L
- 15. Account PostingUSER-024201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 024201403FS00Transaction FS00 StartedFS00-0FS0004USER- 024201403SU3User Master Record USER-024 ChangedSU03- 0SU0301Maintain AuthorizationsUSER-024201403Logon Failed (Reason = 1, Type = A)logn-1logn12USER- 024201403SESSUser Logoffloff-0loff01USER- 024201403FS00User Logoffloff-0loff01USER- 024201403SESSPassword changed for user USER-024 in client 400pwdc-0pwdc03USER-024201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 024201403SESSLogon Failed (Reason = 3, Type = A)logn- 1logn13USER-024201403SU01Transaction SU01 StartedSU01- 0SU0101User MaintenanceUSER-024201403User Logoffloff- 0loff02USER-024201403Logon Successful (Type=A)logn- 0logn03USER-024201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn15USER-024201403SE11User Logoffloff- 0loff01USER-024201403SESSLogon Successful (Type=A)logn- 0logn02USER-024201403SU3Transaction SU3 StartedSU3 - 0SU301Maintain Users Own DataUSER-025201403SESSLogon Successful (Type=A)logn-0logn03USER- 025201403SU01Transaction SU01 StartedSU01-0SU0103User MaintenanceUSER-025201403User Logoffloff-0loff02USER- 025201403SESSPassword changed for user USER-025 in client 400pwdc-0pwdc01USER-025201403SBWPUser Logoffloff- 0loff01USER-025201403SU03Transaction SU03 StartedSU03- 0SU0301Maintain AuthorizationsUSER- 025201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-025201403SBWPTransaction SBWP StartedSBWP-0SBWP02USER-025201403SE11Transaction SE11 StartedSE11-0SE1103ABAP/4 Dictionary MaintenanceUSER-025201403SA38Transaction SA38 StartedSA38-0SA3801ABAP reportingUSER- 025201403PFCGTransaction PFCG StartedPFCG- 0PFCG01Activity Group MaintenanceUSER- 026201403FK01Transaction FK01 StartedFK01-0FK0102Create
- 16. Vendor (Accounting)USER-026201403FB60Transaction FB60 StartedFB60-0FB6002USER-026201403F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER- 026201403FBL1Transaction FBL1N StartedFBL1- 0FBL101Display Vendor Line ItemsUSER- 026201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER-026201403FS00Transaction FS00 StartedFS00-0FS00010USER-026201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 026201403FK05Transaction FK05 StartedFK05-0FK0503Block Vendor (Accounting)USER-026201403FB03Transaction FB03 StartedFB03-0FB0301Display DocumentUSER- 026201403SE11Transaction SE11 StartedSE11- 0SE1106ABAP/4 Dictionary MaintenanceUSER- 026201403FS10Transaction FS10 StartedFS10-0FS1001G/L Account BalanceUSER-026201403SA38Transaction SA38 StartedSA38-0SA3805ABAP reportingUSER- 026201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-026201403User Logoffloff- 0loff02USER-026201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn11USER-026201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 026201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-026201403SESSPassword changed for user USER-026 in client 400pwdc-0pwdc01USER- 026201403Logon Successful (Type=A)logn-0logn01USER- 026201403SESSLogon Successful (Type=A)logn- 0logn01USER-027201403SE11User Logoffloff-0loff01USER- 027201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-027201403SE43User Logoffloff- 0loff01USER-027201403SESSPassword changed for user USER-027 in client 400pwdc-0pwdc01USER-027201403Logon Successful (Type=A)logn-0logn02USER- 027201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER-027201403Start Transaction 8500 Failed-111USER-027201403SU01Transaction
- 17. SU01D StartedSU01-0SU0106User MaintenanceUSER- 027201403FS00Transaction FS00 StartedFS00-0FS0003USER- 027201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-027201403FB60Transaction FB60 StartedFB60-0FB6002USER-027201403FK01Transaction FK01 StartedFK01-0FK0105Create Vendor (Accounting)USER- 027201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 027201403SA38Transaction SA38 StartedSA38-0SA3807ABAP reportingUSER-027201403Start Transaction F5312 Failed- 111USER-027201403FK03Transaction FK03 StartedFK03- 0FK0302Display Vendor (Accounting)USER-028201403User Logoffloff-0loff01USER-028201403SESSLogon Successful (Type=A)logn-0logn01USER-028201403SESSPassword changed for user USER-028 in client 400pwdc-0pwdc01USER- 030201403SESSPassword changed for user USER-030 in client 400pwdc-0pwdc01USER-030201403SE11User Logoffloff- 0loff01USER-030201403SESSLogon Successful (Type=A)logn- 0logn01USER-030201403User Logoffloff-0loff01USER- 030201403Logon Successful (Type=A)logn-0logn01USER- 030201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-030201403FB60Transaction FB60 StartedFB60-0FB6006USER-030201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER- 030201403FK10Transaction FK10N StartedFK10- 0FK1003Vendor Account BalanceUSER- 030201403SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 030201403FS00Transaction FS00 StartedFS00-0FS0001USER- 033201403SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 033201403FS00Transaction FS00 StartedFS00-0FS0003USER- 033201403SESSUser USER-033 in Client 400 Unlocked After BeingSESS-*SESS*1Starting the R/3 menuUSER- 033201403FB60Transaction FB60 StartedFB60-0FB6009USER- 033201403FK03Transaction FK03 StartedFK03-
- 18. 0FK0301Display Vendor (Accounting)USER-033201403Start Transaction S400 Failed-112USER-033201403SESSUser USER- 033 Locked in Client 400 After ErroneoSESS-*SESS*3Starting the R/3 menuUSER-033201403FK01Transaction FK01 StartedFK01-0FK0108Create Vendor (Accounting)USER- 033201403FBR2Transaction FBR2 StartedFBR2-0FBR201Post DocumentUSER-033201403Logon Successful (Type=A)logn- 0logn03USER-033201403SESSLogon Failed (Reason = 2, Type = A)logn-1logn110USER-033201403SESSLogon Failed (Reason = 3, Type = A)logn-1logn115USER-033201403FB60User Logoffloff-0loff01USER-033201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn129USER-033201403SESSLogon Successful (Type=A)logn-0logn01USER-033201403FS00User Logoffloff-0loff01USER-033201403SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER- 033201403Logon Failed (Reason = 1, Type = A)logn- 1logn15USER-033201403SE11User Logoffloff-0loff01USER- 033201403FK01User Logoffloff-0loff01USER-033201403Logon Failed (Reason = 3, Type = A)logn-1logn11USER- 033201403SESSPassword changed for user USER-033 in client 400pwdc-0pwdc04USER-036201403SESSPassword changed for user USER-036 in client 400pwdc-0pwdc01USER- 036201403Logon Successful (Type=A)logn-0logn03USER- 036201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-036201403User Logoffloff-0loff01USER- 036201403FS00User Logoffloff-0loff02USER- 036201403FS00Transaction FS00 StartedFS00-0FS0003USER- 038201403SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-038201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER- 038201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-038201403FS00Transaction FS00 StartedFS00-0FS0001USER-038201403SE11Transaction SE11 StartedSE11-0SE1103ABAP/4 Dictionary MaintenanceUSER- 038201403SESSPassword changed for user USER-038 in client 400pwdc-0pwdc01USER-038201403Logon Successful
- 19. (Type=A)logn-0logn01USER-038201403SESSLogon Successful (Type=A)logn-0logn01USER-038201403User Logoffloff- 0loff02USER-038201403SU01Transaction SU01D StartedSU01- 0SU0101User MaintenanceUSER-040201403SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER- 040201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-040201403User Logoffloff-0loff03USER- 040201403SESSLogon Successful (Type=A)logn- 0logn01USER-040201403SESSPassword changed for user USER-040 in client 400pwdc-0pwdc01USER-040201403Logon Successful (Type=A)logn-0logn02USER- 040201403FB03Transaction FB03 StartedFB03- 0FB0301Display DocumentUSER-040201403FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 040201403SE43Transaction SE43N StartedSE43- 0SE4303Maintain Area MenuUSER-040201403F-02Transaction F-02 StartedF-02-0F-0202Enter G/L Account PostingUSER- 040201403FB60Transaction FB60 StartedFB60-0FB6004USER- 040201403Start Transaction F5060 Failed-111USER- 040201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 040201403FK01Transaction FK01 StartedFK01-0FK0104Create Vendor (Accounting)USER-040201403SM30Transaction SM30 StartedSM30-0SM3001Call View MaintenanceUSER- 040201403SE93Transaction SE93 StartedSE93- 0SE9301Maintain Transaction CodesUSER- 040201403FS10Transaction FS10 StartedFS10-0FS1002G/L Account BalanceUSER-040201403FK03Transaction FK03 StartedFK03-0FK0304Display Vendor (Accounting)USER- 040201403SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-040201403FS00Transaction FS00 StartedFS00- 0FS0002USER-041201403FB03Transaction FB03 StartedFB03- 0FB0301Display DocumentUSER-041201403SO00Transaction SO00 StartedSO00-0SO0001SAPoffice: Short MessageUSER- 041201403SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-041201403SA38Transaction
- 20. SA38 StartedSA38-0SA3807ABAP reportingUSER- 041201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 041201403FB02Transaction FB02 StartedFB02-0FB0201Change DocumentUSER-041201403FB60Transaction FB60 StartedFB60-0FB6007USER-041201403FK03Transaction FK03 StartedFK03-0FK0309Display Vendor (Accounting)USER- 041201403SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 041201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-041201403FS00Transaction FS00 StartedFS00-0FS0001USER-041201403FBR2Transaction FBR2 StartedFBR2-0FBR201Post DocumentUSER- 041201403S00Transaction S00 StartedS00 -0S0001Short MessageUSER-041201403SESSLogon Successful (Type=A)logn-0logn01USER-041201403SU01Transaction SU01 StartedSU01-0SU0104User MaintenanceUSER- 041201403SU03Transaction SU03 StartedSU03- 0SU0301Maintain AuthorizationsUSER- 041201403SU02Transaction SU02 StartedSU02- 0SU0201Maintain Authorization ProfilesUSER- 041201403SA38User Logoffloff-0loff01USER- 041201403SU3Transaction SU3 StartedSU3 -0SU301Maintain Users Own DataUSER-041201403SESSPassword changed for user USER-041 in client 400pwdc-0pwdc01USER- 041201403Logon Successful (Type=A)logn-0logn01USER- 041201403User Logoffloff-0loff01USER- 041201403SU01Transaction SU01D StartedSU01-0SU0105User MaintenanceUSER-042201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 042201403PFCGUser Logoffloff-0loff01USER- 042201403Logon Successful (Type=A)logn-0logn06USER- 042201403User Logoffloff-0loff01USER- 042201403SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER-042201403FS00User Logoffloff- 0loff03USER-042201403FB60User Logoffloff-0loff01USER-
- 21. 042201403SESSUser Logoffloff-0loff01USER- 042201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-042201403SESSPassword changed for user USER-042 in client 400pwdc-0pwdc01USER- 042201403SESSLogon Successful (Type=A)logn- 0logn01USER-042201403SM30Transaction SM30 StartedSM30- 0SM3001Call View MaintenanceUSER- 042201403FS00Transaction FS00 StartedFS00-0FS0005USER- 042201403SA38Transaction SA38 StartedSA38-0SA3806ABAP reportingUSER-042201403SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER-042201403Start Transaction S0000 Failed-111USER- 042201403PFCGTransaction PFCG StartedPFCG- 0PFCG01Activity Group MaintenanceUSER- 042201403FB60Transaction FB60 StartedFB60-0FB6001USER- 043201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-043201403FS00Transaction FS00 StartedFS00-0FS0001USER-043201403SE11Transaction SE11 StartedSE11-0SE1103ABAP/4 Dictionary MaintenanceUSER- 043201403FB60Transaction FB60 StartedFB60-0FB6001USER- 043201403SE13Transaction SE13 StartedSE13- 0SE1301Maintain Technical Settings (Tables)USER- 043201403Logon Successful (Type=A)logn-0logn02USER- 043201403User Logoffloff-0loff01USER-043201403SESSLogon Failed (Reason = 1, Type = A)logn-1logn15USER- 043201403SE11User Logoffloff-0loff01USER- 043201403SESSLogon Successful (Type=A)logn- 0logn01USER-043201403FB60User Logoffloff-0loff01USER- 043201403SESSPassword changed for user USER-043 in client 400pwdc-0pwdc02USER-043201403SESSLogon Failed (Reason = 3, Type = A)logn-1logn11USER-044201403SU3Transaction SU3 StartedSU3 -0SU302Maintain Users Own DataUSER- 044201403SESSPassword changed for user USER-044 in client 400pwdc-0pwdc01USER-044201403Logon Successful (Type=A)logn-0logn02USER-044201403SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-
- 22. 044201403SA38User Logoffloff-0loff01USER-044201403User Logoffloff-0loff02USER-044201403SESSLogon Successful (Type=A)logn-0logn01USER-044201403SU3User Master Record USER-044 ChangedSU03-0SU0301Maintain AuthorizationsUSER-044201403SE43Transaction SE43N StartedSE43-0SE4301Maintain Area MenuUSER- 044201403FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 044201403SBWPTransaction SBWP StartedSBWP- 0SBWP02USER-044201403SA38Transaction SA38 StartedSA38-0SA3801ABAP reportingUSER- 044201403SE11Transaction SE11 StartedSE11- 0SE1102ABAP/4 Dictionary MaintenanceUSER- 044201403FK01Transaction FK01 StartedFK01-0FK0103Create Vendor (Accounting)USER-044201403FB60Transaction FB60 StartedFB60-0FB6003USER-044201403FS10Transaction FS10 StartedFS10-0FS1001G/L Account BalanceUSER- 044201403FB03Transaction FB03 StartedFB03- 0FB0301Display DocumentUSER-044201403F-02Transaction F- 02 StartedF-02-0F-0202Enter G/L Account PostingUSER- 044201403FS00Transaction FS00 StartedFS00-0FS0005USER- 045201403FS00Transaction FS00 StartedFS00-0FS0002USER- 045201403FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-045201403PFCGTransaction PFCG StartedPFCG-0PFCG01Activity Group MaintenanceUSER- 045201403SBWPTransaction SBWP StartedSBWP- 0SBWP01USER-045201403SU02Transaction SU02 StartedSU02-0SU0201Maintain Authorization ProfilesUSER- 045201403SESSPassword changed for user USER-045 in client 400pwdc-0pwdc02USER-045201403SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER- 045201403Logon Successful (Type=A)logn-0logn02USER- 045201403FS00User Logoffloff-0loff01USER- 045201403SU03Transaction SU03 StartedSU03- 0SU0301Maintain AuthorizationsUSER- 045201403SUPCTransaction SUPC StartedSUPC-
- 23. 0SUPC01Profiles for activity groupsUSER- 045201403SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-045201403SU03User Logoffloff-0loff01USER- 049201403Logon Successful (Type=A)logn-0logn01USER- 049201403User Logoffloff-0loff01USER-049201403Password changed for user USER-049 in client 400pwdc-0pwdc01USER- 049201403FK01Transaction FK01 StartedFK01-0FK0101Create Vendor (Accounting)USER-049201403FS00Transaction FS00 StartedFS00-0FS0002USER-049201403FB60Transaction FB60 StartedFB60-0FB6001USER-001201404SESSLogon Failed (Reason = 1, Type = A)logn-1logn11USER-001201404SE11User Logoffloff-0loff02USER-001201404SU10Transaction SU10 StartedSU10-0SU1003Mass Changes to User Master RecordsUSER-001201404FS10User Logoffloff-0loff01USER- 001201404SESSLogon Successful (Type=A)logn- 0logn01USER-001201404Logon Successful (Type=A)logn- 0logn03USER-001201404User Logoffloff-0loff01USER- 001201404SU03Transaction SU03 StartedSU03- 0SU0303Maintain AuthorizationsUSER- 001201404SUGRTransaction SUGR StartedSUGR- 0SUGR01USER-001201404Logon Failed (Reason = 1, Type = A)logn-1logn11USER-001201404FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER- 001201404SU01User ZMYUSER02 CreatedSU01-0SU0101User MaintenanceUSER-001201404FS00Transaction FS00 StartedFS00-0FS0002USER-001201404SU01Authorizations for User ZMYUSER02 ChangedSU01-0SU0101User MaintenanceUSER-001201404Start Transaction 400 Failed- 111USER-001201404FK04Transaction FK04 StartedFK04- 0FK0403Vendor Changes (Accounting)USER- 001201404SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-001201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER- 001201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER-001201404SM20Transaction SM20 StartedSM20- 0SM2002Security Audit Log AssessmentUSER-
- 24. 001201404SM19Transaction SM19 StartedSM19- 0SM1901Security Audit ConfigurationUSER- 001201404SE11Transaction SE11 StartedSE11- 0SE1105ABAP/4 Dictionary MaintenanceUSER- 001201404STADTransaction STAD StartedSTAD- 0STAD03Statistics display for all systemsUSER- 001201404SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-001201404SU01Transaction SU01 StartedSU01-0SU0107User MaintenanceUSER- 002201404FK01Transaction FK01 StartedFK01-0FK0102Create Vendor (Accounting)USER-002201404SA38Transaction SA38 StartedSA38-0SA3804ABAP reportingUSER- 002201404SM04Transaction SM04 StartedSM04-0SM0403User listUSER-002201404FS10Transaction FS10N StartedFS10- 0FS1002G/L Account BalanceUSER- 002201404SM21Transaction SM21 StartedSM21- 0SM2101System LogUSER-002201404SU01Authorizations for User ZMYUSER111 ChangedSU01-0SU0101User MaintenanceUSER-002201404STADTransaction STAD StartedSTAD-0STAD01Statistics display for all systemsUSER- 002201404SU01User ZMYUSER111 CreatedSU01- 0SU0101User MaintenanceUSER-002201404FK02Transaction FK02 StartedFK02-0FK0201Change Vendor (Accounting)USER-002201404ST22Transaction ST22 StartedST22-0ST2201ABAP/4 Runtime Error AnalysisUSER- 002201404Start Transaction SELECT STATICAL RECO Failed- 111USER-002201404SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 002201404SU01Transaction SU01 StartedSU01-0SU0106User MaintenanceUSER-002201404FK04Transaction FK04 StartedFK04-0FK0405Vendor Changes (Accounting)USER- 002201404Logon Successful (Type=A)logn-0logn02USER- 002201404User Logoffloff-0loff03USER- 002201404SUGRTransaction SUGR StartedSUGR- 0SUGR01USER-002201404SU10Transaction SU10 StartedSU10-0SU1006Mass Changes to User Master
- 25. RecordsUSER-002201404SESSLogon Successful (Type=A)logn-0logn01USER-003201404SU03Transaction SU03 StartedSU03-0SU0303Maintain AuthorizationsUSER- 003201404SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-003201404User Logoffloff-0loff01USER- 003201404Logon Successful (Type=A)logn-0logn01USER- 003201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER-003201404SU01Authorizations for User ZMYUSER03 ChangedSU01-0SU0101User MaintenanceUSER- 003201404SU01Transaction SU01 StartedSU01-0SU0101User MaintenanceUSER-003201404SU01User ZMYUSER03 CreatedSU01-0SU0101User MaintenanceUSER- 004201404FK01Transaction FK01 StartedFK01-0FK0105Create Vendor (Accounting)USER-004201404SBWPTransaction SBWP StartedSBWP-0SBWP01USER-004201404SM04Transaction SM04 StartedSM04-0SM0401User listUSER- 004201404SE43Transaction SE43N StartedSE43- 0SE4301Maintain Area MenuUSER-004201404FK03Transaction FK03 StartedFK03-0FK0301Display Vendor (Accounting)USER-004201404SU01Transaction SU01 StartedSU01-0SU0102User MaintenanceUSER- 004201404FS00Transaction FS00 StartedFS00-0FS0003USER- 004201404Start Transaction S04 Failed-111USER- 004201404SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER-004201404Start Transaction ABAP RSPARAM Failed-112USER- 004201404FK10Transaction FK10N StartedFK10- 0FK1001Vendor Account BalanceUSER- 004201404SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER-004201404FB60Transaction FB60 StartedFB60-0FB6002USER-004201404SU01User Logoffloff- 0loff01USER-004201404User Logoffloff-0loff01USER- 004201404Logon Successful (Type=A)logn-0logn03USER- 004201404SU02Transaction SU02 StartedSU02- 0SU0201Maintain Authorization ProfilesUSER- 004201404FB60User Logoffloff-0loff01USER-
- 26. 004201404SESSPassword changed for user USER-004 in client 400pwdc-0pwdc02USER-005201404SESSLogon Failed (Reason = 3, Type = A)logn-1logn11USER-005201404SESSPassword changed for user USER-005 in client 400pwdc-0pwdc01USER- 005201404SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-005201404SESSLogon Successful (Type=A)logn-0logn01USER-005201404SE11User Logoffloff- 0loff01USER-005201404SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 005201404SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 005201404SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-005201404FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 005201404STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 005201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-005201404SM04Transaction SM04 StartedSM04-0SM0401User listUSER-006201404Authorization Z:VENDM06_00/F_LFA1_GRP Activated-002USER- 006201404Authorization Z:VENDM06_00/S_TCODE Activated-002USER-006201404Authorization Z:VENDM06_00/F_BKPF_GSB Activated-002USER- 006201404Authorization Z:VENDM06_00/F_LFA1_AEN Activated-002USER-006201404Authorization Z:VENDM06_00/F_BKPF_BLA Activated-002USER- 006201404Authorization Z:VENDM06_00/F_LFA1_GEN Activated-002USER-006201404SU01User ZMYUSER06 CreatedSU01-0SU0101User MaintenanceUSER- 006201404SU01Authorizations for User ZMYUSER06 ChangedSU01-0SU0102User MaintenanceUSER- 006201404SM04Transaction SM04 StartedSM04-0SM0403User listUSER-006201404FK04Transaction FK04 StartedFK04- 0FK0405Vendor Changes (Accounting)USER- 006201404Authorization Z:VENDM06_00/F_BKPF_KOA Activated-002USER-006201404SA38Transaction SA38
- 27. StartedSA38-0SA3804ABAP reportingUSER- 006201404PFCGTransaction PFCG StartedPFCG- 0PFCG05Activity Group MaintenanceUSER- 006201404SE11Transaction SE11 StartedSE11- 0SE1107ABAP/4 Dictionary MaintenanceUSER- 006201404Authorization Z:VENDM06_00/F_LFA1_BUK Activated-002USER-006201404PFUDTransaction PFUD StartedPFUD-0PFUD01User Master Data ReconciliationUSER- 006201404Authorization Z:VENDM06_00/F_BKPF_BUK Activated-002USER-006201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER- 006201404Authorization Z:VENDM06_00/F_LFA1_BEK Activated-002USER-006201404Authorization Z:VENDM06_00/F_LFA1_APP Activated-002USER- 006201404SM20Transaction SM20 StartedSM20- 0SM2004Security Audit Log AssessmentUSER- 006201404FK03Transaction FK03 StartedFK03- 0FK0304Display Vendor (Accounting)USER- 006201404Authorization Z:VENDM06_00/F_BKPF_BEK Activated-002USER-006201404STADTransaction STAD StartedSTAD-0STAD01Statistics display for all systemsUSER- 006201404Profile Z:VENDM06_ Activated-002USER- 006201404Authorizations for User ZMYUSER06 Changed- 001USER-006201404SU01Transaction SU01 StartedSU01- 0SU0104User MaintenanceUSER-006201404S_BCTransaction S_BCE_68001403 StartedS_BC-0S_BC01USER-006201404User Logoffloff-0loff04USER-006201404SUPCTransaction SUPC StartedSUPC-0SUPC03Profiles for activity groupsUSER- 006201404Logon Successful (Type=A)logn-0logn03USER- 006201404S_BCTransaction S_BCE_68002111 StartedS_BC- 0S_BC01USER-006201404SU03Transaction SU03 StartedSU03-0SU0302Maintain AuthorizationsUSER- 006201404SU01User Master Record ZMYUSER06 ChangedSU03-0SU0302Maintain AuthorizationsUSER- 006201404S_BCTransaction S_BCE_68001767 StartedS_BC- 0S_BC01USER-006201404S_BCTransaction S_BCE_68001398
- 28. StartedS_BC-0S_BC01USER-006201404SXDAStart Transaction SXDA FailedSXDA-1SXDA11SAPDXfer: Control CenterUSER- 006201404SESSLogon Successful (Type=A)logn- 0logn01USER-006201404SU03Authorization Z:AUTH0601/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER-006201404S_BCTransaction S_BCE_68001401 StartedS_BC-0S_BC06USER- 006201404S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC03USER-007201404SU10Transaction SU10 StartedSU10-0SU1001Mass Changes to User Master RecordsUSER-007201404S_BCTransaction S_BCE_68001401 StartedS_BC-0S_BC02USER-007201404User Logoffloff- 0loff03USER-007201404Logon Successful (Type=A)logn- 0logn02USER-007201404SU03Authorization Z:AUTH0701/F_KNA1_BUK ActivatedSU03-0SU0304Maintain AuthorizationsUSER-007201404SU01User Master Record ZMYUSER07 ChangedSU03-0SU0301Maintain AuthorizationsUSER-007201404S_BCTransaction S_BCE_68001419 StartedS_BC-0S_BC02USER- 007201404SESSLogon Successful (Type=A)logn- 0logn01USER-007201404SUPCTransaction SUPC StartedSUPC-0SUPC03Profiles for activity groupsUSER- 007201404SU03Transaction SU03 StartedSU03- 0SU0303Maintain AuthorizationsUSER- 007201404Authorization Z:VENDM07_00/F_LFA1_GRP Activated-001USER-007201404SU01User ZMYUSER07 CreatedSU01-0SU0101User MaintenanceUSER- 007201404Authorization Z:VENDM07_00/F_BKPF_GSB Activated-001USER-007201404Profile Z:VENDM07_ Activated-001USER-007201404Authorization Z:VENDM07_00/F_LFA1_AEN Activated-001USER- 007201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER-007201404Authorization Z:VENDM07_00/F_LFA1_GEN Activated-001USER- 007201404Authorization Z:VENDM07_00/F_BKPF_BLA Activated-001USER-007201404Authorization
- 29. Z:VENDM07_00/F_LFA1_BUK Activated-001USER- 007201404Authorization Z:VENDM07_00/F_LFA1_APP Activated-001USER-007201404SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER- 007201404Authorization Z:VENDM07_00/F_LFA1_BEK Activated-001USER-007201404FK04Transaction FK04 StartedFK04-0FK0401Vendor Changes (Accounting)USER- 007201404PFCGTransaction PFCG StartedPFCG- 0PFCG05Activity Group MaintenanceUSER- 007201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-007201404Authorization Z:VENDM07_00/S_TCODE Activated-001USER- 007201404SE11Transaction SE11 StartedSE11- 0SE1106ABAP/4 Dictionary MaintenanceUSER- 007201404Authorization Z:VENDM07_00/F_BKPF_KOA Activated-001USER-007201404SU01Authorizations for User ZMYUSER07 ChangedSU01-0SU0102User MaintenanceUSER- 007201404SU01Transaction SU01 StartedSU01-0SU0106User MaintenanceUSER-007201404Authorization Z:VENDM07_00/F_BKPF_BUK Activated-001USER- 007201404STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 007201404Authorization Z:VENDM07_00/F_BKPF_BEK Activated-001USER-007201404SM20Transaction SM20 StartedSM20-0SM2001Security Audit Log AssessmentUSER- 008201404Start Transaction ZUSER050 Failed-111USER- 008201404SU01Transaction SU01 StartedSU01-0SU0104User MaintenanceUSER-008201404SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-008201404Start Transaction T100 Failed-111USER-008201404SE11Transaction SE11 StartedSE11-0SE1101ABAP/4 Dictionary MaintenanceUSER-008201404SU01User ZMYUSER008 CreatedSU01-0SU0101User MaintenanceUSER-008201404Start Transaction T1000 Failed-111USER- 008201404SBWPTransaction SBWP StartedSBWP- 0SBWP01USER-008201404PFCGTransaction PFCG
- 30. StartedPFCG-0PFCG02Activity Group MaintenanceUSER- 008201404SU01Authorizations for User ZMYUSER008 ChangedSU01-0SU0101User MaintenanceUSER- 008201404SUPCTransaction SUPC StartedSUPC- 0SUPC02Profiles for activity groupsUSER- 008201404SU01User Logoffloff-0loff01USER- 008201404SESSLogon Failed (Reason = 3, Type = A)logn- 1logn11USER-008201404SESSLogon Failed (Reason = 1, Type = A)logn-1logn14USER-008201404Logon Successful (Type=A)logn-0logn01USER-008201404Logon Failed (Reason = 3, Type = A)logn-1logn11USER-009201404SU03Transaction SU03 StartedSU03-0SU0303Maintain AuthorizationsUSER- 009201404SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-009201404SESSLogon Successful (Type=A)logn-0logn01USER-009201404Logon Successful (Type=A)logn-0logn01USER-009201404FS10User Logoffloff- 0loff01USER-009201404User Logoffloff-0loff01USER- 009201404SU01User ZMYUSER09 CreatedSU01-0SU0101User MaintenanceUSER-009201404SU01Transaction SU01 StartedSU01-0SU0102User MaintenanceUSER- 009201404SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 009201404STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 009201404SA38Transaction SA38 StartedSA38-0SA3801ABAP reportingUSER-009201404FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 009201404SU01Authorizations for User ZMYUSER09 ChangedSU01-0SU0101User MaintenanceUSER- 009201404FK03Transaction FK03 StartedFK03- 0FK0301Display Vendor (Accounting)USER- 009201404SM04Transaction SM04 StartedSM04-0SM0403User listUSER-009201404SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 009201404FS10Transaction FS10N StartedFS10-0FS1002G/L Account BalanceUSER-010201404SM04Transaction SM04
- 31. StartedSM04-0SM0402User listUSER- 010201404SU01Transaction SU01 StartedSU01-0SU0107User MaintenanceUSER-010201404FK04Transaction FK04 StartedFK04-0FK0401Vendor Changes (Accounting)USER- 010201404SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 010201404SU01Authorizations for User ZMYUSER10 ChangedSU01-0SU0102User MaintenanceUSER- 010201404PFCGTransaction PFCG StartedPFCG- 0PFCG05Activity Group MaintenanceUSER- 010201404SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-010201404STADTransaction STAD StartedSTAD-0STAD01Statistics display for all systemsUSER- 010201404SM20Transaction SM20 StartedSM20- 0SM2002Security Audit Log AssessmentUSER- 010201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-010201404Logon Successful (Type=A)logn-0logn01USER-010201404SUPCAuthorization Z:VENDM10_00/F_BKPF_BUK ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 010201404SU01User Master Record ZMYUSER10 ChangedSU03-0SU0302Maintain AuthorizationsUSER- 010201404SU02Transaction SU02 StartedSU02- 0SU0201Maintain Authorization ProfilesUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_BKPF_KOA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404User Logoffloff-0loff02USER- 010201404SUPCAuthorization Z:VENDM10_00/F_BKPF_GSB ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCProfile Z:VENDM10_ ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SESSLogon Successful (Type=A)logn- 0logn01USER-010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_BUK ActivatedSUPC-
- 32. 0SUPC01Profiles for activity groupsUSER- 010201404SU01User ZMYUSER10 CreatedSU01-0SU0101User MaintenanceUSER-010201404SUPCAuthorization Z:VENDM10_00/S_TCODE ActivatedSUPC-0SUPC01Profiles for activity groupsUSER-010201404S_BCTransaction S_BCE_68001419 StartedS_BC-0S_BC02USER- 010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_AEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_BKPF_BLA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_GEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_GRP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SU03Transaction SU03 StartedSU03- 0SU0302Maintain AuthorizationsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_BKPF_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCAuthorization Z:VENDM10_00/F_LFA1_APP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 010201404SUPCTransaction SUPC StartedSUPC- 0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_BKPF_KOA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SU01Transaction SU01 StartedSU01-0SU0103User MaintenanceUSER-012201404SUPCProfile Z:VENDM12_ ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_APP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_BKPF_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SU01Authorizations for User ZMYUSER12 ChangedSU01-0SU0101User MaintenanceUSER- 012201404SUPCAuthorization Z:VENDM12_00/S_TCODE ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SU03Transaction SU03 StartedSU03-
- 33. 0SU0302Maintain AuthorizationsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404Logon Successful (Type=A)logn-0logn01USER- 012201404FK04User Logoffloff-0loff01USER- 012201404SUPCAuthorization Z:VENDM12_00/F_BKPF_BLA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SE11User Logoffloff-0loff01USER- 012201404SU01User ZMYUSER12 CreatedSU01-0SU0101User MaintenanceUSER-012201404SUPCAuthorization Z:VENDM12_00/F_BKPF_GSB ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 012201404SU03Authorization Z:AUTH1201/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER- 012201404STARUser Logoffloff-0loff01USER- 012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_GEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_BKPF_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_AEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 012201404S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC01USER-012201404SESSLogon Successful (Type=A)logn-0logn02USER-012201404SUPCAuthorization Z:VENDM12_00/F_LFA1_GRP ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 012201404SUPCTransaction SUPC StartedSUPC- 0SUPC01Profiles for activity groupsUSER- 012201404SE11Transaction SE11 StartedSE11- 0SE1104ABAP/4 Dictionary MaintenanceUSER- 012201404Authorization Z:VENDM12_00/F_BKPF_BLA Activated-001USER-012201404Authorization Z:VENDM12_00/F_LFA1_BEK Activated-001USER- 012201404STADTransaction STAD StartedSTAD-
- 34. 0STAD01Statistics display for all systemsUSER- 012201404Authorization Z:VENDM12_00/F_LFA1_GEN Activated-001USER-012201404Authorization Z:VENDM12_00/F_LFA1_BUK Activated-001USER- 012201404Authorization Z:VENDM12_00/F_LFA1_GRP Activated-001USER-012201404SM20Transaction SM20 StartedSM20-0SM2001Security Audit Log AssessmentUSER- 012201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER-012201404Authorization Z:VENDM12_00/F_LFA1_APP Activated-001USER- 012201404Authorization Z:VENDM12_00/F_BKPF_GSB Activated-001USER-012201404Authorization Z:VENDM12_00/F_BKPF_BEK Activated-001USER- 012201404Authorization Z:VENDM12_00/F_LFA1_AEN Activated-001USER-012201404PFCGTransaction PFCG StartedPFCG-0PFCG04Activity Group MaintenanceUSER- 012201404Authorization Z:VENDM12_00/S_TCODE Activated-001USER-012201404Authorization Z:VENDM12_00/F_BKPF_BUK Activated-001USER- 012201404SA38Transaction SA38 StartedSA38-0SA3805ABAP reportingUSER-012201404FK04Transaction FK04 StartedFK04- 0FK0403Vendor Changes (Accounting)USER-012201404Profile Z:VENDM12_ Activated-001USER-012201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER- 012201404Authorization Z:VENDM12_00/F_BKPF_KOA Activated-001USER-014201404FK04Transaction FK04 StartedFK04-0FK0401Vendor Changes (Accounting)USER- 014201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER-014201404STADTransaction STAD StartedSTAD- 0STAD03Statistics display for all systemsUSER- 014201404User ZMYUSER014 Created-001USER- 014201404Authorizations for User ZMYUSER014 Changed- 001USER-014201404PFCGTransaction PFCG StartedPFCG- 0PFCG01Activity Group MaintenanceUSER- 014201404SE11Transaction SE11 StartedSE11- 0SE1107ABAP/4 Dictionary MaintenanceUSER-
- 35. 014201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-014201404SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER- 014201404SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 014201404SU01Transaction SU01 StartedSU01-0SU0103User MaintenanceUSER-014201404Logon Successful (Type=A)logn- 0logn01USER-014201404User Logoffloff-0loff01USER- 014201404SU03Transaction SU03 StartedSU03- 0SU0303Maintain AuthorizationsUSER- 014201404SU03Authorization Z:AUTH1401/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER- 014201404PFCGUser Logoffloff-0loff01USER- 014201404SESSLogon Successful (Type=A)logn- 0logn01USER-015201404SE11User Logoffloff-0loff01USER- 015201404Logon Successful (Type=A)logn-0logn01USER- 015201404SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 017201404Authorization Z:VENDM17_00/F_LFA1_APP Activated-001USER-017201404Authorization Z:VENDM17_00/F_LFA1_BUK Activated-001USER- 017201404Profile Z:VENDM17_ Activated-001USER- 017201404STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 017201404Authorization Z:VENDM17_00/F_BKPF_BLA Activated-001USER-017201404Authorization Z:VENDM17_00/F_BKPF_KOA Activated-001USER- 017201404SE11Transaction SE11 StartedSE11- 0SE1105ABAP/4 Dictionary MaintenanceUSER- 017201404Authorization Z:VENDM17_00/F_LFA1_AEN Activated-001USER-017201404Authorization Z:VENDM17_00/F_BKPF_BUK Activated-001USER- 017201404Authorization Z:VENDM17_00/F_LFA1_BEK Activated-001USER-017201404PFCGTransaction PFCG StartedPFCG-0PFCG05Activity Group MaintenanceUSER- 017201404Authorizations for User ZMYUSER17 Changed-
- 36. 001USER-017201404FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 017201404FK03Transaction FK03 StartedFK03- 0FK0302Display Vendor (Accounting)USER- 017201404Authorization Z:VENDM17_00/S_TCODE Activated-001USER-017201404SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER- 017201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-017201404Authorization Z:VENDM17_00/F_BKPF_BEK Activated-001USER- 017201404FS00Transaction FS00 StartedFS00-0FS0001USER- 017201404Authorization Z:VENDM17_00/F_BKPF_GSB Activated-001USER-017201404Authorization Z:VENDM17_00/F_LFA1_GRP Activated-001USER- 017201404SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 017201404Authorization Z:VENDM17_00/F_LFA1_GEN Activated-001USER-017201404SM04Transaction SM04 StartedSM04-0SM0402User listUSER- 017201404SUPCTransaction SUPC StartedSUPC- 0SUPC01Profiles for activity groupsUSER- 017201404SU01Authorizations for User ZMYUSER17 ChangedSU01-0SU0102User MaintenanceUSER- 017201404SU03Transaction SU03 StartedSU03- 0SU0302Maintain AuthorizationsUSER-017201404User Logoffloff-0loff03USER-017201404SU01User ZMYUSER17 CreatedSU01-0SU0101User MaintenanceUSER- 017201404SU01Transaction SU01 StartedSU01-0SU0106User MaintenanceUSER-017201404PFCGUser Logoffloff- 0loff01USER-017201404SU01User Master Record ZMYUSER17 ChangedSU03-0SU0301Maintain AuthorizationsUSER-017201404User Master Record ZMYUSER17 ChangedSU03-0SU0301Maintain AuthorizationsUSER-017201404Logon Successful (Type=A)logn-0logn03USER-017201404SU03Authorization Z:AUTH1701/F_KNA1_BUK ActivatedSU03-0SU0302Maintain
- 37. AuthorizationsUSER-017201404SESSLogon Successful (Type=A)logn-0logn01USER-018201404SU01User ZMYUSER18 CreatedSU01-0SU0101User MaintenanceUSER- 018201404SESSLogon Failed (Reason = 3, Type = A)logn- 1logn12USER-018201404User Logoffloff-0loff01USER- 018201404SESSLogon Failed (Reason = 1, Type = A)logn- 1logn13USER-018201404SESSLogon Successful (Type=A)logn-0logn01USER-018201404Logon Successful (Type=A)logn-0logn02USER-018201404SU01User Logoffloff- 0loff01USER-018201404SU01Transaction SU01 StartedSU01- 0SU0105User MaintenanceUSER- 018201404SU01Authorizations for User ZMYUSER18 ChangedSU01-0SU0101User MaintenanceUSER- 018201404SESSPassword changed for user USER-018 in client 400pwdc-0pwdc01USER-018201404SU03Authorization Z:AUTH1801/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER-018201404SU03Transaction SU03 StartedSU03-0SU0302Maintain AuthorizationsUSER- 018201404SUPCTransaction SUPC StartedSUPC- 0SUPC03Profiles for activity groupsUSER-018201404SE11User Logoffloff-0loff01USER-018201404Start Transaction ZMYUSER18 Failed-111USER-018201404Start Transaction 000 Failed-113USER-018201404SBWPTransaction SBWP StartedSBWP-0SBWP01USER-018201404Start Transaction 010 Failed-112USER-018201404PFCGTransaction PFCG StartedPFCG-0PFCG04Activity Group MaintenanceUSER- 018201404SM04Transaction SM04 StartedSM04-0SM0403User listUSER-018201404Start Transaction 101 Failed-112USER- 018201404FK04Transaction FK04 StartedFK04- 0FK0404Vendor Changes (Accounting)USER- 018201404SE11Transaction SE11 StartedSE11- 0SE1104ABAP/4 Dictionary MaintenanceUSER- 018201404FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-018201404SM21Transaction SM21 StartedSM21-0SM2101System LogUSER- 018201404SM20Transaction SM20 StartedSM20-
- 38. 0SM2002Security Audit Log AssessmentUSER-018201404Start Transaction 001 Failed-111USER-018201405SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER- 018201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 019201405SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 019201405FS00Transaction FS00 StartedFS00-0FS0003USER- 019201405F-02Transaction F-02 StartedF-02-0F-0201Enter G/L Account PostingUSER-019201405FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER- 019201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 019201405FK01Transaction FK01 StartedFK01-0FK0101Create Vendor (Accounting)USER-019201405SM04Transaction SM04 StartedSM04-0SM0402User listUSER- 019201405SE11Transaction SE11 StartedSE11- 0SE1106ABAP/4 Dictionary MaintenanceUSER- 019201405FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 019201405SA38Transaction SA38 StartedSA38-0SA3804ABAP reportingUSER-019201405FK03Transaction FK03 StartedFK03- 0FK0301Display Vendor (Accounting)USER- 019201405PFCGTransaction PFCG StartedPFCG- 0PFCG02Activity Group MaintenanceUSER- 019201405SE43Transaction SE43N StartedSE43- 0SE4302Maintain Area MenuUSER-019201405FK10Transaction FK10N StartedFK10-0FK1001Vendor Account BalanceUSER- 019201405FB60Transaction FB60 StartedFB60-0FB6003USER- 019201405User Logoffloff-0loff03USER-019201405FB01User Logoffloff-0loff01USER-019201405Logon Successful (Type=A)logn-0logn04USER-019201405SU03Transaction SU03 StartedSU03-0SU0302Maintain AuthorizationsUSER- 019201405SU01Transaction SU01 StartedSU01-0SU0103User MaintenanceUSER-019201405SU01User ZMYUSER19 CreatedSU01-0SU0101User MaintenanceUSER-
- 39. 019201405SU01Authorizations for User ZMYUSER19 ChangedSU01-0SU0101User MaintenanceUSER- 019201405SESSPassword changed for user USER-019 in client 400pwdc-0pwdc01USER-019201405SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER- 019201405SU03Authorization Z:AUTH1901/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER- 020201405SU03Authorization Z:AUTH##01/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER- 020201405SU03Transaction SU03 StartedSU03- 0SU0306Maintain AuthorizationsUSER-020201405Logon Successful (Type=A)logn-0logn02USER-020201405User Logoffloff-0loff03USER-020201405S_BCTransaction S_BCE_68001419 StartedS_BC-0S_BC01USER- 020201405SUPCTransaction SUPC StartedSUPC- 0SUPC01Profiles for activity groupsUSER- 020201405SESSLogon Failed (Reason = 1, Type = A)logn- 1logn11USER-020201405SESSLogon Successful (Type=A)logn-0logn02USER-020201405SU01Transaction SU01 StartedSU01-0SU0102User MaintenanceUSER- 020201405SU01Authorizations for User ZMYUSER20 ChangedSU01-0SU0101User MaintenanceUSER- 020201405STADUser Logoffloff-0loff01USER- 020201405SU01User ZMYUSER20 CreatedSU01-0SU0101User MaintenanceUSER-020201405Authorization Z:VENDM20_00/F_LFA1_APP Activated-001USER- 020201405Profile Z:VENDM20_ Activated-001USER- 020201405Authorization Z:VENDM20_00/S_TCODE Activated-001USER-020201405Authorization Z:VENDM20_00/F_LFA1_GRP Activated-001USER- 020201405SE11Transaction SE11 StartedSE11- 0SE1103ABAP/4 Dictionary MaintenanceUSER- 020201405FK03Transaction FK03 StartedFK03- 0FK0301Display Vendor (Accounting)USER- 020201405FK04Transaction FK04 StartedFK04- 0FK0402Vendor Changes (Accounting)USER-
- 40. 020201405Authorization Z:VENDM20_00/F_BKPF_BEK Activated-001USER-020201405Authorization Z:VENDM20_00/F_BKPF_GSB Activated-001USER- 020201405PFCGTransaction PFCG StartedPFCG- 0PFCG03Activity Group MaintenanceUSER- 020201405SM20Transaction SM20 StartedSM20- 0SM2003Security Audit Log AssessmentUSER- 020201405STADTransaction STAD StartedSTAD- 0STAD02Statistics display for all systemsUSER- 020201405Start Transaction PRI Failed-111USER- 020201405Authorization Z:VENDM20_00/F_LFA1_BEK Activated-001USER-020201405Authorization Z:VENDM20_00/F_BKPF_BLA Activated-001USER- 020201405Authorization Z:VENDM20_00/F_BKPF_KOA Activated-001USER-020201405Authorization Z:VENDM20_00/F_LFA1_GEN Activated-001USER- 020201405Authorization Z:VENDM20_00/F_BKPF_BUK Activated-001USER-020201405Authorization Z:VENDM20_00/F_LFA1_AEN Activated-001USER- 020201405SM04Transaction SM04 StartedSM04-0SM0402User listUSER-020201405SA38Transaction SA38 StartedSA38- 0SA3802ABAP reportingUSER-020201405Authorization Z:VENDM20_00/F_LFA1_BUK Activated-001USER- 021201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER-021201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 021201405SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-021201405FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 021201405SE11Transaction SE11 StartedSE11- 0SE1102ABAP/4 Dictionary MaintenanceUSER- 021201405SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 021201405FS10Transaction FS10N StartedFS10-0FS1002G/L Account BalanceUSER-021201405SESSLogon Successful (Type=A)logn-0logn01USER-021201405SE11User Logoffloff-
- 41. 0loff01USER-022201405Logon Successful (Type=A)logn- 0logn05USER-022201405SU03Transaction SU03 StartedSU03- 0SU0303Maintain AuthorizationsUSER-022201405User Logoffloff-0loff04USER-022201405SE11User Logoffloff- 0loff01USER-022201405PFCGUser Logoffloff-0loff01USER- 022201405S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC01USER-022201405SU03Authorization Z:AUTH2201/F_KNA1_BUK ActivatedSU03-0SU0302Maintain AuthorizationsUSER-022201405SU01Authorizations for User ZMYUSER22 ChangedSU01-0SU0101User MaintenanceUSER- 022201405User Master Record ZMYUSER22 ChangedSU03- 0SU0302Maintain AuthorizationsUSER- 022201405SUPCTransaction SUPC StartedSUPC- 0SUPC03Profiles for activity groupsUSER- 022201405SESSLogon Successful (Type=A)logn- 0logn01USER-022201405SU01User ZMYUSER22 CreatedSU01-0SU0101User MaintenanceUSER- 022201405SU01Transaction SU01 StartedSU01-0SU0105User MaintenanceUSER-022201405Authorizations for User ZMYUSER22 Changed-002USER-022201405Authorization Z:VENDM22_00/F_LFA1_AEN Activated-002USER- 022201405SE11Transaction SE11 StartedSE11- 0SE1105ABAP/4 Dictionary MaintenanceUSER- 022201405Authorization Z:VENDM22_00/F_LFA1_GEN Activated-002USER-022201405FK04Transaction FK04 StartedFK04-0FK0402Vendor Changes (Accounting)USER- 022201405SM04Transaction SM04 StartedSM04-0SM0402User listUSER-022201405Authorization Z:VENDM22_00/F_LFA1_BEK Activated-002USER- 022201405Start Transaction USER-022 Failed-111USER- 022201405Authorization Z:VENDM22_00/F_BKPF_BLA Activated-002USER-022201405Authorization Z:VENDM22_00/S_TCODE Activated-002USER- 022201405SA38Transaction SA38 StartedSA38-0SA3806ABAP reportingUSER-022201405Authorization Z:VENDM22_00/F_LFA1_GRP Activated-002USER-
- 42. 022201405Authorization Z:VENDM22_00/F_BKPF_KOA Activated-002USER-022201405Authorization Z:VENDM22_00/F_BKPF_BEK Activated-002USER- 022201405Authorization Z:VENDM22_00/F_LFA1_BUK Activated-002USER-022201405Authorization Z:VENDM22_00/F_LFA1_APP Activated-002USER- 022201405Authorization Z:VENDM22_00/F_BKPF_GSB Activated-002USER-022201405SM20Transaction SM20 StartedSM20-0SM2001Security Audit Log AssessmentUSER- 022201405STADTransaction STAD StartedSTAD- 0STAD05Statistics display for all systemsUSER- 022201405SE13Transaction SE13 StartedSE13- 0SE1301Maintain Technical Settings (Tables)USER- 022201405Authorization Z:VENDM22_00/F_BKPF_BUK Activated-002USER-022201405PFCGTransaction PFCG StartedPFCG-0PFCG05Activity Group MaintenanceUSER- 022201405FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-022201405Profile Z:VENDM22_ Activated-002USER-024201405FK04Transaction FK04 StartedFK04-0FK0401Vendor Changes (Accounting)USER- 024201405SE11Transaction SE11 StartedSE11- 0SE1102ABAP/4 Dictionary MaintenanceUSER- 024201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER-024201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 024201405FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-024201405SM20Transaction SM20 StartedSM20-0SM2002Security Audit Log AssessmentUSER- 024201405SESSLogon Successful (Type=A)logn- 0logn01USER-024201405SE11User Logoffloff-0loff01USER- 026201405SU01User Master Record ZMYUSER26 ChangedSU03-0SU0301Maintain AuthorizationsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_BKPF_KOA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER-
- 43. 026201405SUPCProfile Z:VENDM26_ ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_GEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SUPCTransaction SUPC StartedSUPC- 0SUPC03Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_GRP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_BKPF_BLA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SU01Transaction SU01 StartedSU01-0SU0104User MaintenanceUSER-026201405SUPCAuthorization Z:VENDM26_00/F_BKPF_GSB ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER-026201405User Logoffloff-0loff01USER-026201405SU01Authorizations for User ZMYUSER26 ChangedSU01-0SU0102User MaintenanceUSER-026201405SUPCAuthorization Z:VENDM26_00/F_BKPF_BEK ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_AEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SE11User Logoffloff-0loff01USER- 026201405SU03Authorization Z:AUTH2601/F_KNA1_BUK ActivatedSU03-0SU0305Maintain AuthorizationsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_LFA1_APP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SUPCAuthorization Z:VENDM26_00/F_BKPF_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 026201405SU01User ZMYUSER26 CreatedSU01-0SU0101User MaintenanceUSER-026201405SUPCAuthorization Z:VENDM26_00/S_TCODE ActivatedSUPC-0SUPC01Profiles for activity groupsUSER-026201405S_BCTransaction S_BCE_68001419 StartedS_BC-0S_BC02USER- 026201405SU03Transaction SU03 StartedSU03-
- 44. 0SU0302Maintain AuthorizationsUSER-026201405Logon Successful (Type=A)logn-0logn01USER- 026201405SU10Transaction SU10 StartedSU10-0SU1001Mass Changes to User Master RecordsUSER-026201405SESSLogon Successful (Type=A)logn-0logn01USER- 026201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 026201405SM04Transaction SM04 StartedSM04-0SM0402User listUSER-026201405FS10Transaction FS10N StartedFS10- 0FS1001G/L Account BalanceUSER- 026201405FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 026201405PFCGTransaction PFCG StartedPFCG- 0PFCG05Activity Group MaintenanceUSER- 026201405SU01Transaction SU01D StartedSU01-0SU0101User MaintenanceUSER-026201405SM20Transaction SM20 StartedSM20-0SM2003Security Audit Log AssessmentUSER- 026201405SE11Transaction SE11 StartedSE11- 0SE1106ABAP/4 Dictionary MaintenanceUSER- 026201405SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-027201405Authorization Z:VENDMAIN00/F_LFA1_APP Activated-001USER- 027201405Authorization Z:VENDMAIN00/F_LFA1_GRP Activated-001USER-027201405Profile Z:VENDMAIN Activated-001USER-027201405PFCGTransaction PFCG StartedPFCG-0PFCG05Activity Group MaintenanceUSER- 027201405Authorization Z:VENDMAIN00/F_LFA1_BEK Activated-001USER-027201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER- 027201405SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 027201405Authorization Z:VENDMAIN00/F_BKPF_KOA Activated-001USER-027201405Authorization Z:VENDMAIN00/F_BKPF_BLA Activated-001USER- 027201405Authorization Z:VENDMAIN00/F_BKPF_BUK Activated-001USER-027201405Authorization
- 45. Z:VENDMAIN00/S_TCODE Activated-001USER- 027201405Authorization Z:VENDMAIN00/F_BKPF_GSB Activated-001USER-027201405Authorization Z:VENDMAIN00/F_LFA1_GEN Activated-001USER- 027201405Authorization Z:VENDMAIN00/F_LFA1_BUK Activated-001USER-027201405Authorization Z:VENDMAIN00/F_LFA1_AEN Activated-001USER- 027201405Authorization Z:VENDMAIN00/F_BKPF_BEK Activated-001USER-027201405PFCGUser Logoffloff- 0loff01USER-027201405SU03Transaction SU03 StartedSU03- 0SU0302Maintain AuthorizationsUSER-027201405SU01User ZMYUSER27 CreatedSU01-0SU0101User MaintenanceUSER- 027201405SU01Transaction SU01 StartedSU01-0SU0103User MaintenanceUSER-027201405SUPCTransaction SUPC StartedSUPC-0SUPC02Profiles for activity groupsUSER- 027201405SU01Authorizations for User ZMYUSER27 ChangedSU01-0SU0101User MaintenanceUSER- 027201405Logon Successful (Type=A)logn-0logn01USER- 027201405S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC02USER-027201405SU02Transaction SU02 StartedSU02-0SU0201Maintain Authorization ProfilesUSER- 028201405User Logoffloff-0loff02USER-028201405SESSLogon Failed (Reason = 1, Type = A)logn-1logn12USER- 028201405SESSLogon Successful (Type=A)logn- 0logn02USER-028201405SESSPassword changed for user USER-028 in client 400pwdc-0pwdc01USER- 028201405STADTransaction STAD StartedSTAD- 0STAD01Statistics display for all systemsUSER- 028201405SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER-028201405ST03Transaction ST03N StartedST03-0ST0301Performance,SAP Statistics, WorkloadUSER-028201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER- 033201405SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-033201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER-
- 46. 033201405FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 033201405SESSUser USER-033 in Client 400 Unlocked After BeingSESS-*SESS*1Starting the R/3 menuUSER- 033201405FS10Transaction FS10N StartedFS10-0FS1002G/L Account BalanceUSER-033201405STADTransaction STAD StartedSTAD-0STAD01Statistics display for all systemsUSER- 033201405SESSUser USER-033 Locked in Client 400 After ErroneoSESS-*SESS*1Starting the R/3 menuUSER- 033201405SE11Transaction SE11 StartedSE11- 0SE1101ABAP/4 Dictionary MaintenanceUSER- 033201405SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER- 033201405FS10Transaction FS10NA StartedFS10-0FS1001G/L Account BalanceUSER-033201405SESSLogon Failed (Reason = 2, Type = A)logn-1logn11USER-033201405SESSPassword changed for user USER-033 in client 400pwdc-0pwdc01USER- 033201405SESSLogon Successful (Type=A)logn- 0logn01USER-033201405SE11User Logoffloff-0loff01USER- 033201405SESSLogon Failed (Reason = 3, Type = A)logn- 1logn13USER-033201405SESSLogon Failed (Reason = 1, Type = A)logn-1logn19USER-033201405Logon Failed (Reason = 3, Type = A)logn-1logn11USER-038201405SU01Transaction SU01 StartedSU01-0SU0102User MaintenanceUSER- 038201405FK04User Logoffloff-0loff01USER- 038201405SESSLogon Successful (Type=A)logn- 0logn01USER-038201405Logon Successful (Type=A)logn- 0logn01USER-038201405SE11User Logoffloff-0loff01USER- 038201405SU03Transaction SU03 StartedSU03- 0SU0301Maintain AuthorizationsUSER- 038201405SU01Authorizations for User ZMYUSER38 ChangedSU01-0SU0101User MaintenanceUSER- 038201405SU01User ZMYUSER38 CreatedSU01-0SU0101User MaintenanceUSER-038201405STADTransaction STAD StartedSTAD-0STAD01Statistics display for all systemsUSER- 038201405SE11Transaction SE11 StartedSE11-
- 47. 0SE1101ABAP/4 Dictionary MaintenanceUSER- 038201405SM04Transaction SM04 StartedSM04-0SM0401User listUSER-038201405SA38Transaction SA38 StartedSA38- 0SA3804ABAP reportingUSER-038201405FK04Transaction FK04 StartedFK04-0FK0401Vendor Changes (Accounting)USER-038201405SM20Transaction SM20 StartedSM20-0SM2002Security Audit Log AssessmentUSER- 040201405Authorization Z:VENDM40_00/S_TCODE Activated-001USER-040201405Authorization Z:VENDM40_00/F_LFA1_BUK Activated-001USER- 040201405FK04Transaction FK04 StartedFK04- 0FK0409Vendor Changes (Accounting)USER- 040201405Authorization Z:VENDM40_00/F_LFA1_GRP Activated-001USER-040201405Authorization Z:VENDM40_00/F_BKPF_KOA Activated-001USER- 040201405Authorization Z:VENDM40_00/F_LFA1_BEK Activated-001USER-040201405FK01Transaction FK01 StartedFK01-0FK0101Create Vendor (Accounting)USER- 040201405Authorization Z:VENDM40_00/F_BKPF_GSB Activated-001USER-040201405SE11Transaction SE11 StartedSE11-0SE1106ABAP/4 Dictionary MaintenanceUSER- 040201405Authorization Z:VENDM40_00/F_BKPF_BUK Activated-001USER-040201405STADTransaction STAD StartedSTAD-0STAD02Statistics display for all systemsUSER- 040201405SA38Transaction SA38 StartedSA38-0SA3803ABAP reportingUSER-040201405Authorization Z:VENDM40_00/F_LFA1_APP Activated-001USER- 040201405Authorization Z:VENDM40_00/F_LFA1_GEN Activated-001USER-040201405SM04Transaction SM04 StartedSM04-0SM0405User listUSER- 040201405FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER-040201405Authorization Z:VENDM40_00/F_BKPF_BEK Activated-001USER- 040201405PFCGTransaction PFCG StartedPFCG- 0PFCG09Activity Group MaintenanceUSER-040201405Profile Z:VENDM40_ Activated-001USER-040201405Authorization
- 48. Z:VENDM40_00/F_LFA1_AEN Activated-001USER- 040201405Authorization Z:VENDM40_00/F_BKPF_BLA Activated-001USER-040201405SM20Transaction SM20 StartedSM20-0SM2001Security Audit Log AssessmentUSER- 040201405S_BCTransaction S_BCE_68001767 StartedS_BC- 0S_BC01USER-040201405S_BCTransaction S_BCE_68001417 StartedS_BC-0S_BC01USER-040201405Logon Successful (Type=A)logn-0logn01USER-040201405SU03Authorization Z:AUTH4001/F_KNA1_BUK ActivatedSU03-0SU0301Maintain AuthorizationsUSER-040201405SU03Transaction SU03 StartedSU03-0SU0304Maintain AuthorizationsUSER- 040201405User Logoffloff-0loff02USER-040201405SU01User ZMYUSER40 CreatedSU01-0SU0101User MaintenanceUSER- 040201405S_BCTransaction S_BCE_68001418 StartedS_BC- 0S_BC01USER-040201405SUGRTransaction SUGRD StartedSUGR-0SUGR01USER-040201405SUGRTransaction SUGR StartedSUGR-0SUGR02USER- 040201405SUPCTransaction SUPC StartedSUPC- 0SUPC03Profiles for activity groupsUSER- 040201405SU01User Master Record ZMYUSER40 ChangedSU03-0SU0302Maintain AuthorizationsUSER- 040201405S_BCTransaction S_BCE_68001401 StartedS_BC- 0S_BC02USER-040201405SU01Transaction SU01 StartedSU01-0SU0109User MaintenanceUSER- 040201405SU01Authorizations for User ZMYUSER40 ChangedSU01-0SU0102User MaintenanceUSER- 040201405SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-040201405SU02Transaction SU02 StartedSU02- 0SU0203Maintain Authorization ProfilesUSER- 040201405S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC01USER-040201405SESSLogon Successful (Type=A)logn-0logn01USER-040201405SU01Transaction SU01D StartedSU01-0SU0102User MaintenanceUSER- 041201405SUPCAuthorization Z:VENDM41501/F_BKPF_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_BKPF_GSB
- 49. ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_BKPF_BLA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_LFA1_AEN ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SU01User Logoffloff-0loff01USER-041201405User Logoffloff-0loff02USER-041201405SUPCAuthorization Z:VENDM41500/S_TCODE ActivatedSUPC-0SUPC01Profiles for activity groupsUSER-041201405SUPCAuthorization Z:VENDM41501/F_LFA1_APP ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 041201405SUPCProfile Z:VENDM415 ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 041201405SUPCTransaction SUPC StartedSUPC- 0SUPC06Profiles for activity groupsUSER- 041201405SU03Transaction SU03 StartedSU03- 0SU0307Maintain AuthorizationsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_LFA1_BUK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SU01User Master Record ZMYUSER41 ChangedSU03-0SU0302Maintain AuthorizationsUSER- 041201405S_BCTransaction S_BCE_68001419 StartedS_BC- 0S_BC03USER-041201405SUPCAuthorization Z:VENDM41501/F_LFA1_GEN ActivatedSUPC- 0SUPC01Profiles for activity groupsUSER- 041201405SESSLogon Successful (Type=A)logn- 0logn01USER-041201405SE11User Logoffloff-0loff02USER- 041201405Logon Successful (Type=A)logn-0logn05USER- 041201405PFCGUser Logoffloff-0loff01USER- 041201405SUPCAuthorization Z:VENDM41501/F_BKPF_KOA ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_BKPF_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SESSLogon Failed (Reason = 1, Type = A)logn- 1logn12USER-041201405SU01Transaction SU01 StartedSU01- 0SU0106User MaintenanceUSER-
- 50. 041201405SUPCAuthorization Z:VENDM41501/F_LFA1_GRP ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SUPCAuthorization Z:VENDM41501/F_LFA1_BEK ActivatedSUPC-0SUPC01Profiles for activity groupsUSER- 041201405SU01User ZMYUSER41 CreatedSU01-0SU0101User MaintenanceUSER-041201405SU01Authorizations for User ZMYUSER41 ChangedSU01-0SU0103User MaintenanceUSER- 041201405SU03Authorization Z:AUTH4101/F_KNA1_BUK ActivatedSU03-0SU0303Maintain AuthorizationsUSER- 041201405Authorization Z:VENDM41500/F_LFA1_GRP Activated-001USER-041201405Start Transaction ZMYUSER41 Failed-111USER-041201405Start Transaction USER-041 Failed-111USER-041201405Authorization Z:VENDM41500/F_BKPF_BUK Activated-001USER- 041201405Authorization Z:VENDM41500/F_LFA1_APP Activated-001USER-041201405FS10Transaction FS10N StartedFS10-0FS1001G/L Account BalanceUSER- 041201405FK03Transaction FK03 StartedFK03- 0FK0303Display Vendor (Accounting)USER- 041201405SM04Transaction SM04 StartedSM04-0SM0404User listUSER-041201405Authorization Z:VENDM41500/F_LFA1_AEN Activated-001USER- 041201405Profile Z:VENDM415 Activated-001USER- 041201405Authorization Z:VENDM41500/F_LFA1_BUK Activated-001USER-041201405PFCGTransaction PFCG StartedPFCG-0PFCG013Activity Group MaintenanceUSER- 041201405FK04Transaction FK04 StartedFK04- 0FK0402Vendor Changes (Accounting)USER- 041201405SD11Transaction SD11 StartedSD11-0SD1101Data ModelerUSER-041201405STADTransaction STAD StartedSTAD-0STAD03Statistics display for all systemsUSER- 041201405Authorization Z:VENDM41500/F_LFA1_BEK Activated-001USER-041201405Authorization Z:VENDM41500/F_BKPF_BEK Activated-001USER- 041201405SM20Transaction SM20 StartedSM20- 0SM2001Security Audit Log AssessmentUSER-
- 51. 041201405SE11Transaction SE11 StartedSE11- 0SE1108ABAP/4 Dictionary MaintenanceUSER- 041201405Authorization Z:VENDM41500/S_TCODE Activated-001USER-041201405SA38Transaction SA38 StartedSA38-0SA3802ABAP reportingUSER- 041201405Authorization Z:VENDM41500/F_LFA1_GEN Activated-001USER-041201405Authorization Z:VENDM41500/F_BKPF_KOA Activated-001USER- 041201405Authorization Z:VENDM41500/F_BKPF_GSB Activated-001USER-041201405FK02Transaction FK02 StartedFK02-0FK0201Change Vendor (Accounting)USER- 041201405Authorization Z:VENDM41500/F_BKPF_BLA Activated-001USER-042201405SM04Transaction SM04 StartedSM04-0SM0402User listUSER- 042201405SA38Transaction SA38 StartedSA38-0SA3806ABAP reportingUSER-042201405SM20Transaction SM20 StartedSM20-0SM2001Security Audit Log AssessmentUSER- 042201405STADTransaction STAD StartedSTAD- 0STAD05Statistics display for all systemsUSER- 042201405FK04Transaction FK04 StartedFK04- 0FK0401Vendor Changes (Accounting)USER- 042201405SESSLogon Successful (Type=A)logn- 0logn02USER-042201405FK04User Logoffloff-0loff01USER- 042201405SA38User Logoffloff-0loff01USER- 015201406SESSLogon Failed (Reason = 8, Type = A)logn- 1logn12USER-004201407SESSLogon Failed (Reason = 1, Type = A)logn-1logn12 &A Page &P Sheet1Alphabetic list of all actions and their frequency by any selectF2F31. Alphabetic list of all actions and their frequency by any selected user, e.g. USER-040useridtextTCOUNTUSER- 040Authorization Z:AUTH4001/F_KNA1_BUK Activated1Authorization Z:VENDM40_00/F_BKPF_BEK Activated1Authorization Z:VENDM40_00/F_BKPF_BLA Activated1Authorization Z:VENDM40_00/F_BKPF_BUK
- 52. Activated1Authorization Z:VENDM40_00/F_BKPF_GSB Activated1Authorization Z:VENDM40_00/F_BKPF_KOA Activated1Authorization Z:VENDM40_00/F_LFA1_AEN Activated1Authorization Z:VENDM40_00/F_LFA1_APP Activated1Authorization Z:VENDM40_00/F_LFA1_BEK Activated1Authorization Z:VENDM40_00/F_LFA1_BUK Activated1Authorization Z:VENDM40_00/F_LFA1_GEN Activated1Authorization Z:VENDM40_00/F_LFA1_GRP Activated1Authorization Z:VENDM40_00/S_TCODE Activated1Authorizations for User ZMYUSER40 Changed2Logon Failed (Reason = 1, Type = A)4Logon Successful (Type=A)5Password changed for user USER-040 in client 4001Profile Z:VENDM40_ Activated1Start Transaction F5060 Failed1Transaction F-02 Started2Transaction FB03 Started1Transaction FB60 Started4Transaction FK01 Started5Transaction FK03 Started4Transaction FK04 Started9Transaction FK10N Started1Transaction FS00 Started2Transaction FS10 Started2Transaction FS10N Started1Transaction PFCG Started9Transaction S_BCE_68001401 Started2Transaction S_BCE_68001417 Started1Transaction S_BCE_68001418 Started1Transaction S_BCE_68001419 Started1Transaction S_BCE_68001767 Started1Transaction SA38 Started6Transaction SE11 Started9Transaction SE43N Started3Transaction SE93 Started1Transaction SM04 Started5Transaction SM20 Started1Transaction SM30 Started1Transaction STAD Started2Transaction SU01 Started9Transaction SU01D Started4Transaction SU02 Started3Transaction SU03 Started4Transaction SUGR Started2Transaction SUGRD Started1Transaction SUPC Started3User Logoff5User Master Record ZMYUSER40 Changed2User ZMYUSER40 Created1USER-040 Total135Grand Total135 Sheet2