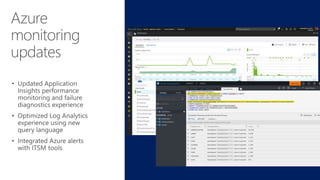
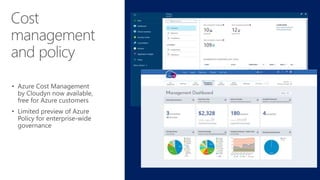
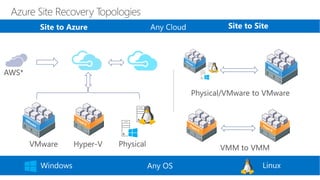
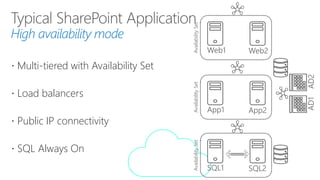
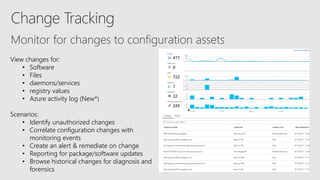
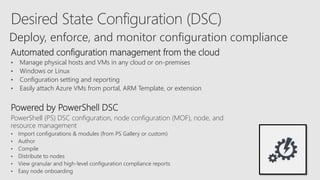
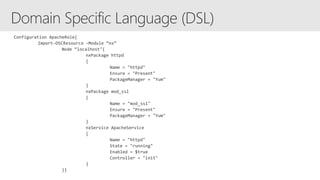
The document outlines Microsoft's Azure security features, emphasizing high availability, disaster recovery, and backup for applications and data. It discusses functionalities like Desired State Configuration (DSC), change tracking, and automated configuration management across Windows and Linux environments. Additionally, it highlights monitoring and logging capabilities for security events, detailed reporting, and analytics to enhance operational efficiency and incident response.