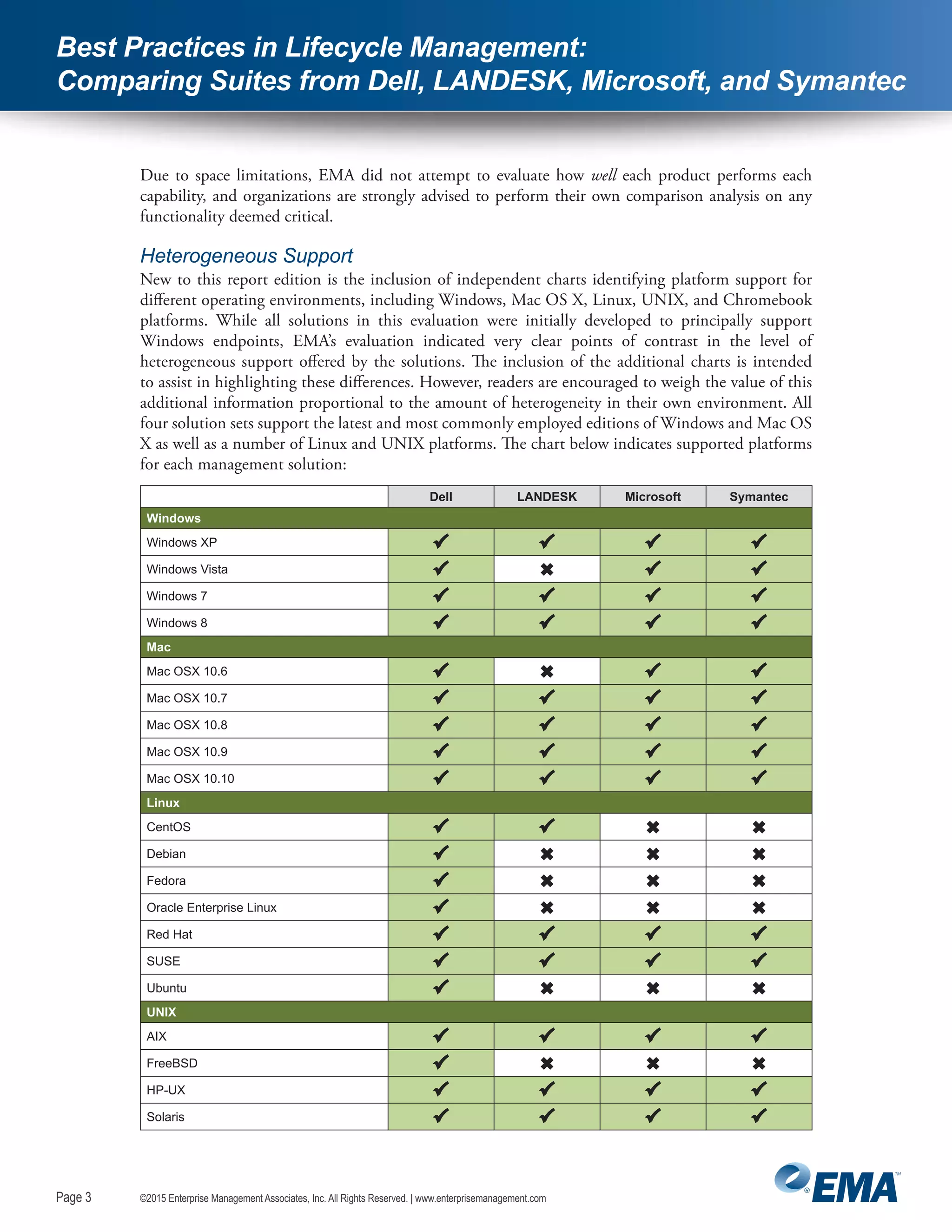
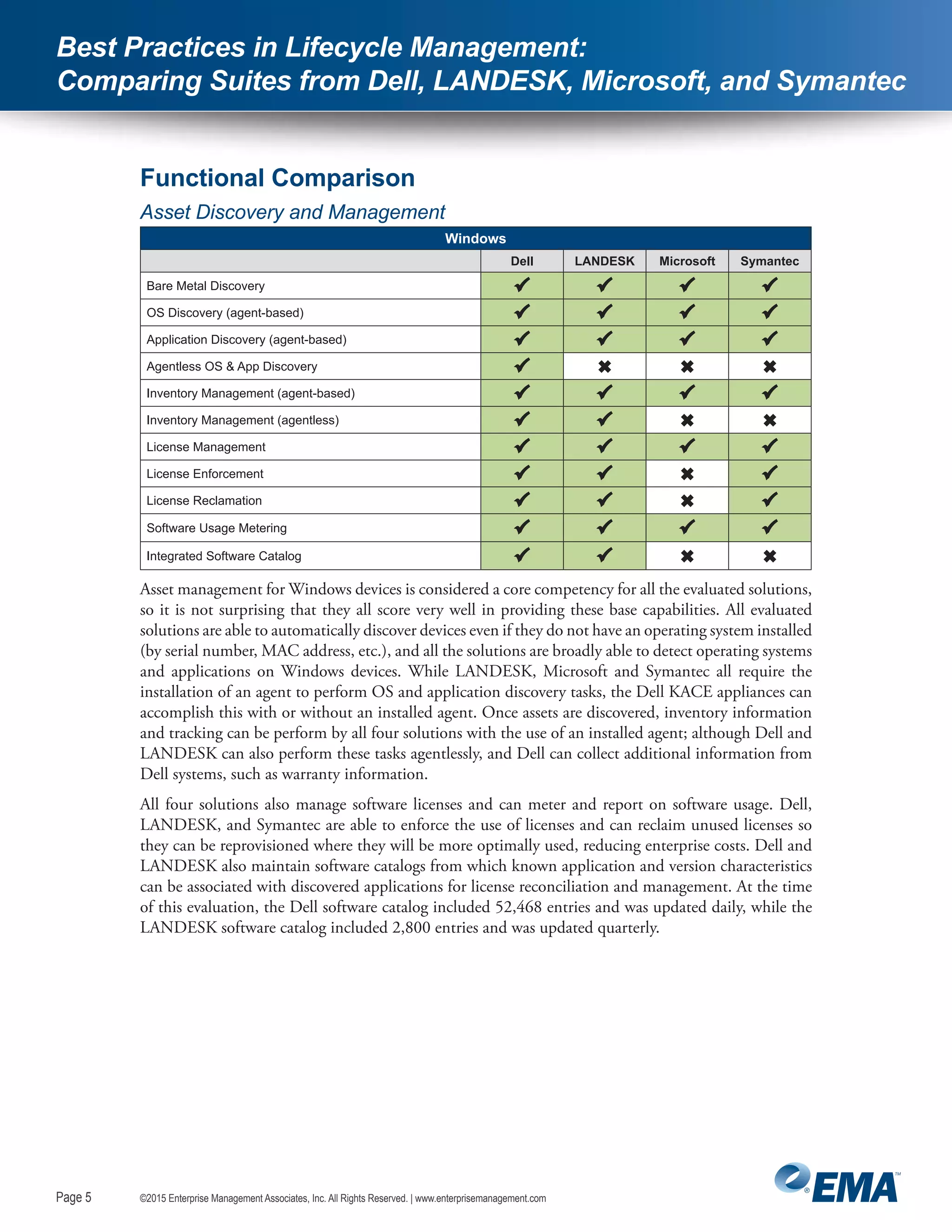
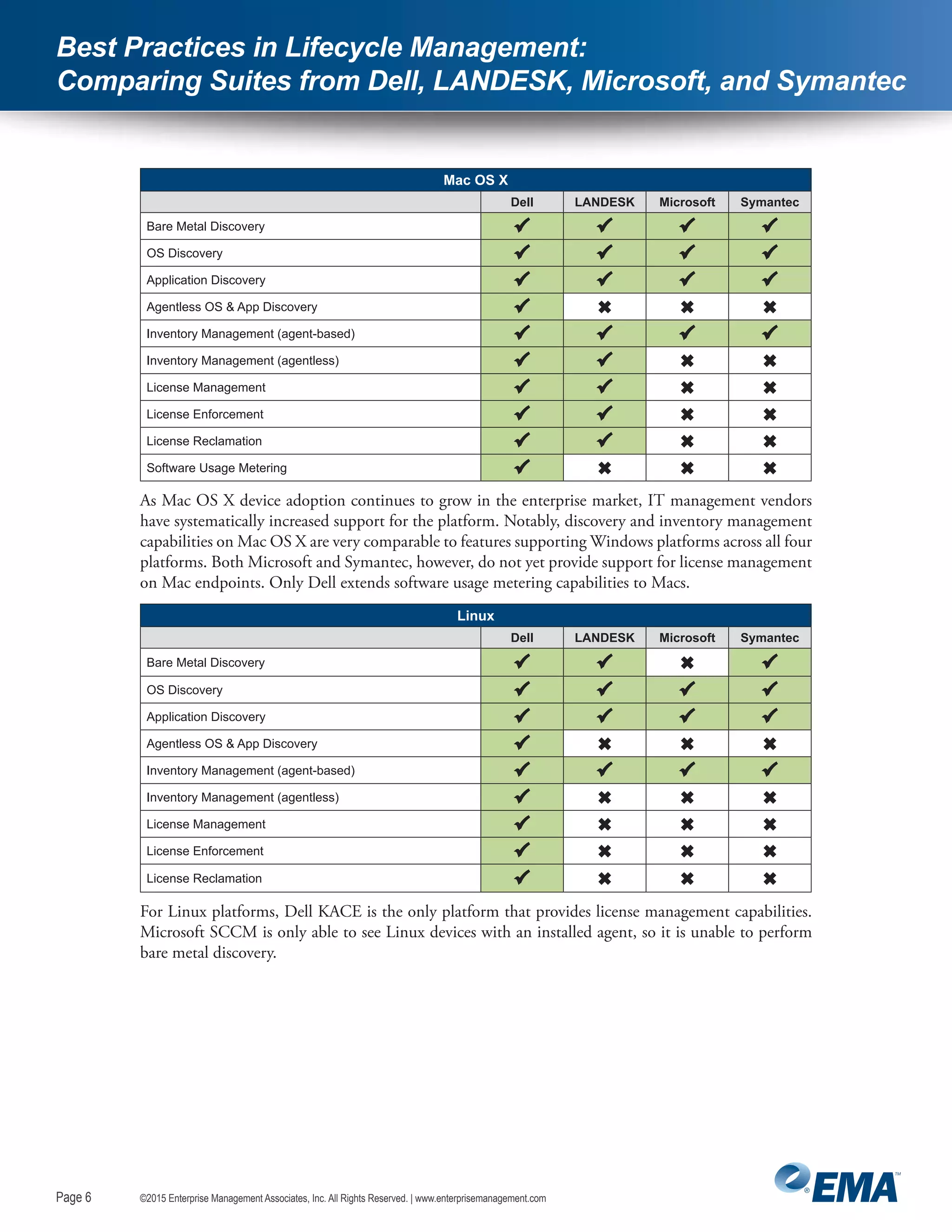
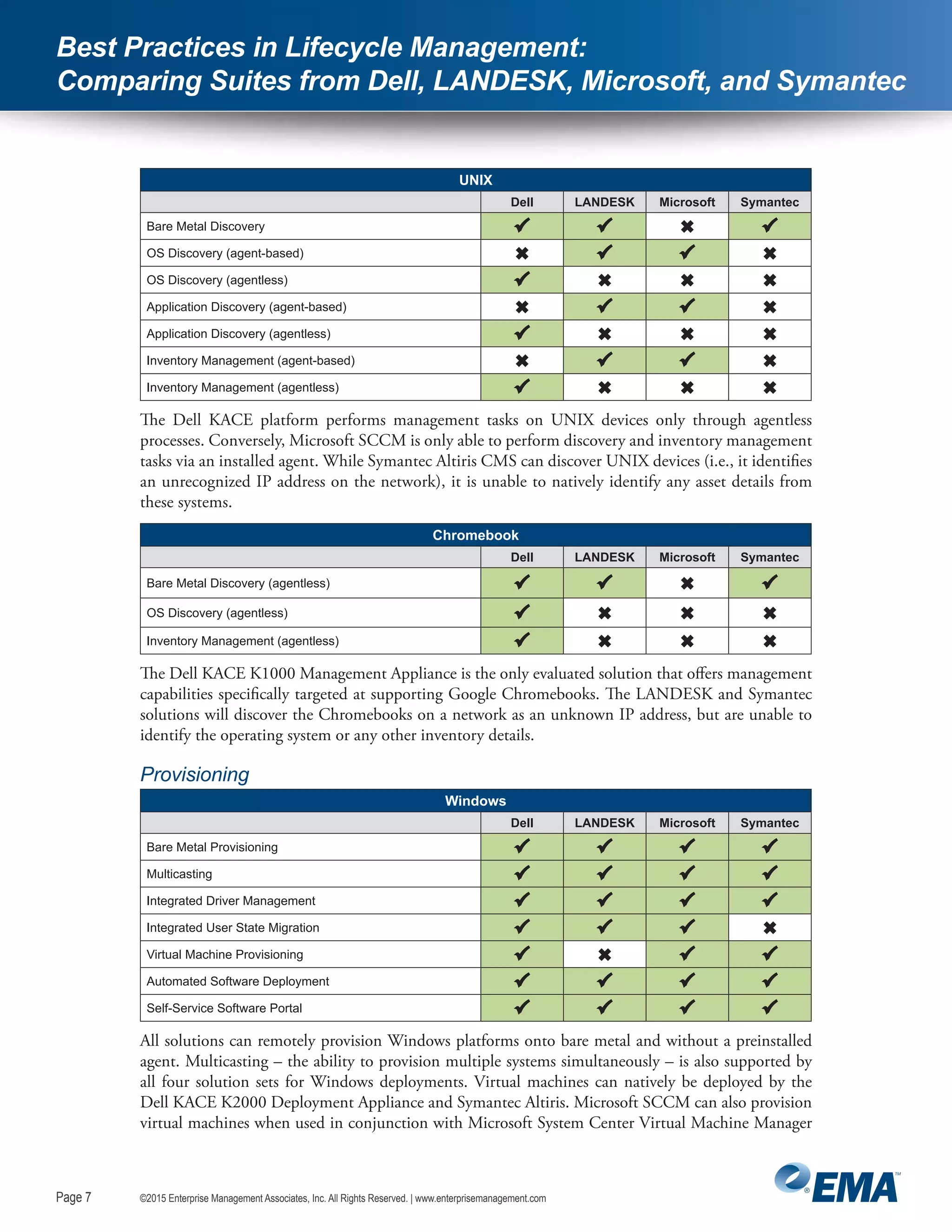
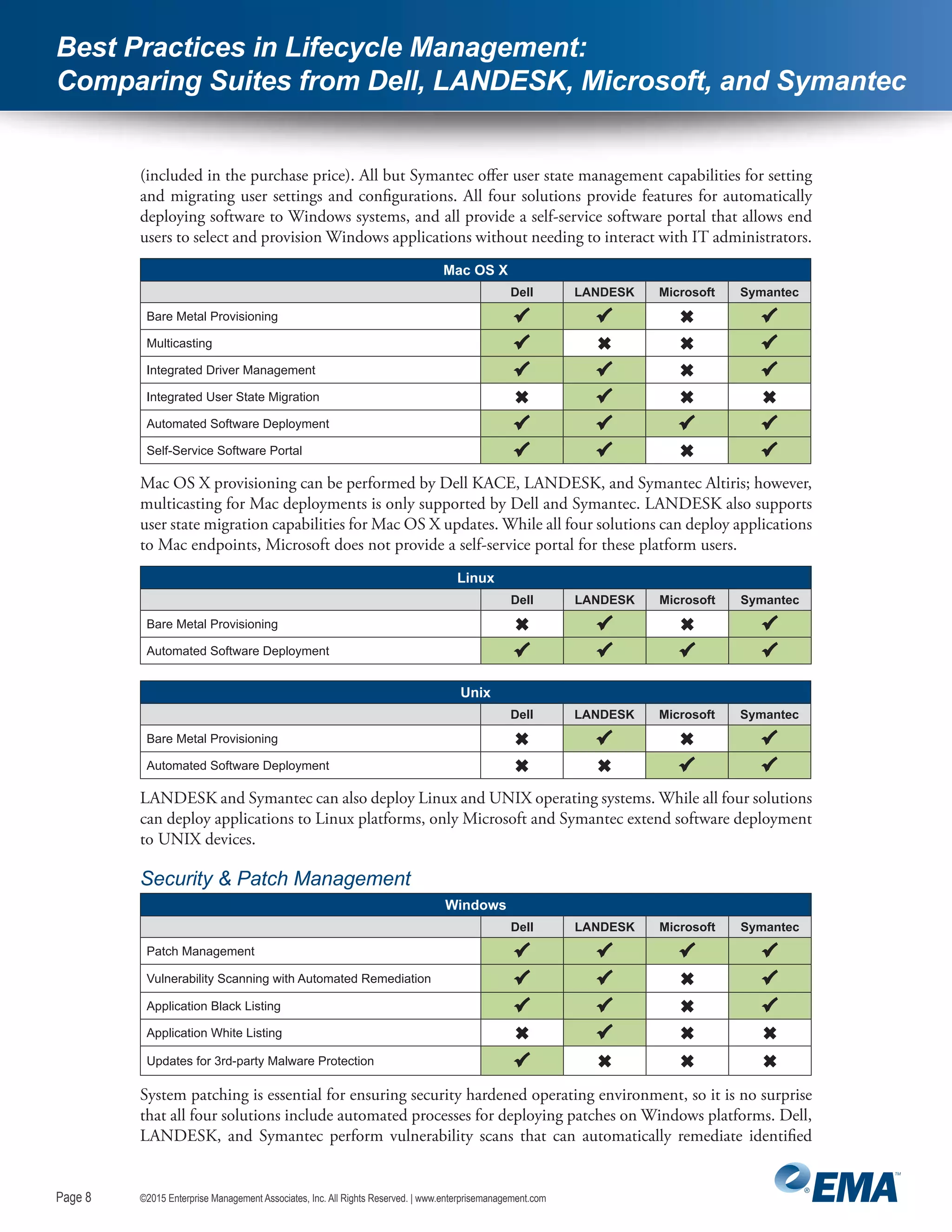
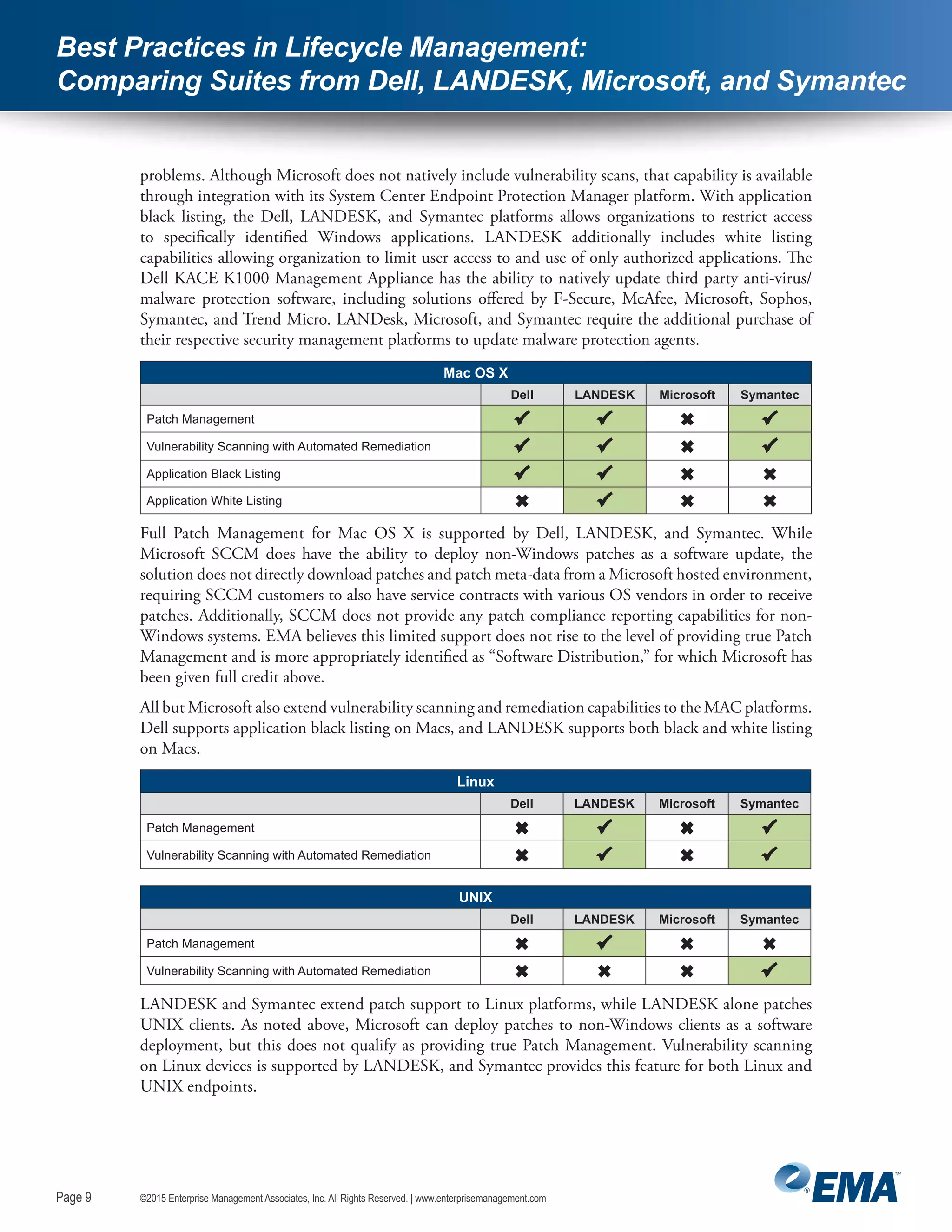
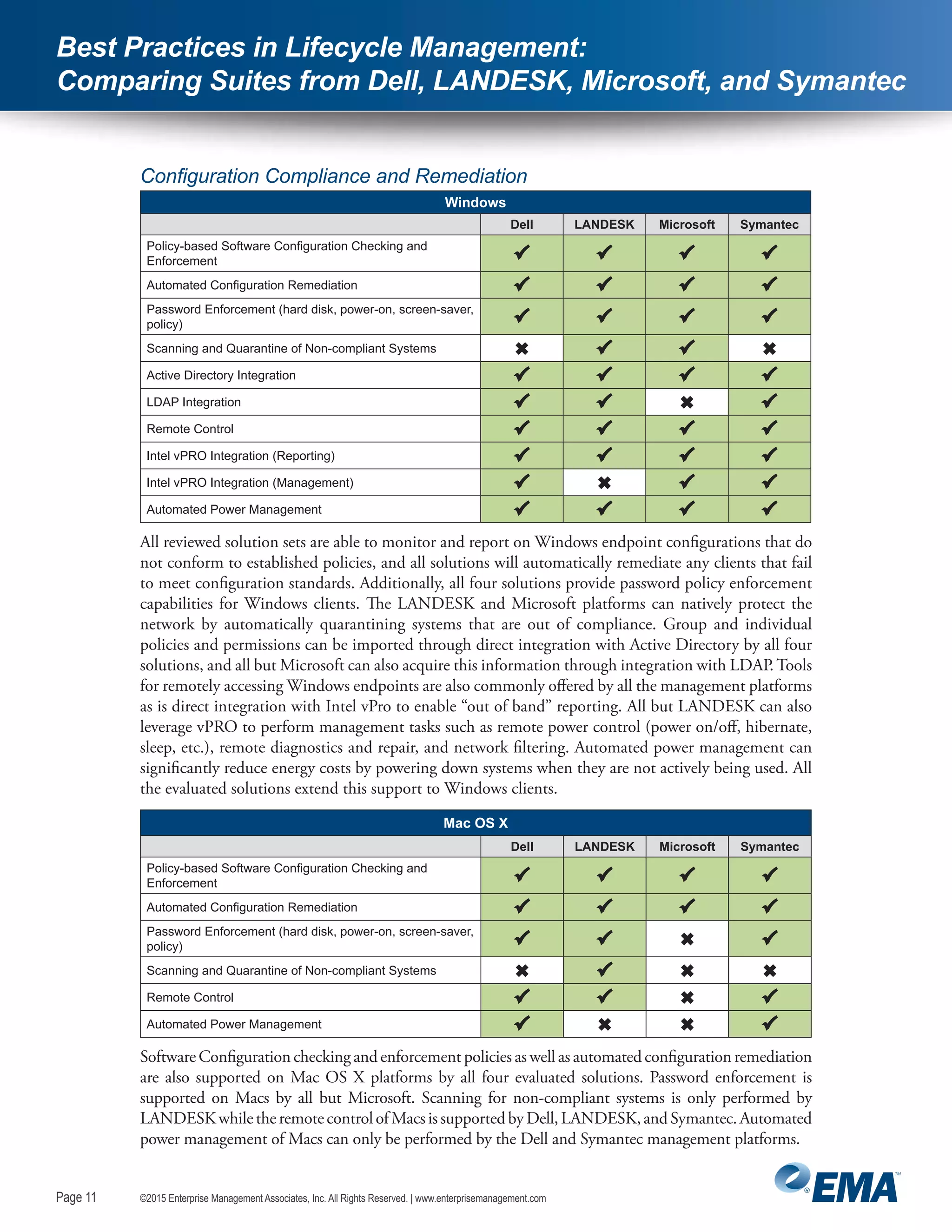
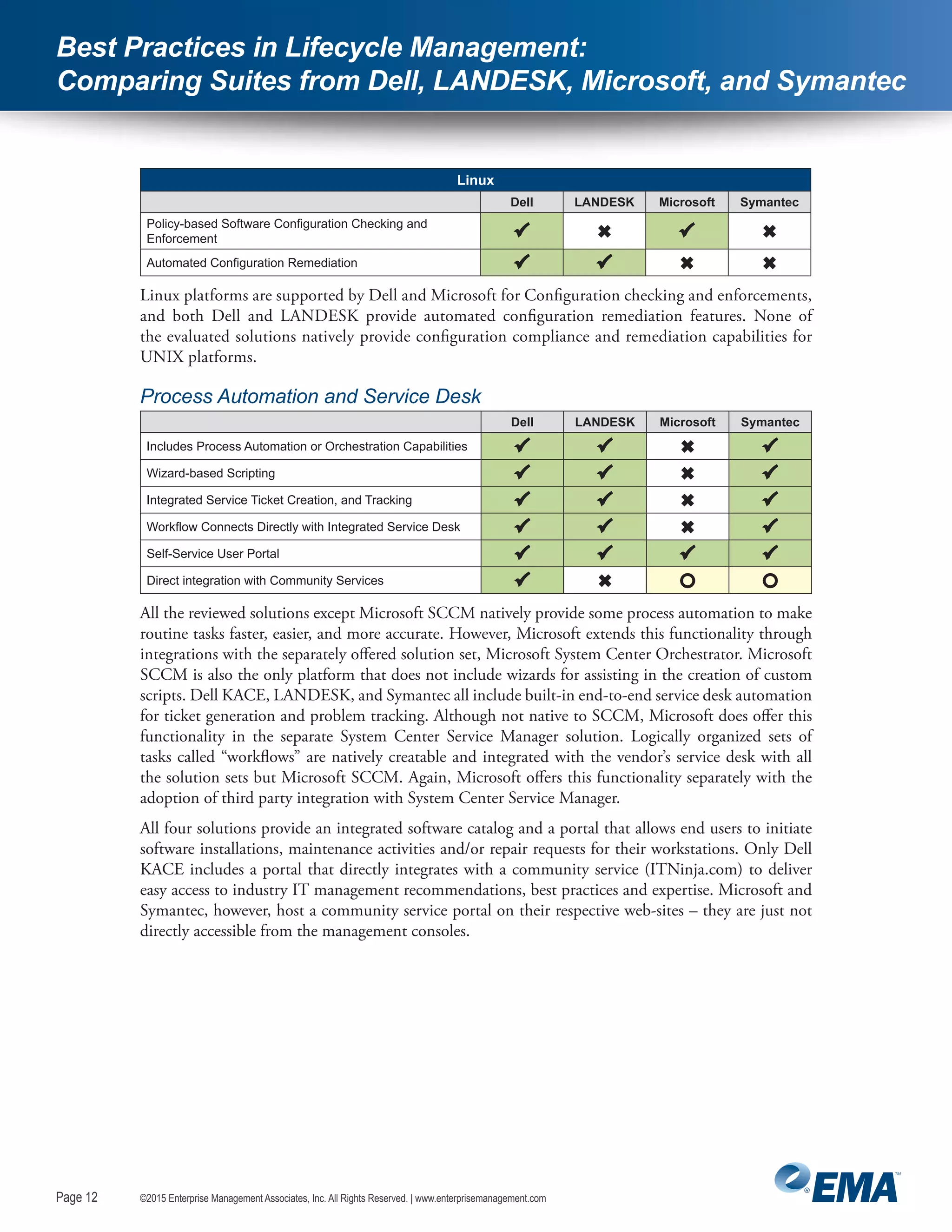
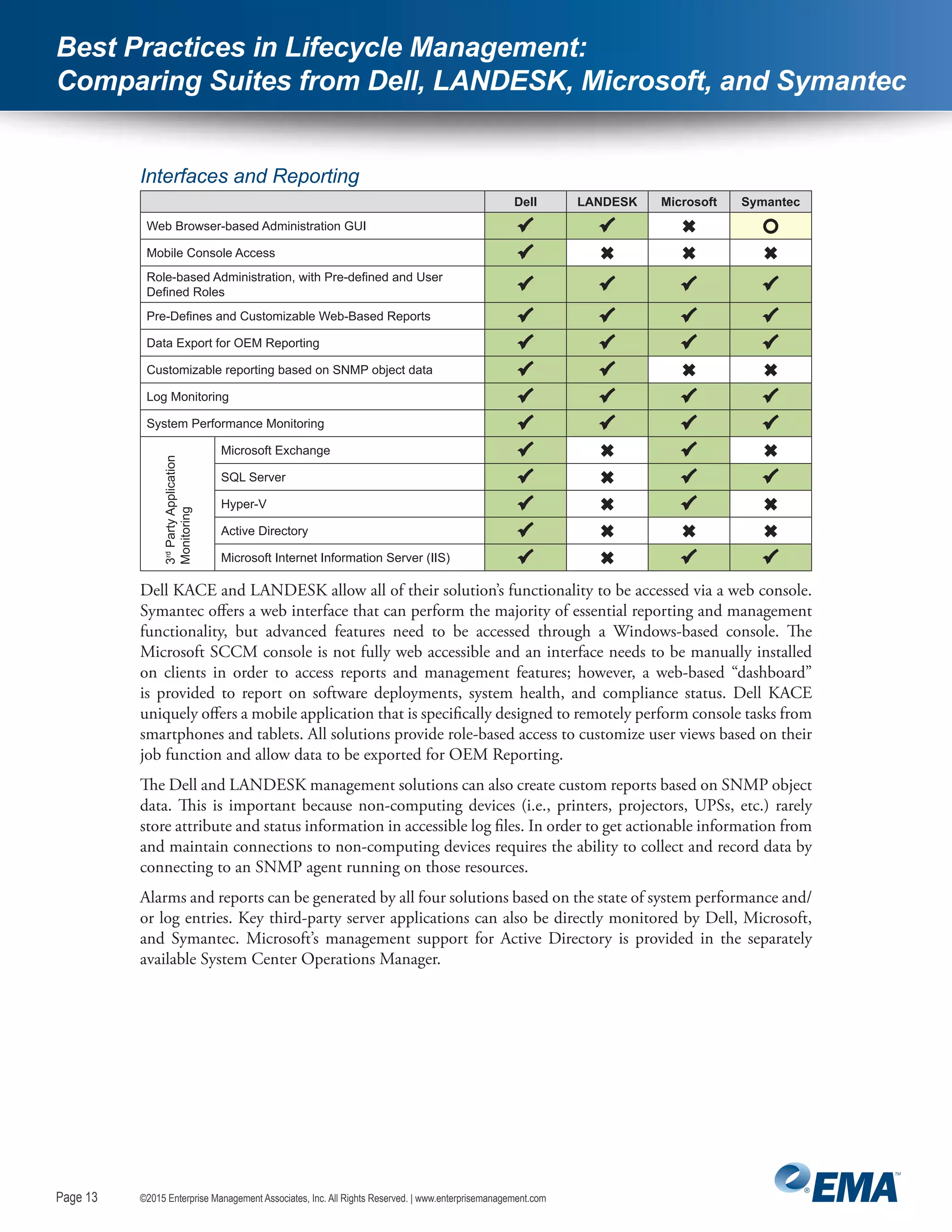
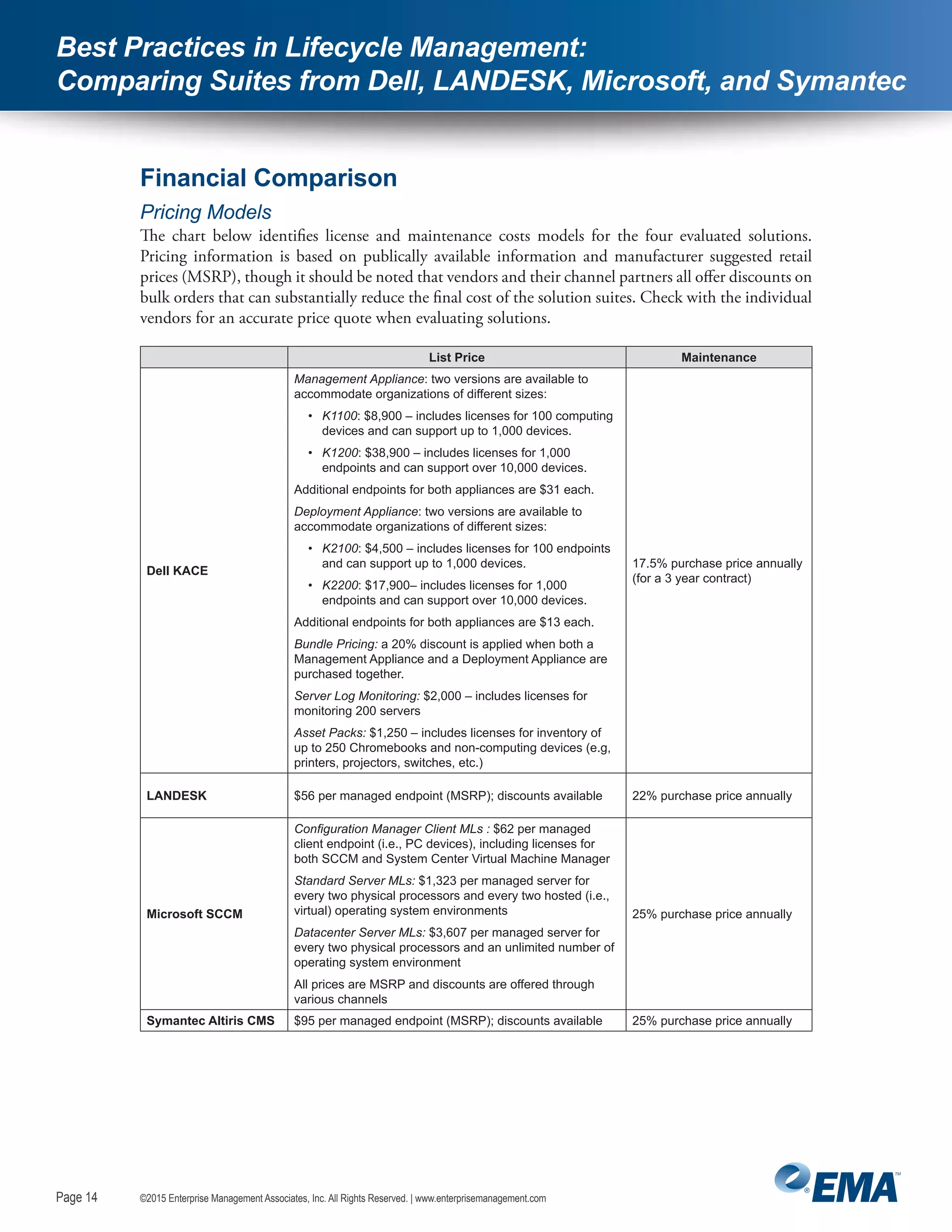
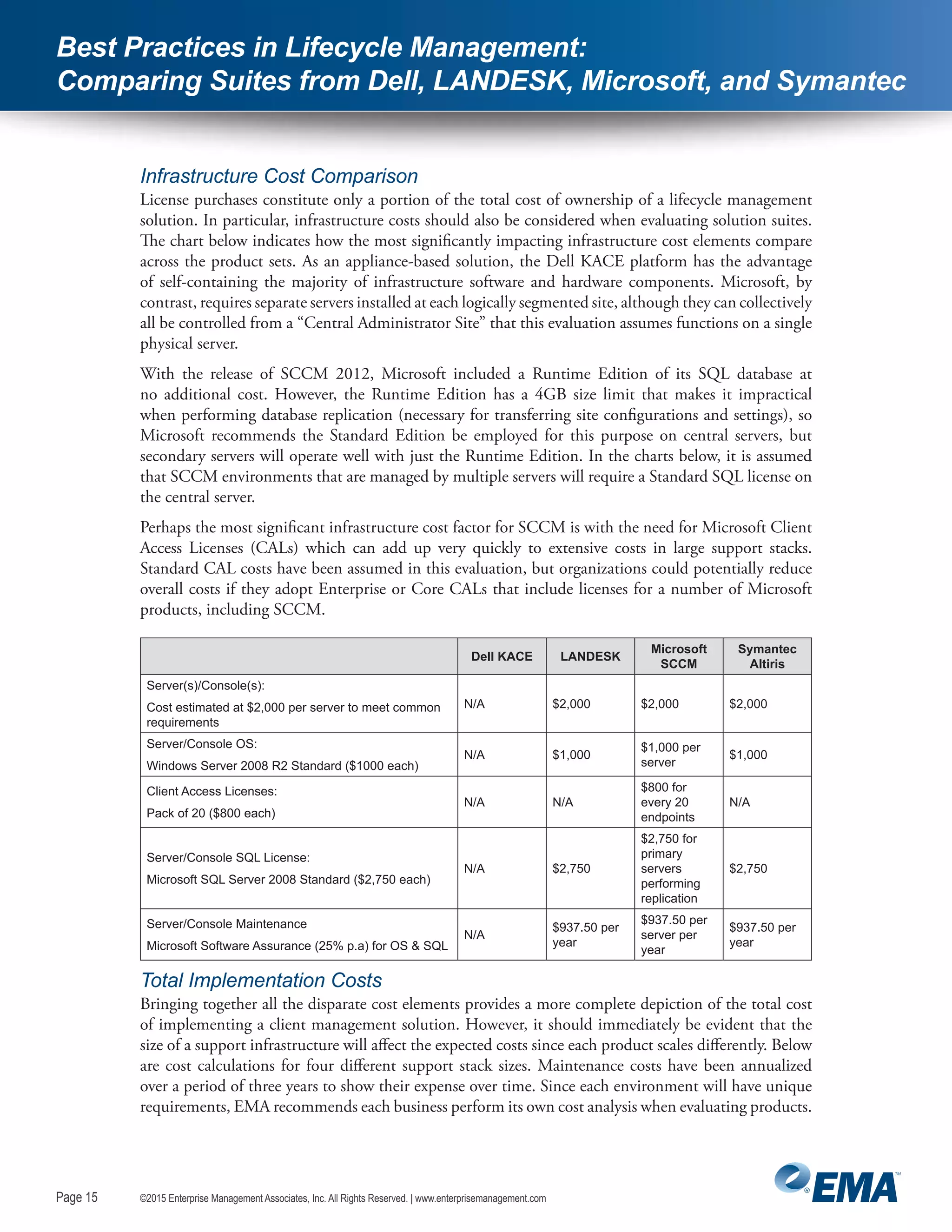
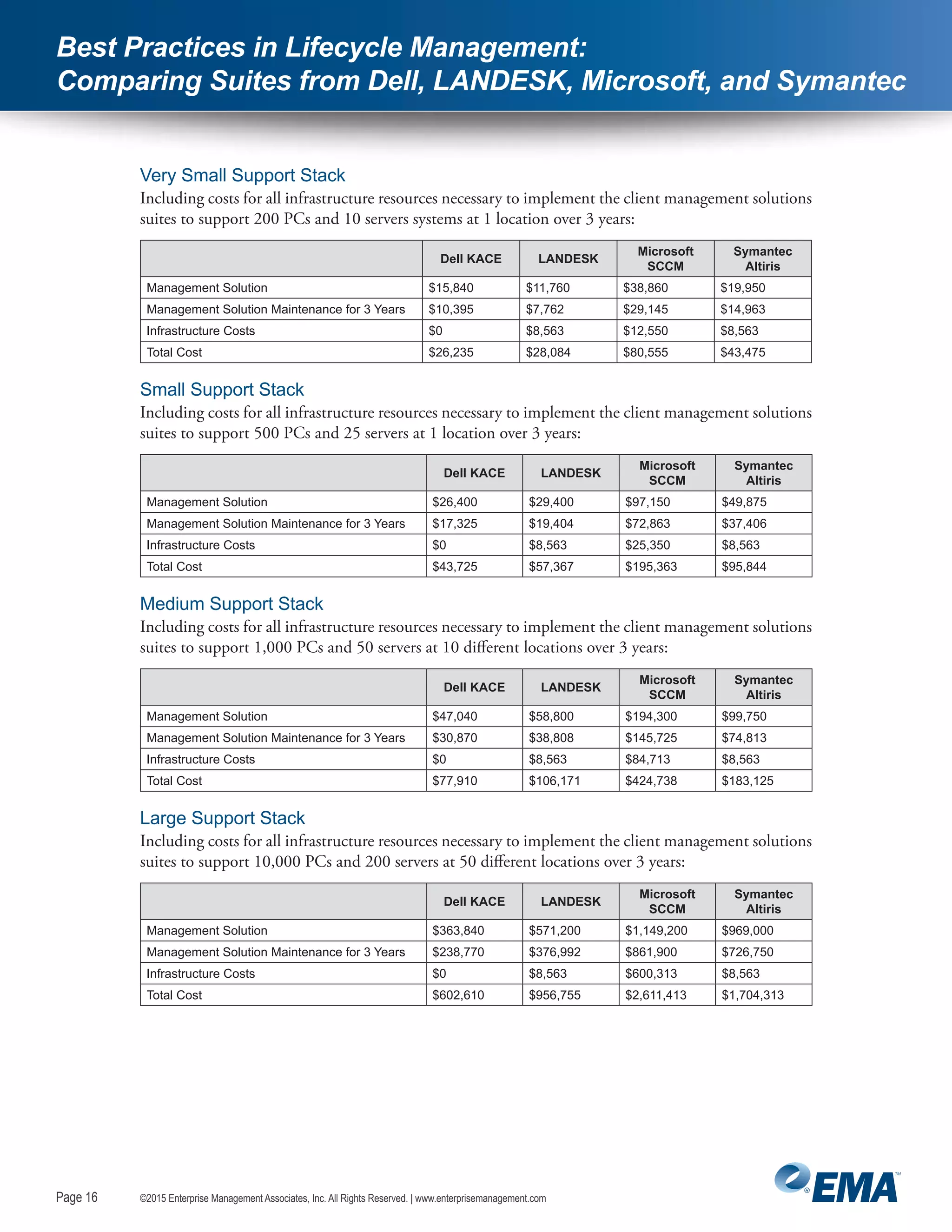
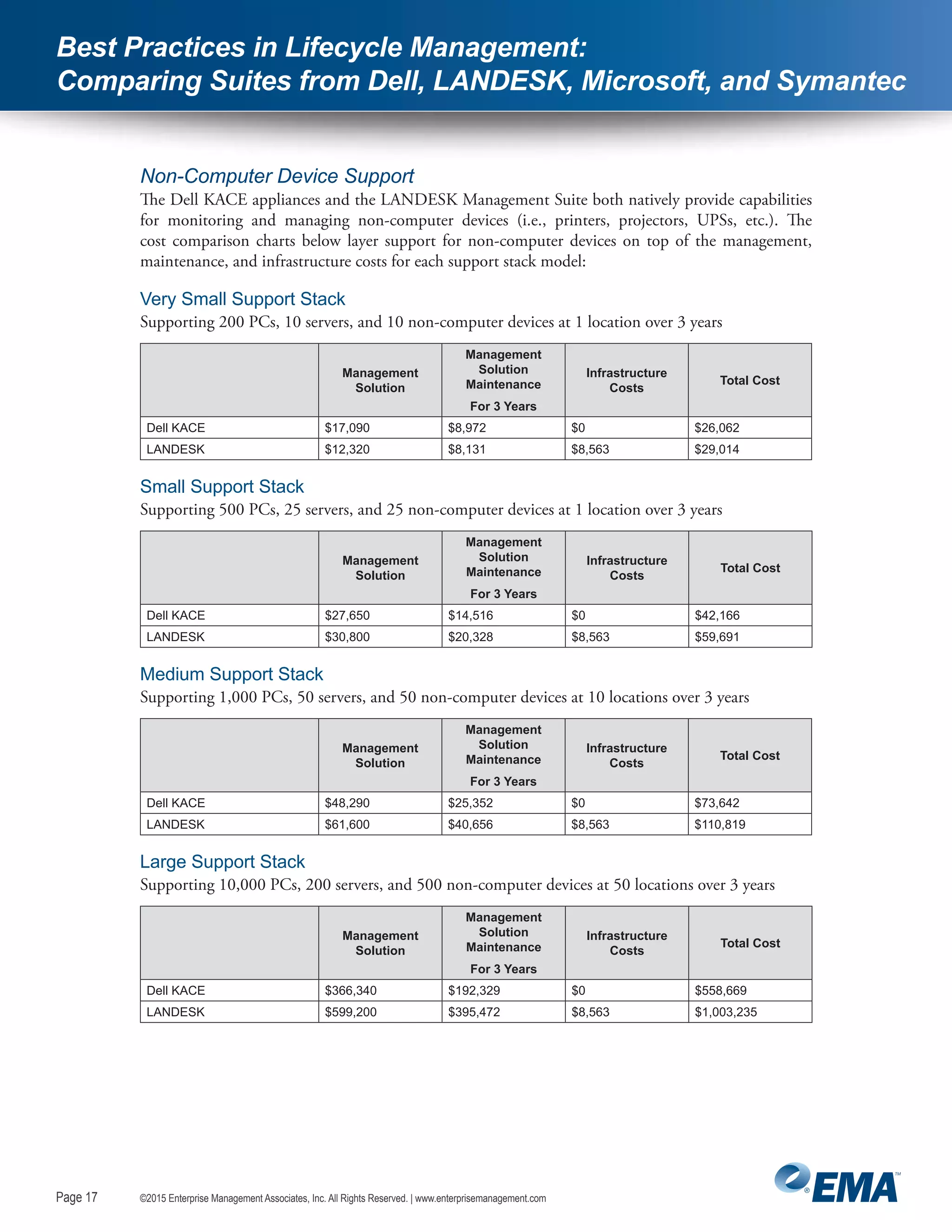
The document provides a comparison of lifecycle management capabilities across Dell, LANDESK, Microsoft, and Symantec solutions. It finds that all solutions effectively discover and manage assets on Windows, while Dell offers additional agentless discovery capabilities. Dell also maintains the largest software catalog. Overall, the analysis shows Dell provides comparable functionality to competitors at a lower total cost of ownership.