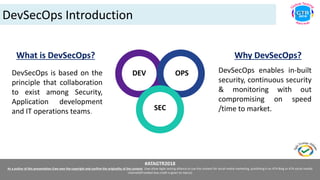
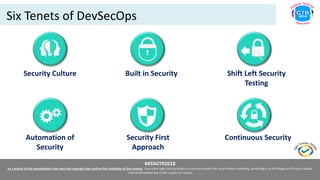
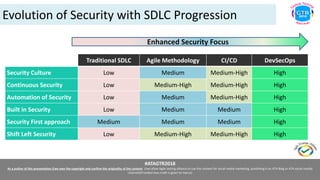
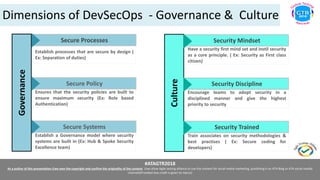
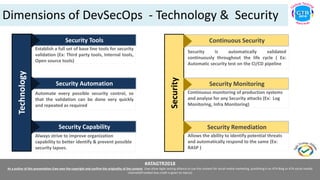
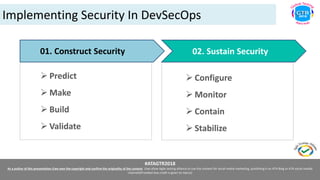
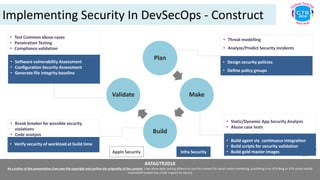
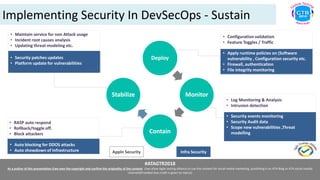
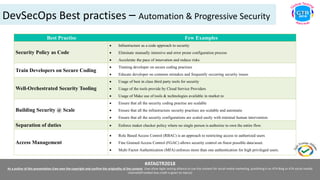
The document presents an overview of DevSecOps, emphasizing the importance of incorporating security into the development and operations processes through collaboration among teams. Key tenets include built-in security, continuous monitoring, and automation of security practices to ensure timely and efficient project delivery. It also outlines best practices for implementation, governance, culture, and technological aspects of security in a DevSecOps framework.