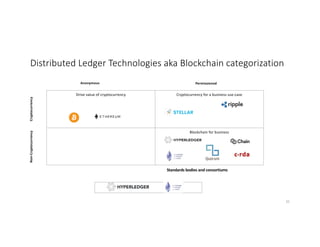
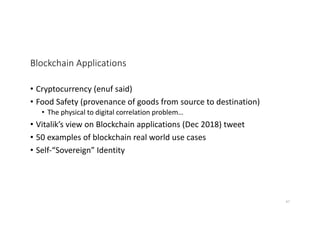
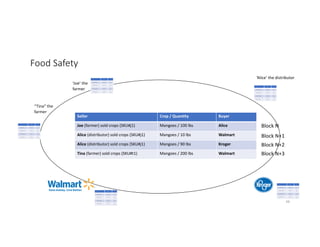
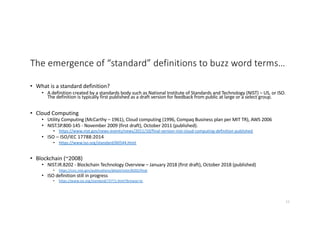
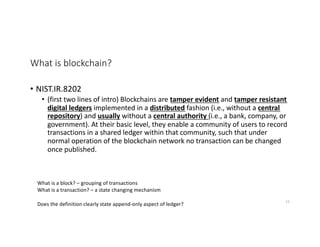
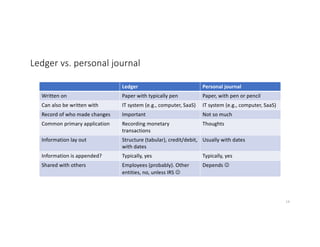
The document discusses the emerging technology of blockchain, aiming to clarify common misconceptions and provide an understanding of its components, including trust, consensus algorithms, and various applications. It covers the definitions of blockchain, the significance of decentralized digital ledgers, and compares different types of consensus mechanisms and blockchain structures. Additionally, it introduces Hyperledger as a collaborative effort for developing cross-industry blockchain technologies.

![[Lack of] Central authority or central repository - Examples
• I run a database on my single machine.
• Central repository?
• Central authority?
• A big search engine has a massive farm of distributed machines connected over network, that work
together to respond to search queries.
• Central repository?
• Central authority?
• A music file-sharing system (Napster) has a central list of which users have files, but files are
downloaded peer-to-peer.
• Central authority?
• Central repository?
• A file-sharing network has a distributed index of files and file chunks.
• Central repository?
• Central authority?
17](https://image.slidesharecdn.com/blockchain-beyond-the-hype-190731143510/85/Blockchain-Beyond-the-Hype-17-320.jpg)
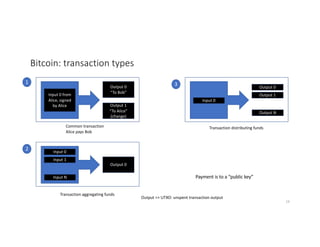
![Bitcoin: transactions are grouped into blocks
Block N
T1
T2: A -> B
T3
T4
Block N+1
B->C
Block N+2
C->D
H(N) H(N+1)
T1 T2 T3 T4
H() H() H() H()
H() H()
H(N) Mining: find a nonce such hash of merkle tree + nonce
is less than target and takes on avg 10 minutes to compute
Which transaction to include in block? Transaction fee higher
than some minimum. [decentralized or distributed?]
20](https://image.slidesharecdn.com/blockchain-beyond-the-hype-190731143510/85/Blockchain-Beyond-the-Hype-20-320.jpg)
![Consensus algorithms - Background
• Lamport Byzantine generals problem [1982]
• Schneider – task of reaching and maintaining consensus among nodes
involves [1990]:
• A (deterministic) state machine that implements the logic of the service to be
replicated
• A consensus protocol to disseminate requests among the nodes, such that
each node executes the same sequence of requests on its instance of the
service.
• Traditionally in literature, consensus means reaching agreement on
single request (first) – atomic broadcasts provide agreement on
sequence of requests.
Cachin, Vucolic - https://arxiv.org/pdf/1707.01873.pdf
30](https://image.slidesharecdn.com/blockchain-beyond-the-hype-190731143510/85/Blockchain-Beyond-the-Hype-30-320.jpg)