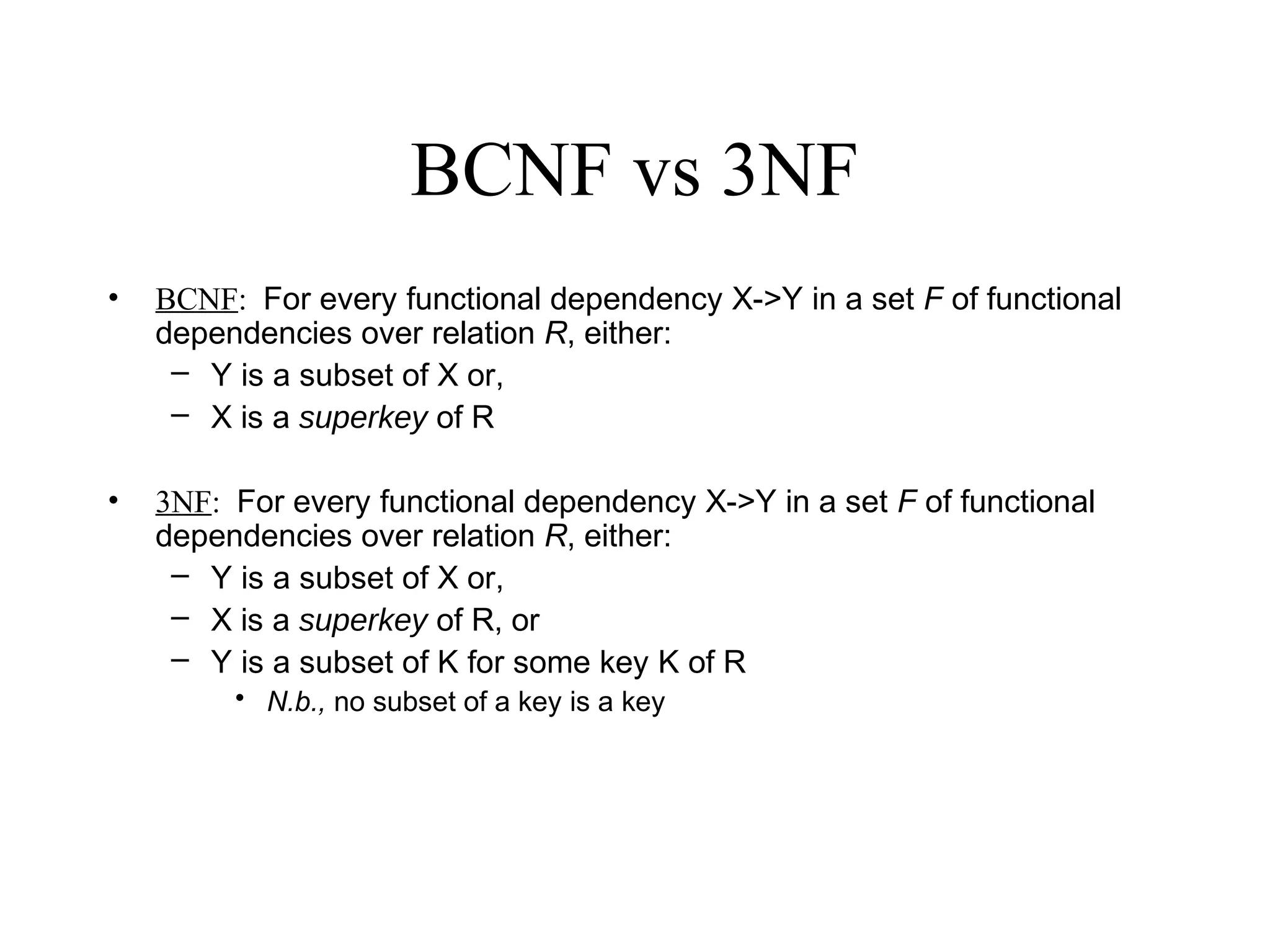
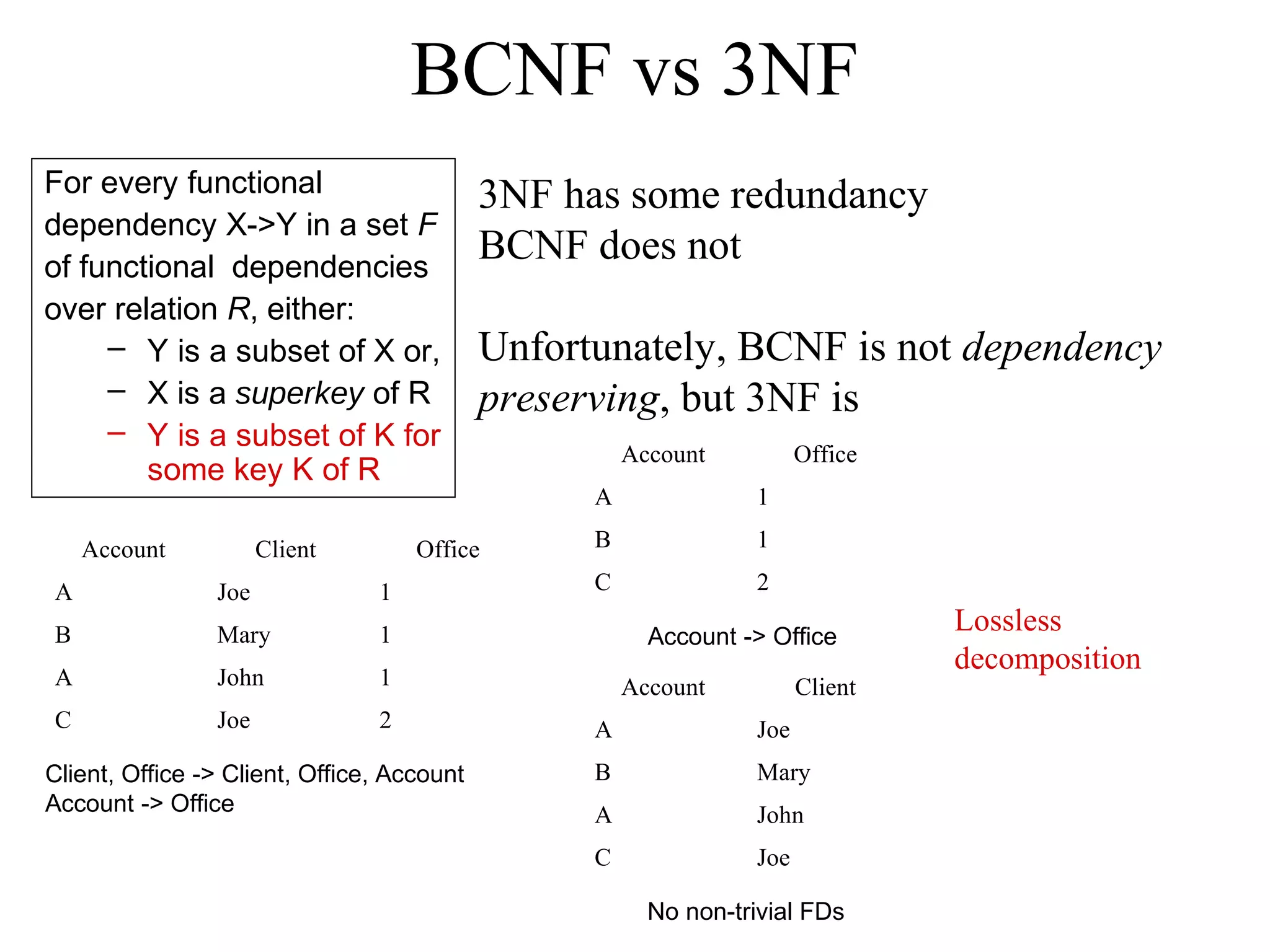
The document compares BCNF and 3NF normal forms. BCNF requires that for every functional dependency X->Y, either Y is a subset of X or X is a superkey. 3NF is less restrictive, also allowing Y to be a subset of some key K. While 3NF allows some redundancy, it is dependency preserving, unlike BCNF. The document also provides pseudocode for closure, BCNF decomposition, B-tree insertion, and B-tree deletion algorithms.