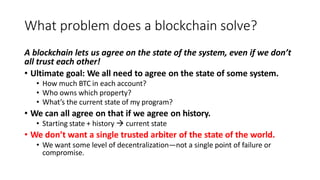
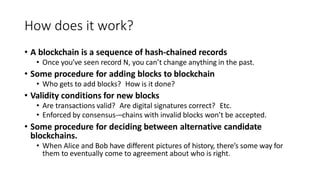
Blockchains allow mutually distrusting entities to agree on a system's state by agreeing on its transaction history. They use cryptographic hash chains, where each record contains the hash of the previous record. This commits all records to the chain, preventing changes. Blockchains add validity conditions and consensus rules to decide which chains are accepted. In permissioned blockchains, trusted entities vote to add blocks. In proof-of-work blockchains like Bitcoin, miners perform computations to add blocks and resolve disputes between chains. While powerful, proof-of-work has costs around efficiency and incentives that permissioned alternatives aim to address. Overall, blockchains coordinate distributed consensus without a central authority.