Banner Configuration
•
2 likes•330 views
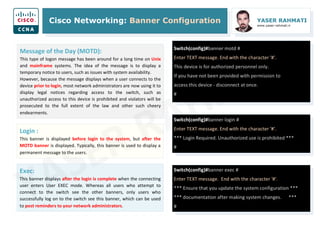
A banner is a message presented to a user who is using the Cisco switch. The type of banner you configured for use determines when this message is shown. You can configure three main types of banners on your Cisco switch, as shown here.
Report
Share
Report
Share
Recommended
Swift Study #7

This document summarizes Swift protocols including defining protocols, conforming to protocols with classes, structures and enums, protocol requirements for properties and methods, protocol inheritance, checking for protocol conformance, optional protocol requirements, and using protocols as types. Protocols allow defining a common behavior that multiple types can conform to, enabling polymorphism.
Navigating the ios

Primary Modes
The two primary modes of operation are user EXEC mode and privileged EXEC mode. Tthe privileged EXEC mode has a higher level of authority in what it allows the user to do with the device.
User EXEC Mode
The user EXEC mode has limited capabilities but is useful for some basic operations. This mode is the first mode encountered upon entrance into the CLI of an IOS device.
This is often referred to as view-only mode. The user EXEC level does not allow the execution of any commands that might change the configuration of the device.
By default, there is no authentication required to access the user EXEC mode from the console. However, it is a good practice to ensure that authentication is configured during the initial configuration.
The user EXEC mode is identified by the CLI prompt that ends with the > symbol. This is an example that shows the > symbol in the prompt: Switch>
Privileged EXEC Mode
The execution of configuration and management commands requires that the network administrator use the privileged EXEC mode, or a more specific mode in the hierarchy.
The privileged EXEC mode can be identified by the prompt ending with the #symbol. Switch#
By default, privileged EXEC mode does not require authentication.
Global configuration mode and all other more specific configuration modes can only be reached from the privileged EXEC mode.
Global Configuration Mode and Submodes
Global configuration mode and interface configuration modes can only be reached from the privileged EXEC mode.
From global config, CLI configuration changes are made that affect the operation of the device as a whole.
Switch# configure terminal
Switch(config)#
From the global config mode, the user can enter different subconfiguration modes. Each of these modes allows the configuration of a particular part or function of the IOS device.
Interface mode - to configure one of the network interfaces (Fa0/0, S0/0/0)
Line mode - to configure one of the physical or virtual lines (console, AUX, VTY)
To exit a specific configuration mode and return to global configuration mode, enter exit at a prompt. To leave configuration mode completely and return to privileged EXEC mode, enter end or use the key sequence Ctrl-Z.
As commands are used and modes are changed, the prompt changes to reflect the current context.
Web engine

Blog engine adalah aplikasi berbasis web untuk membuat blog. Beberapa contoh blog engine gratis berbasis PHP adalah WordPress, Drupal, dan Joomla, sementara blog engine gratis lainnya termasuk WordPress.com, Blogspot.com, dan Tumblr.com. Keuntungan menggunakan blog engine adalah fleksibilitas untuk mengustomisasi tampilan dan fitur serta kemampuan mengkonfigurasi sendiri.
Logros de la revolución ciudadana 

Este documento presenta las 35 propuestas del programa de gobierno del Movimiento Alianza PAIS para el período 2013-2017. Las propuestas se agrupan en 10 áreas de transformación: revolución económica, del conocimiento, social, de la justicia, cultural, ética, política y constitucional, de la soberanía y la integración, ecológica y urbana. El objetivo general es profundizar la Revolución Ciudadana para construir una sociedad más justa basada en el buen vivir.
Introduction to Infrastructure as Code & Automation / Introduction to Chef

The document discusses infrastructure as code and Chef. It introduces Chef as an open source automation framework that allows system administrators to define infrastructure in code. It describes how Chef uses a policy-based approach to ensure nodes comply with defined policies and discusses how this allows for scalable, automated management of infrastructure.
OSPF 2

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
Password Recovery

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
RIP Update Timers

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
Recommended
Swift Study #7

This document summarizes Swift protocols including defining protocols, conforming to protocols with classes, structures and enums, protocol requirements for properties and methods, protocol inheritance, checking for protocol conformance, optional protocol requirements, and using protocols as types. Protocols allow defining a common behavior that multiple types can conform to, enabling polymorphism.
Navigating the ios

Primary Modes
The two primary modes of operation are user EXEC mode and privileged EXEC mode. Tthe privileged EXEC mode has a higher level of authority in what it allows the user to do with the device.
User EXEC Mode
The user EXEC mode has limited capabilities but is useful for some basic operations. This mode is the first mode encountered upon entrance into the CLI of an IOS device.
This is often referred to as view-only mode. The user EXEC level does not allow the execution of any commands that might change the configuration of the device.
By default, there is no authentication required to access the user EXEC mode from the console. However, it is a good practice to ensure that authentication is configured during the initial configuration.
The user EXEC mode is identified by the CLI prompt that ends with the > symbol. This is an example that shows the > symbol in the prompt: Switch>
Privileged EXEC Mode
The execution of configuration and management commands requires that the network administrator use the privileged EXEC mode, or a more specific mode in the hierarchy.
The privileged EXEC mode can be identified by the prompt ending with the #symbol. Switch#
By default, privileged EXEC mode does not require authentication.
Global configuration mode and all other more specific configuration modes can only be reached from the privileged EXEC mode.
Global Configuration Mode and Submodes
Global configuration mode and interface configuration modes can only be reached from the privileged EXEC mode.
From global config, CLI configuration changes are made that affect the operation of the device as a whole.
Switch# configure terminal
Switch(config)#
From the global config mode, the user can enter different subconfiguration modes. Each of these modes allows the configuration of a particular part or function of the IOS device.
Interface mode - to configure one of the network interfaces (Fa0/0, S0/0/0)
Line mode - to configure one of the physical or virtual lines (console, AUX, VTY)
To exit a specific configuration mode and return to global configuration mode, enter exit at a prompt. To leave configuration mode completely and return to privileged EXEC mode, enter end or use the key sequence Ctrl-Z.
As commands are used and modes are changed, the prompt changes to reflect the current context.
Web engine

Blog engine adalah aplikasi berbasis web untuk membuat blog. Beberapa contoh blog engine gratis berbasis PHP adalah WordPress, Drupal, dan Joomla, sementara blog engine gratis lainnya termasuk WordPress.com, Blogspot.com, dan Tumblr.com. Keuntungan menggunakan blog engine adalah fleksibilitas untuk mengustomisasi tampilan dan fitur serta kemampuan mengkonfigurasi sendiri.
Logros de la revolución ciudadana 

Este documento presenta las 35 propuestas del programa de gobierno del Movimiento Alianza PAIS para el período 2013-2017. Las propuestas se agrupan en 10 áreas de transformación: revolución económica, del conocimiento, social, de la justicia, cultural, ética, política y constitucional, de la soberanía y la integración, ecológica y urbana. El objetivo general es profundizar la Revolución Ciudadana para construir una sociedad más justa basada en el buen vivir.
Introduction to Infrastructure as Code & Automation / Introduction to Chef

The document discusses infrastructure as code and Chef. It introduces Chef as an open source automation framework that allows system administrators to define infrastructure in code. It describes how Chef uses a policy-based approach to ensure nodes comply with defined policies and discusses how this allows for scalable, automated management of infrastructure.
OSPF 2

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
Password Recovery

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
RIP Update Timers

This study guide is intended to provide those pursuing the CCNA certification with a framework of what concepts need to be studied. This is not a comprehensive document containing all the secrets of the CCNA, nor is it a “braindump” of questions and answers.
I sincerely hope that this document provides some assistance and clarity in your studies.
Pwning bsnl

The document summarizes vulnerabilities in UTSTARCOM routers distributed by BSNL in India that allow unauthorized access and control. The routers have hard-coded default credentials that can be easily exploited to gain administrative access. Once compromised, the routers are open to denial of service attacks, traffic sniffing, and phishing. The document provides proof-of-concept code to remotely access a vulnerable router and change its settings without authentication. It also discusses potential mitigations like changing default passwords and implementing proper access control on the router instead of using client-side scripts.
BSNL hacks

The document summarizes vulnerabilities in UTSTARCOM routers distributed by BSNL in India that allow unauthorized access and control. The routers have hard-coded default credentials, lack proper access control, and have flaws that allow privileges to be escalated. This allows attackers to compromise routers remotely and carry out denial of service attacks, sniffing, or phishing. The document provides proofs-of-concept code to remotely access and reconfigure victim routers without authentication. It is recommended to change default credentials, implement server-side access control instead of client-side scripts, and provide better user instructions.
Cisco Router and Switch Security Hardening Guide

10 important steps to secure and harden Cisco IOS network devices. Security checklist and configuration guide.
Host Based Security Best Practices

This document provides guidelines for securing host-based systems. It recommends installing and configuring a host-based firewall, keeping the operating system and applications patched, backing up the system regularly, monitoring logs, disabling unused services, using strong passwords, replacing insecure services with secure alternatives like SSH, and restricting access to services where possible. It then provides more detailed recommendations for securing Windows, UNIX, Linux, and RedHat Linux systems during installation and configuration.
MARS User Login Logout MIS for Cisco Call Manager

This document provides an overview of PARSEC's "User EM based Login Logout MIS (ELLM)" application for Cisco CUCM. The application collects user login and logout data from Cisco IP phones using Extension Mobility. It stores this historical data in a Microsoft SQL database. The ELLM application then provides web-based reports and downloads of this login/logout activity including user login durations, individual user login/logout times, and device details. The system requirements specify that the ELLM application needs to be installed on a separate Windows server with SQL Server, and have access to the Cisco CallManager cluster in order to collect Extension Mobility data.
Campaign of networking in csit association of Nepal

This document summarizes a networking presentation by CAS Group. It discusses virtual networking using virtual machines, wired networking using switches and routers, and wireless networking using WiFi access points. Key topics covered include the definition of virtual machines and their advantages, how to set up wired and wireless local area networks, and demonstrations of file sharing, remote desktop connections, and shutting down computers on the network. The presentation aims to teach networking concepts and skills to IT students.
Total control brochure_sb-047a

TotalControl software allows users to remotely monitor and control building automation systems from any internet-connected device with a web browser. It integrates data from multiple building control protocols into a central database and presents customizable interface pages. Users can view alarms, schedules, trends and control systems. TotalControl provides unified control of building functions like HVAC, security and energy use from any location.
Pandora FMS: Cisco Remote inventory modules

Three modules for the remote inventory feature on Pandora FMS Enterprise. Get's information from CISCO devices like CPU, IOS version, Interfaces and other hardware info (version, s/n). For mo
CCNA Icnd110 s04l04

The document discusses the startup process of a Cisco router. It describes how the router performs POST and loads the IOS image at startup. It then lists the interfaces found and their status before configuration. It walks through configuring global parameters such as the hostname, passwords, and IP settings. Finally it recaps how to access privileged EXEC mode, check configurations, and verify a router's initial startup status using show commands.
Remote Login

Remote login allows users to access and control a remote computer over a network connection. It involves installing desktop sharing software on both the host and client computers. The client software connects the user's keyboard and display to the host computer, allowing them to interact with it remotely. Desktop sharing works by encrypting and transmitting packets of information about the host's screen to the client. Remote login is commonly used for remote technical support and real-time collaboration between coworkers in different locations. While convenient, it also presents security risks that require the use of secure protocols like SSH.
Backdoor Entry to a Windows Computer

This document discusses the creation of a backdoor to gain unauthorized access to a Windows computer. It begins with an abstract that outlines creating an advanced backdoor file that works like normal files but allows an attacker to retain access and make changes. The document then covers how backdoors work by bypassing authentication, different types of backdoors like Trojans and web shells, an overview of the proposed backdoor system using Python sockets and commands, and requirements for the system.
Securing Switch Access 

Switches direct and control much of the data flowing across computer networks.
Conventional network security often focuses more on routers and blocking traffic from the outside.
Switches are internal to the organization and designed to allow ease of connectivity, therefore only
limited or no security measures are applied.
How to configure cisco router password

This document provides instructions for configuring passwords on a Cisco router to restrict access to the console, virtual terminals (VTY), and privileged EXEC mode. It explains that passwords should be set on the console and VTY lines to prevent unauthorized access. The steps shown allow setting passwords on the console line using the "line console 0" and "password" commands. VTY line passwords are configured on lines 0 to 4 using similar commands. Privileged EXEC mode passwords can be set with the "enable password" command, while "enable secret" encrypts the password. Finally, the "service password-encryption" command encrypts all router passwords.
Embedded monitordescription

The document describes an application called embeddedmonitor.com that allows non-GSM devices to send and receive SMS alerts virtually through a server. It provides a 3-tier architecture where Ethernet devices can post messages to the server over HTTP, the server manages subscriptions and sends SMS messages, and users receive alerts on their phones. Key benefits are that devices do not need SIM cards or GSM capabilities, and programming logic is simplified. The document provides instructions for testing the system by emulating messages from a web form or Excel macro.
Network security

This document discusses network security and firewalls. It explains that network security aims to create a secure computing platform and protect systems from hackers through devices like firewalls. Firewalls examine incoming and outgoing messages on a network and block those that do not meet security criteria. They can filter network traffic using packet filtering, proxy services, or stateful inspection. Firewalls are customizable and can filter based on IP addresses, domains, protocols, and other conditions to control network access and traffic flow.
B1803011013

The document describes an integrated home automation system that allows users to control devices locally or remotely using GSM, web, or speech-based commands. The system has two main modules: 1) a server module with a database that stores control requests and commands devices, and 2) hardware interface modules that provide connections to home appliances. Users can send control requests via SMS, a web interface, or voice commands, which are stored in the server database and carried out by activating the relevant hardware interfaces. The system aims to provide a flexible platform for remote home device control using different input methods.
network security

This document discusses securing Cisco routers. It covers topics like securing physical and remote access to routers, configuring administrative roles and views, and monitoring router activity. Some key points include assigning privilege levels to restrict commands, creating CLI views to control command access for different user roles, and using login features like quiet mode, block lists, and banners to restrict failed login attempts. The document provides examples of securing routers by configuring services like SSH and encrypting passwords.
Networking and Computer Troubleshooting

This document provides information on various topics related to computer networks and security. It discusses network switches and routers, different types of network cables, examples of networked applications through history, peer-to-peer and cloud computing, transmission speed measurements, the differences between local and wide area networks, common computer troubleshooting steps, and methods for password protecting computers and setting BIOS passwords. The overall focus is on fundamental concepts of computer networks, applications, and basic security practices.
A Complete Software Engineer With Hardware / Networking Skill's

1. The document discusses various techniques for verifying user identities on dynamic websites, including two-step verification using SMS codes, face recognition, voice recognition, fingerprint scanning, and eye/retina scanning.
2. It also recommends steps to enhance security for customized client-side systems, such as using unique credentials for users, databases, firewalls, antivirus software, and encrypting sensitive data.
3. Recommended security measures include changing default passwords, installing firewalls, regular backups, and only enabling necessary ports when connecting systems to the internet or remote databases.
Cisco WLAN - Chapter. 08 : Applications, Design, and Site Survey Preparation

This document discusses site surveys for wireless networks. It describes the steps in performing a site survey, including gathering tools and documentation. Key considerations for site surveys are determining feasible coverage, identifying interference sources, and understanding wired connectivity limitations. Proper documentation of access point locations and network information is also discussed. Site surveys are important for designing a wireless network that meets coverage, capacity, and reliability needs.
Cisco WLAN - Chapter. 07 : Antennas

The document discusses various types of antennas used for wireless LANs. It describes how directional antennas radiate RF energy predominantly in one direction, while omnidirectional antennas radiate equally in all horizontal directions. Key points include:
- Directional antennas include Yagis and parabolic dishes, which have a narrow beamwidth. Omnidirectional types include dipoles, patches, and various indoor/outdoor models.
- Parameters like gain, beamwidth, bandwidth, polarization and EIRP are defined. Higher gain antennas have a stronger but narrower signal.
- Common Cisco antenna models are described for 2.4GHz and 5GHz networks, including rubber ducks, ceiling mounts,
More Related Content
Similar to Banner Configuration
Pwning bsnl

The document summarizes vulnerabilities in UTSTARCOM routers distributed by BSNL in India that allow unauthorized access and control. The routers have hard-coded default credentials that can be easily exploited to gain administrative access. Once compromised, the routers are open to denial of service attacks, traffic sniffing, and phishing. The document provides proof-of-concept code to remotely access a vulnerable router and change its settings without authentication. It also discusses potential mitigations like changing default passwords and implementing proper access control on the router instead of using client-side scripts.
BSNL hacks

The document summarizes vulnerabilities in UTSTARCOM routers distributed by BSNL in India that allow unauthorized access and control. The routers have hard-coded default credentials, lack proper access control, and have flaws that allow privileges to be escalated. This allows attackers to compromise routers remotely and carry out denial of service attacks, sniffing, or phishing. The document provides proofs-of-concept code to remotely access and reconfigure victim routers without authentication. It is recommended to change default credentials, implement server-side access control instead of client-side scripts, and provide better user instructions.
Cisco Router and Switch Security Hardening Guide

10 important steps to secure and harden Cisco IOS network devices. Security checklist and configuration guide.
Host Based Security Best Practices

This document provides guidelines for securing host-based systems. It recommends installing and configuring a host-based firewall, keeping the operating system and applications patched, backing up the system regularly, monitoring logs, disabling unused services, using strong passwords, replacing insecure services with secure alternatives like SSH, and restricting access to services where possible. It then provides more detailed recommendations for securing Windows, UNIX, Linux, and RedHat Linux systems during installation and configuration.
MARS User Login Logout MIS for Cisco Call Manager

This document provides an overview of PARSEC's "User EM based Login Logout MIS (ELLM)" application for Cisco CUCM. The application collects user login and logout data from Cisco IP phones using Extension Mobility. It stores this historical data in a Microsoft SQL database. The ELLM application then provides web-based reports and downloads of this login/logout activity including user login durations, individual user login/logout times, and device details. The system requirements specify that the ELLM application needs to be installed on a separate Windows server with SQL Server, and have access to the Cisco CallManager cluster in order to collect Extension Mobility data.
Campaign of networking in csit association of Nepal

This document summarizes a networking presentation by CAS Group. It discusses virtual networking using virtual machines, wired networking using switches and routers, and wireless networking using WiFi access points. Key topics covered include the definition of virtual machines and their advantages, how to set up wired and wireless local area networks, and demonstrations of file sharing, remote desktop connections, and shutting down computers on the network. The presentation aims to teach networking concepts and skills to IT students.
Total control brochure_sb-047a

TotalControl software allows users to remotely monitor and control building automation systems from any internet-connected device with a web browser. It integrates data from multiple building control protocols into a central database and presents customizable interface pages. Users can view alarms, schedules, trends and control systems. TotalControl provides unified control of building functions like HVAC, security and energy use from any location.
Pandora FMS: Cisco Remote inventory modules

Three modules for the remote inventory feature on Pandora FMS Enterprise. Get's information from CISCO devices like CPU, IOS version, Interfaces and other hardware info (version, s/n). For mo
CCNA Icnd110 s04l04

The document discusses the startup process of a Cisco router. It describes how the router performs POST and loads the IOS image at startup. It then lists the interfaces found and their status before configuration. It walks through configuring global parameters such as the hostname, passwords, and IP settings. Finally it recaps how to access privileged EXEC mode, check configurations, and verify a router's initial startup status using show commands.
Remote Login

Remote login allows users to access and control a remote computer over a network connection. It involves installing desktop sharing software on both the host and client computers. The client software connects the user's keyboard and display to the host computer, allowing them to interact with it remotely. Desktop sharing works by encrypting and transmitting packets of information about the host's screen to the client. Remote login is commonly used for remote technical support and real-time collaboration between coworkers in different locations. While convenient, it also presents security risks that require the use of secure protocols like SSH.
Backdoor Entry to a Windows Computer

This document discusses the creation of a backdoor to gain unauthorized access to a Windows computer. It begins with an abstract that outlines creating an advanced backdoor file that works like normal files but allows an attacker to retain access and make changes. The document then covers how backdoors work by bypassing authentication, different types of backdoors like Trojans and web shells, an overview of the proposed backdoor system using Python sockets and commands, and requirements for the system.
Securing Switch Access 

Switches direct and control much of the data flowing across computer networks.
Conventional network security often focuses more on routers and blocking traffic from the outside.
Switches are internal to the organization and designed to allow ease of connectivity, therefore only
limited or no security measures are applied.
How to configure cisco router password

This document provides instructions for configuring passwords on a Cisco router to restrict access to the console, virtual terminals (VTY), and privileged EXEC mode. It explains that passwords should be set on the console and VTY lines to prevent unauthorized access. The steps shown allow setting passwords on the console line using the "line console 0" and "password" commands. VTY line passwords are configured on lines 0 to 4 using similar commands. Privileged EXEC mode passwords can be set with the "enable password" command, while "enable secret" encrypts the password. Finally, the "service password-encryption" command encrypts all router passwords.
Embedded monitordescription

The document describes an application called embeddedmonitor.com that allows non-GSM devices to send and receive SMS alerts virtually through a server. It provides a 3-tier architecture where Ethernet devices can post messages to the server over HTTP, the server manages subscriptions and sends SMS messages, and users receive alerts on their phones. Key benefits are that devices do not need SIM cards or GSM capabilities, and programming logic is simplified. The document provides instructions for testing the system by emulating messages from a web form or Excel macro.
Network security

This document discusses network security and firewalls. It explains that network security aims to create a secure computing platform and protect systems from hackers through devices like firewalls. Firewalls examine incoming and outgoing messages on a network and block those that do not meet security criteria. They can filter network traffic using packet filtering, proxy services, or stateful inspection. Firewalls are customizable and can filter based on IP addresses, domains, protocols, and other conditions to control network access and traffic flow.
B1803011013

The document describes an integrated home automation system that allows users to control devices locally or remotely using GSM, web, or speech-based commands. The system has two main modules: 1) a server module with a database that stores control requests and commands devices, and 2) hardware interface modules that provide connections to home appliances. Users can send control requests via SMS, a web interface, or voice commands, which are stored in the server database and carried out by activating the relevant hardware interfaces. The system aims to provide a flexible platform for remote home device control using different input methods.
network security

This document discusses securing Cisco routers. It covers topics like securing physical and remote access to routers, configuring administrative roles and views, and monitoring router activity. Some key points include assigning privilege levels to restrict commands, creating CLI views to control command access for different user roles, and using login features like quiet mode, block lists, and banners to restrict failed login attempts. The document provides examples of securing routers by configuring services like SSH and encrypting passwords.
Networking and Computer Troubleshooting

This document provides information on various topics related to computer networks and security. It discusses network switches and routers, different types of network cables, examples of networked applications through history, peer-to-peer and cloud computing, transmission speed measurements, the differences between local and wide area networks, common computer troubleshooting steps, and methods for password protecting computers and setting BIOS passwords. The overall focus is on fundamental concepts of computer networks, applications, and basic security practices.
A Complete Software Engineer With Hardware / Networking Skill's

1. The document discusses various techniques for verifying user identities on dynamic websites, including two-step verification using SMS codes, face recognition, voice recognition, fingerprint scanning, and eye/retina scanning.
2. It also recommends steps to enhance security for customized client-side systems, such as using unique credentials for users, databases, firewalls, antivirus software, and encrypting sensitive data.
3. Recommended security measures include changing default passwords, installing firewalls, regular backups, and only enabling necessary ports when connecting systems to the internet or remote databases.
Similar to Banner Configuration (20)
Campaign of networking in csit association of Nepal

Campaign of networking in csit association of Nepal
A Complete Software Engineer With Hardware / Networking Skill's

A Complete Software Engineer With Hardware / Networking Skill's
More from Yaser Rahmati
Cisco WLAN - Chapter. 08 : Applications, Design, and Site Survey Preparation

This document discusses site surveys for wireless networks. It describes the steps in performing a site survey, including gathering tools and documentation. Key considerations for site surveys are determining feasible coverage, identifying interference sources, and understanding wired connectivity limitations. Proper documentation of access point locations and network information is also discussed. Site surveys are important for designing a wireless network that meets coverage, capacity, and reliability needs.
Cisco WLAN - Chapter. 07 : Antennas

The document discusses various types of antennas used for wireless LANs. It describes how directional antennas radiate RF energy predominantly in one direction, while omnidirectional antennas radiate equally in all horizontal directions. Key points include:
- Directional antennas include Yagis and parabolic dishes, which have a narrow beamwidth. Omnidirectional types include dipoles, patches, and various indoor/outdoor models.
- Parameters like gain, beamwidth, bandwidth, polarization and EIRP are defined. Higher gain antennas have a stronger but narrower signal.
- Common Cisco antenna models are described for 2.4GHz and 5GHz networks, including rubber ducks, ceiling mounts,
Cisco WLAN - Chapter. 06 : bridges

Cisco Fundamentals of Wireless LANs
Ch. 06 - Bridges
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Cisco WLAN - Chapter. 05 : Access Points

Cisco Fundamentals of Wireless LANs
Ch. 05 – Access Points
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Cisco WLAN - Chapter. 03 : wireless radio technology

This document provides an overview of wireless radio technology concepts including:
1. Wireless propagation is affected by attenuation from obstructions, reflection, refraction, and diffraction of radio signals. Multipath reflection can reduce signal strength.
2. Weather such as rain, snow, ice and wind can impact wireless signals through attenuation, damage to antennas, or changing the aim of antennas.
3. Wireless power is measured in watts and decays exponentially over distance according to the inverse square law. Power ratios and decibel measurements are used to quantify changes in signal strength.
Cisco WLAN - Chapter. 04 : wireless topologies

This document provides an overview of wireless topologies, including:
- Wireless devices must use 802.11 standards for interoperability.
- Access points connect wireless networks to wired networks and allow wireless clients to connect.
- Antennas are selected based on the access point and desired coverage area.
- Topologies include basic service sets using a single access point, extended service sets connecting multiple access points to a wired network, and wireless bridges connecting networks in different buildings with a point-to-point configuration.
- Proper channel planning is important to minimize interference between overlapping wireless networks.
Cisco WLAN - Chapter. 02 : Part 3 – 802.11 phy

Cisco Fundamentals of Wireless LANs
Cisco Fundamentals of Wireless LANs - Ch. 02 – Part 3 – 802.11 PHY
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Cisco WLAN - Chapter. 02 : Part 2 – 802.11 MAC

Cisco Fundamentals of Wireless LANs
Cisco Fundamentals of Wireless LANs - Ch. 02 – Part 2 – 802.11 MAC
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Cisco WLAN - Chapter. 02 : Part 1 – 802.11 MAC and Cisco Client Adapters

Cisco Fundamentals of Wireless LANs
Ch. 02 – Part 1 – 802.11 MAC and Cisco Client Adapters
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Cisco WLAN - Chapter. 01 : Overview of Wireless LANs

Cisco Fundamentals of Wireless LANs
Ch. 01 – Overview of Wireless LANs (WLANs)
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
MTCNA - MikroTik Certified Network Associate - v2

MTCNA Outline
Module 1 : introduction
Module 2 : DHCP
Module 3 : Bridging
Module 4 : Routing
Module 5 : Wireless
Module 7 : QoS
Module 8 : Tunnels
Module 9 : Misc
Find me in :
https://www.instagram.com/yaser.rahmati
Chapter 07 - Routing Dynamically

Chapter 7: Objectives
--------------------------------------------
Explain the basic operation of dynamic routing protocols.
Compare and contrast dynamic and static routing.
Determine which networks are available during an initial network discovery phase.
Define the different categories of routing protocols.
Describe the process by which distance vector routing protocols learn about other networks.
Identify the types of distance-vector routing protocols.
Configure the RIP routing protocol.
Configure the RIPng routing protocol.
Explain the process by which link-state routing protocols learn about other networks.
Describe the information sent in a link-state update.
Describe advantages and disadvantages of using link-state routing protocols.
Identify protocols that use the link-state routing process. (OSPF, IS-IS)
Determine the route source, administrative distance, and metric for a given route.
Explain the concept of a parent/child relationship in a dynamically built routing table.
Compare the IPv4 classless route lookup process and the IPv6 lookup process.
Analyze a routing table to determine which route will be used to forward a packet.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 11 - Network Address Translation for IPv4

Chapter 11: Objectives
------------------------------------------------------
Describe NAT characteristics.
Describe the benefits and drawbacks of NAT.
Configure static NAT using the CLI.
Configure dynamic NAT using the CLI.
Configure PAT using the CLI.
Configure port forwarding using the CLI.
Configure NAT64.
Use show commands to verify NAT operation.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 10 - DHCP

Chapter 10: Objectives
------------------------------------------------------
Describe the operation of DHCPv4 in a small-to-medium-sized business network.
Configure a router as a DHCPv4 server.
Configure a router as a DHCPv4 client.
Troubleshoot a DHCP configuration for IPv4 in a switched network.
Explain the operation of DHCPv6.
Configure a stateless DHCPv6 for a small-to-medium-sized business.
Configure a stateful DHCPv6 for a small-to-medium-sized business.
Troubleshoot a DHCP configuration for IPv6 in a switched network.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 09 - Access Control Lists

Chapter 9: Objectives
-----------------------------------------------------------
Explain how ACLs are used to filter traffic.
Compare standard and extended IPv4 ACLs.
Explain how ACLs use wildcard masks.
Explain the guidelines for creating ACLs.
Explain the guidelines for placement of ACLs.
Configure standard IPv4 ACLs to filter traffic according to networking requirements.
Modify a standard IPv4 ACL using sequence numbers.
Configure a standard ACL to secure vty access.
Explain the structure of an extended access control entry (ACE).
Configure extended IPv4 ACLs to filter traffic according to networking requirements.
Configure an ACL to limit debug output.
Explain how a router processes packets when an ACL is applied.
Troubleshoot common ACL errors using CLI commands.
Compare IPv4 and IPv6 ACL creation.
Configure IPv6 ACLs to filter traffic according to networking requirements.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 08 - Single-Area OSPF

OSPF Accumulates Costs
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 06 - Static Routing

Chapter 6: Objectives
-----------------------------------------------
Explain the advantages and disadvantages of static routing.
Explain the purpose of different types of static routes.
Configure IPv4 and IPv6 static routes by specifying a next-hop address.
Configure an IPv4 and IPv6 default routes.
Explain the use of legacy classful addressing in network implementation.
Explain the purpose of CIDR in replacing classful addressing.
Design and implement a hierarchical addressing scheme.
Configure an IPv4 and IPv6 summary network address to reduce the number of routing table updates.
Configure a floating static route to provide a backup connection.
Explain how a router processes packets when a static route is configured.
Troubleshoot common static and default route configuration issues.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 04 - Routing Concepts

Chapter 4: Objectives
-------------------------------------------------
Configure a router to route between multiple directly connected networks
Describe the primary functions and features of a router.
Explain how routers use information in data packets to make forwarding decisions in a small- to medium-sized business network.
Explain the encapsulation and de-encapsulation process used by routers when switching packets between interfaces.
Compare ways in which a router builds a routing table when operating in a small- to medium-sized business network.
Explain routing table entries for directly connected networks.
Explain how a router builds a routing table of directly connected networks.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 05 - Inter-VLAN Routing

Chapter 5: Objectives
---------------------------------------------------------
Describe the three primary options for enabling inter-VLAN routing.
Configure legacy inter-VLAN routing.
Configure router-on-a-stick inter-VLAN routing.
Troubleshoot common inter-VLAN configuration issues.
Troubleshoot common IP addressing issues in an inter-VLAN-routed environment.
Configure inter-VLAN routing using Layer 3 switching.
Troubleshoot inter-VLAN routing in a Layer 3-switched environment.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
Chapter 02 - Introduction to Switched Networks

Chapter 2: Objectives
--------------------------------------------------
Upon completion of this chapter, you will be able to:
Explain the advantages and disadvantages of static routing.
Configure initial settings on a Cisco switch.
Configure switch ports to meet network requirements.
Configure the management switch virtual interface.
Describe basic security attacks in a switched environment.
Describe security best practices in a switched environment.
Configure the port security feature to restrict network access.
Yaser Rahmati | یاسر رحمتی
Rahmati Academy | آکادمی رحمتی
www.yaser-rahmati.ir
www.rahmati-academy.ir
More from Yaser Rahmati (20)
Cisco WLAN - Chapter. 08 : Applications, Design, and Site Survey Preparation

Cisco WLAN - Chapter. 08 : Applications, Design, and Site Survey Preparation
Cisco WLAN - Chapter. 03 : wireless radio technology

Cisco WLAN - Chapter. 03 : wireless radio technology
Cisco WLAN - Chapter. 02 : Part 1 – 802.11 MAC and Cisco Client Adapters

Cisco WLAN - Chapter. 02 : Part 1 – 802.11 MAC and Cisco Client Adapters
Cisco WLAN - Chapter. 01 : Overview of Wireless LANs

Cisco WLAN - Chapter. 01 : Overview of Wireless LANs
Recently uploaded
Your Skill Boost Masterclass: Strategies for Effective Upskilling

Your Skill Boost Masterclass: Strategies for Effective UpskillingExcellence Foundation for South Sudan
Strategies for Effective Upskilling is a presentation by Chinwendu Peace in a Your Skill Boost Masterclass organisation by the Excellence Foundation for South Sudan on 08th and 09th June 2024 from 1 PM to 3 PM on each day.Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...Dr. Vinod Kumar Kanvaria
Exploiting Artificial Intelligence for Empowering Researchers and Faculty,
International FDP on Fundamentals of Research in Social Sciences
at Integral University, Lucknow, 06.06.2024
By Dr. Vinod Kumar KanvariaMATATAG CURRICULUM: ASSESSING THE READINESS OF ELEM. PUBLIC SCHOOL TEACHERS I...

In this research, it concludes that while the readiness of teachers in Caloocan City to implement the MATATAG Curriculum is generally positive, targeted efforts in professional development, resource distribution, support networks, and comprehensive preparation can address the existing gaps and ensure successful curriculum implementation.
A Survey of Techniques for Maximizing LLM Performance.pptx

A Survey of Techniques for Maximizing LLM Performance
DRUGS AND ITS classification slide share

Any substance (other than food) that is used to prevent, diagnose, treat, or relieve symptoms of a
disease or abnormal condition
Introduction to AI for Nonprofits with Tapp Network

Dive into the world of AI! Experts Jon Hill and Tareq Monaur will guide you through AI's role in enhancing nonprofit websites and basic marketing strategies, making it easy to understand and apply.
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama UniversityAkanksha trivedi rama nursing college kanpur.
Natural birth techniques are various type such as/ water birth , alexender method, hypnosis, bradley method, lamaze method etcChapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is special for master students (MIBS & MIFB) in UUM. Also useful for readers who are interested in the topic of contemporary Islamic banking.
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
Azure Interview Questions and Answers PDF By ScholarHat

Azure Interview Questions and Answers PDF By ScholarHat
Advanced Java[Extra Concepts, Not Difficult].docx![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This is part 2 of my Java Learning Journey. This contains Hashing, ArrayList, LinkedList, Date and Time Classes, Calendar Class and more.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
Recently uploaded (20)
Liberal Approach to the Study of Indian Politics.pdf

Liberal Approach to the Study of Indian Politics.pdf
Pride Month Slides 2024 David Douglas School District

Pride Month Slides 2024 David Douglas School District
Your Skill Boost Masterclass: Strategies for Effective Upskilling

Your Skill Boost Masterclass: Strategies for Effective Upskilling
Group Presentation 2 Economics.Ariana Buscigliopptx

Group Presentation 2 Economics.Ariana Buscigliopptx
Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...
MATATAG CURRICULUM: ASSESSING THE READINESS OF ELEM. PUBLIC SCHOOL TEACHERS I...

MATATAG CURRICULUM: ASSESSING THE READINESS OF ELEM. PUBLIC SCHOOL TEACHERS I...
A Survey of Techniques for Maximizing LLM Performance.pptx

A Survey of Techniques for Maximizing LLM Performance.pptx
Introduction to AI for Nonprofits with Tapp Network

Introduction to AI for Nonprofits with Tapp Network
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama University
Chapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptx
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
Azure Interview Questions and Answers PDF By ScholarHat

Azure Interview Questions and Answers PDF By ScholarHat
Banner Configuration
- 1. Cisco Networking: Banner Configuration YASER RAHMATI www.yaser-rahmati.ir Switch(config)#banner motd # Enter TEXT message. End with the character '#'. This device is for authorized personnel only. If you have not been provided with permission to access this device - disconnect at once. # Message of the Day (MOTD): This type of logon message has been around for a long time on Unix and mainframe systems. The idea of the message is to display a temporary notice to users, such as issues with system availability. However, because the message displays when a user connects to the device prior to login, most network administrators are now using it to display legal notices regarding access to the switch, such as unauthorized access to this device is prohibited and violators will be prosecuted to the full extent of the law and other such cheery endearments. Switch(config)#banner login # Enter TEXT message. End with the character '#'. *** Login Required. Unauthorized use is prohibited *** # Switch(config)#banner exec # Enter TEXT message. End with the character '#'. *** Ensure that you update the system configuration *** *** documentation after making system changes. *** # Login : This banner is displayed before login to the system, but after the MOTD banner is displayed. Typically, this banner is used to display a permanent message to the users. Exec: This banner displays after the login is complete when the connecting user enters User EXEC mode. Whereas all users who attempt to connect to the switch see the other banners, only users who successfully log on to the switch see this banner, which can be used to post reminders to your network administrators.
