Here are the steps to configure wireless on Windows XP:
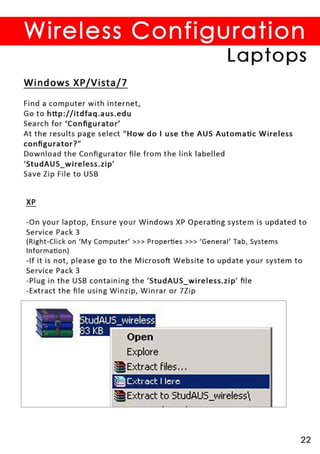
1. Insert the USB with the downloaded file into the laptop
2. Double click on the StudAUS_wireless.zip file to extract the contents
3. Double click on Setup.exe
4. Follow the on-screen instructions
5. Once installed, it will automatically detect and configure the wireless settings for AUS_Wireless
No further configuration should be needed. The laptop should now be able to connect to AUS_Wireless.
Let me know if you have any other questions!