The document provides an overview of IT audit concepts including:
- Why IT systems need to be audited due to risks of errors, inaccuracies, and deficiencies affecting financial reporting
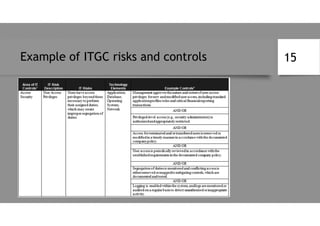
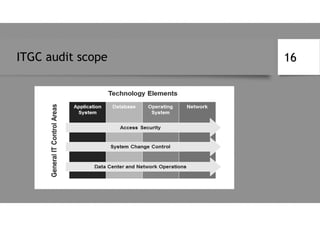
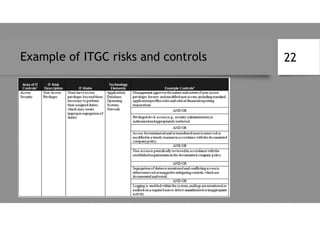
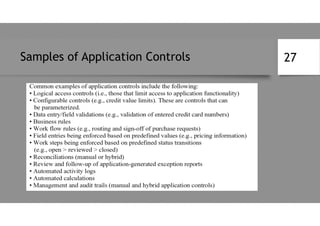
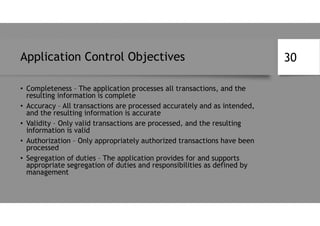
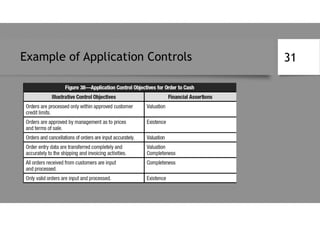
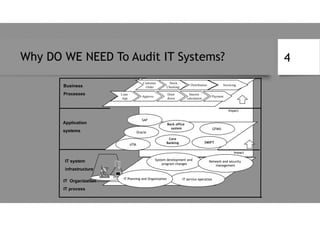
- The types of IT controls including general controls over the IT infrastructure and environment, and application controls specific to automated applications
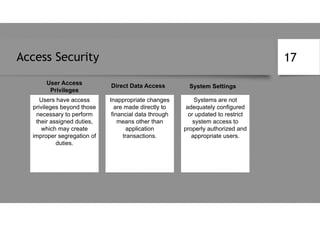
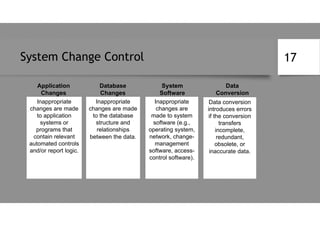
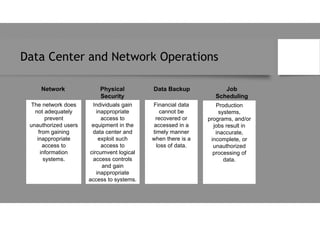
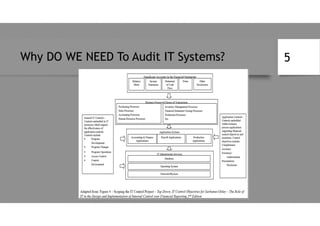
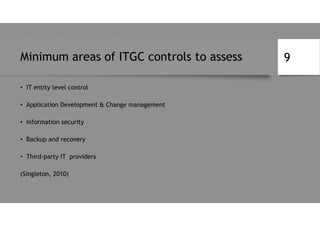
- Examples of minimum areas to assess for IT general controls including entity-level controls, access security, change management, backup/recovery and third parties
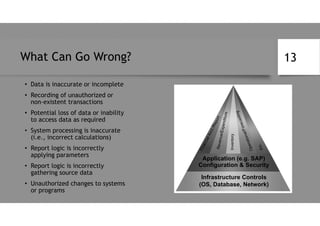
- Risks that can occur if IT general controls are deficient including inaccurate or unauthorized processing, data issues, and unauthorized access or changes
![Identify ITGC Risks 14
PCAOB
Literature
The auditor should obtain an understanding of specific risks to a company's internal
control over financial reporting resulting from IT. Examples of such risks include:
• Reliance on systems or programs that are inaccurately processing data, processing
inaccurate data, or both;
• Unauthorized access to data that might result in destruction of data or improper
changes to data, including the recording of unauthorized or nonexistent
transactions or inaccurate recording of transactions (particular risks might arise
when multiple users access a common database);
• The possibility of IT personnel gaining access privileges beyond those necessary to
perform their assigned duties, thereby breaking down segregation of duties;
• Unauthorized changes to data in master files;
• Unauthorized changes to systems or programs;
• Failure to make necessary changes to systems or programs;
• Inappropriate manual intervention; and
• Potential loss of data or inability to access data as required. [PCAOB AS 12.B4 ]](https://image.slidesharecdn.com/auditit250759-220802132051-b50f73e3/85/audit_it_250759-pdf-14-320.jpg)