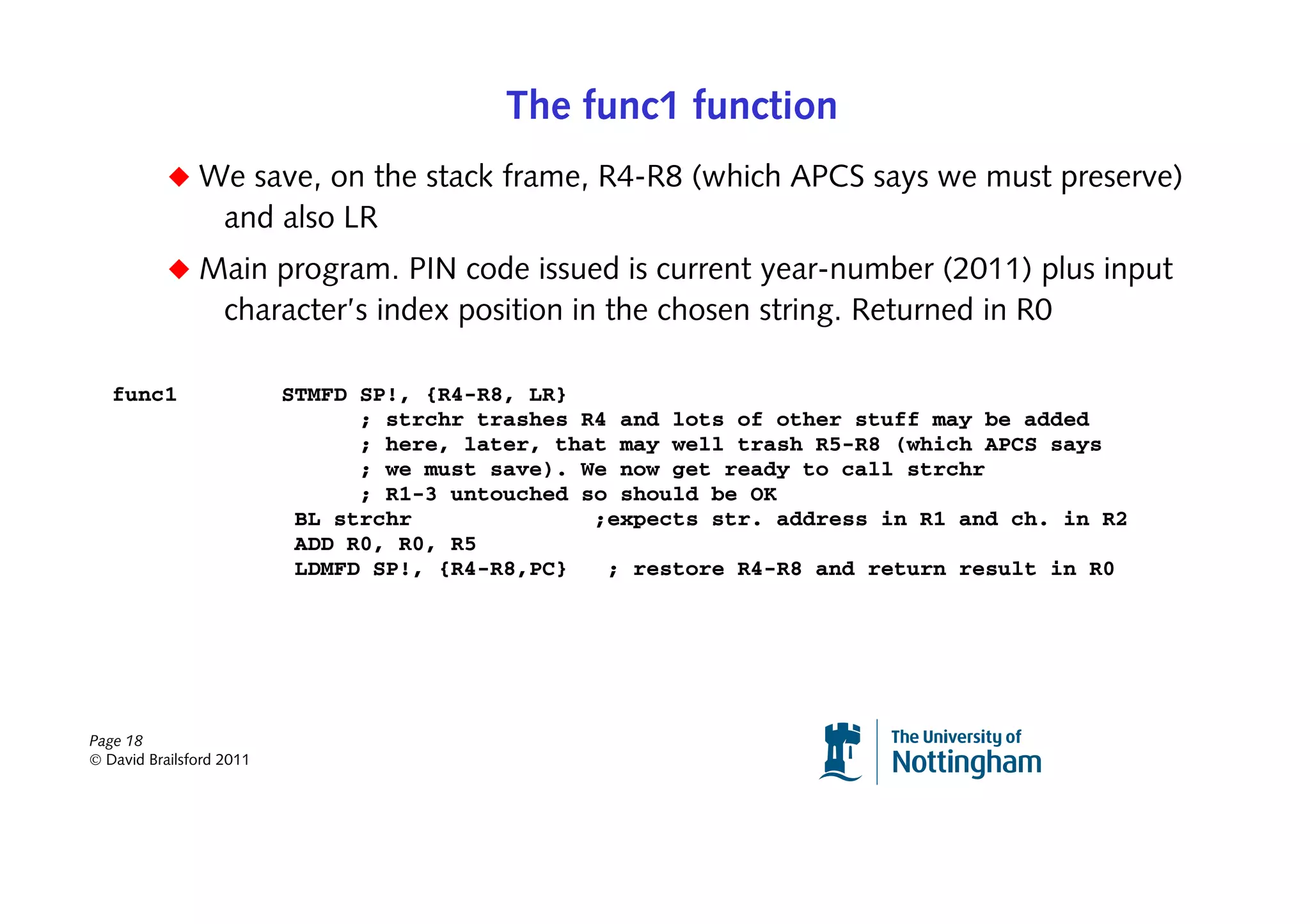
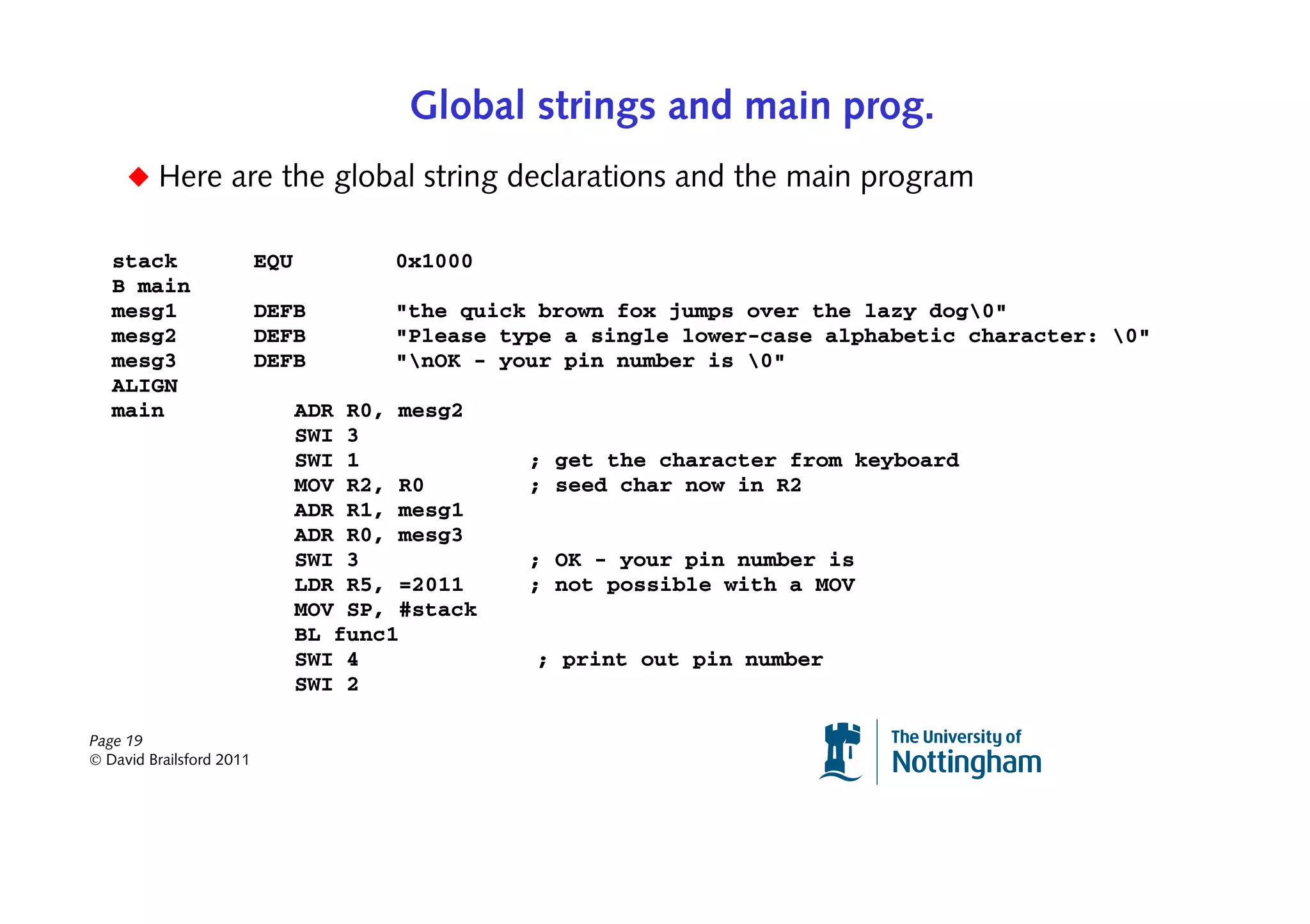
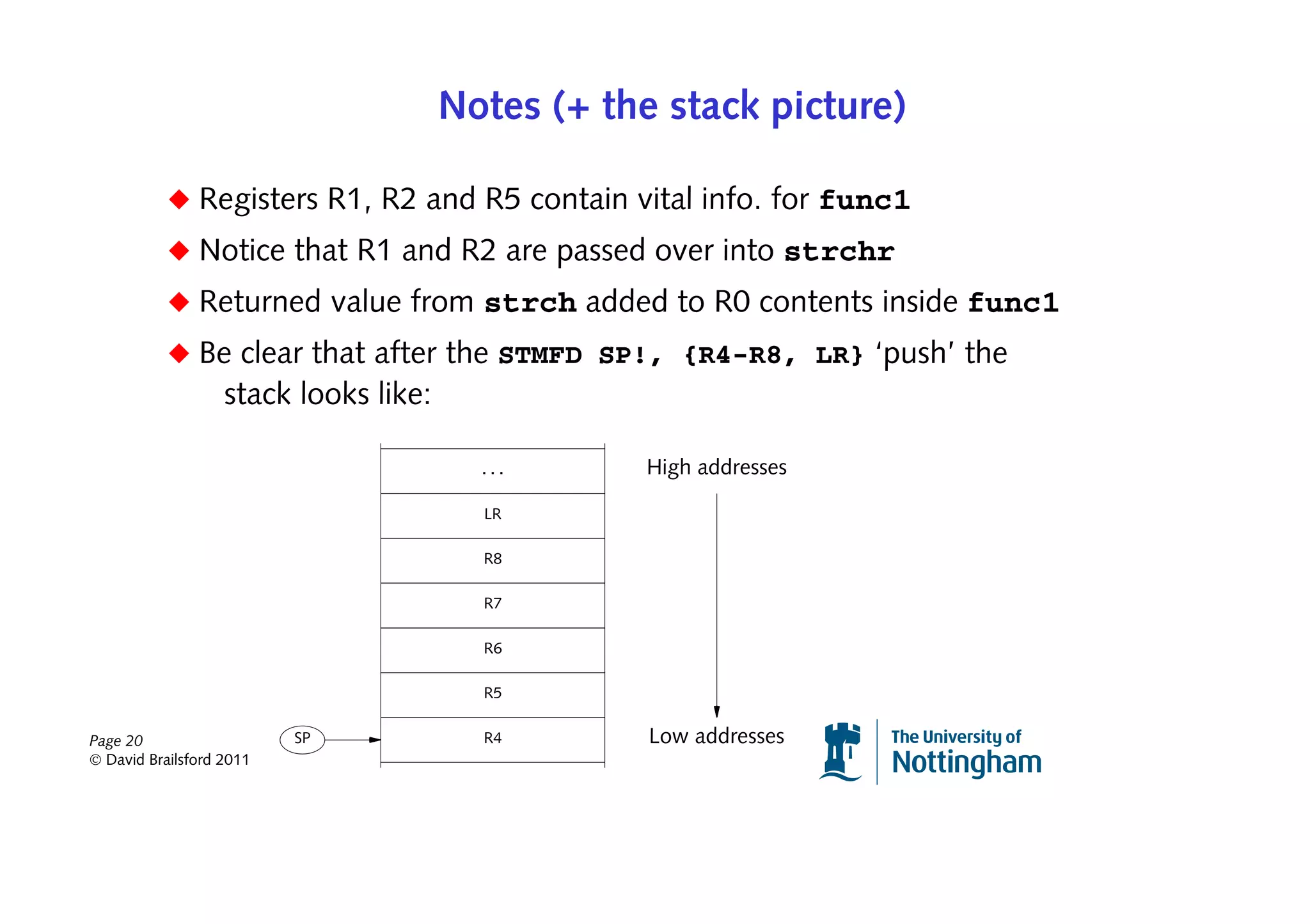
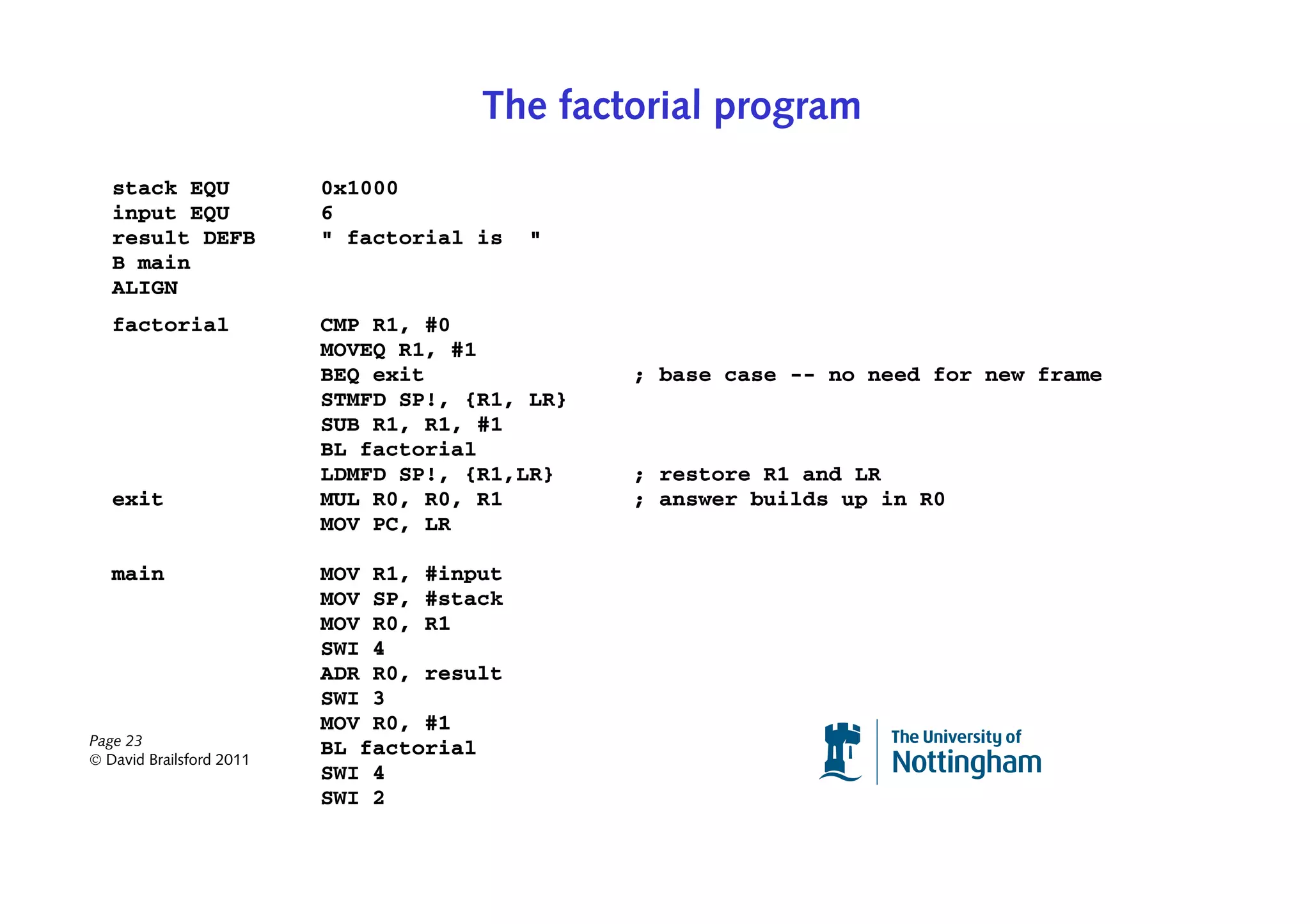
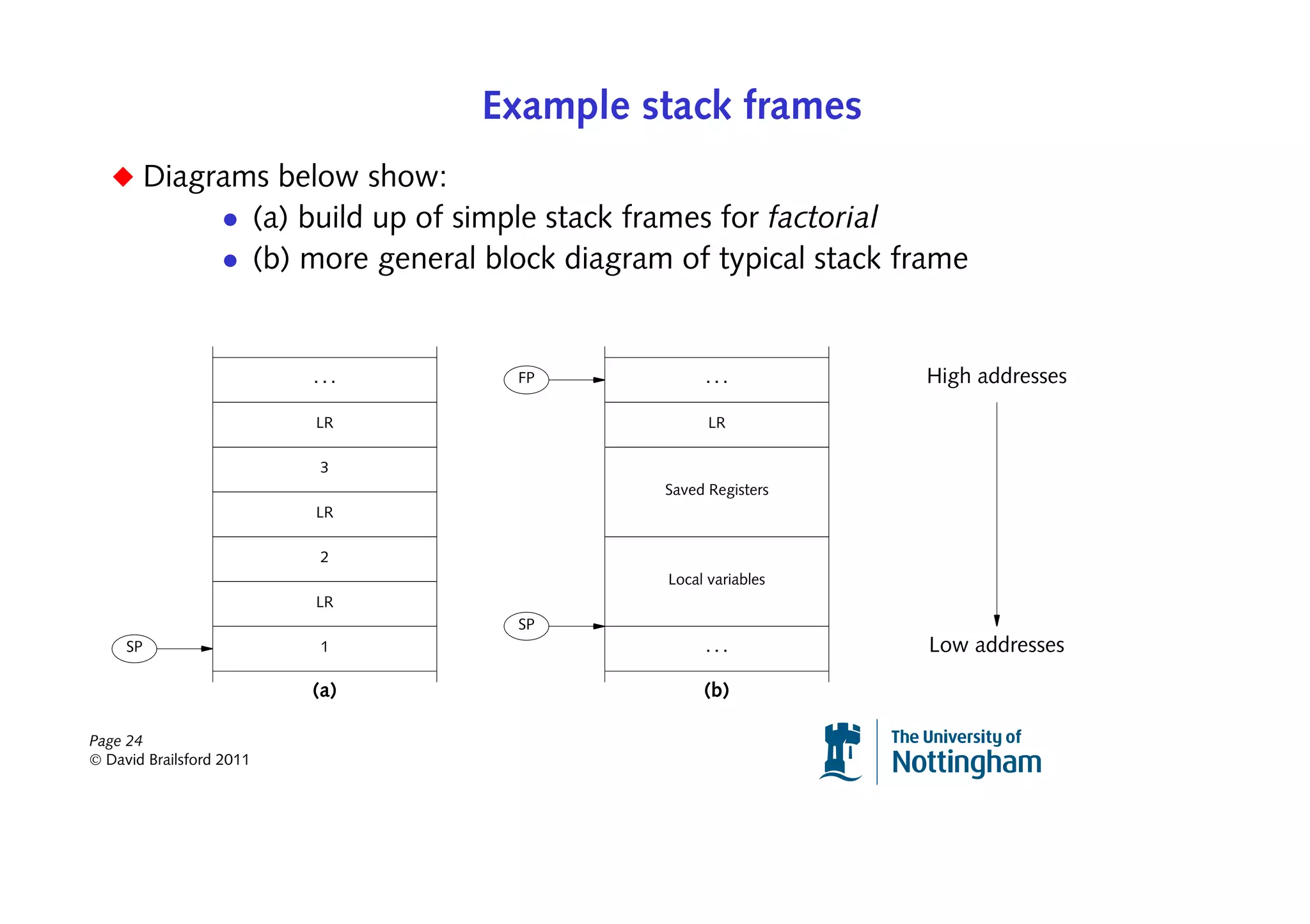
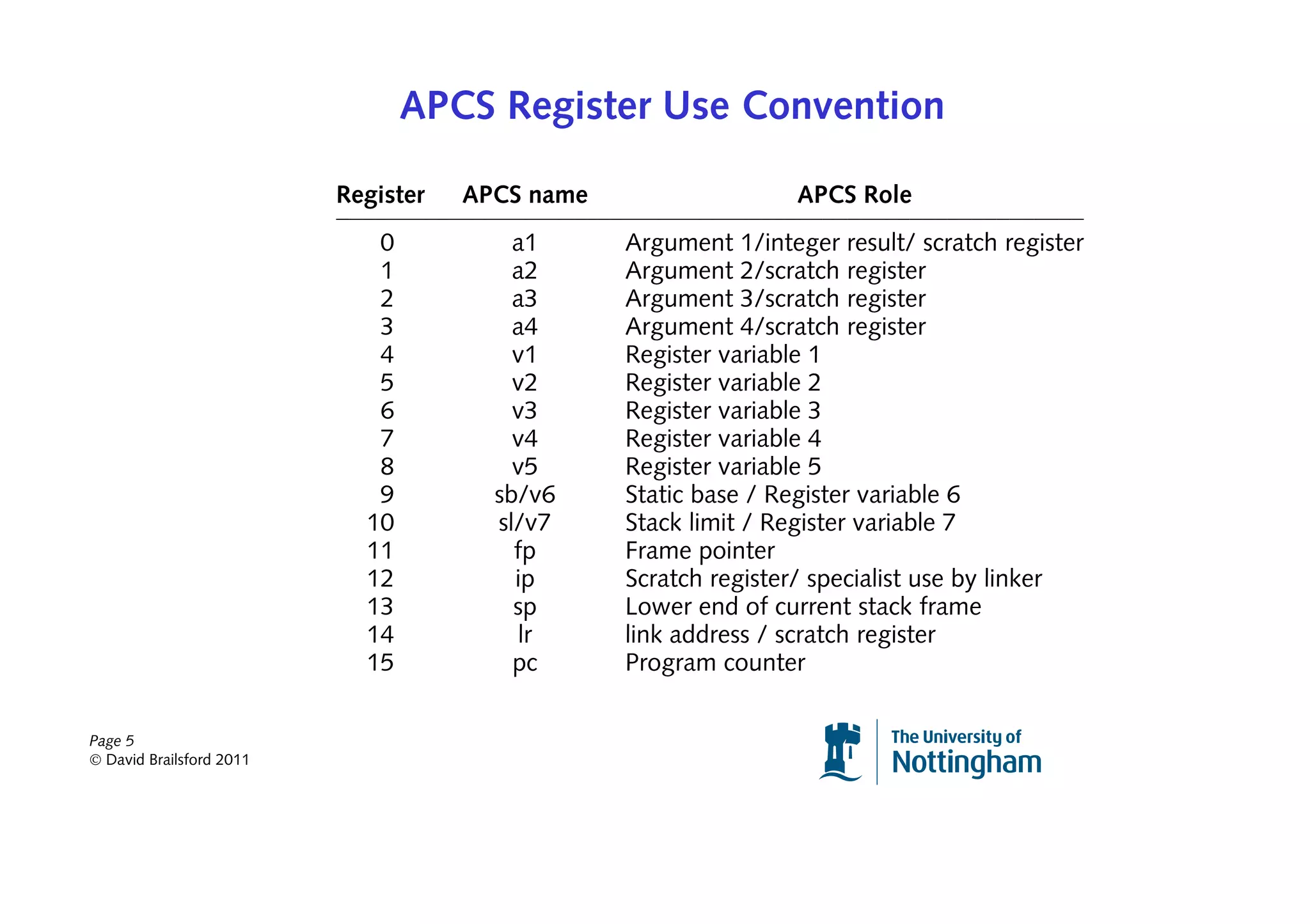
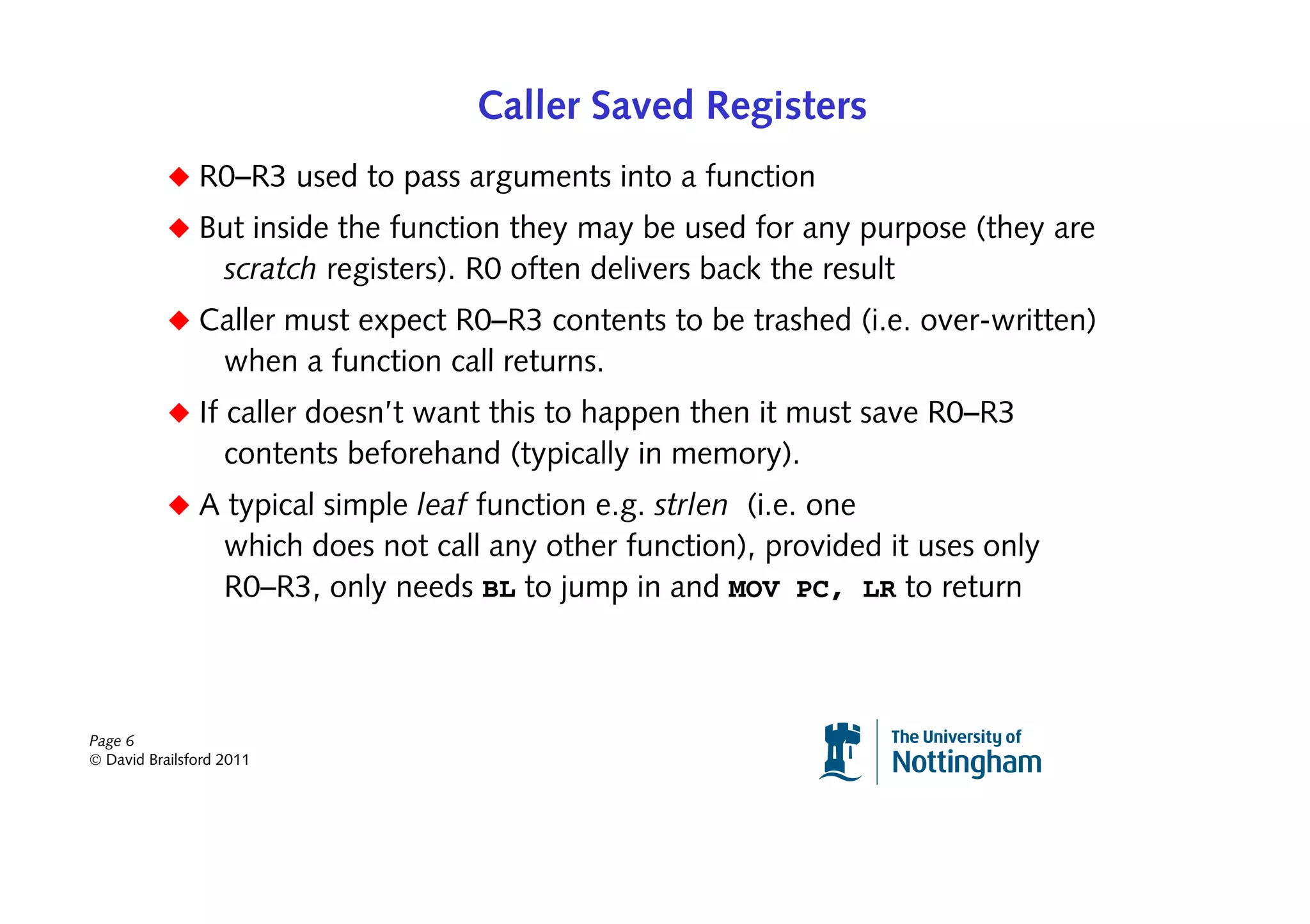
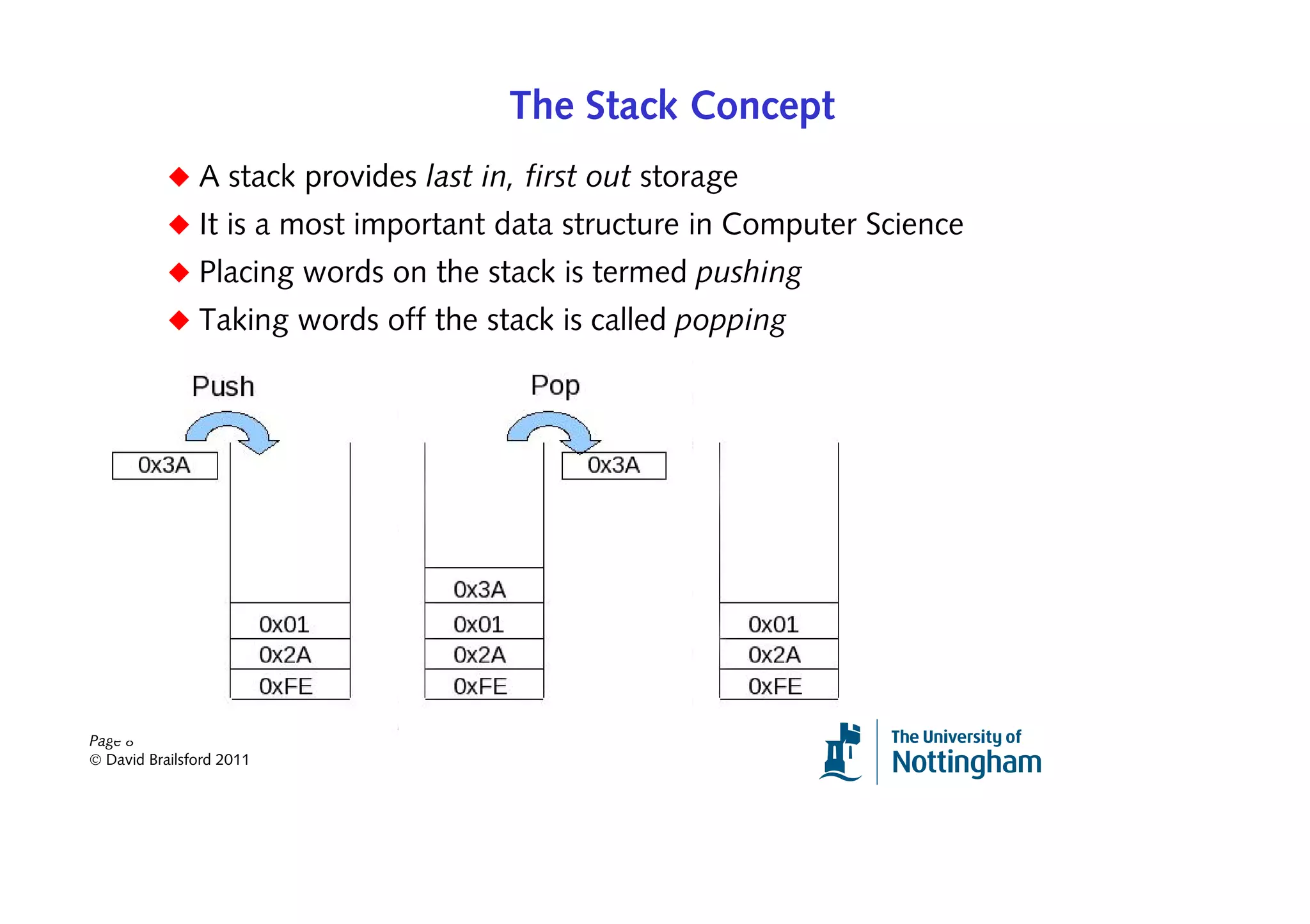
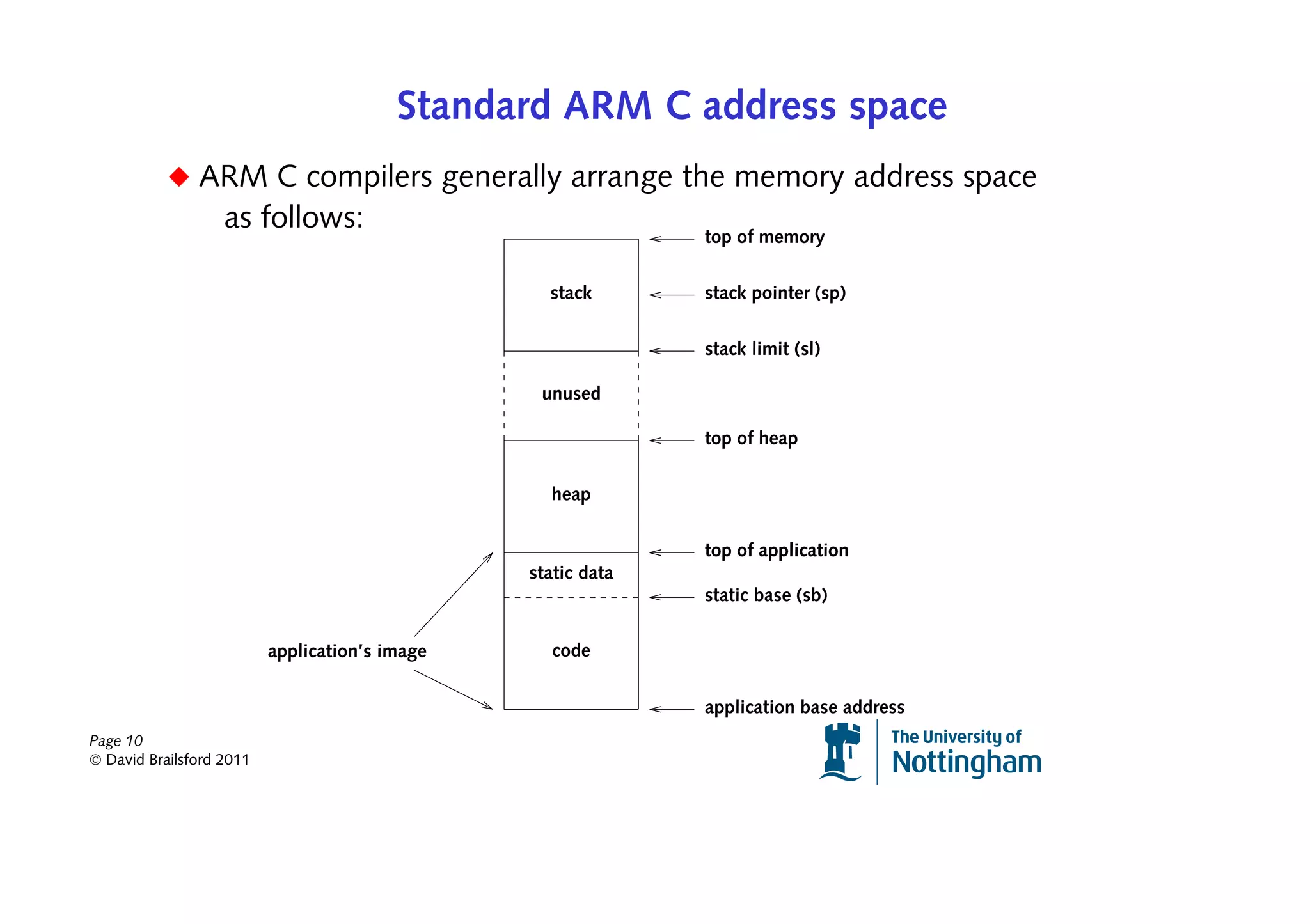
The document discusses ARM procedure calling conventions, outlining the role of procedures (or subroutines) in programming, particularly in regard to recursion and stack management. It details the ARM Procedure Call Standard (APCS), which establishes register usage, caller and callee registration responsibilities, and stack frame management, including how to efficiently manage local variables and function calls. The document also explains how to implement recursive functions, highlighting the complexity and considerations necessary for correct operation.
![Multiple Loads and Stores — Details
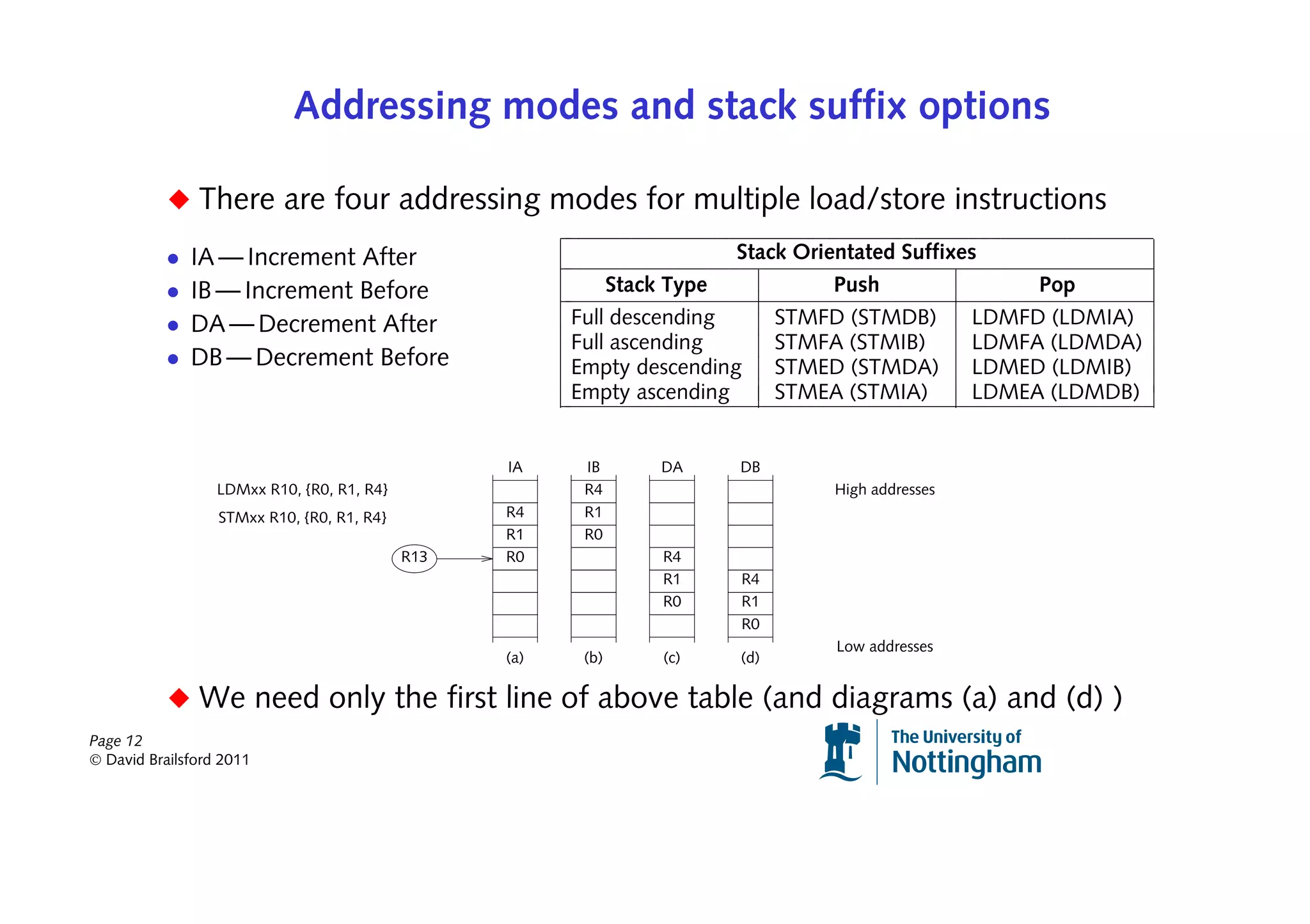
◆ In the Full Descending scheme a multiple store (STMFD) corresponds
to pushing register contents onto the stack
◆ Conversely a multiple load (LDMFD) corresponds to a pop from the stack
◆ These operations could use the mnemonics STMDB and LDMIA if preferred
◆ Let’s assume we want to retrieve data from the stack into registers
◆ Consider LDMFD SP, {R0-R3}. Here the SP holds the base address
◆ The overall effect is equivalent to:
LDR R0, [SP]
LDR R1, [SP, #4]
LDR R2, [SP, #8]
LDR R3, [SP, #12]
◆ But notice, in the above sequence, that SP itself has not been changed
◆ If we want SP to be altered (and we usually will) we write
Page 13
LDMFD SP!, {R0-R3}
© David Brailsford 2011](https://image.slidesharecdn.com/armprocedurecallingconventionsandrecursion-130111104614-phpapp02/75/ARM-procedure-calling-conventions-and-recursion-13-2048.jpg)