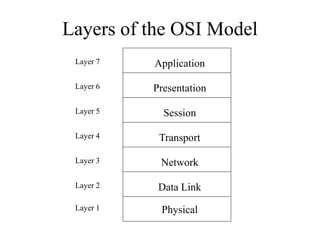
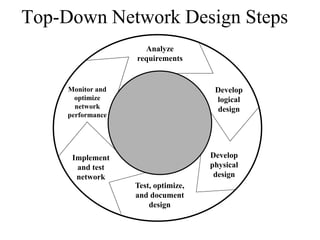
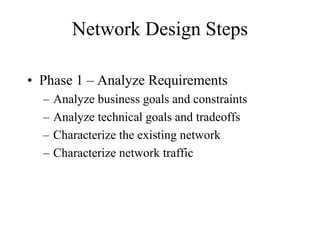
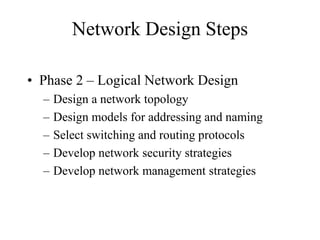
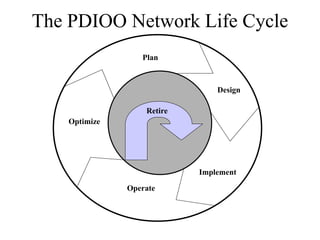
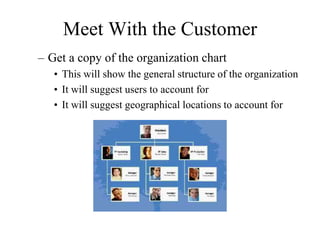
The document discusses the importance of taking a top-down approach to network design that begins by analyzing business goals and constraints. It emphasizes understanding the organization, applications, and information flows before designing network structures and technologies. The network design process involves gathering requirements, developing logical and physical designs, testing and optimizing the network, and then operating and maintaining it over time.