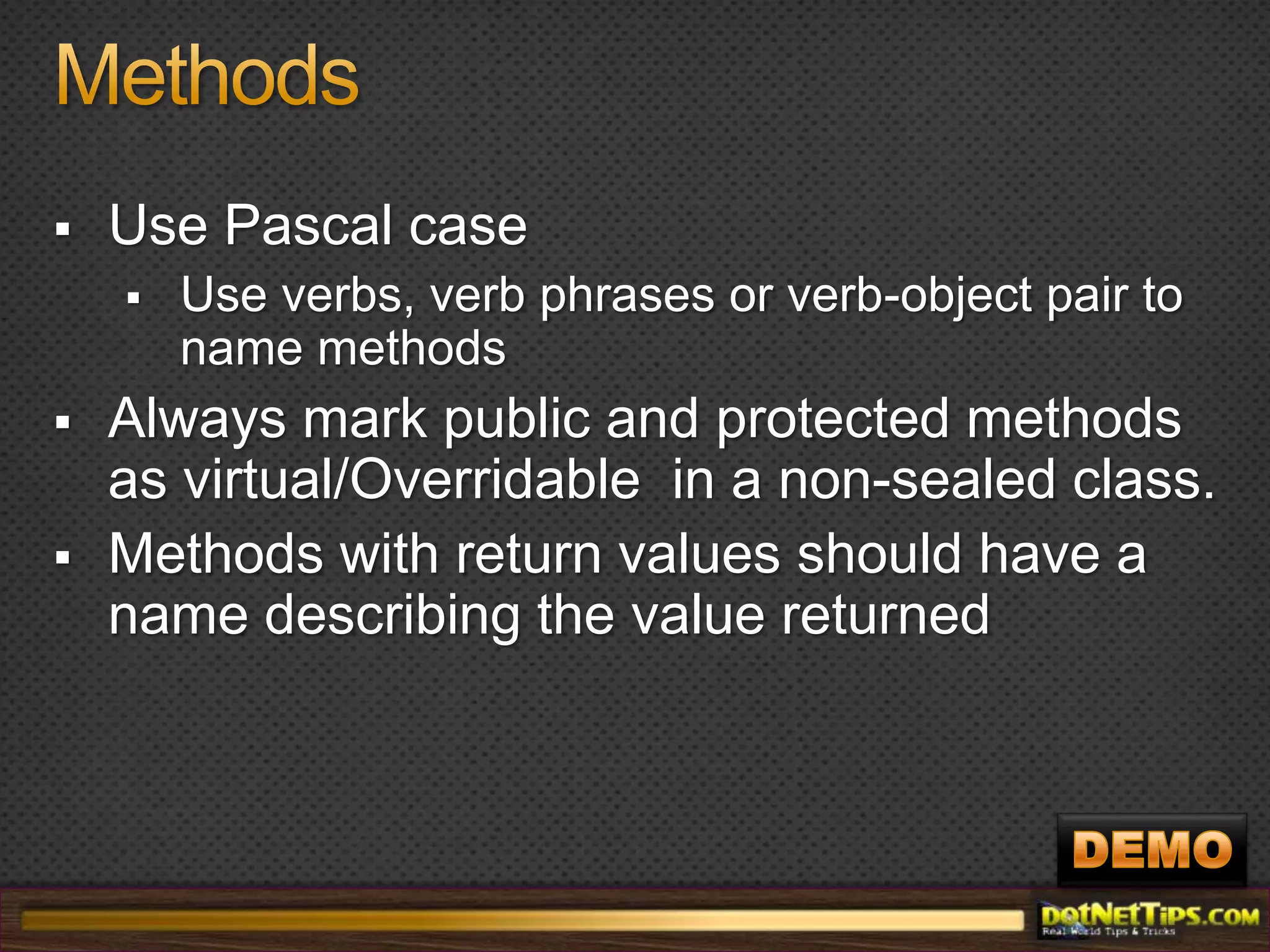
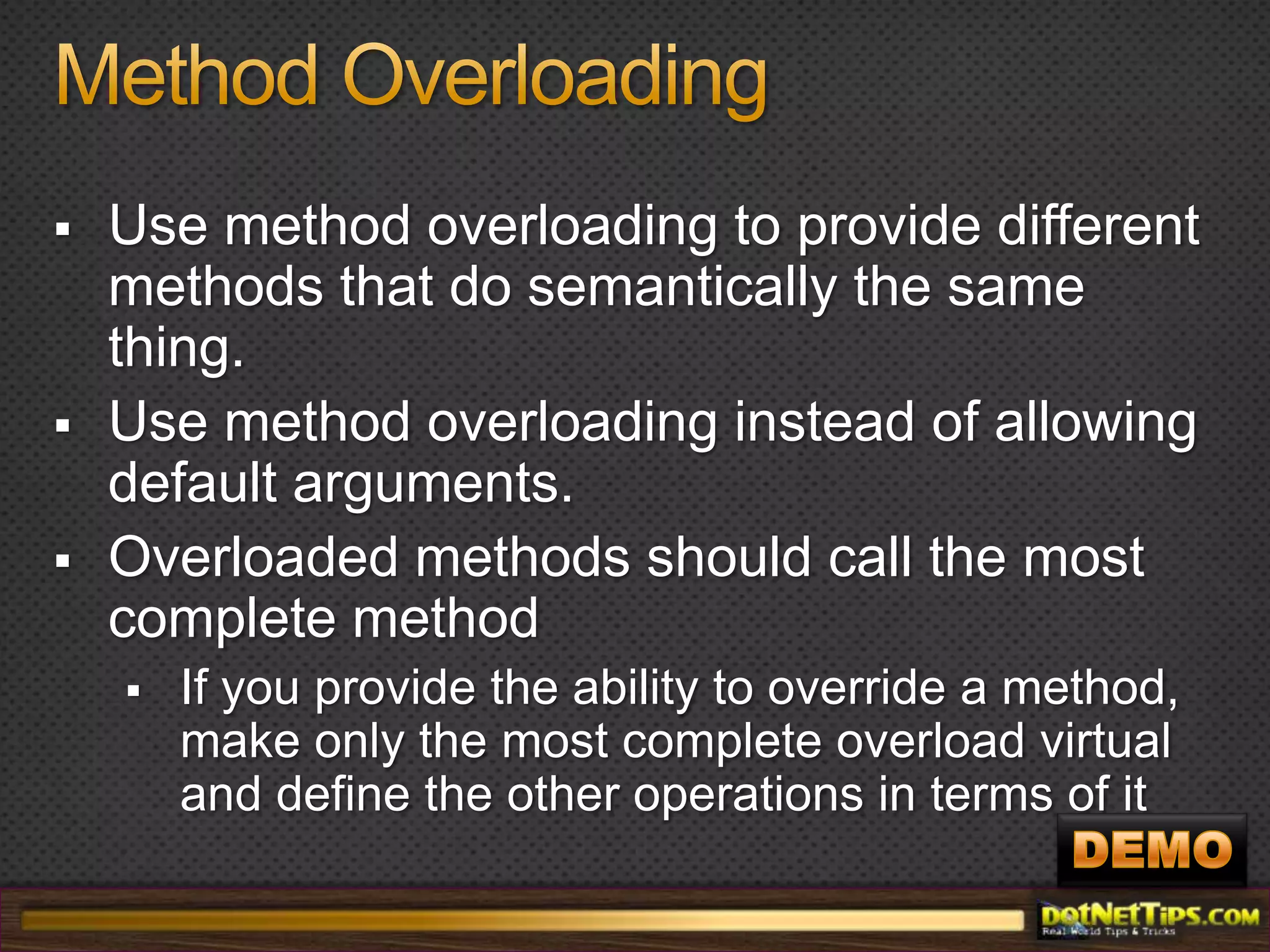
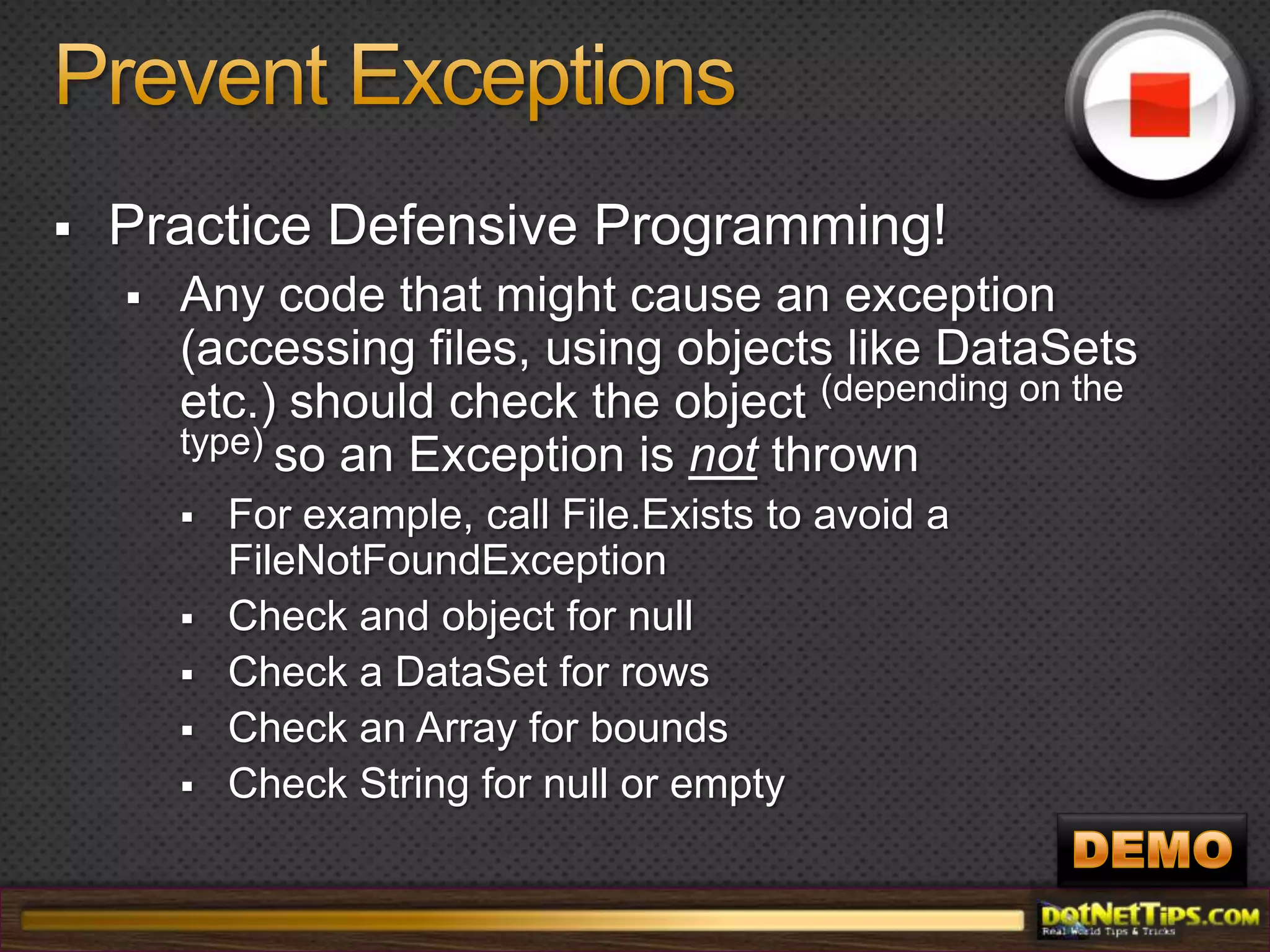
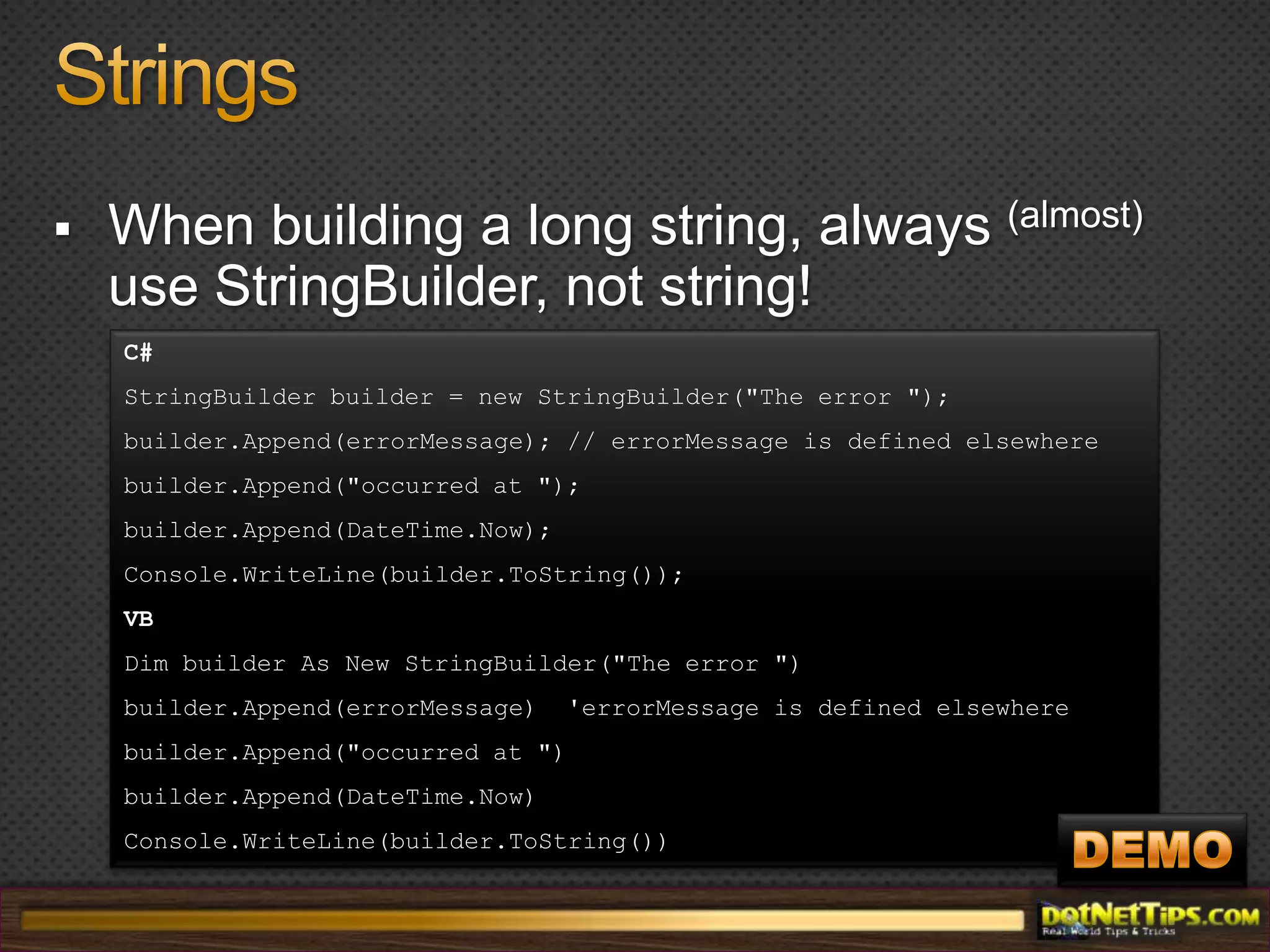
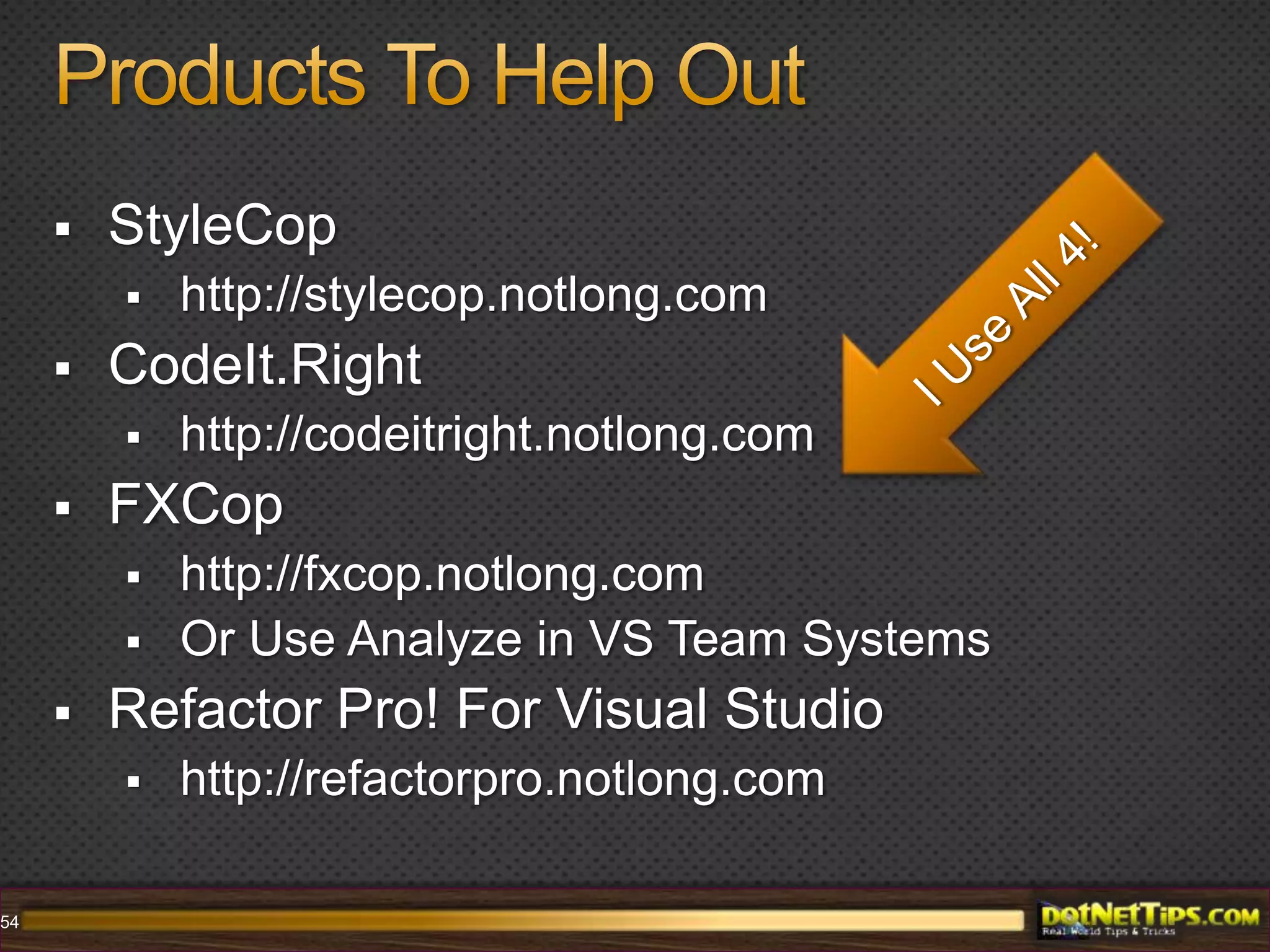
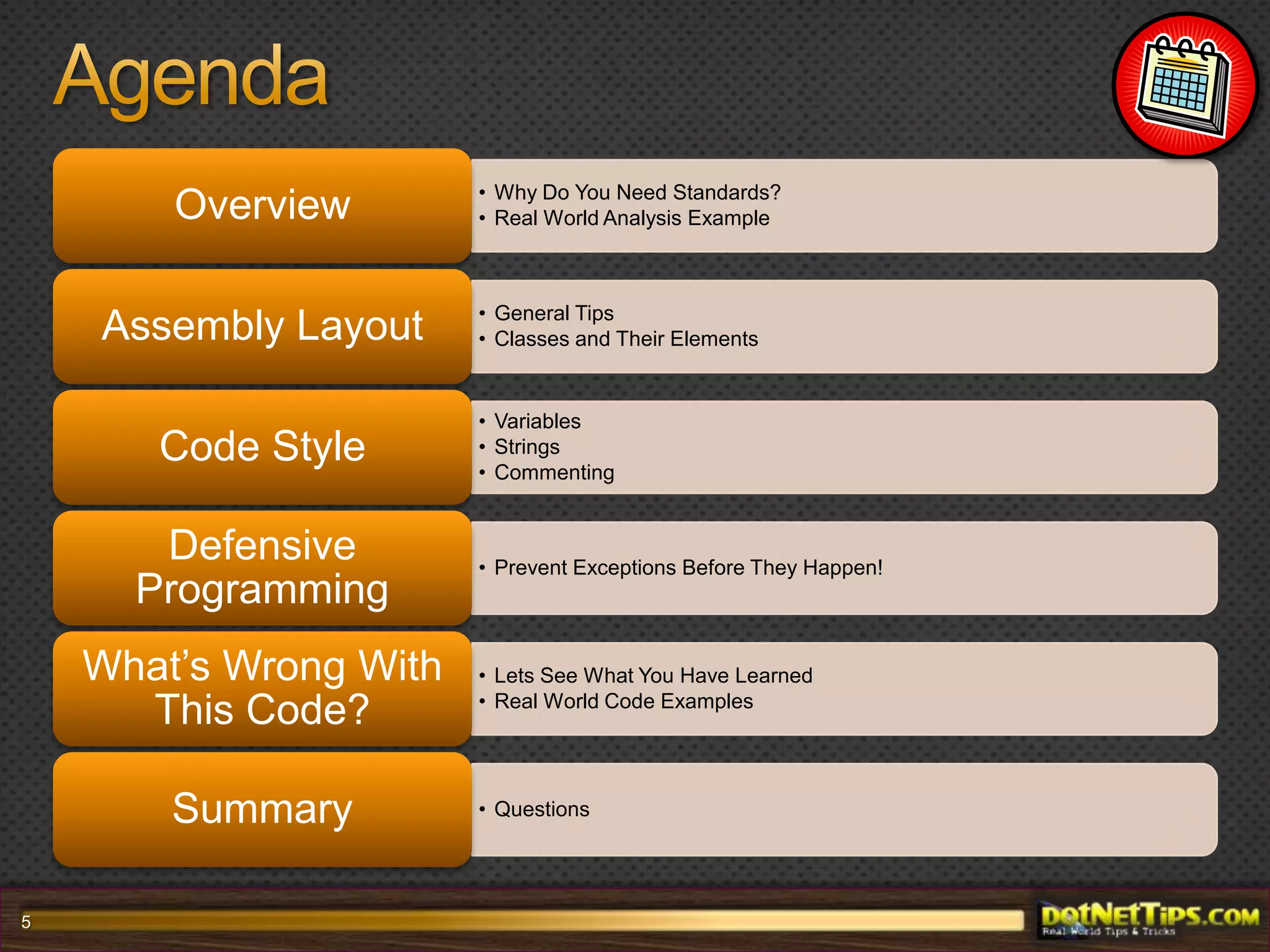
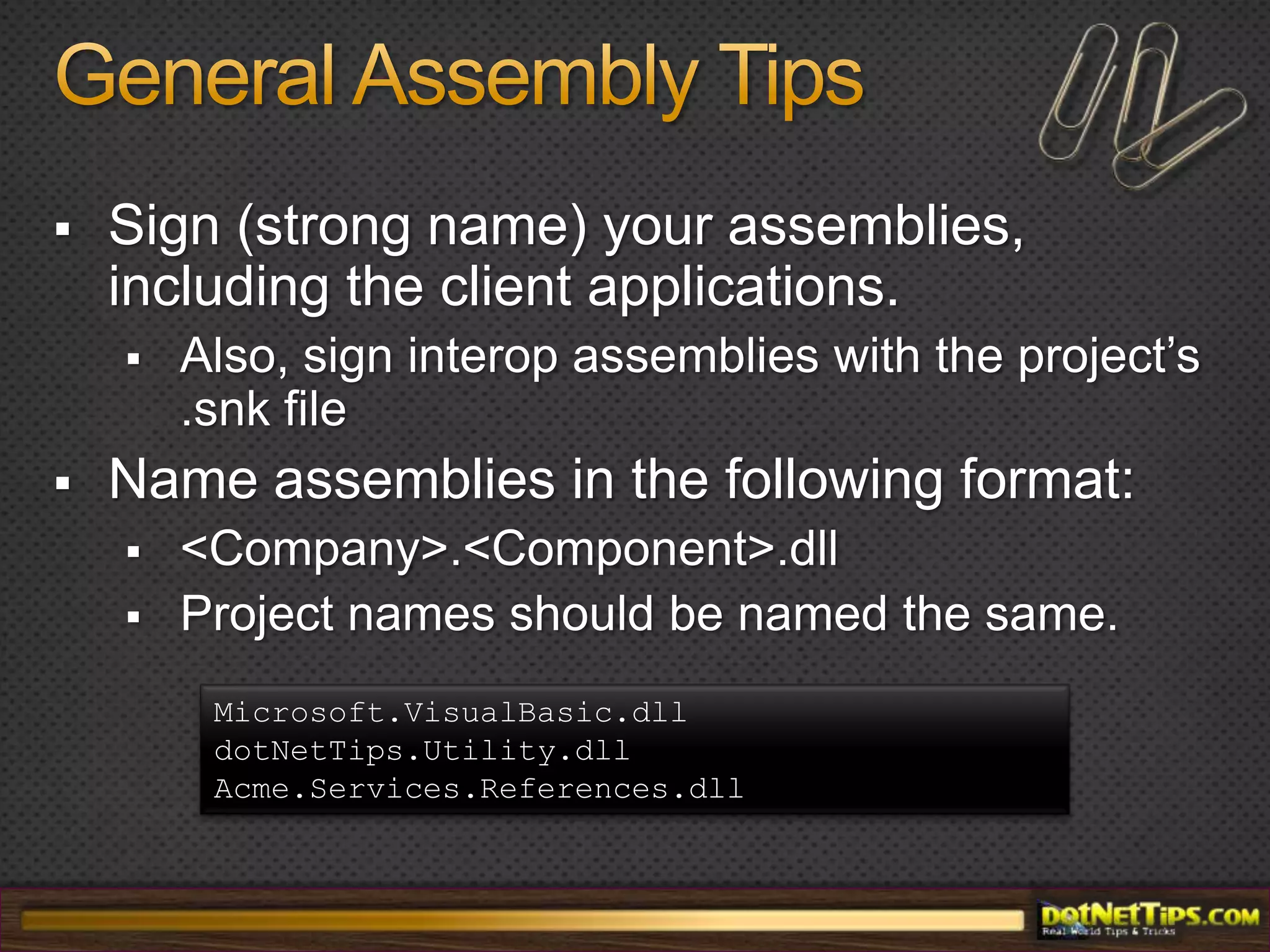
The document discusses .NET coding standards and best practices that enhance code quality and maintainability. It emphasizes the importance of adhering to coding standards for better collaboration among programmers, offering tools like StyleCop and CodeIt.Right for code analysis. Additionally, it provides detailed guidelines on naming conventions, method design, error handling, and defensive programming to prevent exceptions during development.


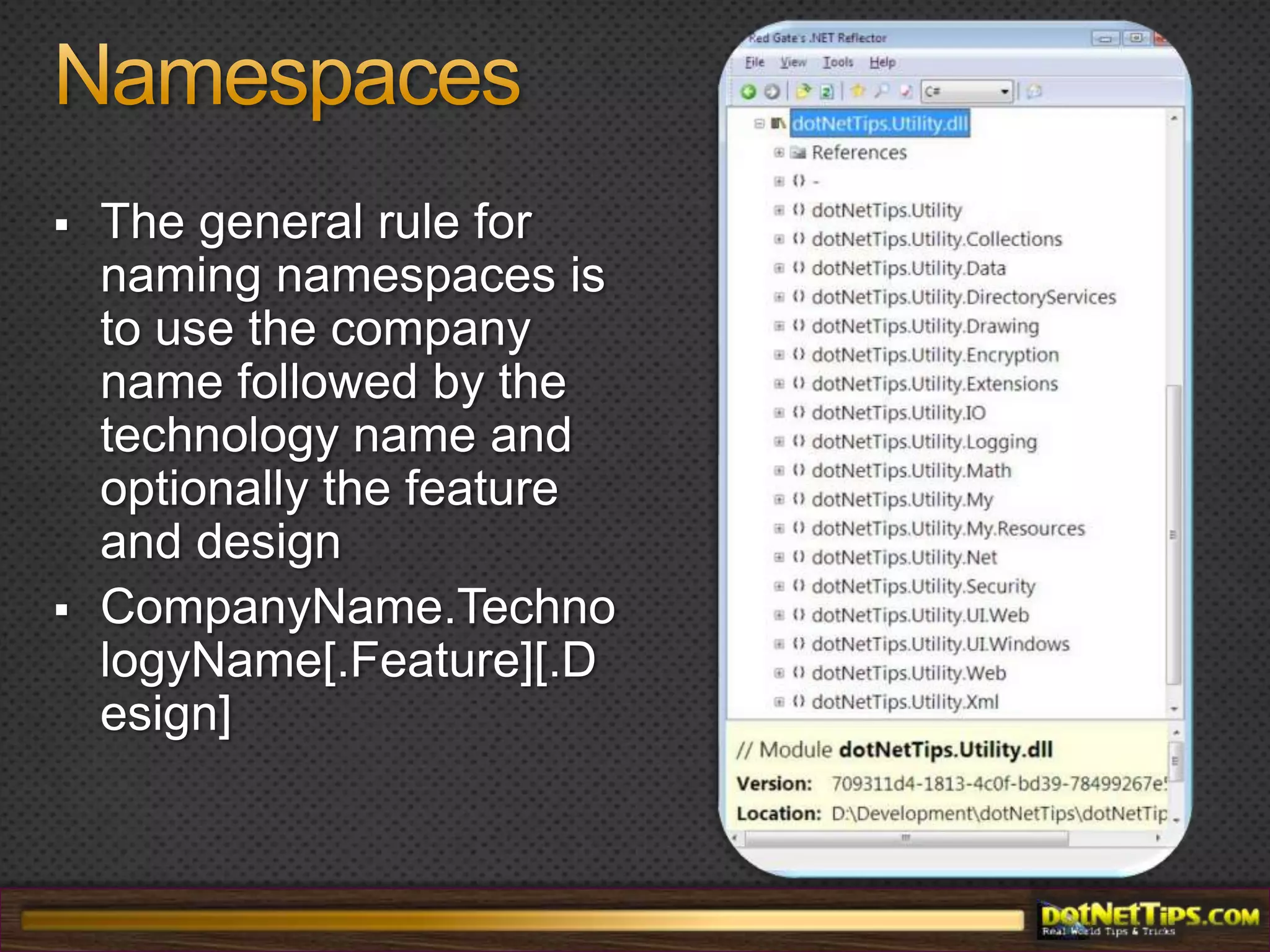
![NamespacesThe general rule for naming namespaces is to use the company name followed by the technology name and optionally the feature and designCompanyName.TechnologyName[.Feature][.Design]](https://image.slidesharecdn.com/back-2-basics-dotnetcodingstandardsfortherealworld-100628150323-phpapp02/75/Back-2-Basics-NET-Coding-Standards-For-The-Real-World-17-2048.jpg)