Report
Share
Recommended
Designing Countermeasures For Tomorrows Threats : Documentation

Abstract:
Internet and network security is the most important and top priority issues for almost all types of organizations, for instance, military divisions, ministries, banks, other public and private sectors, and even to everyone who concerns it.
These organizations may use security mechanisms to protect their assets safe against evil and attackers, but most of the security countermeasures that they use are based on known attacks, threats and vulnerabilities. They hardly pay attention to protect their assets against unknown and new types of attacks, threats and vulnerabilities. Most of the organizations faced to challenges the new types of unknown attacks and threats.
This research paper's main aim is to focus and study approaches and solutions against the unknown attacks and threats, and therefore, titled Designing Countermeasures for Tomorrows Threats to make the organizations enable to detect new types attacks, threats or vulnerabilities before they damage their assets or systems.
In addition, the outcome of this research paper will give the chance to the organizations to learn who is attacking their systems, how they are being attacked, and what the attackers are trying to achieve. The concepts that this research paper (thesis) used for Designing Countermeasures for Tomorrows Threats are Honeypot and Honeynet systems.
Honeypot and Honeynet Systems are one of the most interesting and well-known concepts for all the security professionals to know their enemies and identify their weakness. Worth mentioning that most of the countries i.e. Iran, Pakistan, India, Saudi Arabia, Germany and Polish are using these concepts to protect their internal networks and assets against the attackers. Besides, there are a great number of security organizations and communities that use these concepts for research to learn and educate public about new types of attacks, threats and vulnerabilities naming Honeynet Project, Norse, FireEye, WorldMap and Global Botnet Threat Activity.
This thesis implemented most of the existed-based technologies on the concept of Honeypot and Honeynet systems both open source and close source. Finally suggest and recommend the best solution for Afghanistan to protect its internal networks especially important organizations like Ministry of Interior and other ministries and sectors.
Am barcelona

Este documento presenta una lista de lugares y atracciones turísticas en Barcelona, España. Incluye lugares emblemáticos como la Sagrada Familia, el Parque Güell y varias casas diseñadas por arquitectos modernistas como Gaudí, Puig i Cadafalch y Domenech i Montaner. También menciona playas, parques, plazas y calles principales de la ciudad, así como vistas panorámicas desde el Tibidabo y Montjuïc.
44CON @ IPexpo - You're fighting an APT with what exactly?

The document discusses strategies for defending against advanced persistent threats (APTs). It notes that many organizations are still relying on network configurations and security tools conceived decades ago. Modern APTs have evolved tactics to avoid detection, like using internal peer-to-peer communications and fast-flux domain naming that evade perimeter-based security tools. The document advocates deploying detection capabilities throughout the network rather than just at the boundary, and maintaining coordinated incident response plans and skills to understand adversaries' techniques.
Recommended
Designing Countermeasures For Tomorrows Threats : Documentation

Abstract:
Internet and network security is the most important and top priority issues for almost all types of organizations, for instance, military divisions, ministries, banks, other public and private sectors, and even to everyone who concerns it.
These organizations may use security mechanisms to protect their assets safe against evil and attackers, but most of the security countermeasures that they use are based on known attacks, threats and vulnerabilities. They hardly pay attention to protect their assets against unknown and new types of attacks, threats and vulnerabilities. Most of the organizations faced to challenges the new types of unknown attacks and threats.
This research paper's main aim is to focus and study approaches and solutions against the unknown attacks and threats, and therefore, titled Designing Countermeasures for Tomorrows Threats to make the organizations enable to detect new types attacks, threats or vulnerabilities before they damage their assets or systems.
In addition, the outcome of this research paper will give the chance to the organizations to learn who is attacking their systems, how they are being attacked, and what the attackers are trying to achieve. The concepts that this research paper (thesis) used for Designing Countermeasures for Tomorrows Threats are Honeypot and Honeynet systems.
Honeypot and Honeynet Systems are one of the most interesting and well-known concepts for all the security professionals to know their enemies and identify their weakness. Worth mentioning that most of the countries i.e. Iran, Pakistan, India, Saudi Arabia, Germany and Polish are using these concepts to protect their internal networks and assets against the attackers. Besides, there are a great number of security organizations and communities that use these concepts for research to learn and educate public about new types of attacks, threats and vulnerabilities naming Honeynet Project, Norse, FireEye, WorldMap and Global Botnet Threat Activity.
This thesis implemented most of the existed-based technologies on the concept of Honeypot and Honeynet systems both open source and close source. Finally suggest and recommend the best solution for Afghanistan to protect its internal networks especially important organizations like Ministry of Interior and other ministries and sectors.
Am barcelona

Este documento presenta una lista de lugares y atracciones turísticas en Barcelona, España. Incluye lugares emblemáticos como la Sagrada Familia, el Parque Güell y varias casas diseñadas por arquitectos modernistas como Gaudí, Puig i Cadafalch y Domenech i Montaner. También menciona playas, parques, plazas y calles principales de la ciudad, así como vistas panorámicas desde el Tibidabo y Montjuïc.
44CON @ IPexpo - You're fighting an APT with what exactly?

The document discusses strategies for defending against advanced persistent threats (APTs). It notes that many organizations are still relying on network configurations and security tools conceived decades ago. Modern APTs have evolved tactics to avoid detection, like using internal peer-to-peer communications and fast-flux domain naming that evade perimeter-based security tools. The document advocates deploying detection capabilities throughout the network rather than just at the boundary, and maintaining coordinated incident response plans and skills to understand adversaries' techniques.
Programa Pedagògic 2017-2018

Guia d'activitats pedagògiques del Museu Marítim de Barcelona per al curs 2017-2018
Guia de recursos d'educació ambiental 14-15 - Variats Mallorca

Part de la Guia de recursos d'educació ambiental disponibles per a tots els centres educatius de les Illes Balears per al curs 2014-2015, de forma gratuïta. En concret, aquí es mostren algunes de les activitats de Mallorca.
Camp d'Aprenentatge Vall de Boí - 6è

Presentació de diapositives reunió de pares - Camp d'Aprenentatge Vall de Boí. Escola El Prat de Llobregat I
Programa d'activitats pedagògiques mmb 2016 2017

Programa d'activitats pedagògiques del Museu Marítim de Barcelona per al curs 2016-2017
Activitats aqueni. 2020 21

Dossier d'activitats que oferim a diferents espais naturals de la província de Girona. Per fer amb grups escolars o amb grups particulars.
More Related Content
Similar to Aquàrium !!!
Programa Pedagògic 2017-2018

Guia d'activitats pedagògiques del Museu Marítim de Barcelona per al curs 2017-2018
Guia de recursos d'educació ambiental 14-15 - Variats Mallorca

Part de la Guia de recursos d'educació ambiental disponibles per a tots els centres educatius de les Illes Balears per al curs 2014-2015, de forma gratuïta. En concret, aquí es mostren algunes de les activitats de Mallorca.
Camp d'Aprenentatge Vall de Boí - 6è

Presentació de diapositives reunió de pares - Camp d'Aprenentatge Vall de Boí. Escola El Prat de Llobregat I
Programa d'activitats pedagògiques mmb 2016 2017

Programa d'activitats pedagògiques del Museu Marítim de Barcelona per al curs 2016-2017
Activitats aqueni. 2020 21

Dossier d'activitats que oferim a diferents espais naturals de la província de Girona. Per fer amb grups escolars o amb grups particulars.
Similar to Aquàrium !!! (20)
Guia de recursos d'educació ambiental 14-15 - Variats Mallorca

Guia de recursos d'educació ambiental 14-15 - Variats Mallorca
Submergiu vos en una aventura marina. curs 2005-06

Submergiu vos en una aventura marina. curs 2005-06
Radio Híbrido en la Revista Bocamolla del IES Manacor de España. 

Radio Híbrido en la Revista Bocamolla del IES Manacor de España.
More from RibasLG
Les Bondats del programari Lliure

Este documento describe los beneficios del software libre, incluyendo la libertad de distribución, uso y modificación del código. El software libre ofrece ventajas como código abierto que permite a otros usar y mejorar el software, y libertad total sobre cómo y para qué se usa el programa.
Les Bondats del Programari Lliure

Este documento describe los beneficios del software libre, incluyendo la libertad de distribución, uso y modificación del código. El software libre ofrece ventajas como código abierto que permite a otros usar y mejorar el software, y libertad de uso sin restricciones.
Les Bondats del programari Lliure

Este documento describe los beneficios del software libre, incluyendo la libertad de distribución, uso y modificación del código. El software libre ofrece ventajas como código abierto que permite a otros aprender de él y mejorarlo, libertad de uso sin restricciones, y capacidad de adaptar el software para usos específicos.
Les Bondats del Programari Lliure

Este documento describe los beneficios del software libre, incluyendo la libertad de distribución, uso y modificación del código. El software libre ofrece ventajas como código abierto que permite a otros aprender de él y mejorarlo, libertad de uso sin restricciones, y capacidad de adaptar el software para usos específicos.
More from RibasLG (10)
Recently uploaded
INFORME ASSIGNADES CURS 24-25. ROSER CAPDEVILA

Persones assignades a l'escola Roser Capdevila, de Sant Joan Despí, per al curs 2024-2025
Viceverba_appdelmes_0624_joc per aprendre verbs llatins

Vice Verba és una aplicació educativa dissenyada per ajudar els estudiants de llatí a aprendre i practicar verbs llatins d'una manera interactiva i entretinguda.
INFORME_LLISTA_ESPERA_OME_LLISTA_ESPERA (2).pdf

Llista d'espera per la preinscripció 24-25 de l'escola Roser Capdevila de Sant Joan Despí.
Recently uploaded (9)
Implica't+ amb la Carta de la Terra i l'Agenda 2030

Implica't+ amb la Carta de la Terra i l'Agenda 2030
INFORME_PREINSCRITES_OME_INFORME_PREINSCRITES_OME.pdf

INFORME_PREINSCRITES_OME_INFORME_PREINSCRITES_OME.pdf
Viceverba_appdelmes_0624_joc per aprendre verbs llatins

Viceverba_appdelmes_0624_joc per aprendre verbs llatins
Aquàrium !!!
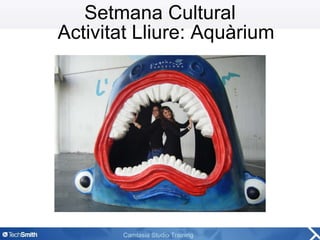
- 1. Setmana Cultural Activitat Lliure: Aquàrium
- 2. El Centre Des del Departament d'Educació de L'Aquàrium de Barcelona hem elaborat una sèrie d'activitats per a tots els nivells educatius atenint-nos als objectius del currículum establert i amb un triple objectiu: - Apropar l’alumnat al fascinant món submarí, en especial a la mar Mediterrània. - Sensibilitzar l’alumnat pel que fa a la preservació del medi marí. - Ésser un suport per al professorat, oferint L’Aquàrium com una eina de treball completa, divertida i interessant.
- 5. Resposta dels nens: Els nens posaven cara de sorpresa en escoltar les explicacions, i encara se’ls miraven amb més entusiasme i admiració. El que ens va cridar força l’atenció van ser les explicacions dels guies on les paraules tècniques (tecnicismes) els hi feien repetir 2 o 3 cops. Exemple: simbiosi o habitat. Després de les explicacions, en el torn de preguntes els nens realitzaven moltes intervencions tot i que no fossin preguntes. Per acabar l’activitat al Aquàrium, varem anar a una aula taller, la qual van realitzar col·laboradors del centre una petita interpretació teatral.