Backup and restore router configuration
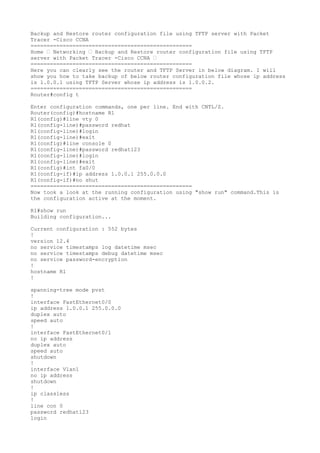
- 1. Backup and Restore router configuration file using TFTP server with Packet Tracer -Cisco CCNA ================================================== Home › Networking › Backup and Restore router configuration file using TFTP server with Packet Tracer -Cisco CCNA › ================================================== Here you can clearly see the router and TFTP Server in below diagram. I will show you how to take backup of below router configuration file whose ip address is 1.0.0.1 using TFTP Server whose ip address is 1.0.0.2. ================================================== Router#config t Enter configuration commands, one per line. End with CNTL/Z. Router(config)#hostname R1 R1(config)#line vty 0 R1(config-line)#password redhat R1(config-line)#login R1(config-line)#exit R1(config)#line console 0 R1(config-line)#password redhat123 R1(config-line)#login R1(config-line)#exit R1(config)#int fa0/0 R1(config-if)#ip address 1.0.0.1 255.0.0.0 R1(config-if)#no shut ================================================== Now took a look at the running configuration using "show run" command.This is the configuration active at the moment. R1#show run Building configuration... Current configuration : 552 bytes ! version 12.4 no service timestamps log datetime msec no service timestamps debug datetime msec no service password-encryption ! hostname R1 ! spanning-tree mode pvst ! interface FastEthernet0/0 ip address 1.0.0.1 255.0.0.0 duplex auto speed auto ! interface FastEthernet0/1 no ip address duplex auto speed auto shutdown ! interface Vlan1 no ip address shutdown ! ip classless ! line con 0 password redhat123 login
- 2. ! line aux 0 ! line vty 0 password redhat login line vty 1 4 login ! end ========================================================= Now using show version or show flash command we can see the router ios file. R1#show version Cisco IOS Software, 1841 Software (C1841-ADVIPSERVICESK9-M), Version 12.4(15)T1, RELEASE SOFTWARE (fc2) Technical Support: http://www.cisco.com/techsupport Copyright (c) 1986-2007 by Cisco Systems, Inc. Compiled Wed 18-Jul-07 04:52 by pt_team ROM: System Bootstrap, Version 12.3(8r)T8, RELEASE SOFTWARE (fc1) System returned to ROM by power-on System image file is "flash:c1841-advipservicesk9-mz.124-15.T1.bin" Cisco 1841 (revision 5.0) with 114688K/16384K bytes of memory. Processor board ID FTX0947Z18E M860 processor: part number 0, mask 49 2 FastEthernet/IEEE 802.3 interface(s) 191K bytes of NVRAM. 63488K bytes of ATA CompactFlash (Read/Write) Configuration register is 0x2102 ========================================================= R1#show flash System flash directory: File Length Name/status 3 33591768 c1841-advipservicesk9-mz.124-15.T1.bin 2 28282 sigdef-category.xml 1 227537 sigdef-default.xml [33847587 bytes used, 30168797 available, 64016384 total] 63488K bytes of processor board System flash (Read/Write) ======================================================= Now we are going to take backup of router IOS on tftp Server using below mentioned command. R1#copy flash tftp Source filename []? c1841-advipservicesk9-mz.124-15.T1.bin Address or name of remote host []? 1.0.0.2 Destination filename [c1841-advipservicesk9-mz.124-15.T1.bin]? Writing c1841-advipservicesk9-mz.124- 15.T1.bin....!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
- 3. !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! [OK - 33591768 bytes] 33591768 bytes copied in 5.796 secs (5795000 bytes/sec) R1# Now copy running-config to startup-config. R1#copy run start Destination filename [startup-config]? Building configuration... [OK] Then copy the startup-config file to tftp server machine so that we can get it back from there whenever we need. R1#copy startup-config tftp Address or name of remote host []? 1.0.0.2 Destination filename [R1-confg]? R1-config Writing startup-config...!! [OK - 552 bytes] 552 bytes copied in 0.001 secs (552000 bytes/sec) Now Go To TFTP Server and Verify: in the above image you can clearly see we have successfully taken backup of Router IOS to tftp Server and router configuration also to tftp server. Now after Backup it's time to test recovery or restore. i.e we will test how to restore router configuration. Here in this tutorial we will discuss about how to restore back router configuration from tftp server. To test restore configuration of router first we need to first erase the configuration on routers. ======================================================== R1#erase startup-config Erasing the nvram filesystem will remove all configuration files! Continue? [confirm] [OK] Erase of nvram: complete %SYS-7-NV_BLOCK_INIT: Initialized the geometry of nvram After erasing check whether you have successfully erased or not. ======================================================== R1#show startup-config startup-config is not present R1# Now you can clearly see there is no output,means no configuration remains now.It means everything has been erased.
- 4. Note:After reload i have a brand new router.Means all previous configuration lost. ======================================================== R1#reload Proceed with reload? [confirm] System Bootstrap, Version 12.3(8r)T8, RELEASE SOFTWARE (fc1) Cisco 1841 (revision 5.0) with 114688K/16384K bytes of memory. Self decompressing the image : ########################################################################## [OK] Restricted Rights Legend --- System Configuration Dialog --- Continue with configuration dialog? [yes/no]: no Press RETURN to get started! Router> Now check your configuration after reload. Router>enable Router#show run Building configuration... Current configuration : 489 bytes ! version 12.4 no service timestamps log datetime msec no service timestamps debug datetime msec no service password-encryption ! hostname Router ! ! ! spanning-tree mode pvst ! interface FastEthernet0/0 no ip address duplex auto speed auto shutdown ! interface FastEthernet0/1 no ip address duplex auto speed auto shutdown ! interface Vlan1 no ip address shutdown ! ip classless Now you can clearly see no ip, no hostaname, everything have been removed from router previous configuration. so now we have to assign ip address again to have a fresh start to connect with tftp so that we recover our configuration file back as it was previous. ======================================================== So we are going to get back our IOS configuration file from tftp server to router using below command. =========================================================
- 5. Router#copy tftp running-config Address or name of remote host []? 1.0.0.2 Source filename []? R1-config Destination filename [running-config]? Accessing tftp://1.0.0.2/R1-config........ %Error opening tftp://1.0.0.2/R1-config (Timed out) Router# You can clearly see that copy from tftp server failed because router interface is down,we have to manualy up router interface ========================================================= Router#config t Enter configuration commands, one per line. End with CNTL/Z. Router(config)#int fa0/0 Router(config-if)#ip address 1.0.0.1 255.0.0.0 Router(config-if)#no shut Now our router interface have an ip address again and port is also up now we can start restore process. Router#copy tftp running-config Address or name of remote host []? 1.0.0.2 Source filename []? R1-config Destination filename [running-config]? Accessing tftp://1.0.0.2/R1-config.... Loading R1-config from 1.0.0.2: ! [OK - 552 bytes] 552 bytes copied in 3.003 secs (183 bytes/sec) R1# %SYS-5-CONFIG_I: Configured from console by console Now check whether we have successfully able to restore our IOS configuration file or not. R1#show run Building configuration... Current configuration : 552 bytes ! version 12.4 no service timestamps log datetime msec no service timestamps debug datetime msec no service password-encryption ! hostname R1 ! ! spanning-tree mode pvst ! interface FastEthernet0/0 ip address 1.0.0.1 255.0.0.0 duplex auto speed auto ! interface FastEthernet0/1 no ip address duplex auto speed auto shutdown !
- 6. interface Vlan1 no ip address shutdown ! ip classless ! ! line con 0 password redhat123 login ! line aux 0 ! line vty 0 password redhat login line vty 1 4 login ! end --More-- You can clearly see that now our router is as it was in start.Everything come back as it is.same password for console port,as it is configuration for telnet. everything as it is. Hence we have successfully restore our router configuration.. ======================================================== this is configuration with troubleshooting for to see how the TFTP server running Thank you..!!!
- 7. interface Vlan1 no ip address shutdown ! ip classless ! ! line con 0 password redhat123 login ! line aux 0 ! line vty 0 password redhat login line vty 1 4 login ! end --More-- You can clearly see that now our router is as it was in start.Everything come back as it is.same password for console port,as it is configuration for telnet. everything as it is. Hence we have successfully restore our router configuration.. ======================================================== this is configuration with troubleshooting for to see how the TFTP server running Thank you..!!!