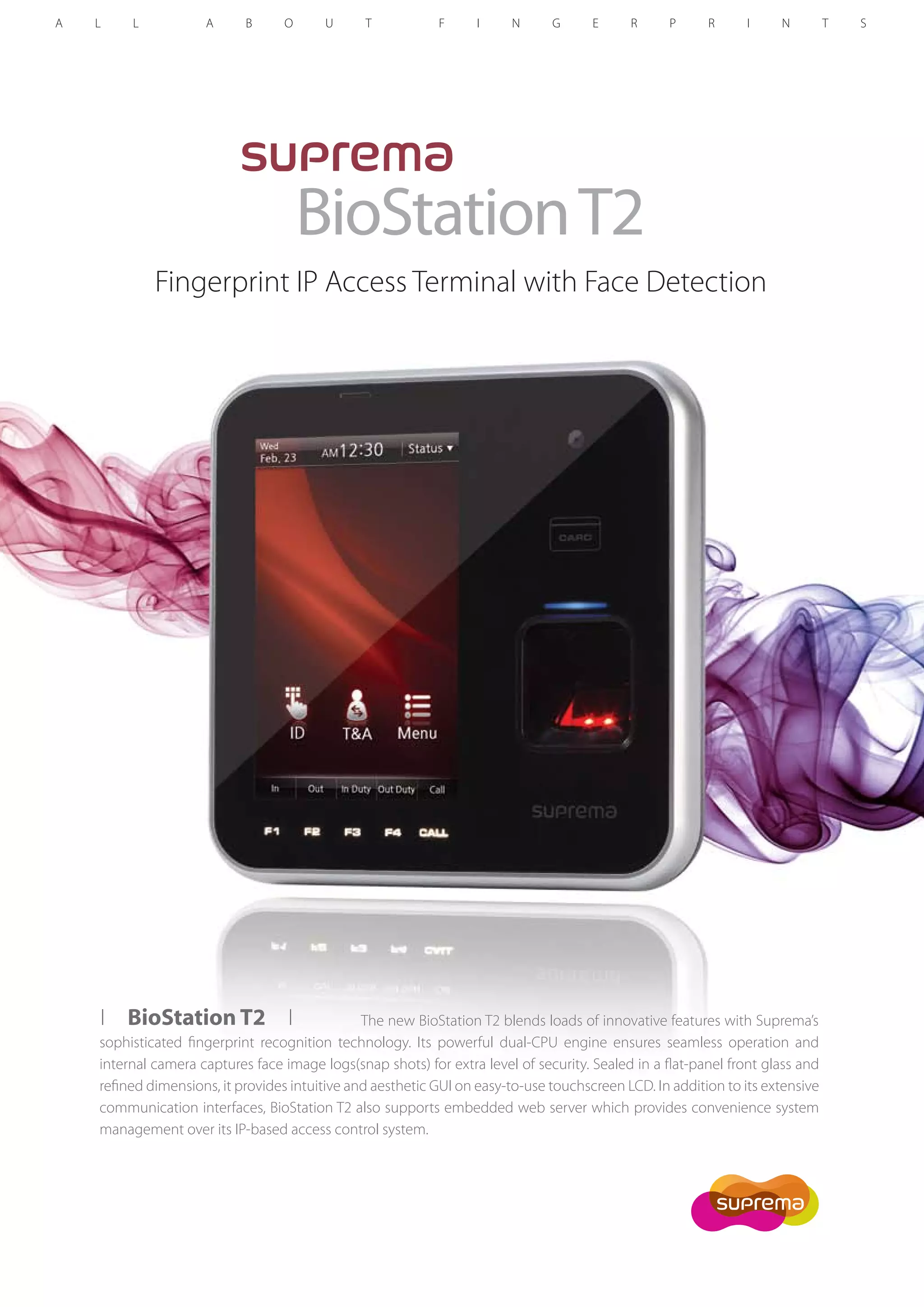
The biostation T2 is an advanced fingerprint IP access terminal that incorporates face detection technology and a dual-CPU engine for efficient operation. It features a 5-inch touchscreen LCD, extensive communication options, and an embedded web server for system management. With capabilities of matching 1:3,000 fingerprints in one second and supporting up to 200,000 users, it is designed for enhanced security and convenience.