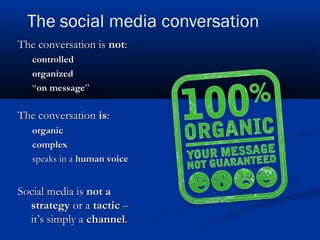
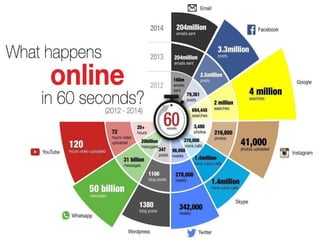
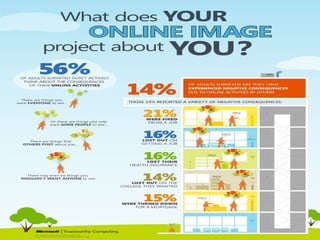
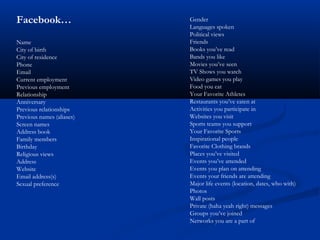
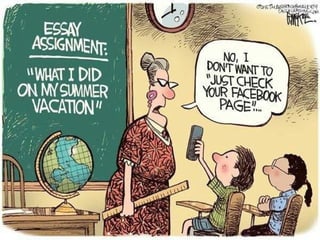
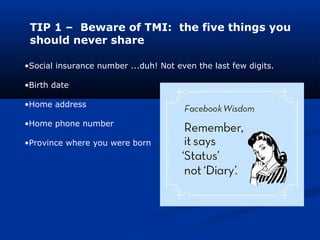
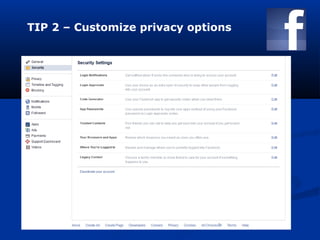
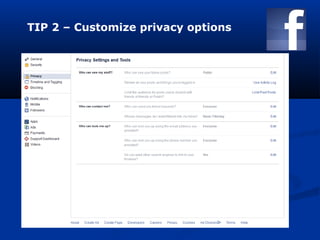
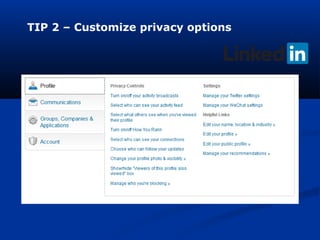
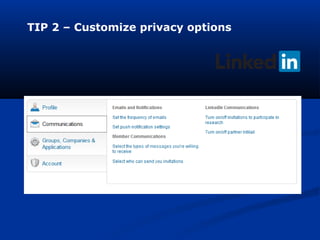
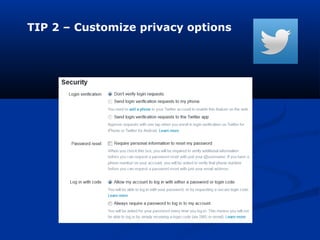
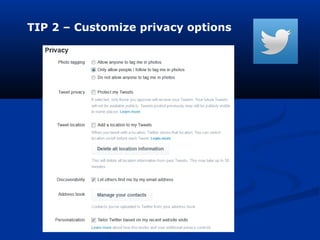
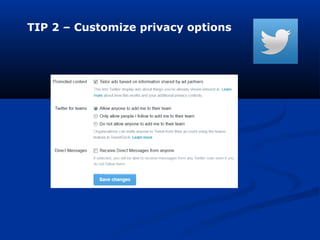
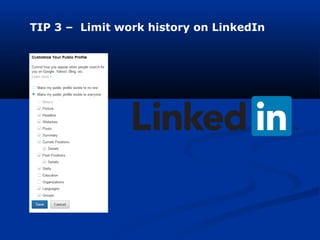
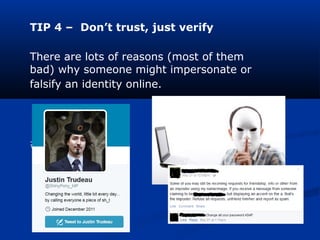
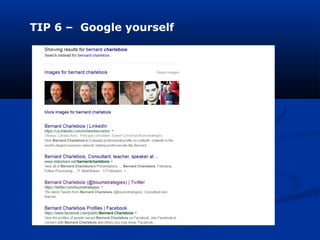
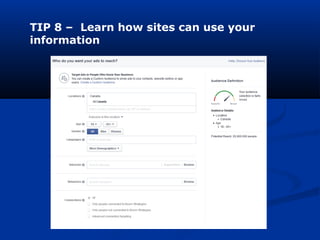
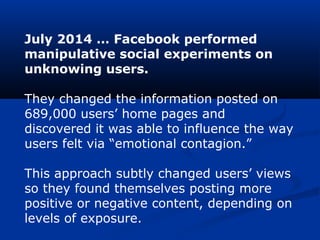
This document discusses social media and provides tips for safe usage. It defines social media as online platforms that allow users to create and share content. While social media can help people connect, it also poses risks if personal information is shared publicly. The document provides 10 tips for maintaining privacy and a positive online reputation, such as customizing privacy settings, limiting work history on profiles, avoiding oversharing of details, and being aware of how sites collect and use personal data. The overall message is that social media users should educate themselves on appropriate usage and potential downsides to ensure their online presence does not harm them professionally or personally.