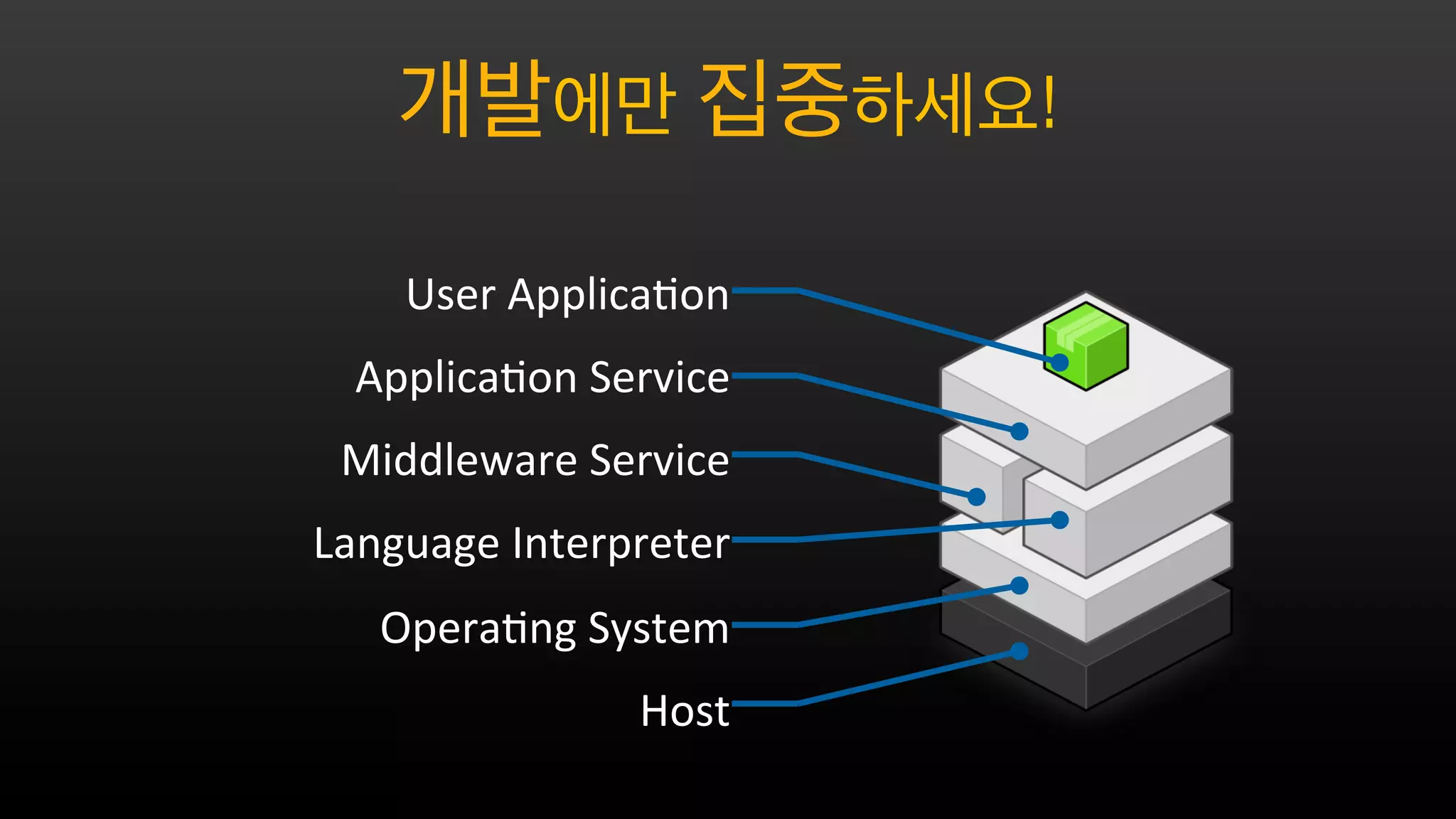
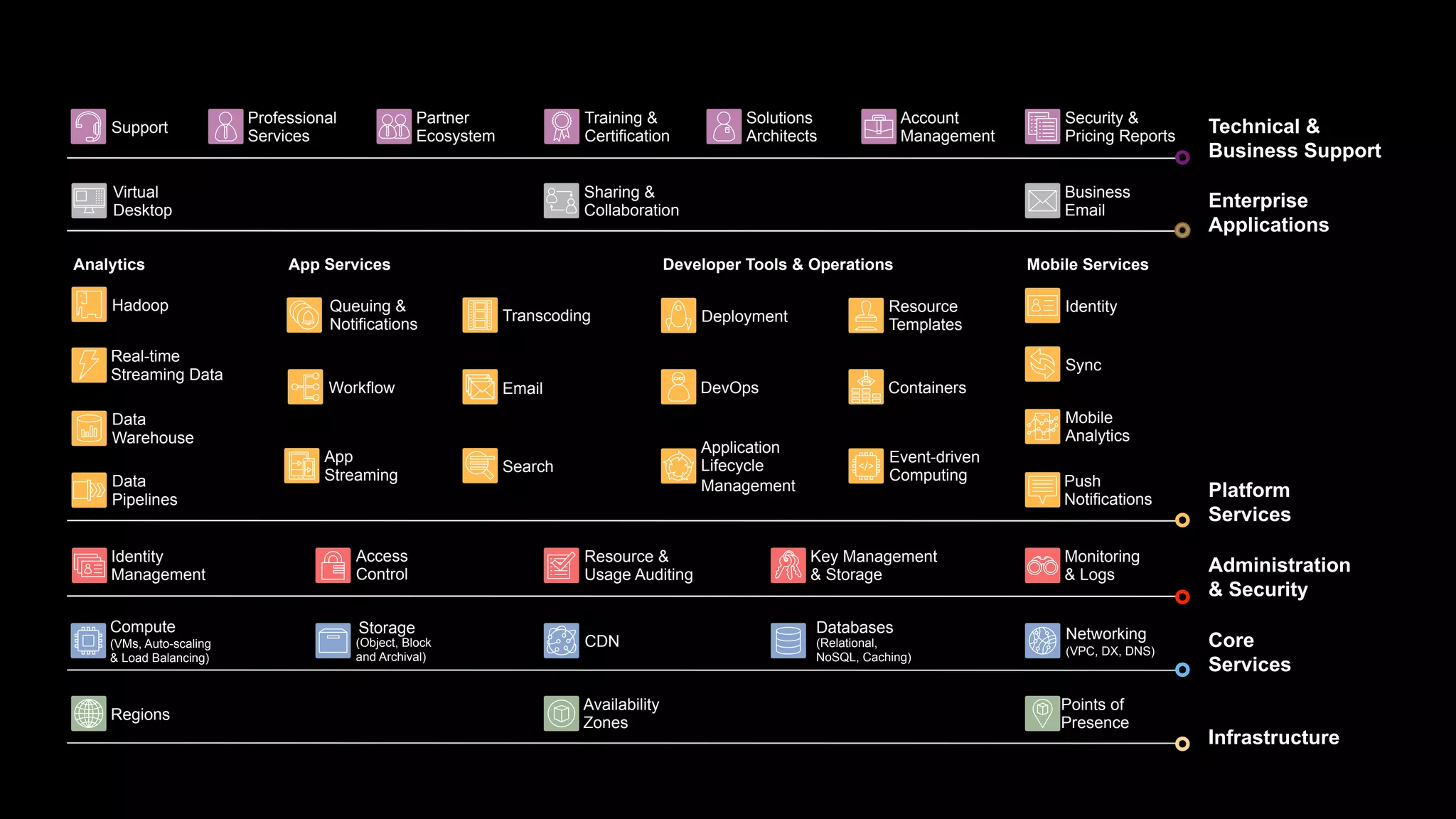
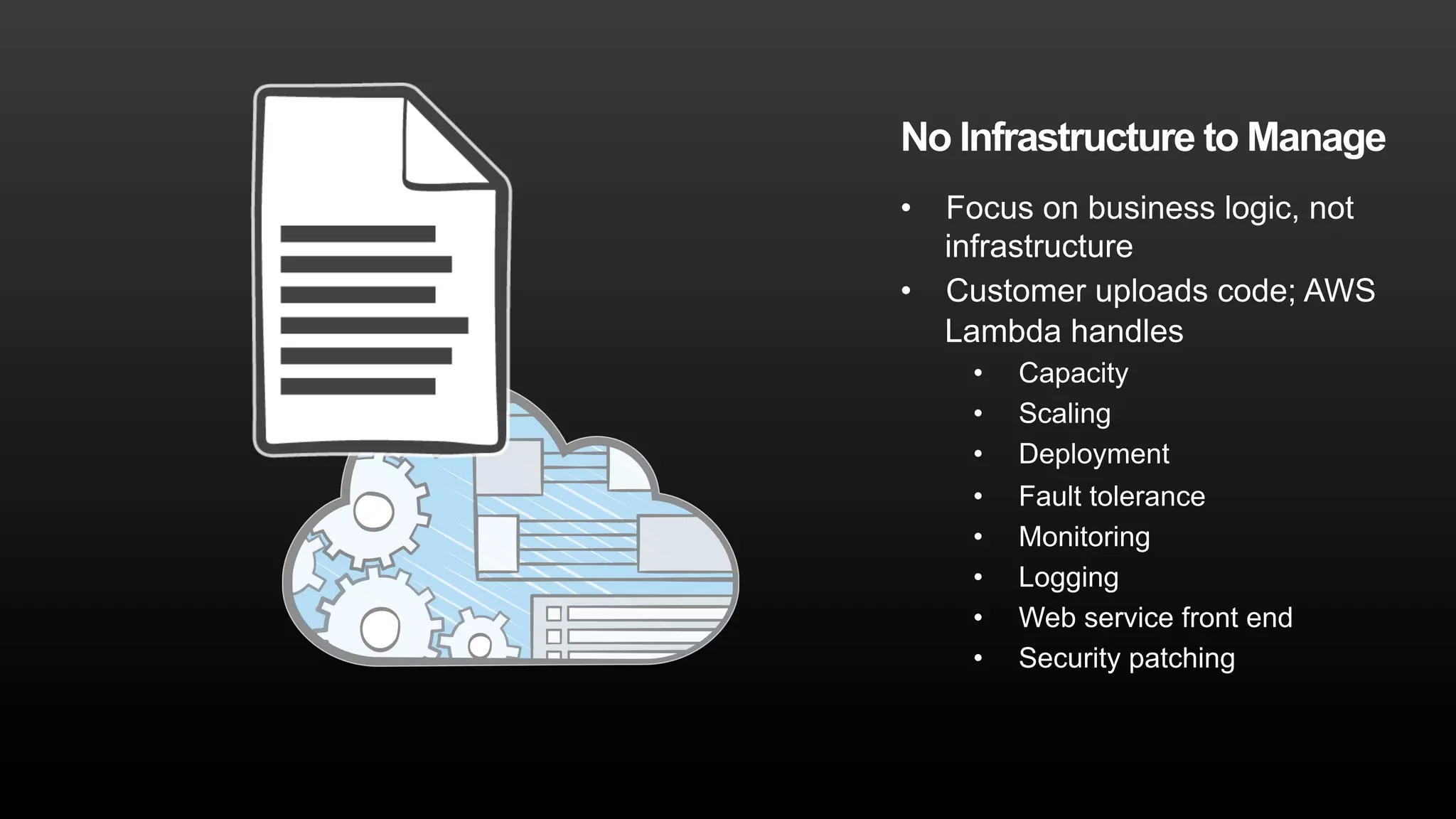
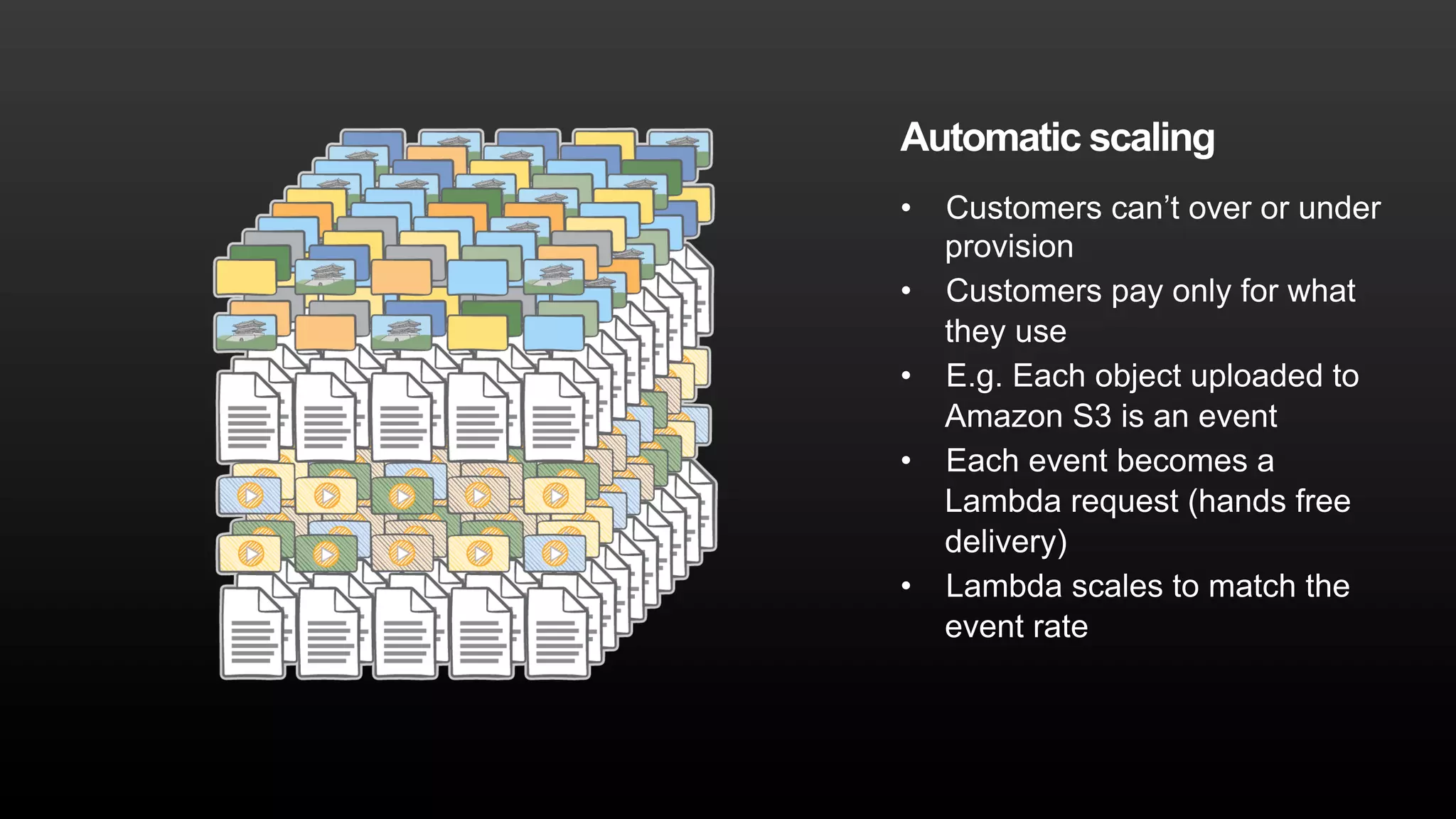
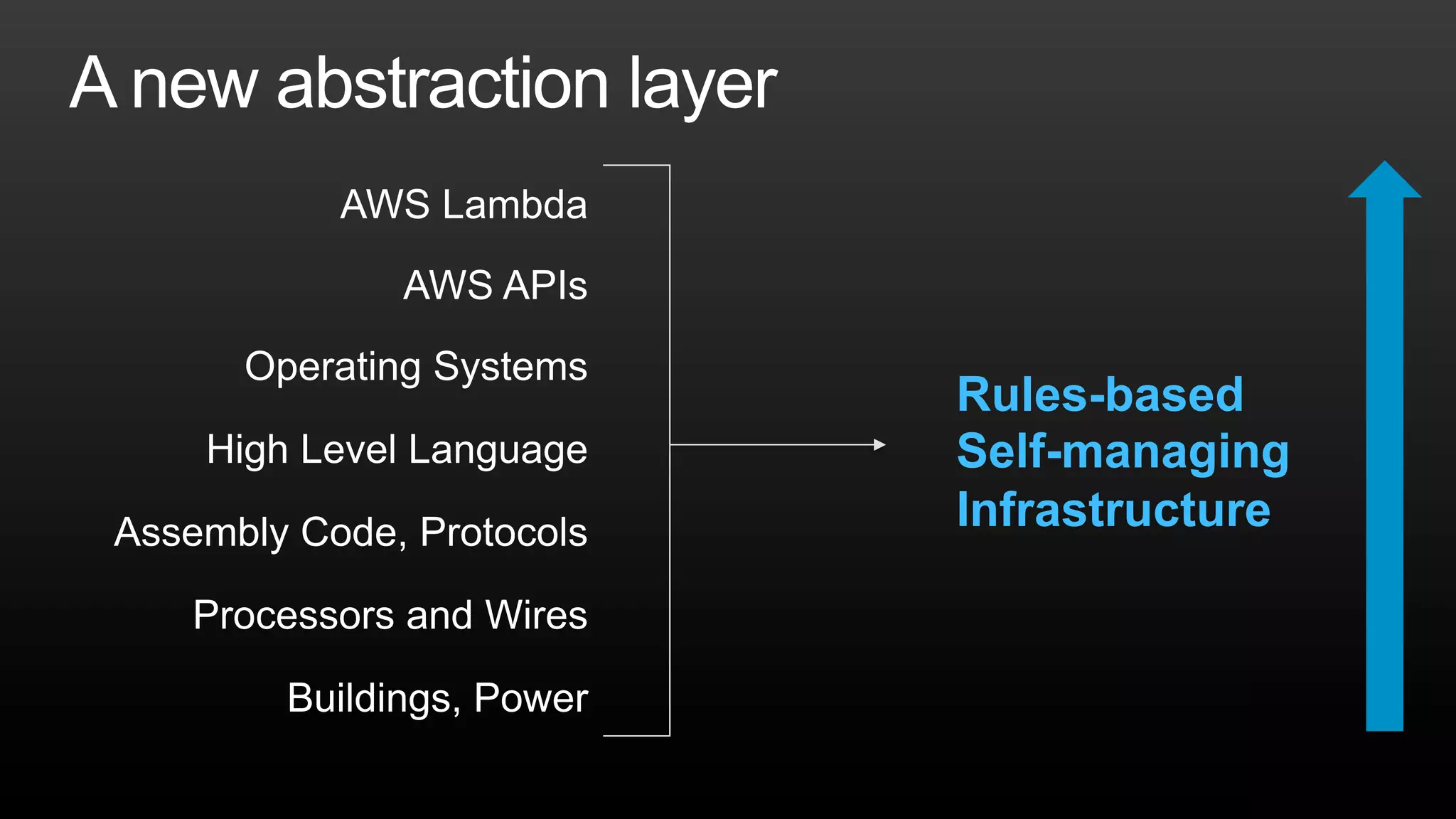
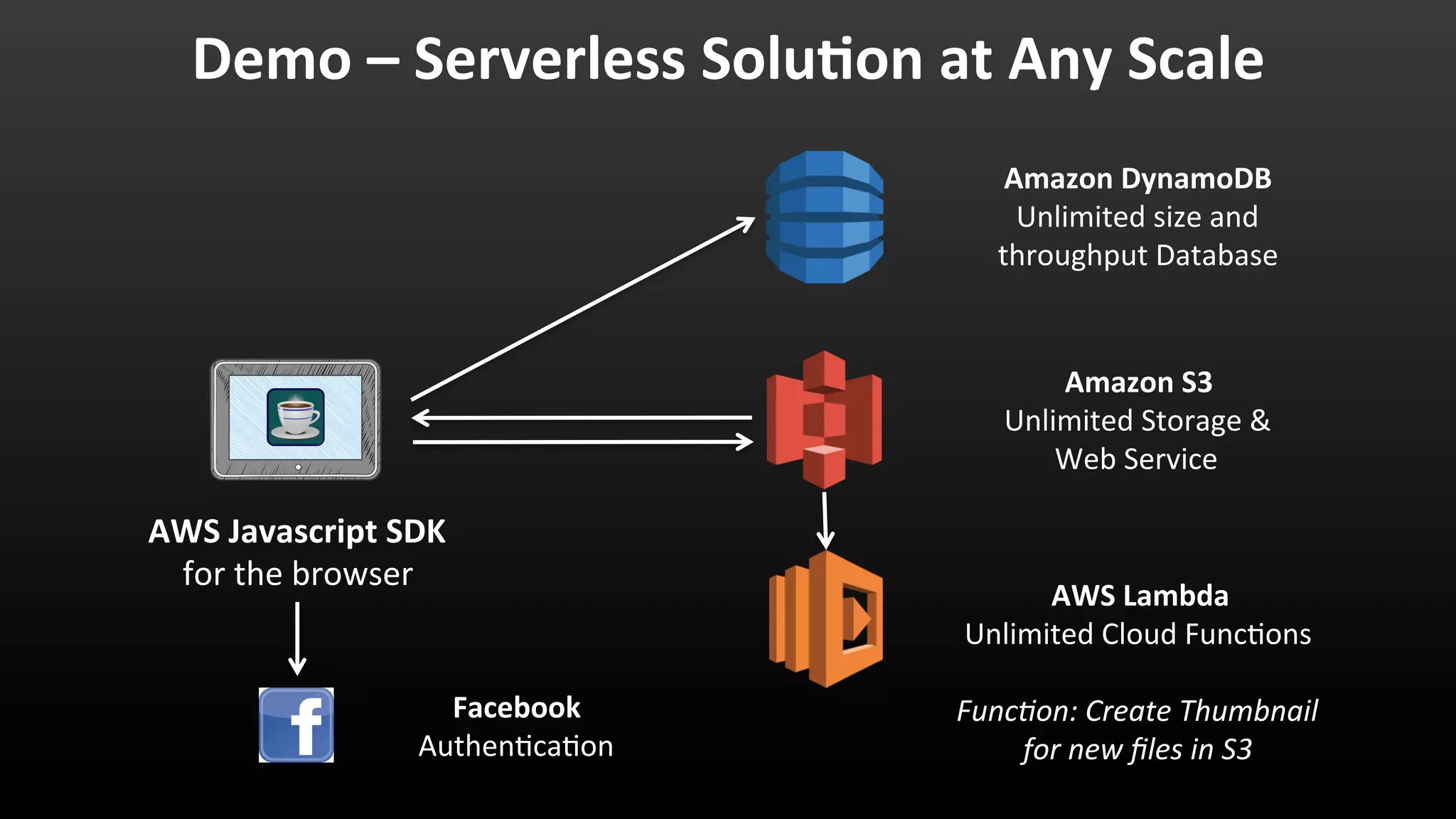
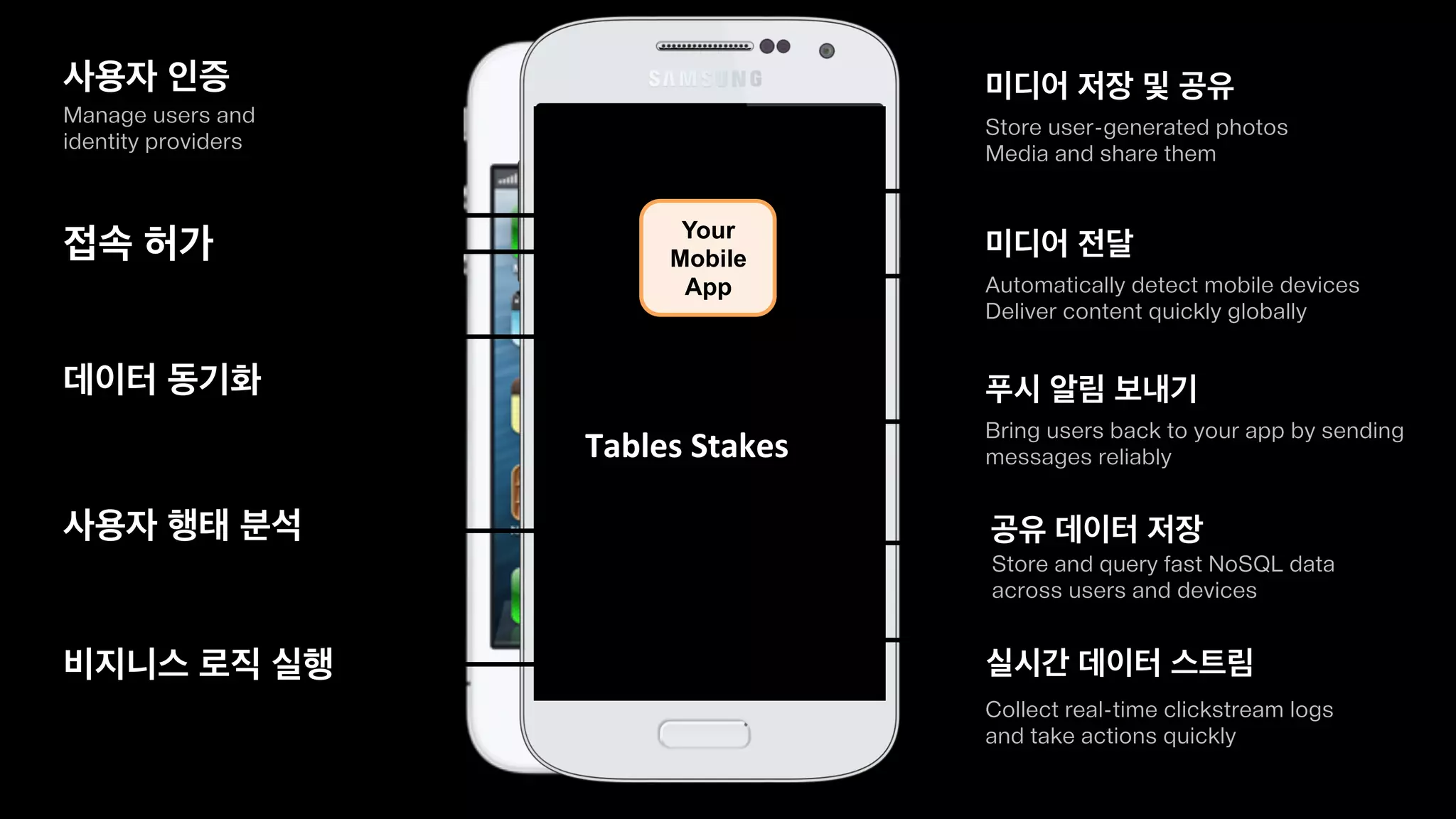
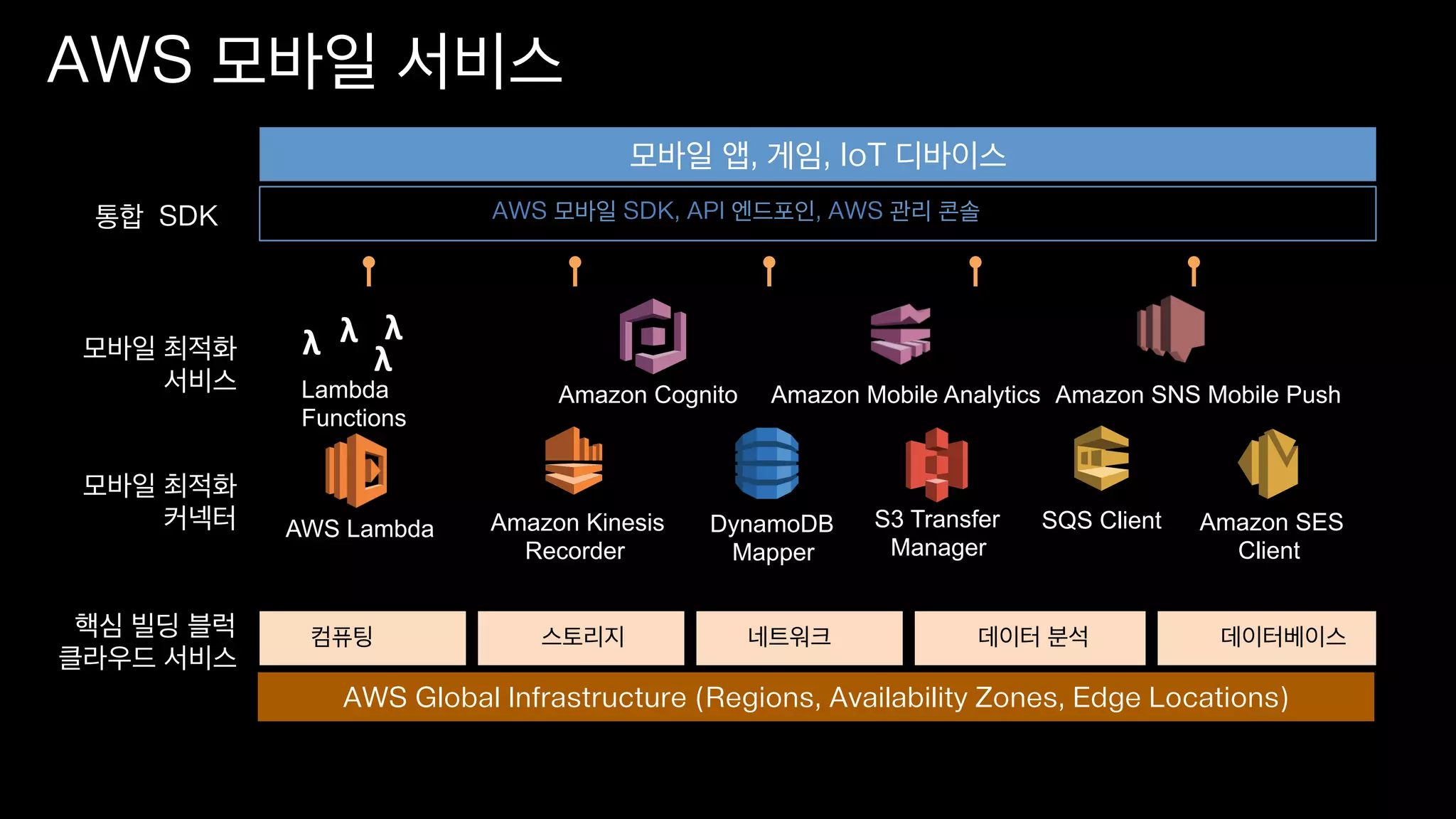
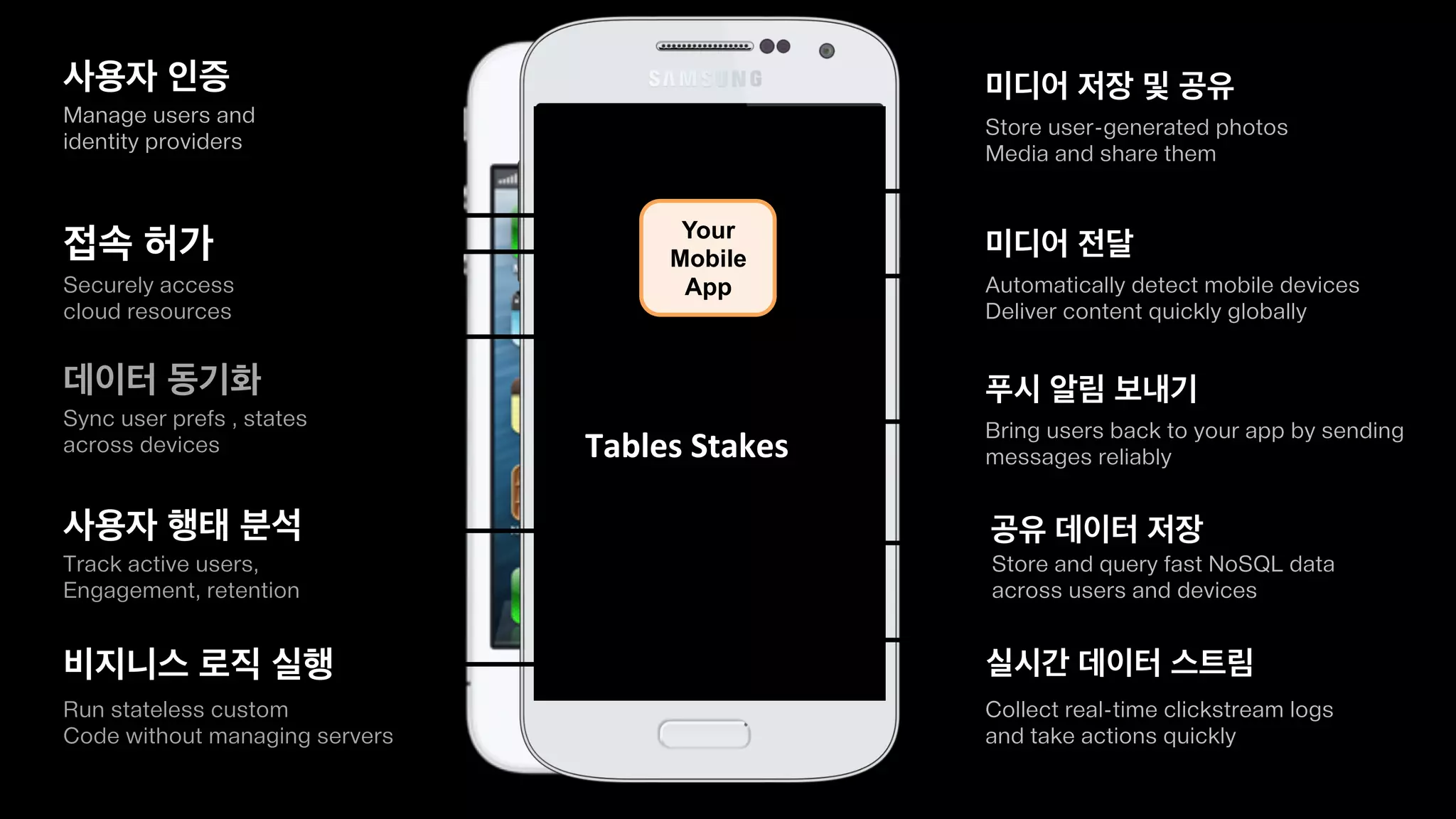
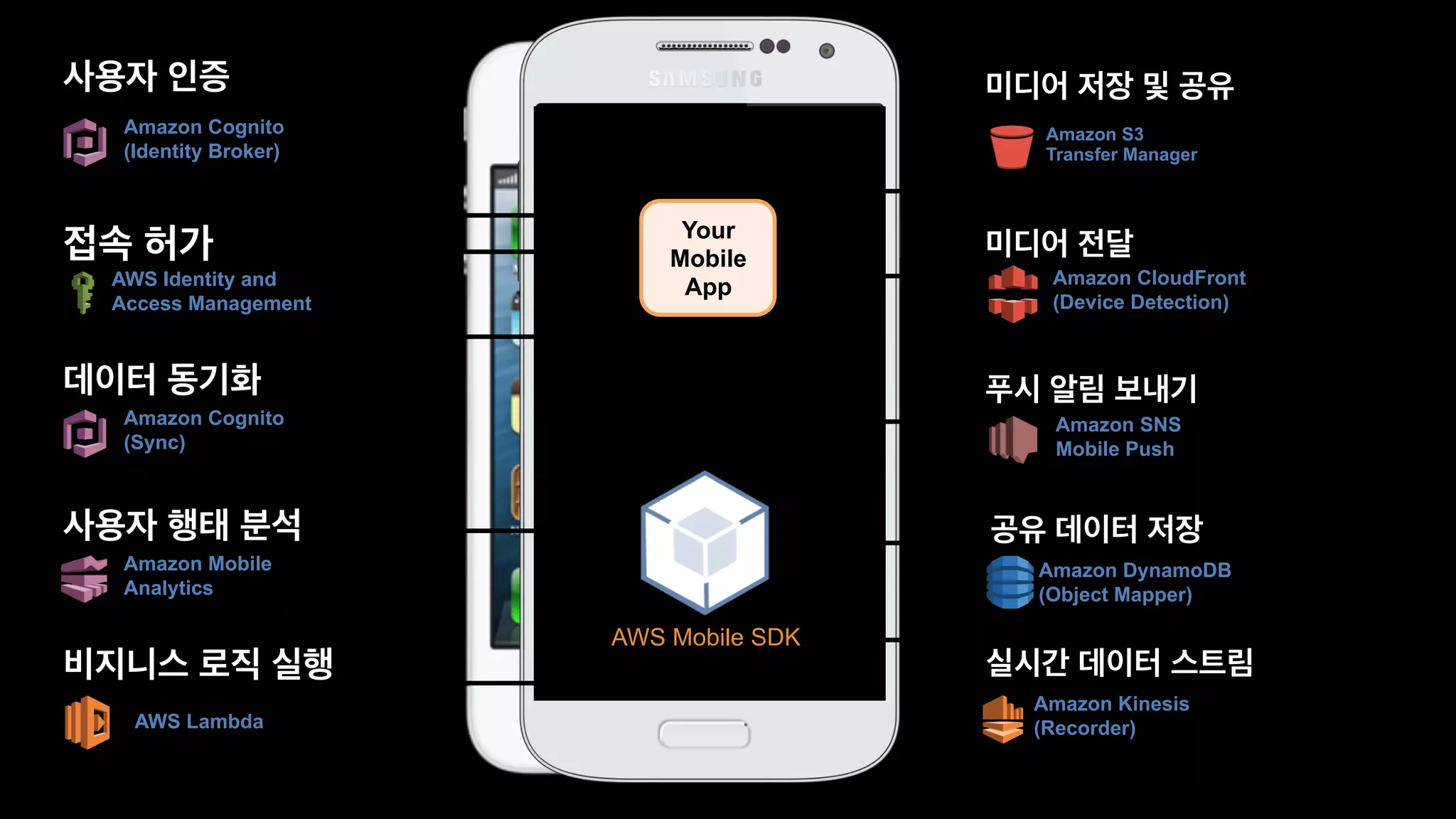
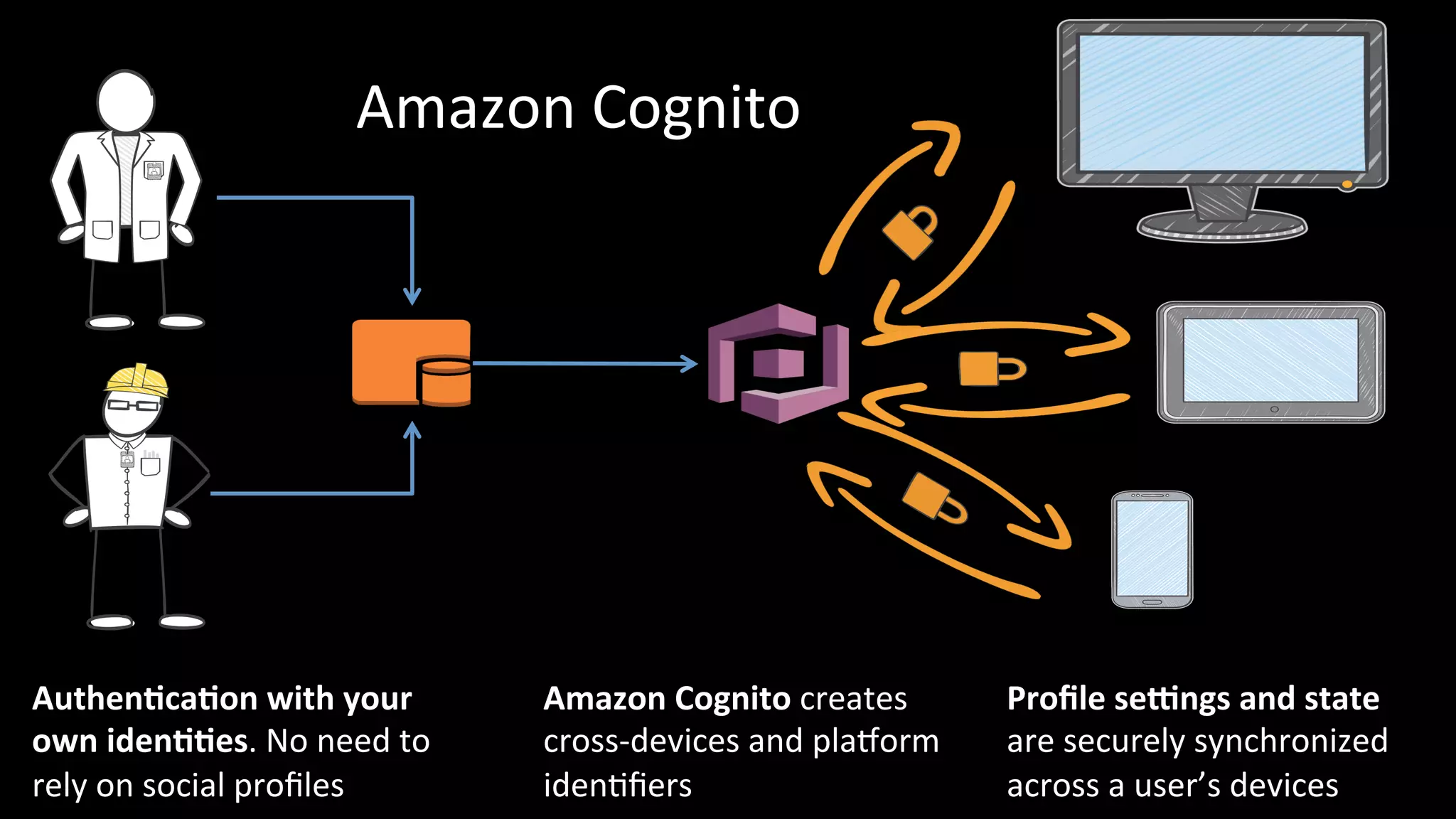
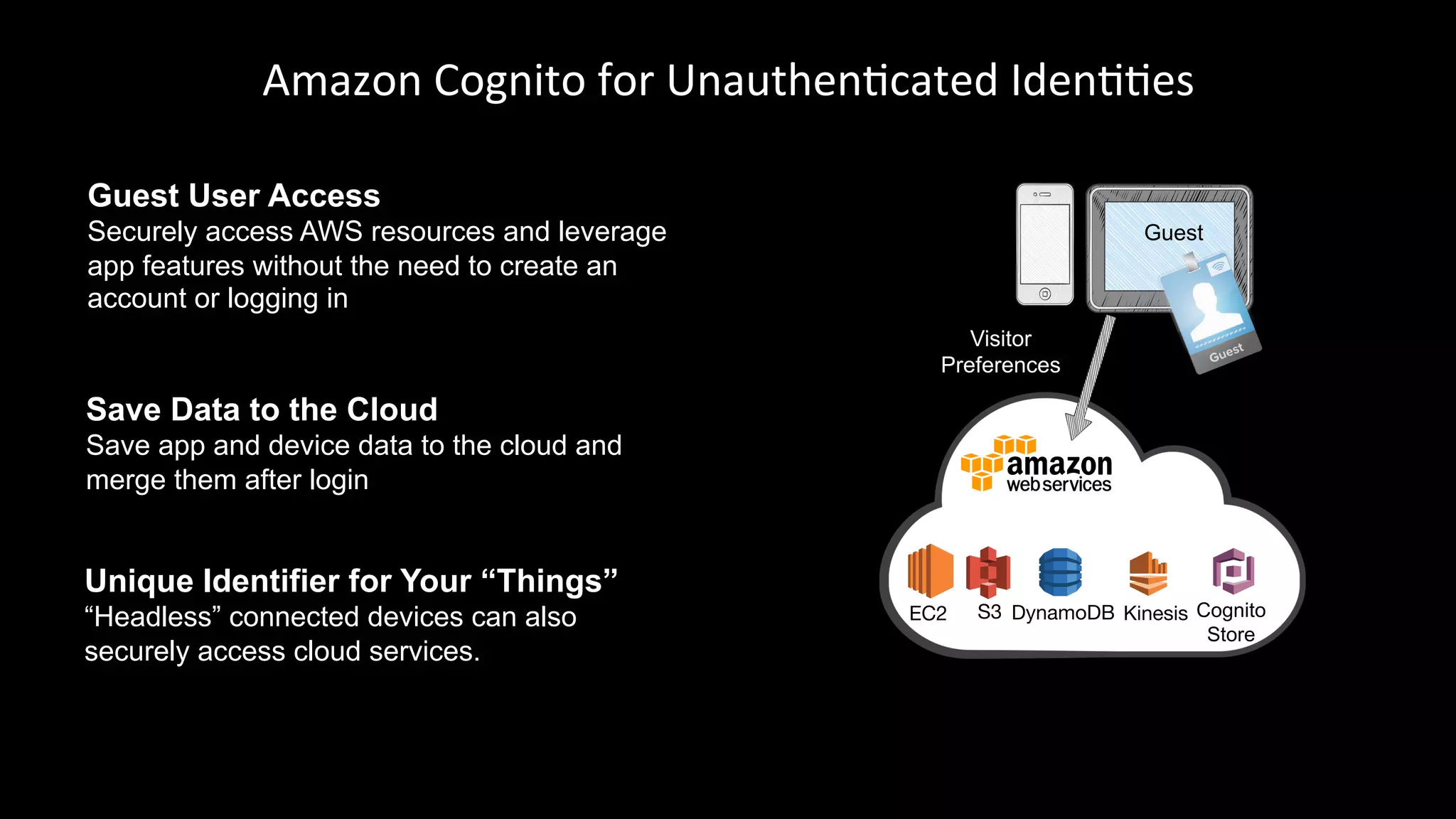
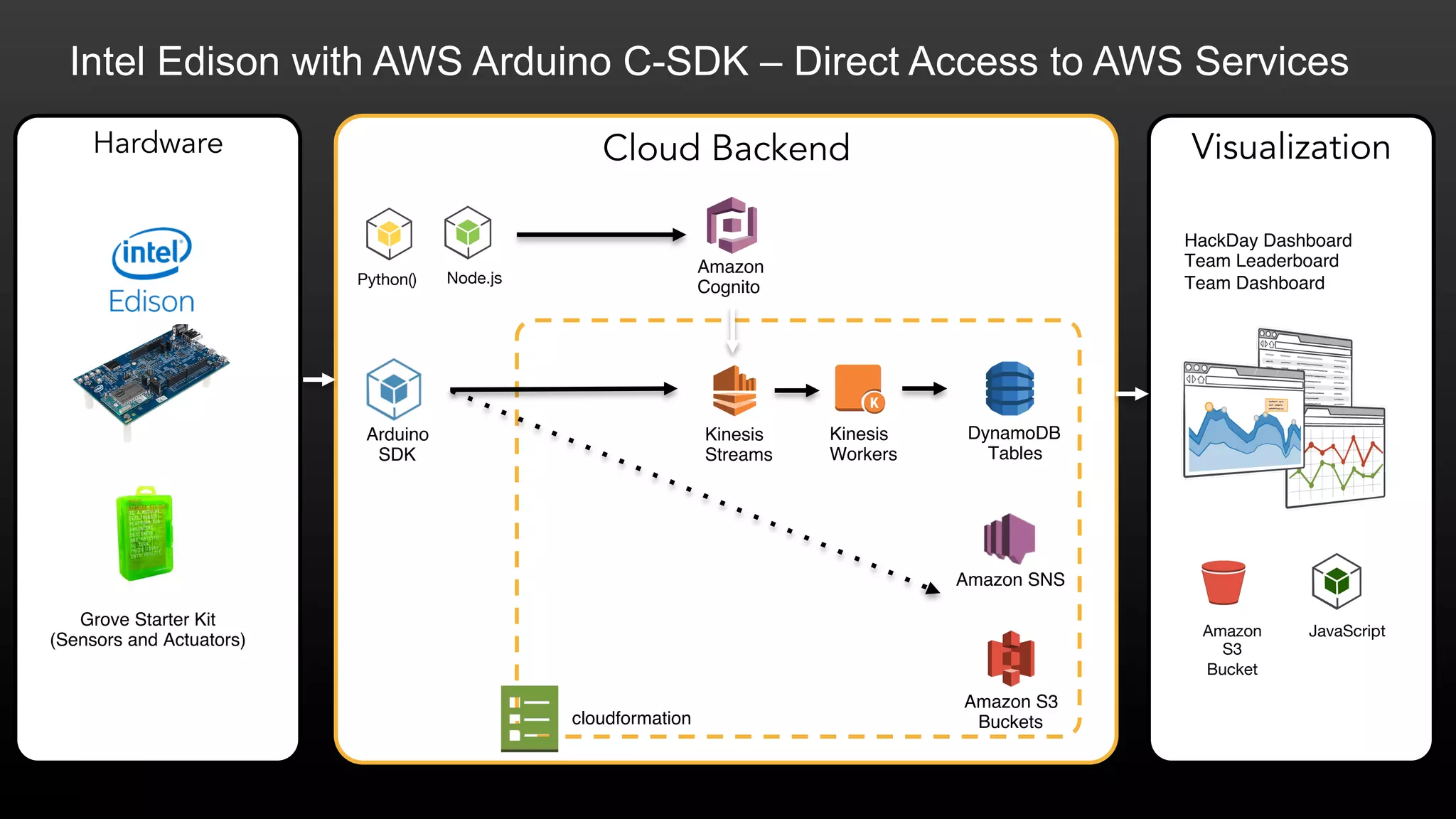
The document discusses advancements in serverless cloud computing for IoT and mobile applications, emphasizing rapid development using AWS services. It highlights various AWS tools and features, such as Lambda for event-driven compute, Cognito for user authentication, and mobile SDKs for app management. Additionally, it outlines the benefits of scalability, security, and cost efficiency offered by AWS solutions.