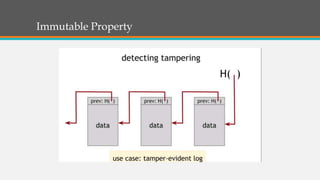
Blockchain is a decentralized approach to solving the double spend problem of digital currencies without a central authority. It uses a distributed ledger maintained on many computers to record transactions in blocks linked through cryptography. This allows participants to verify transactions without trusting a central party. Blockchain addresses issues like single points of failure, censorship, and high fees by achieving consensus across a peer-to-peer network through proof of work and an incentive for honest participation in maintaining the ledger. Potential applications include cryptocurrencies like Bitcoin and programmable platforms for smart contracts.