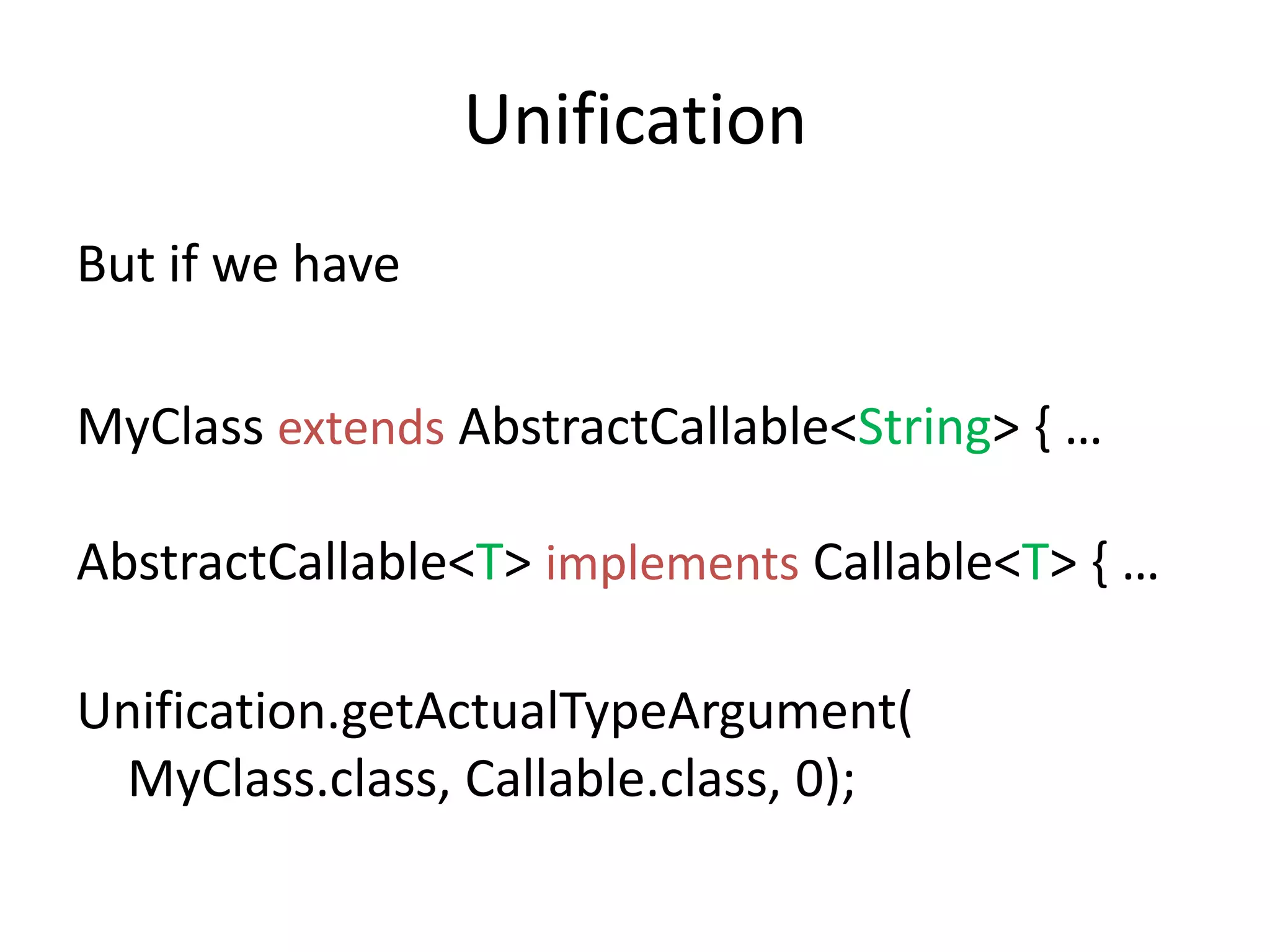
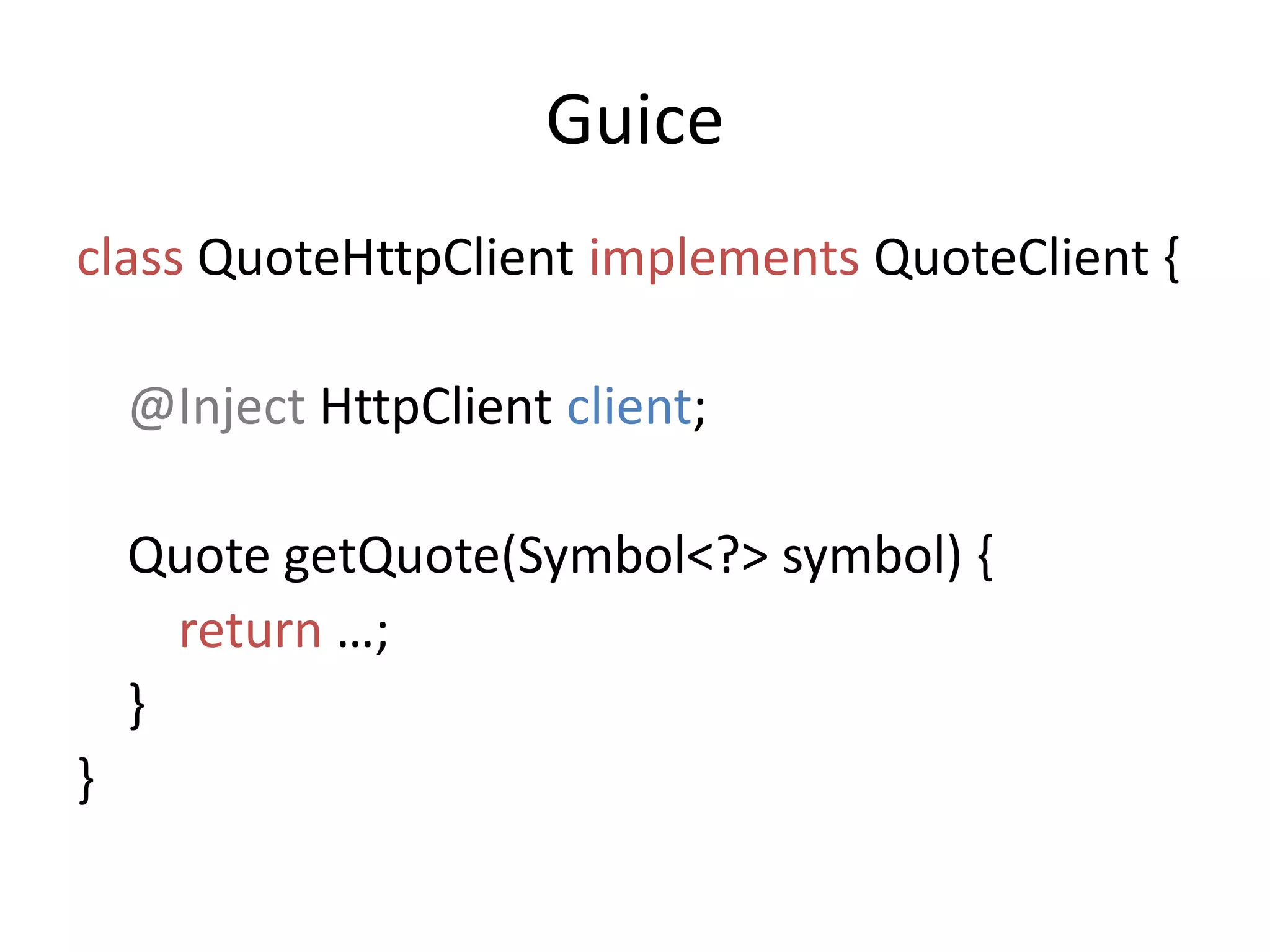
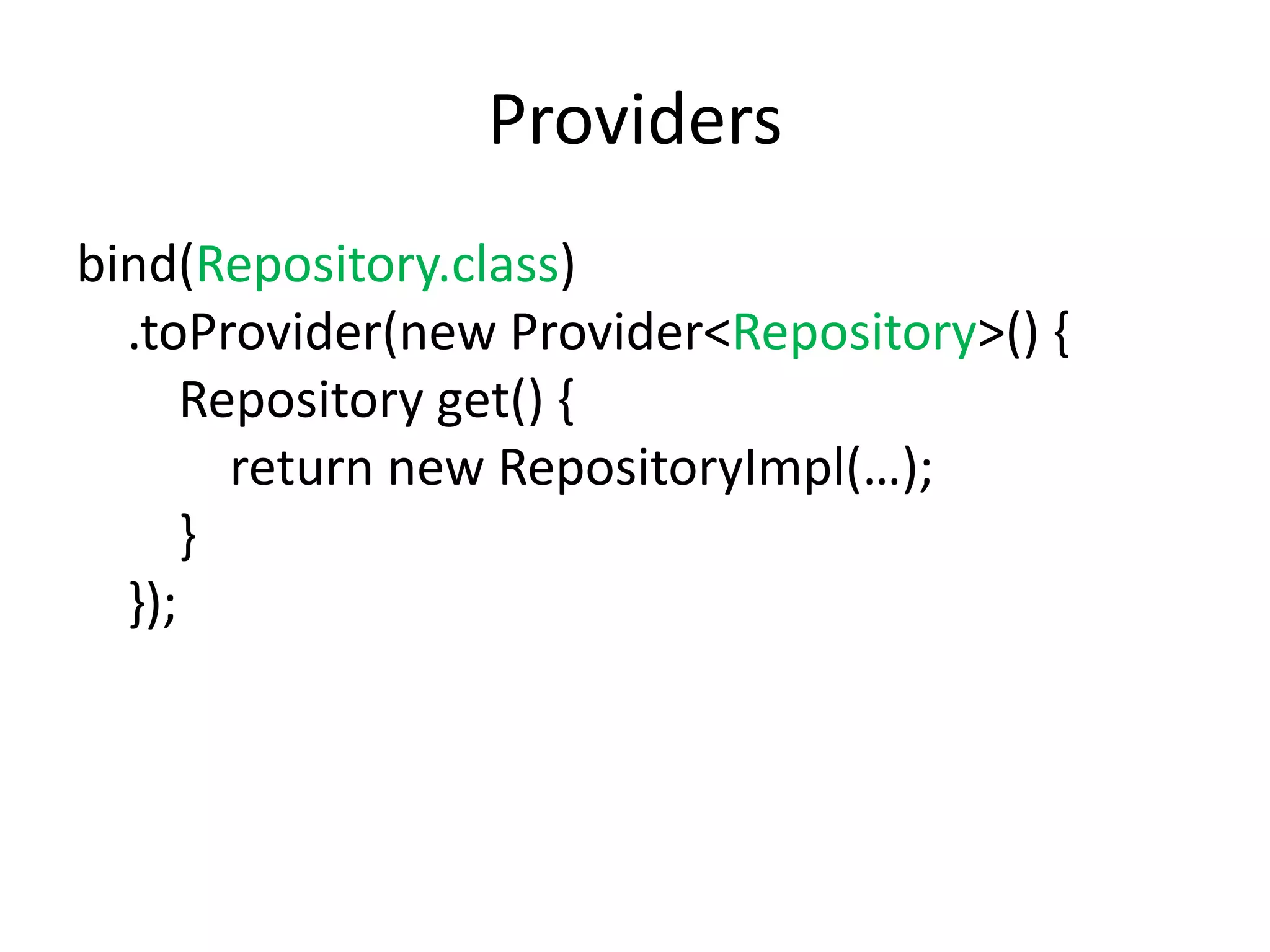
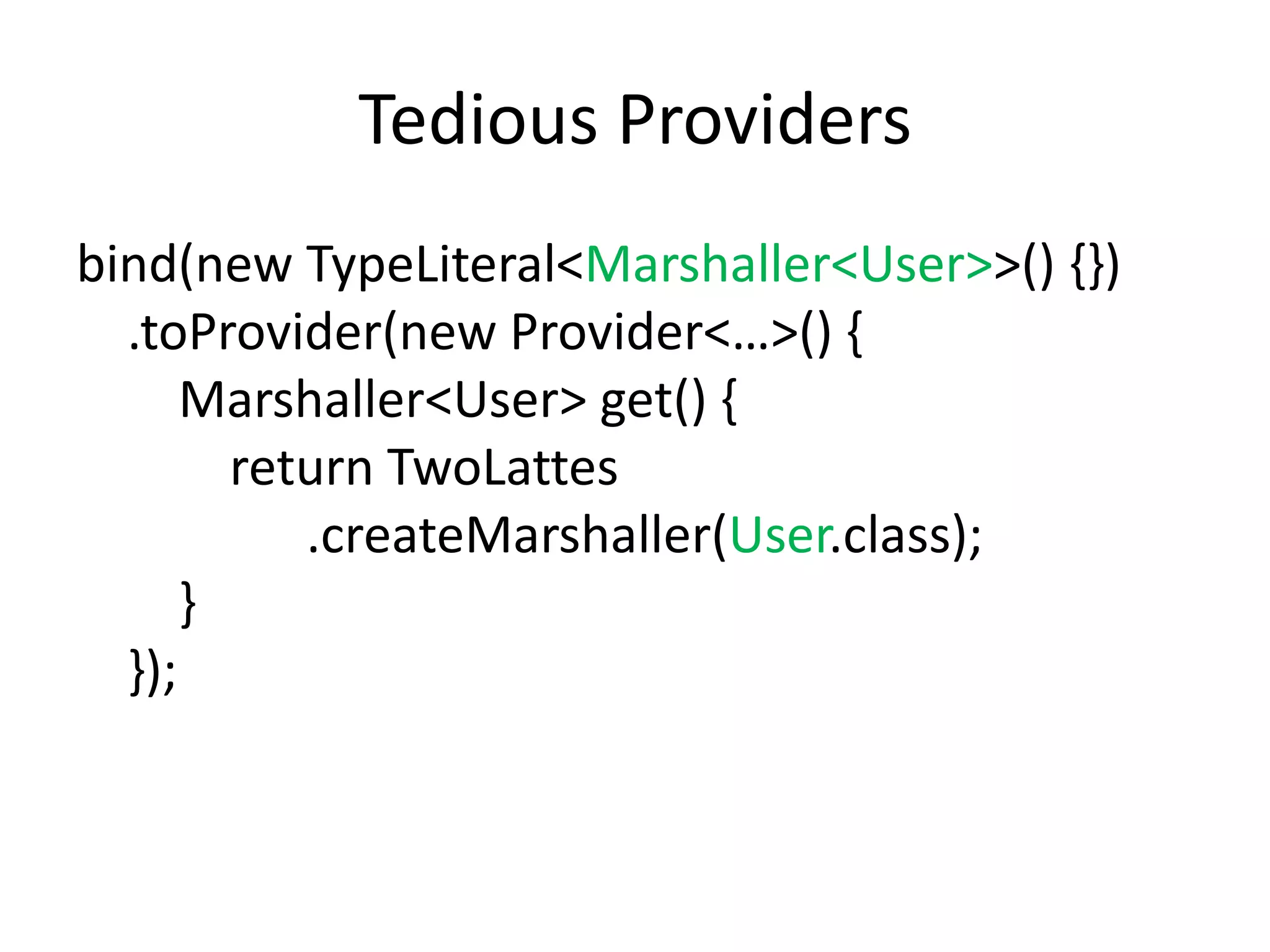
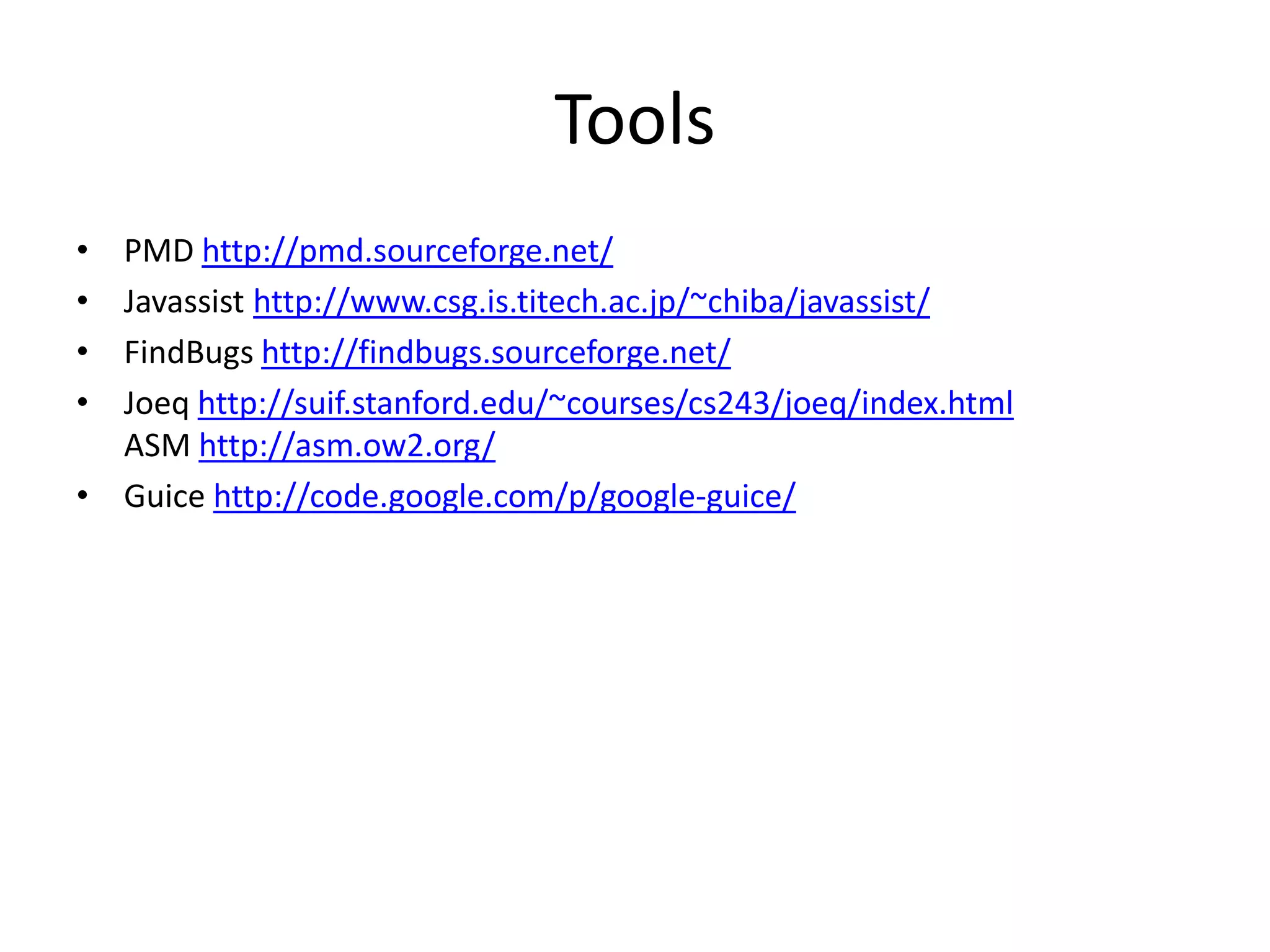
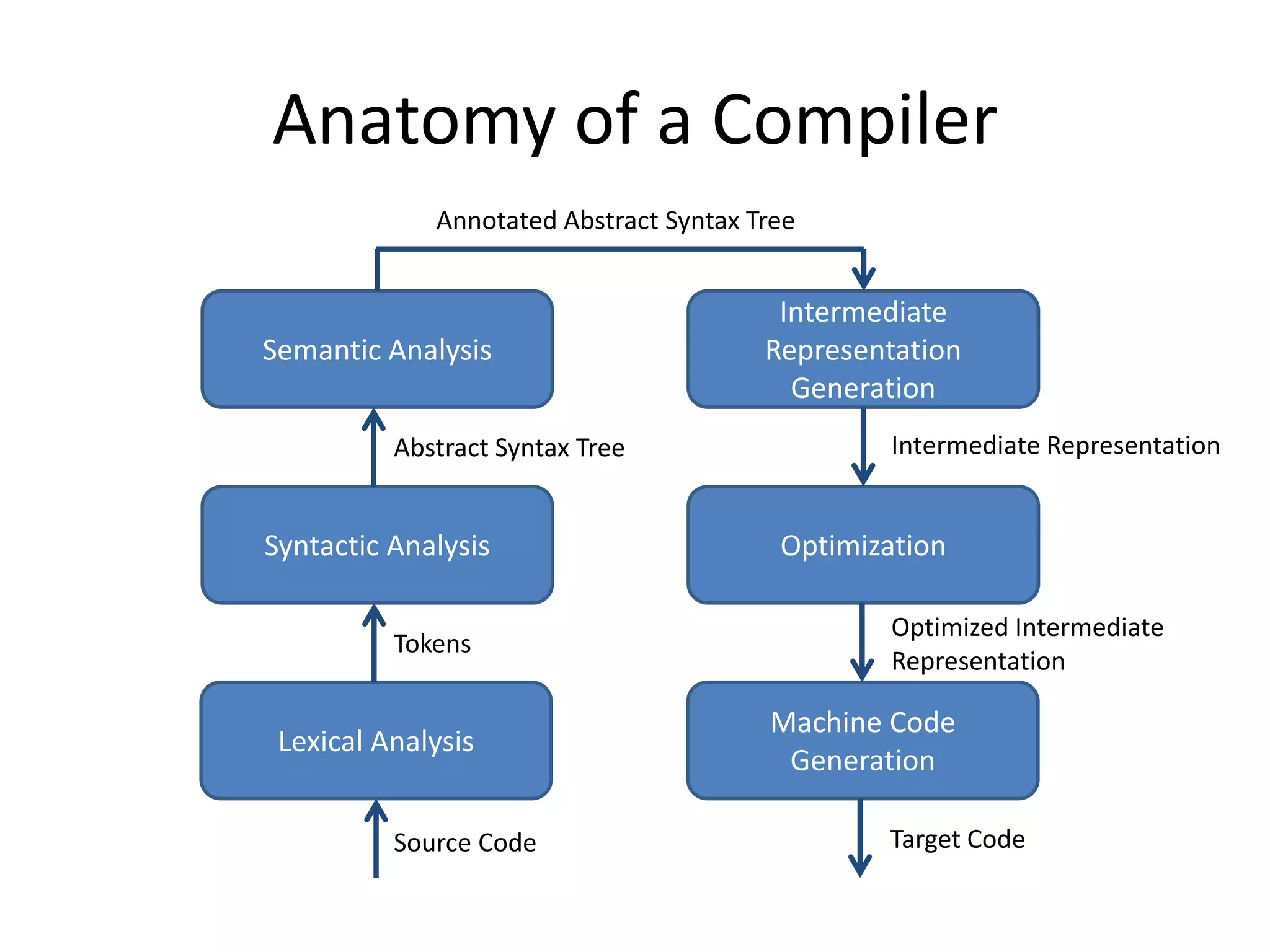
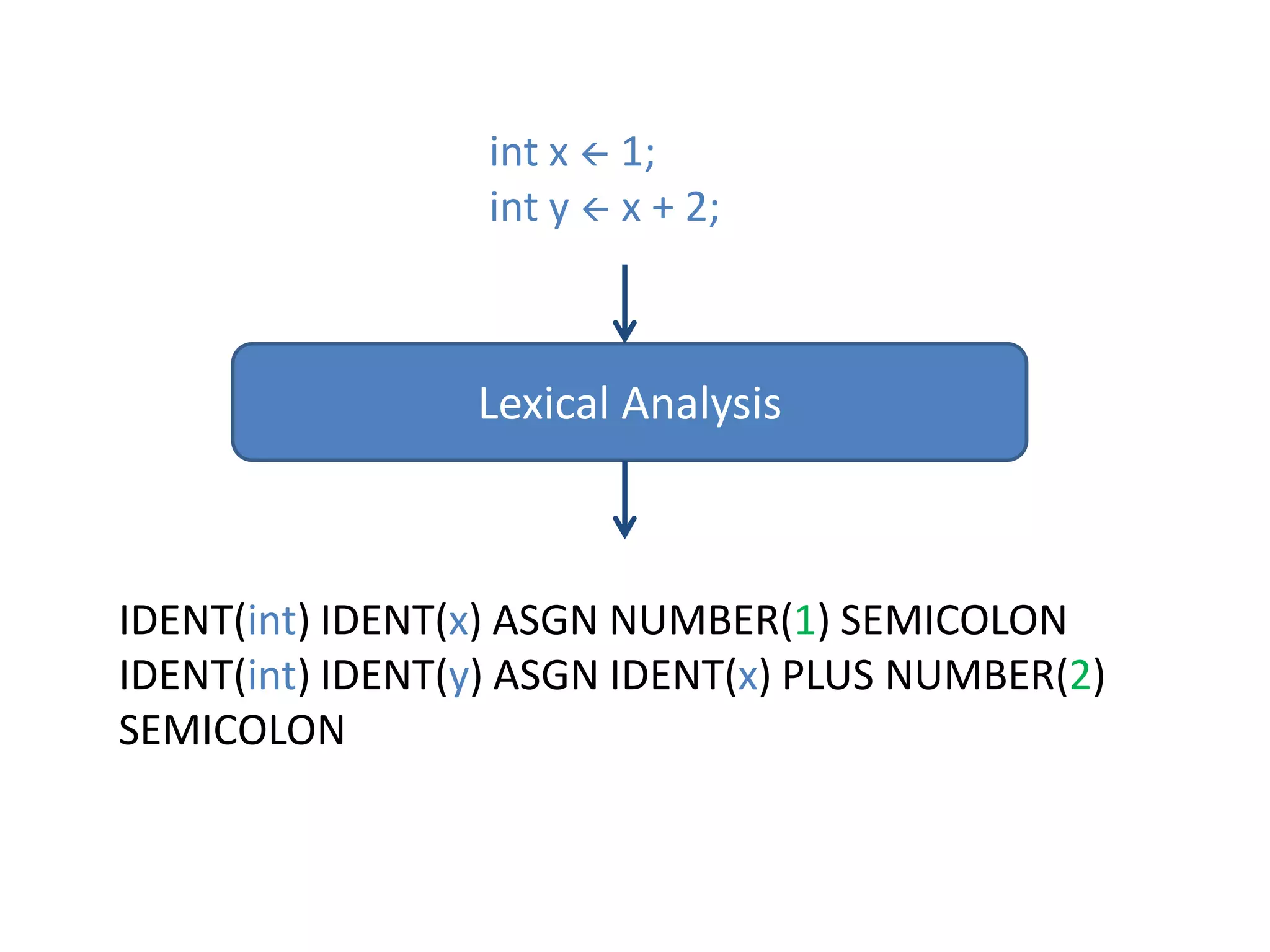
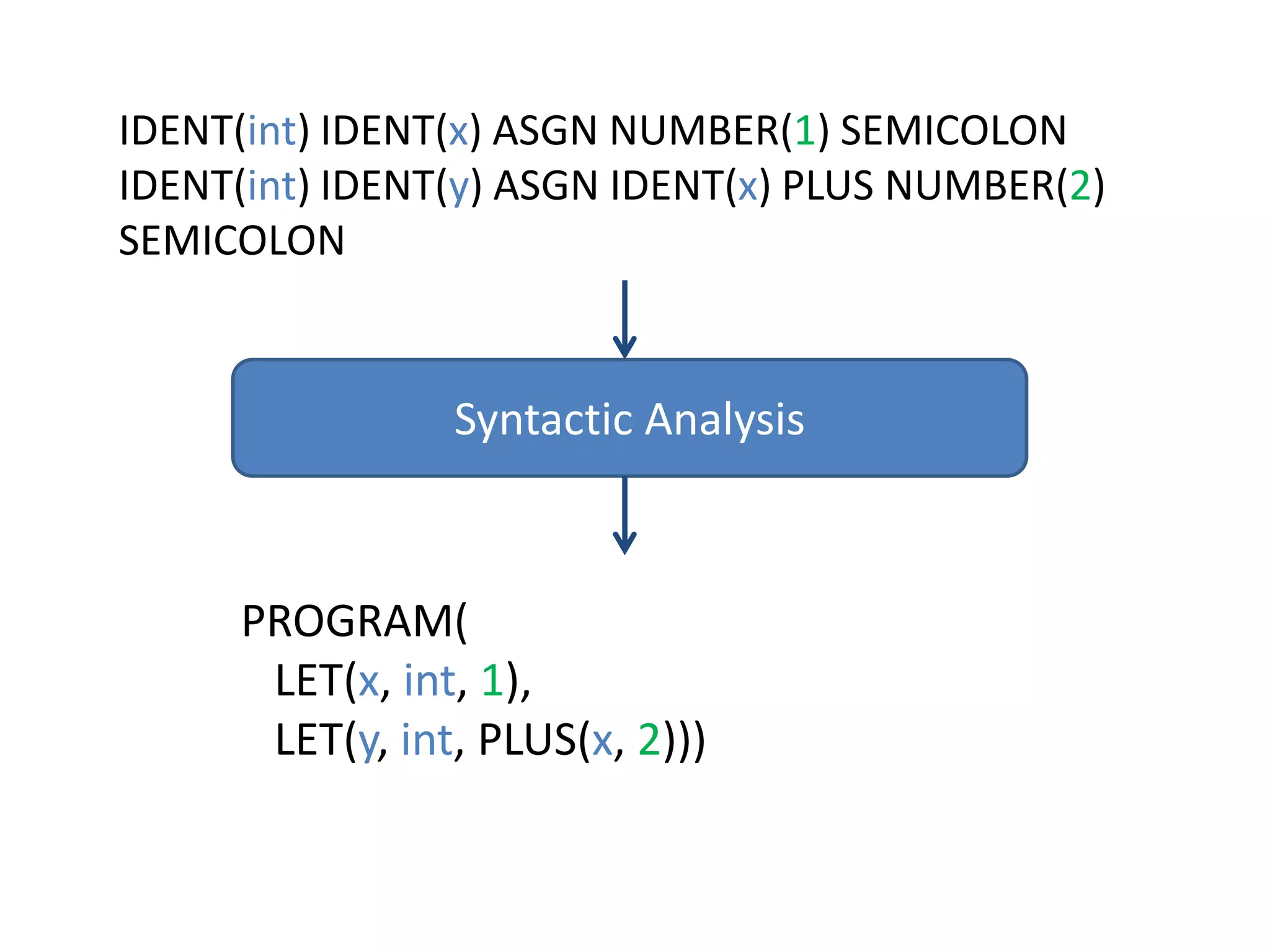
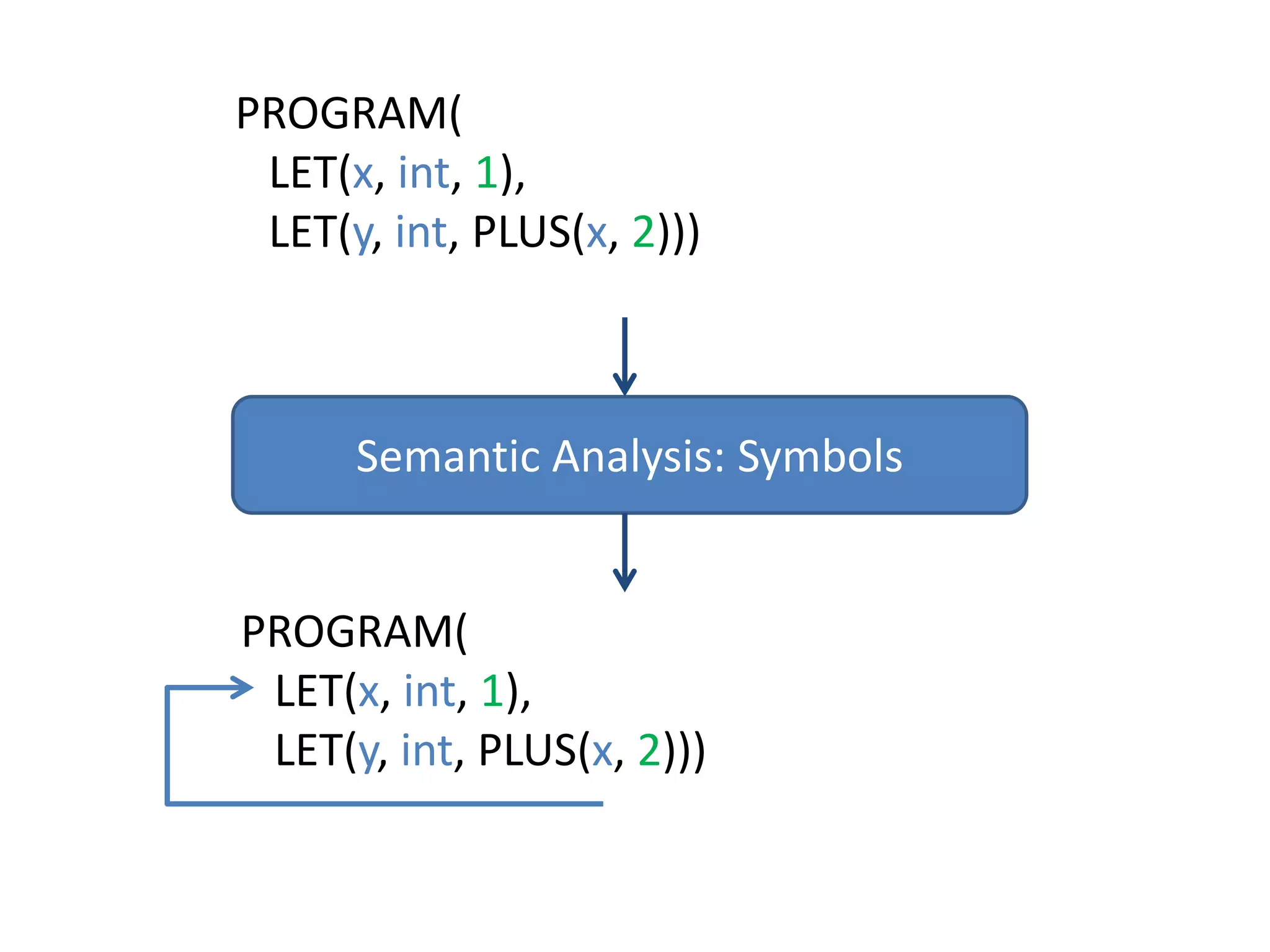
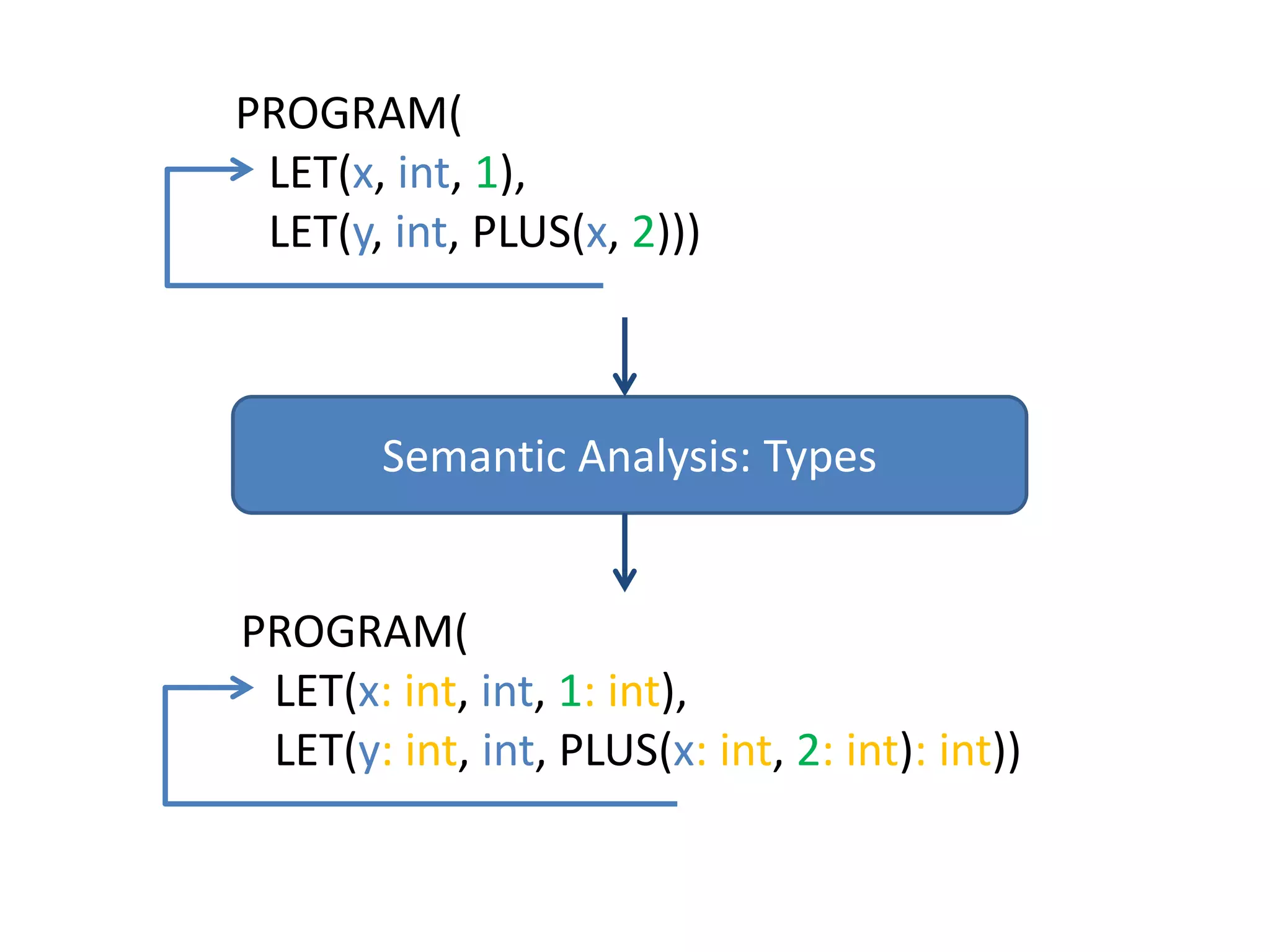
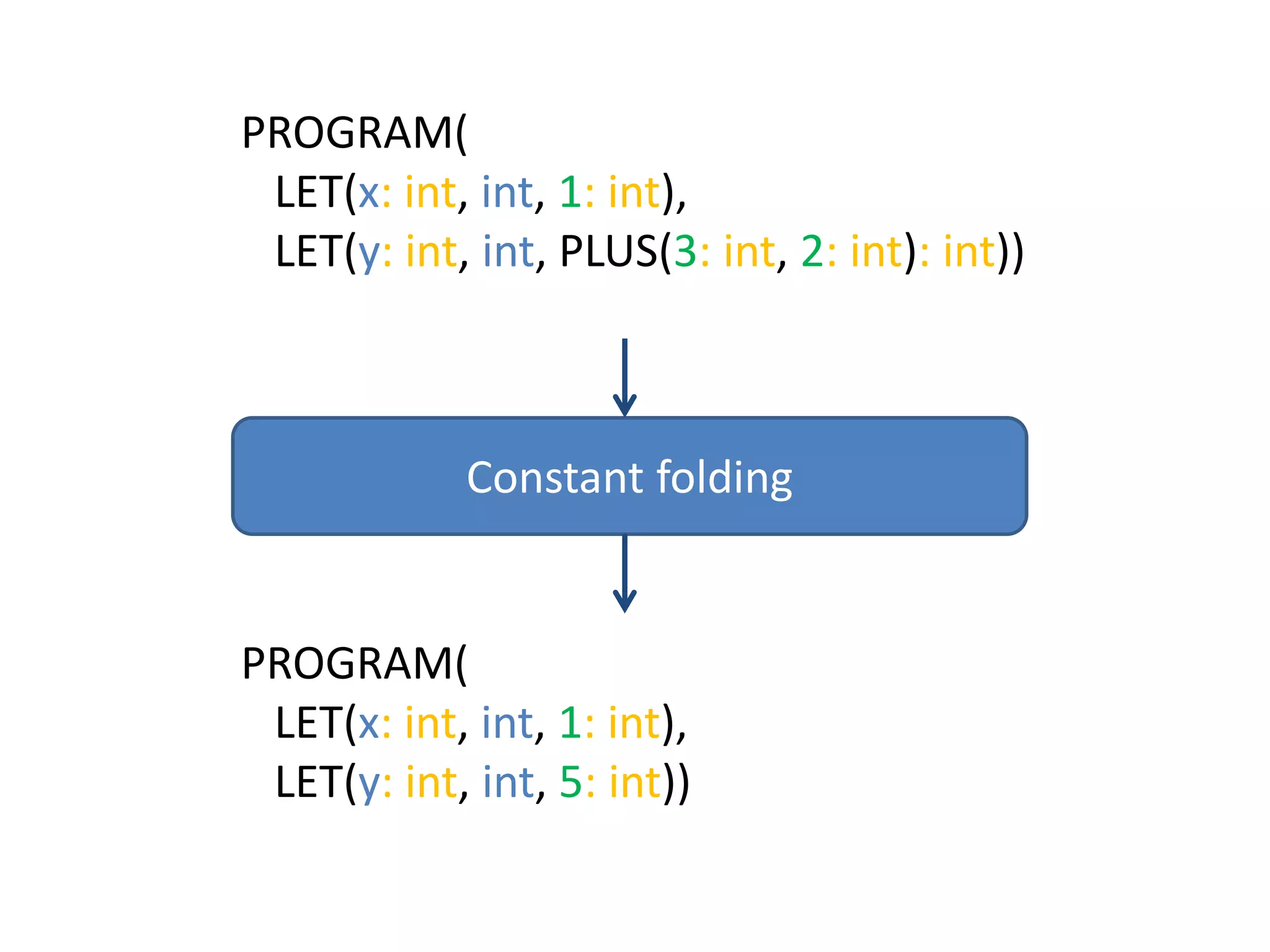
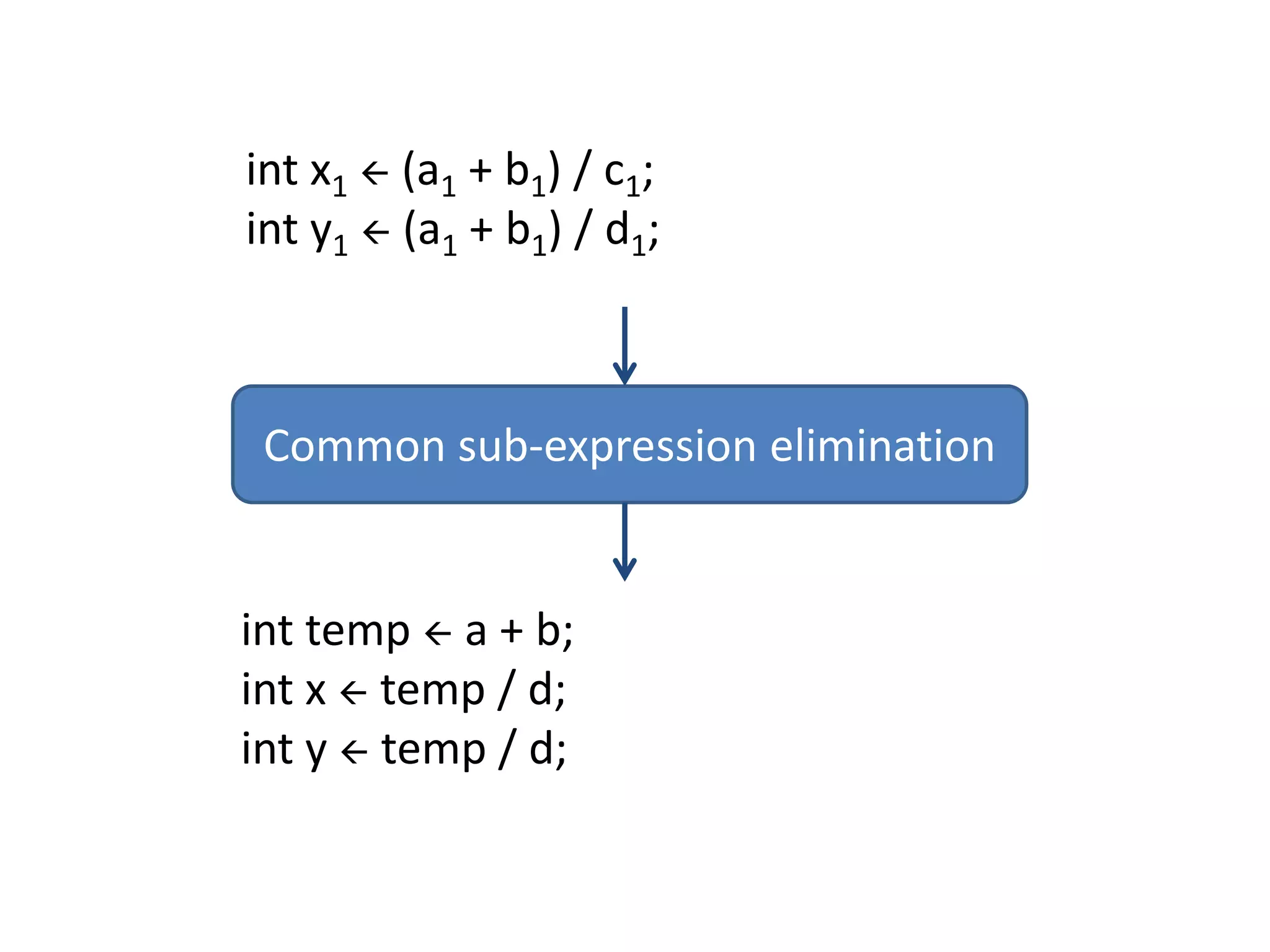
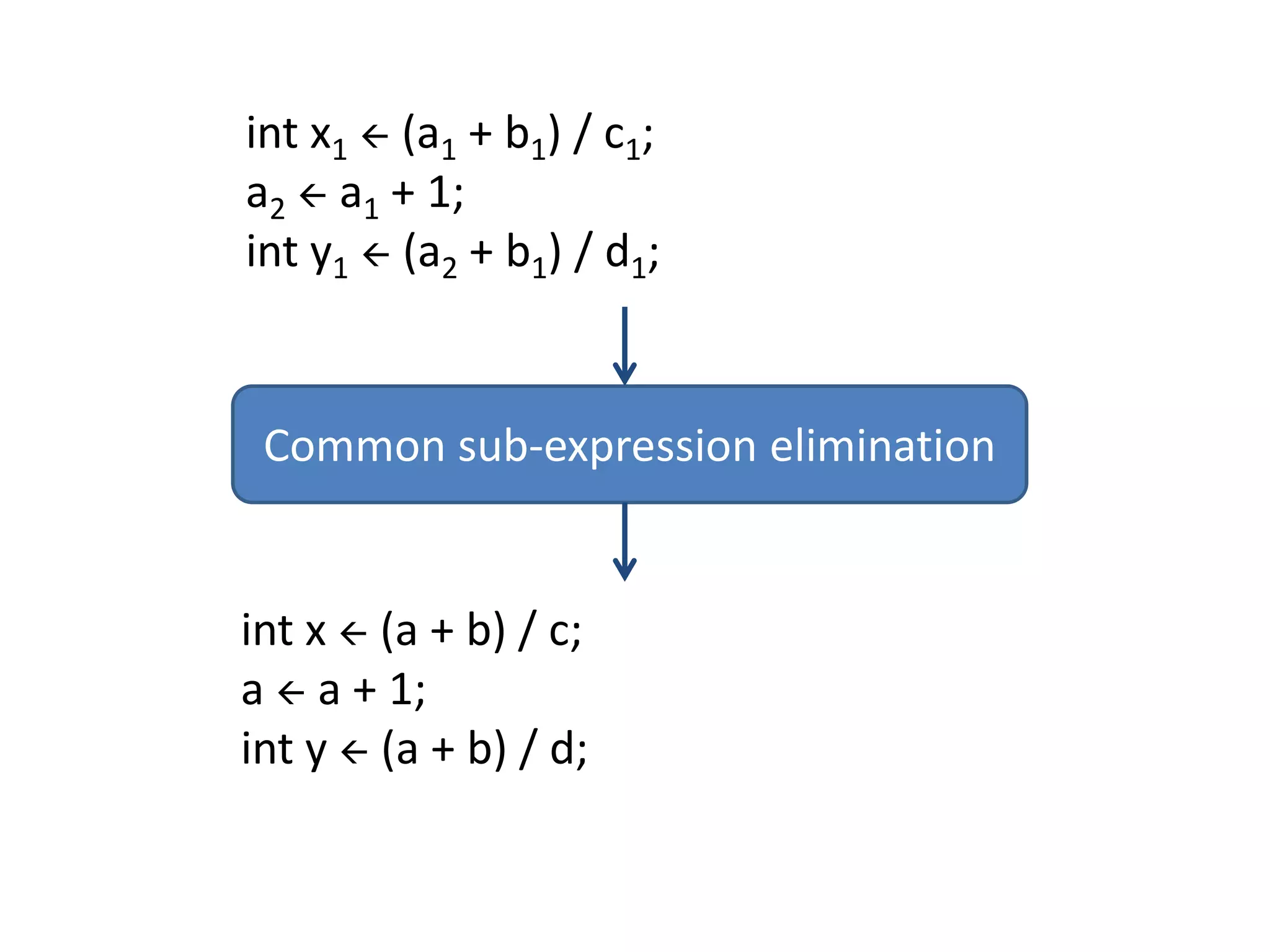
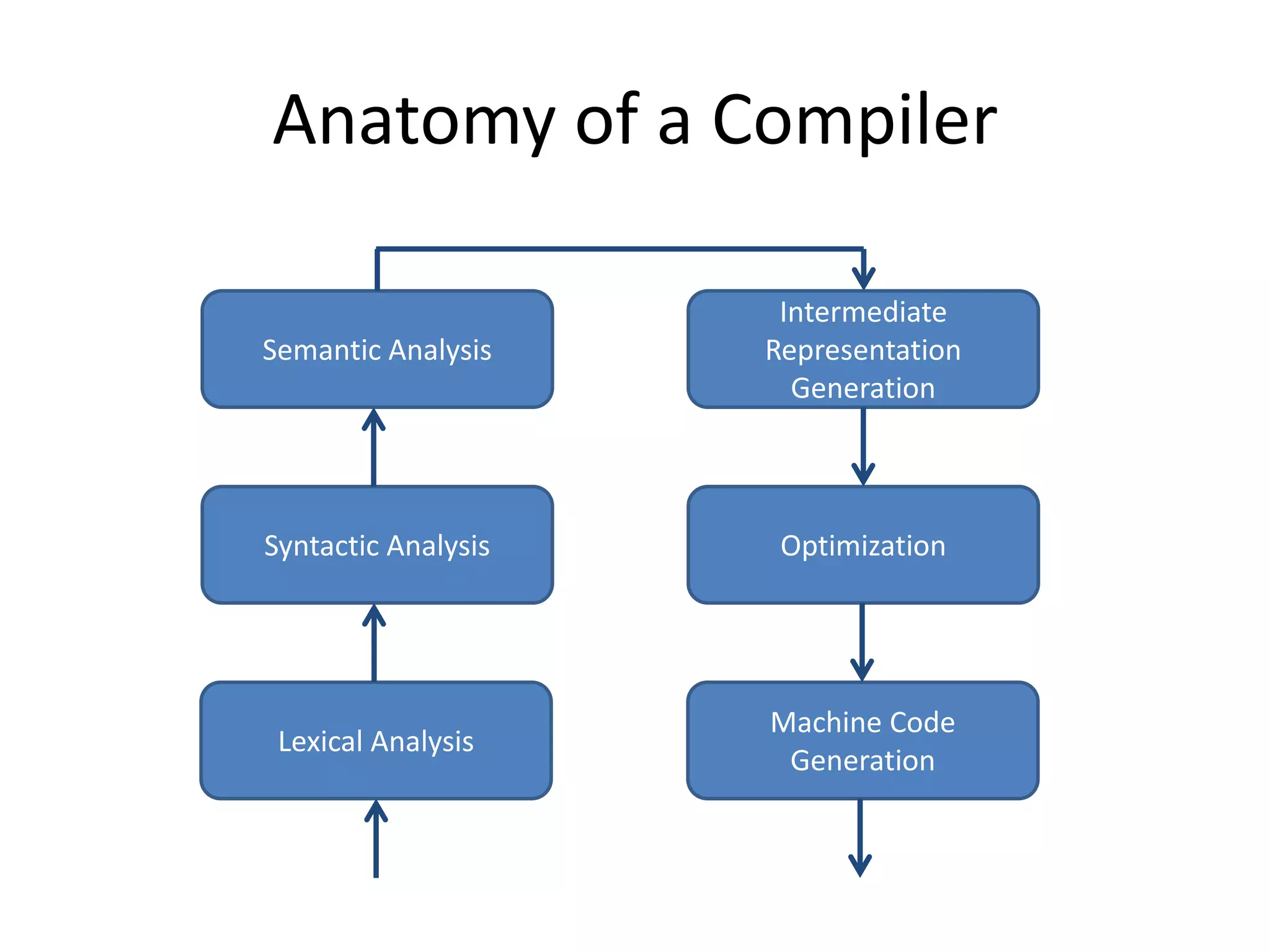
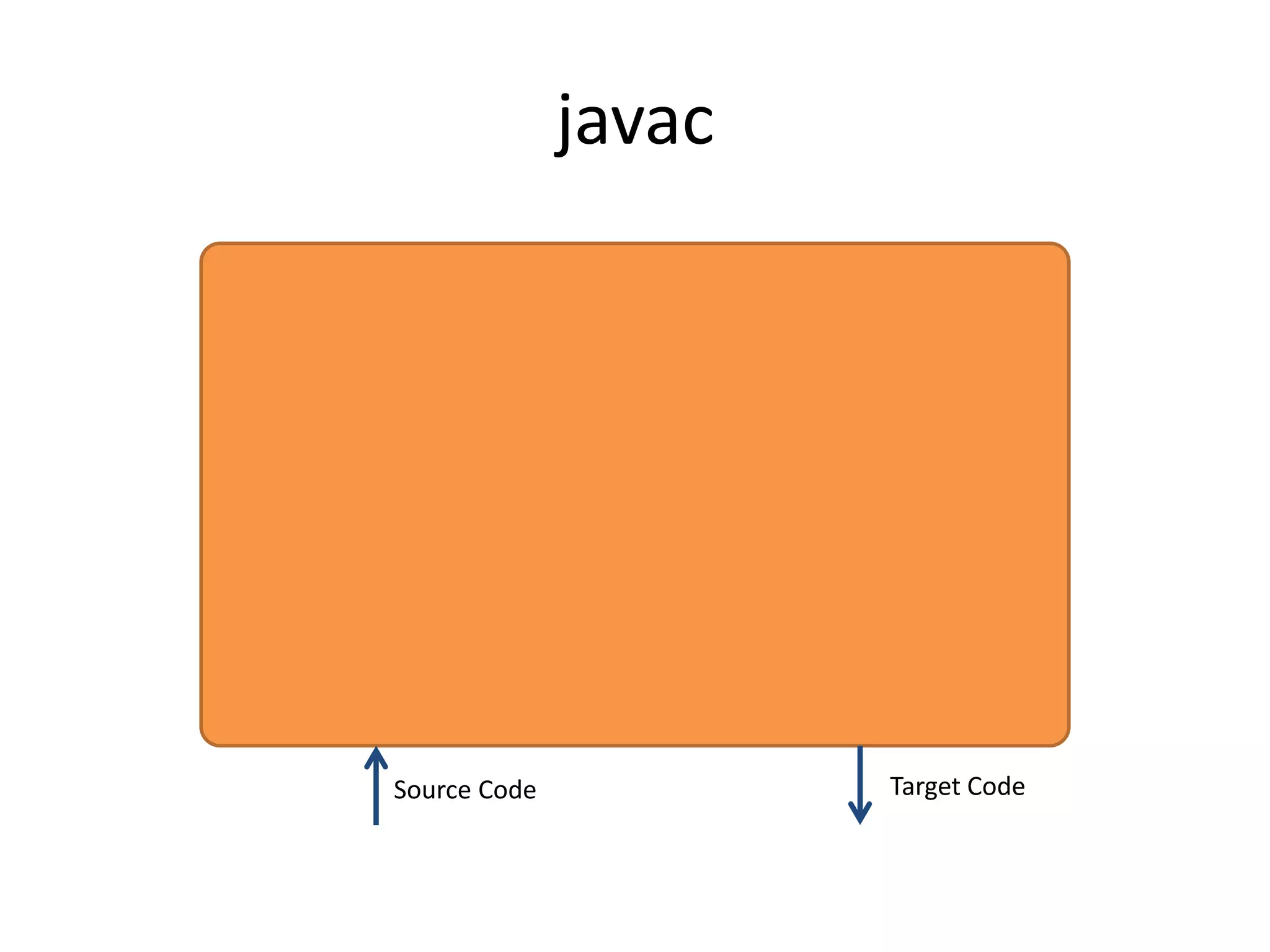
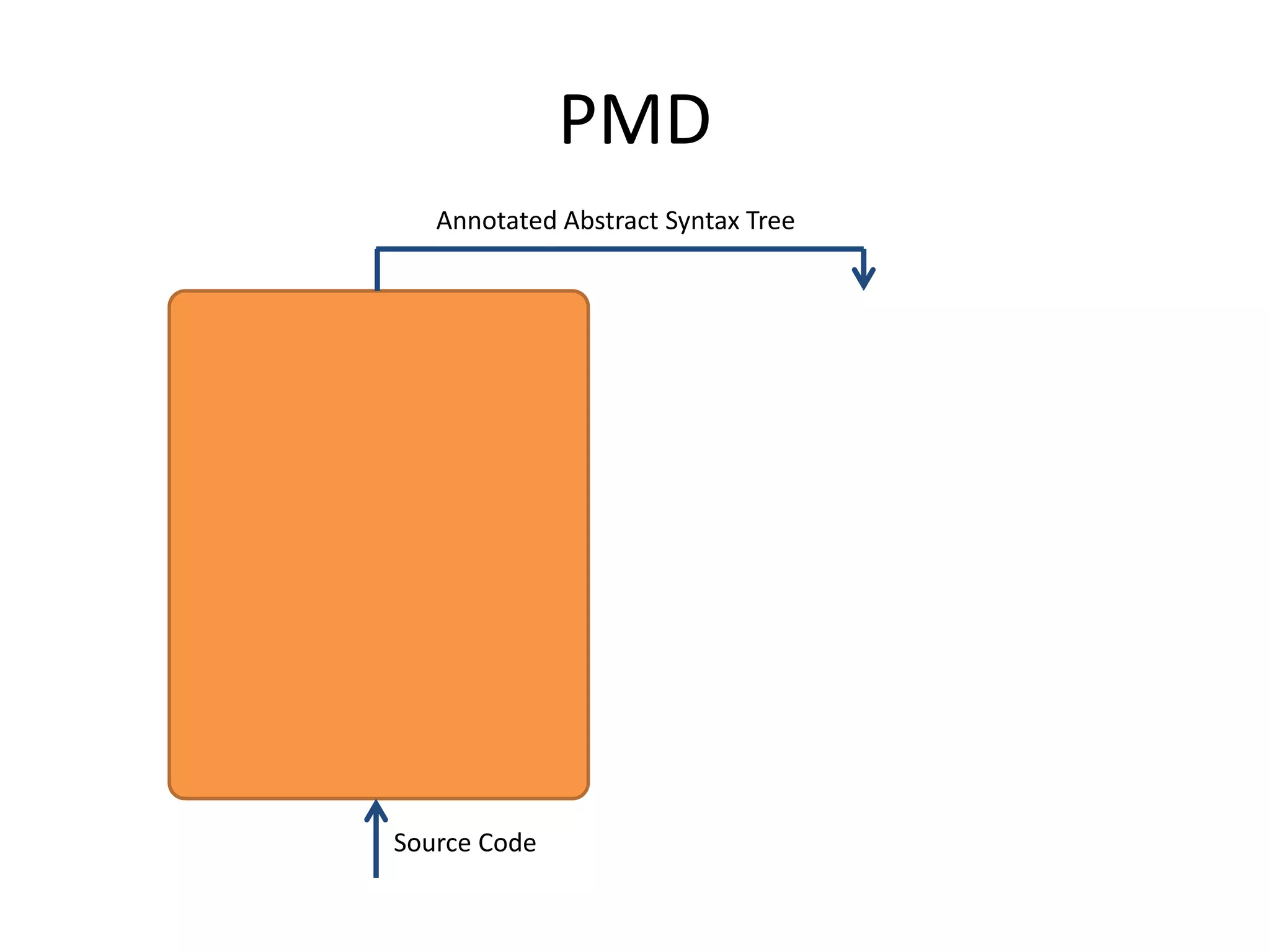
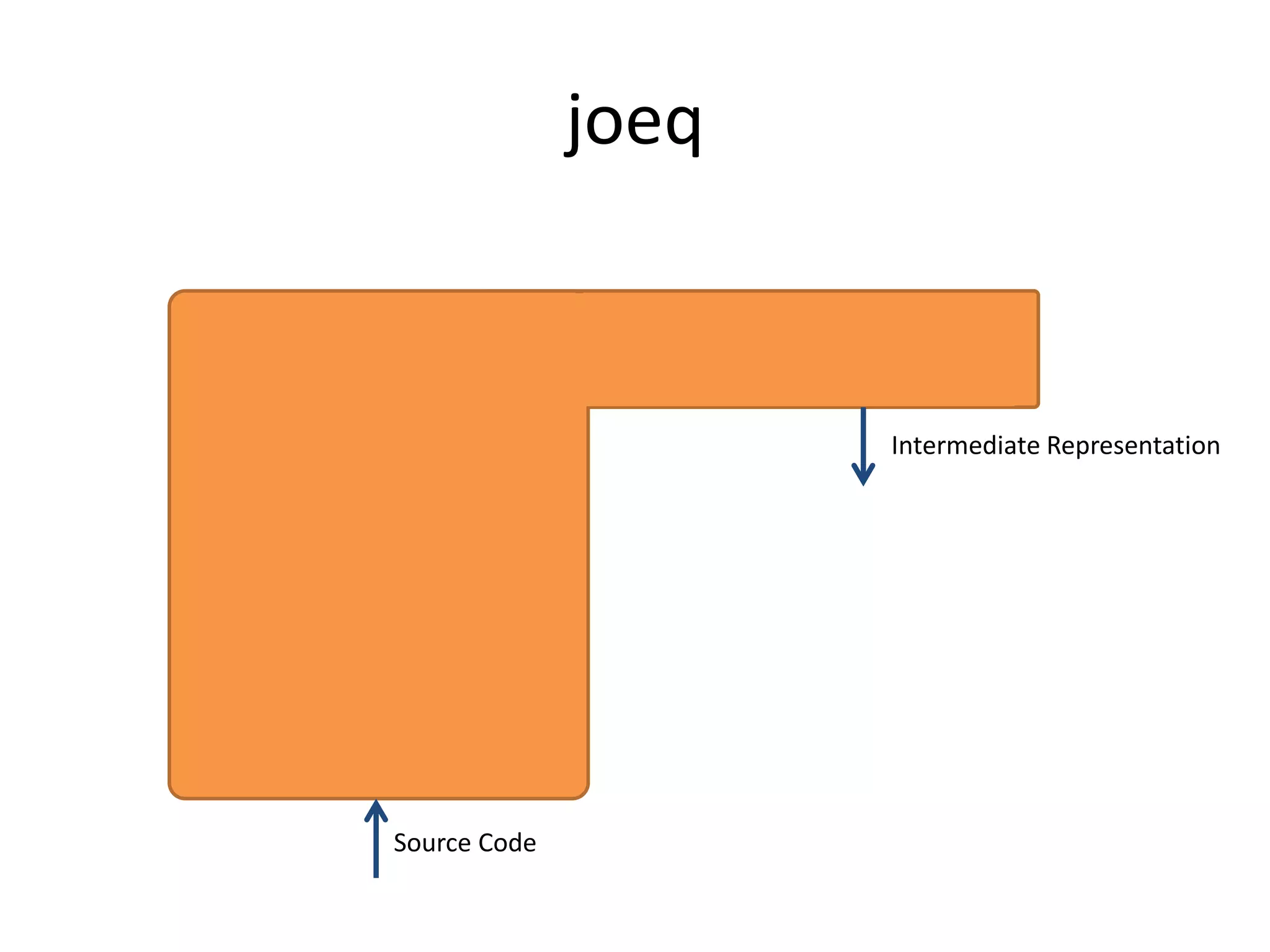
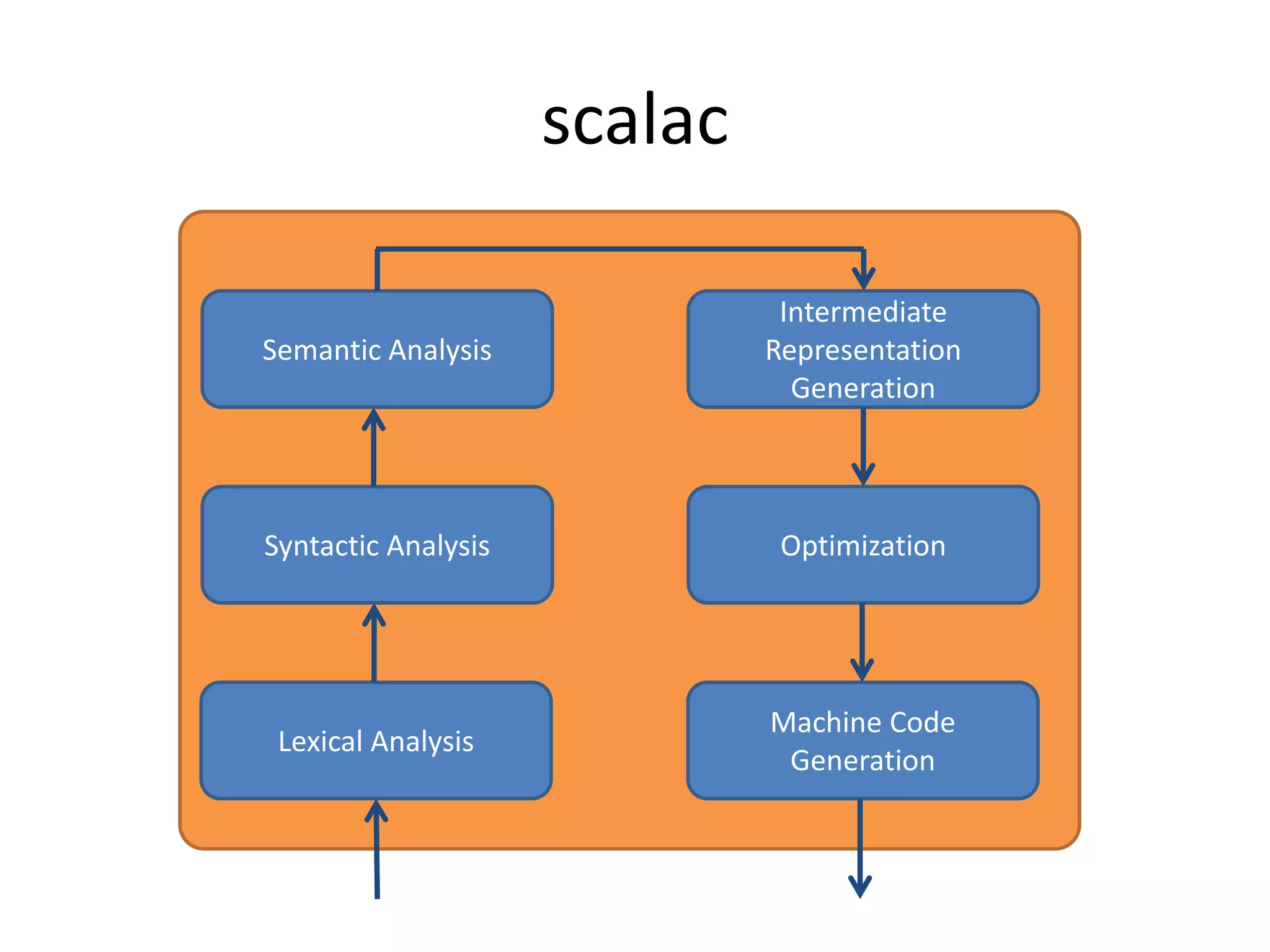
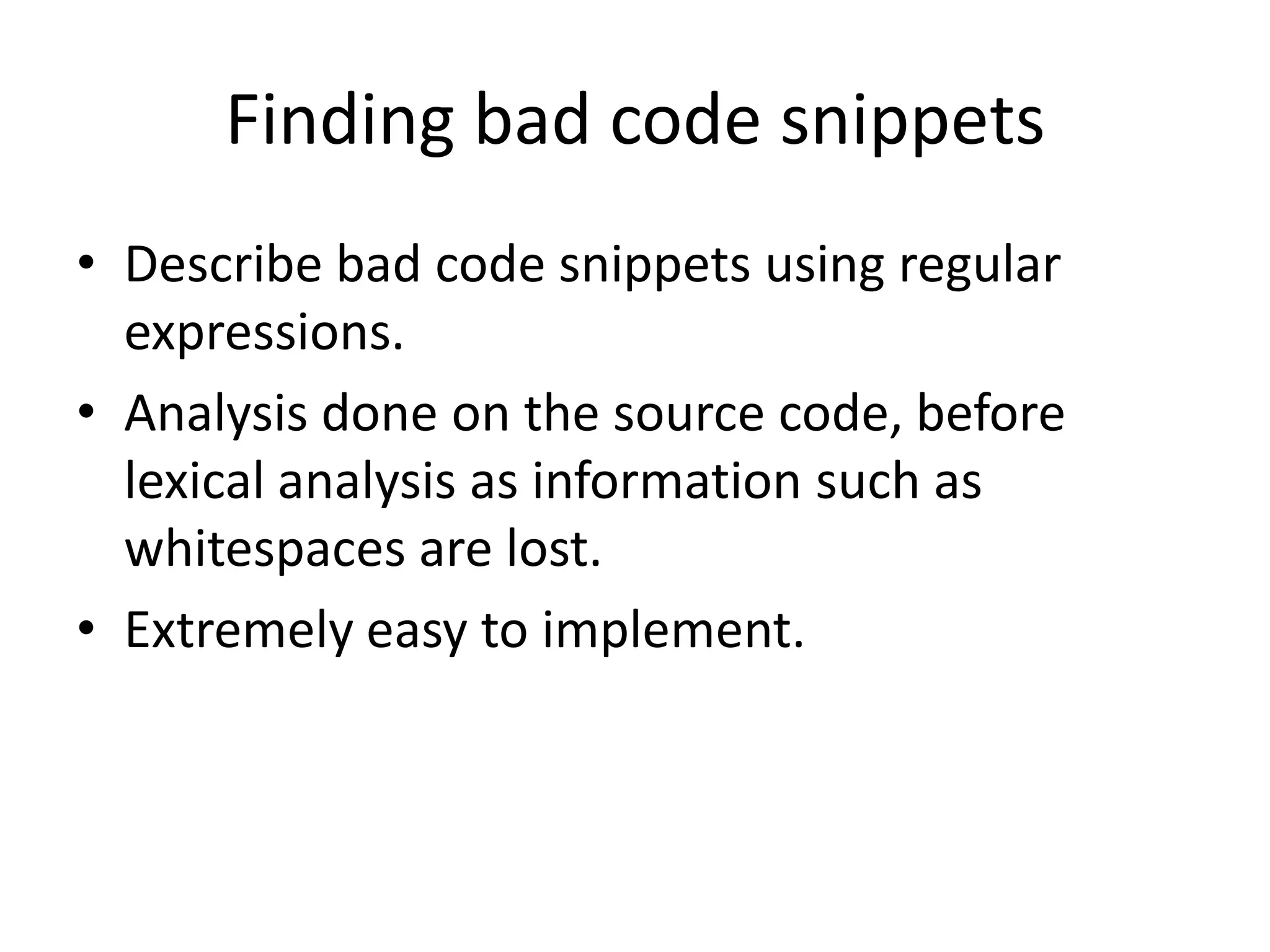
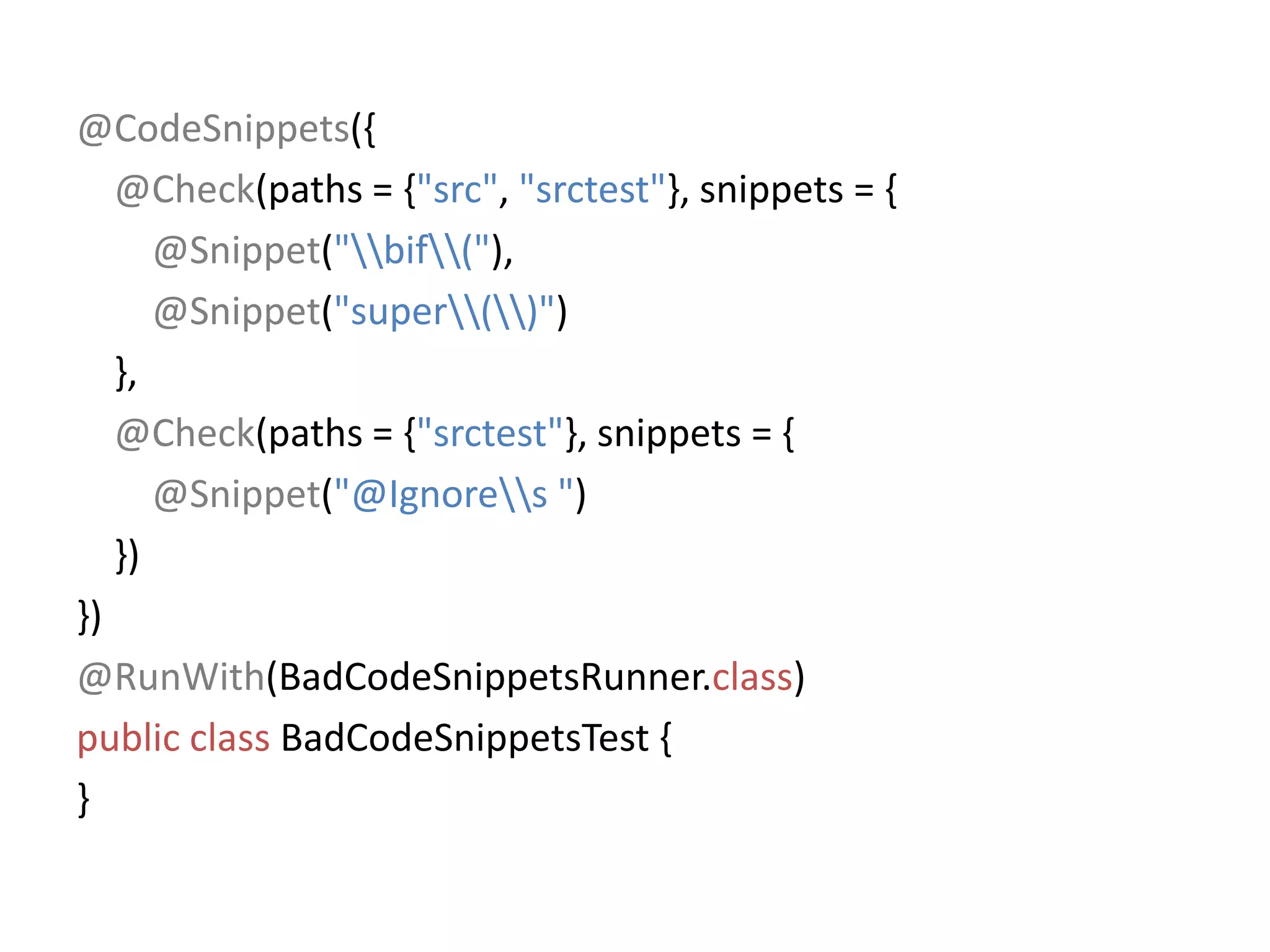
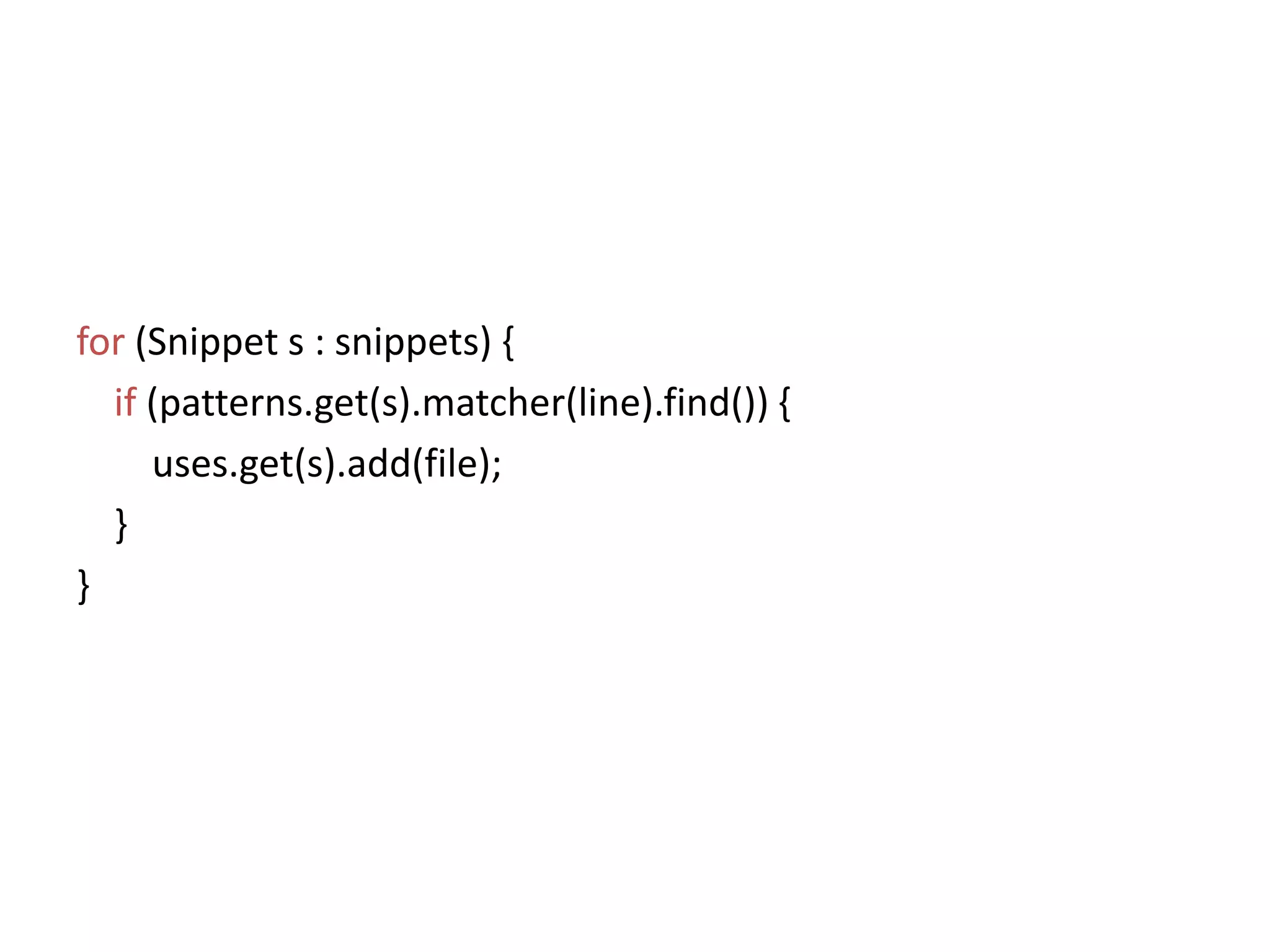
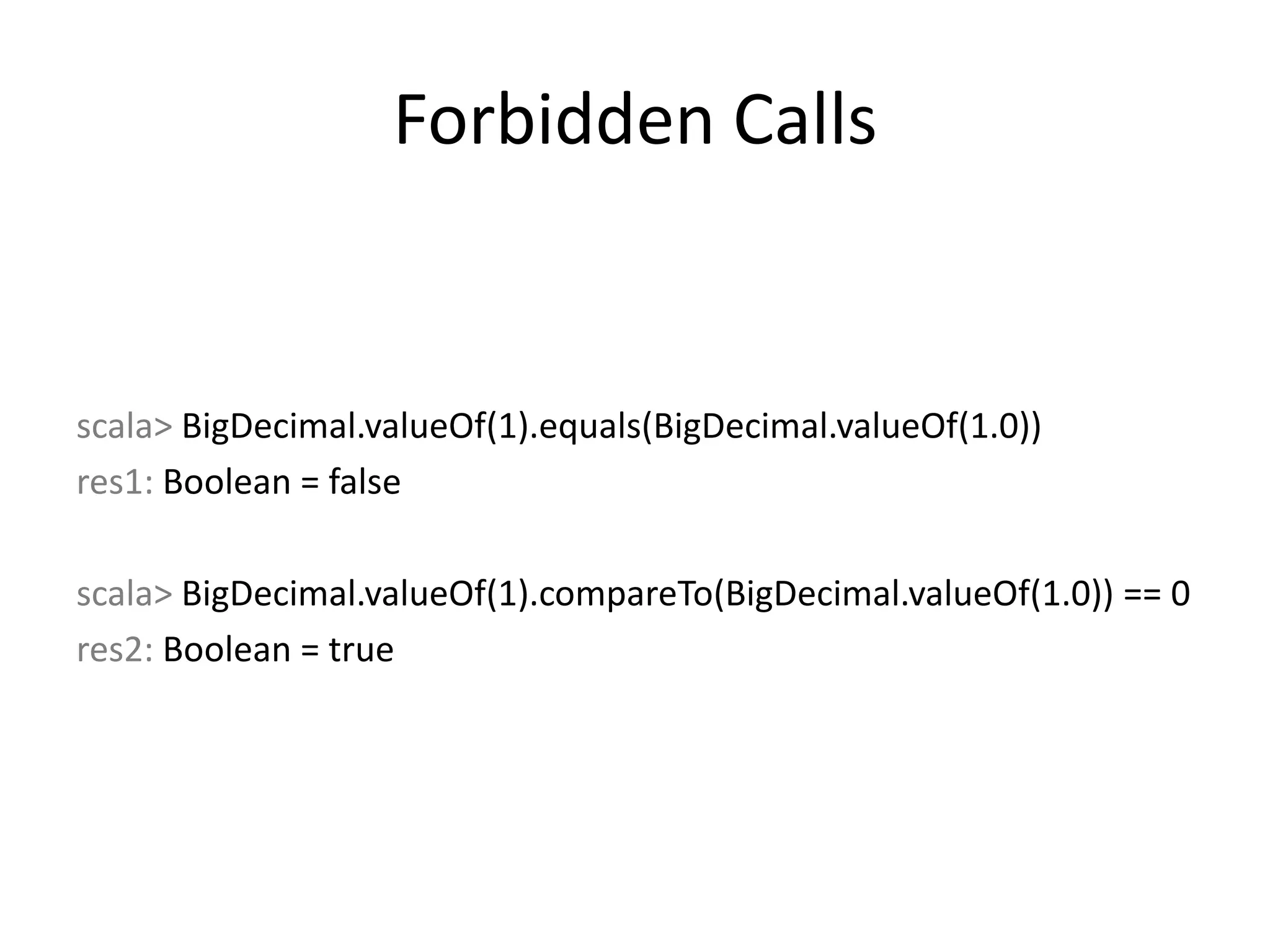
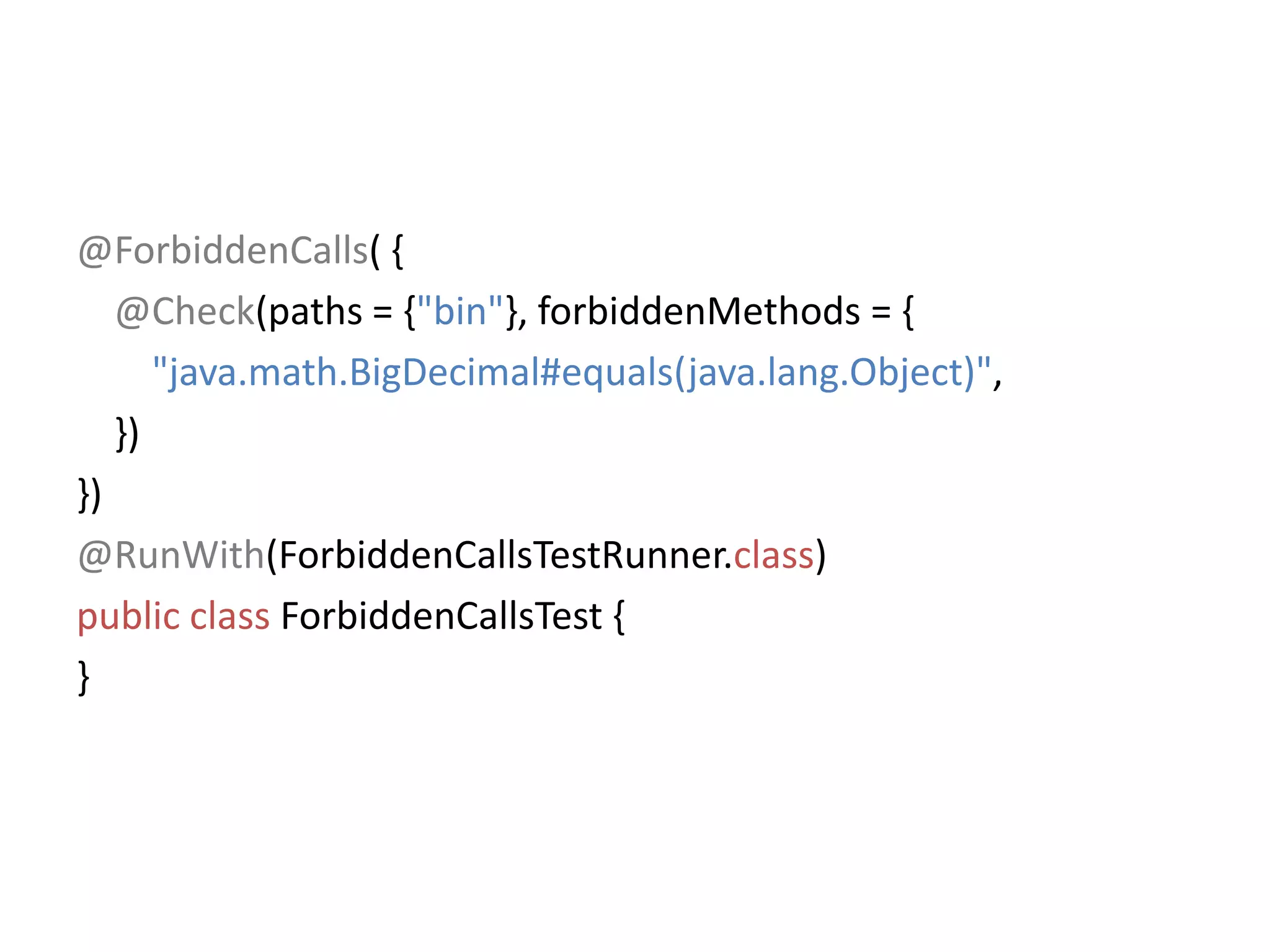
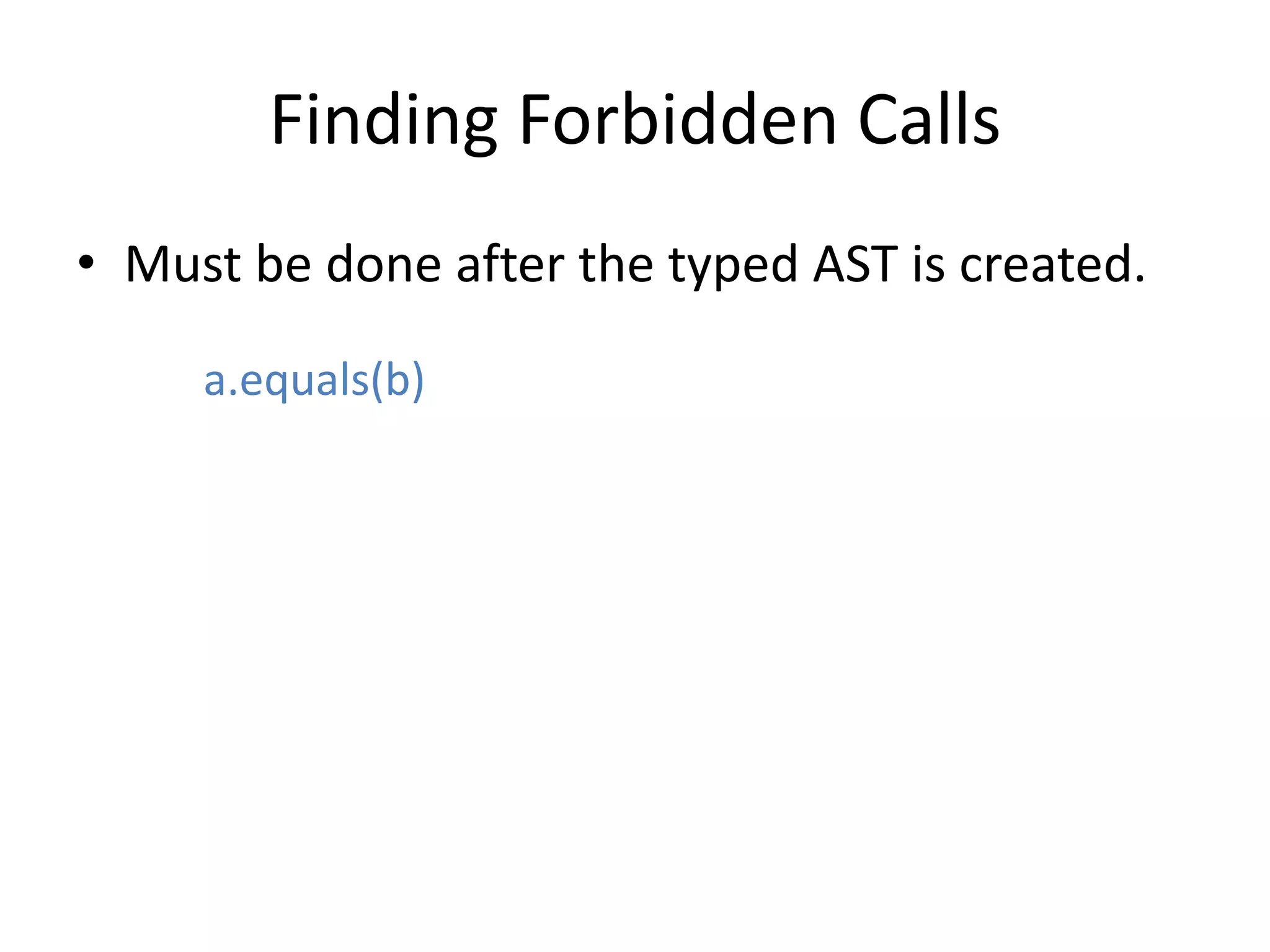
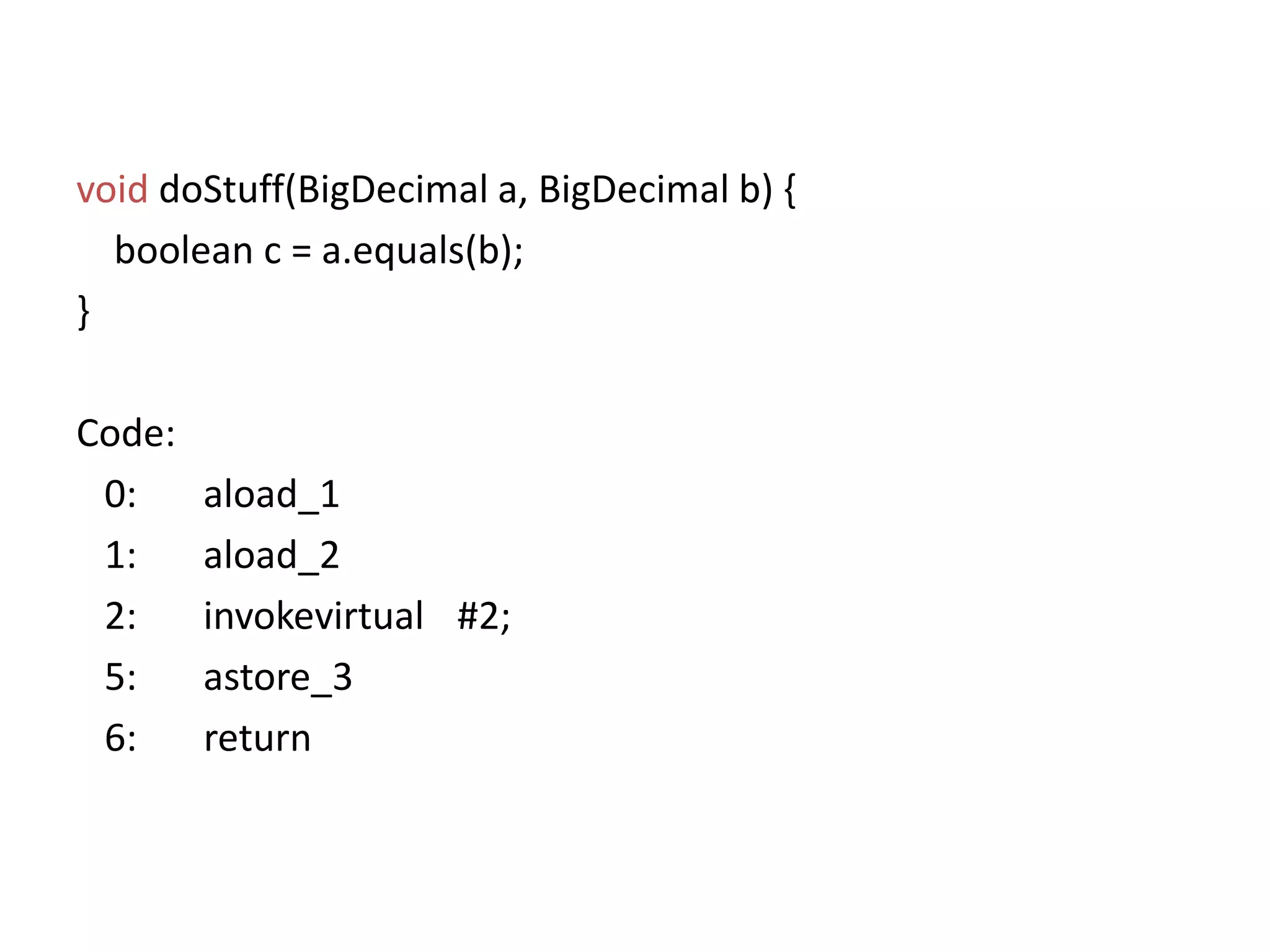
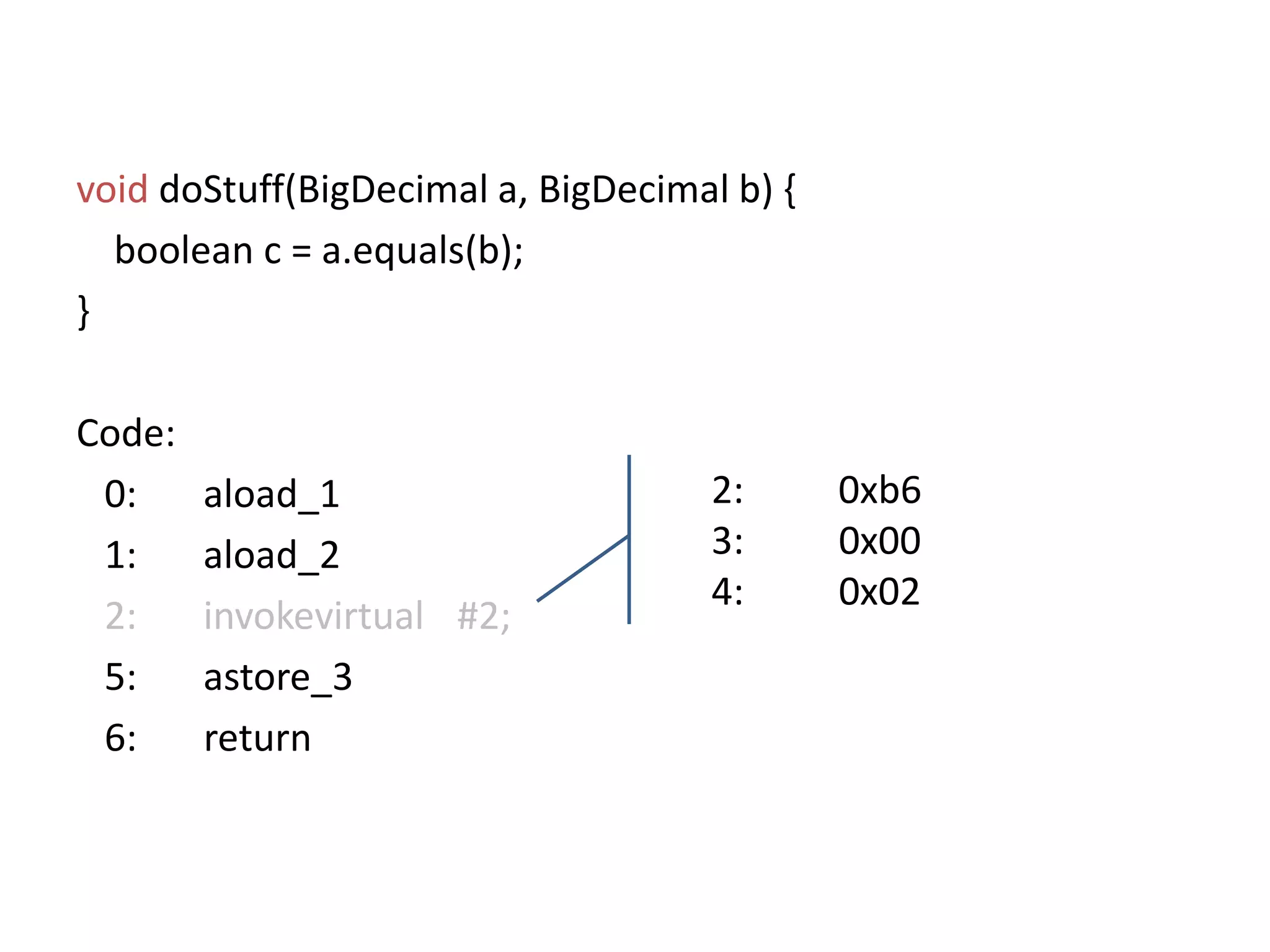
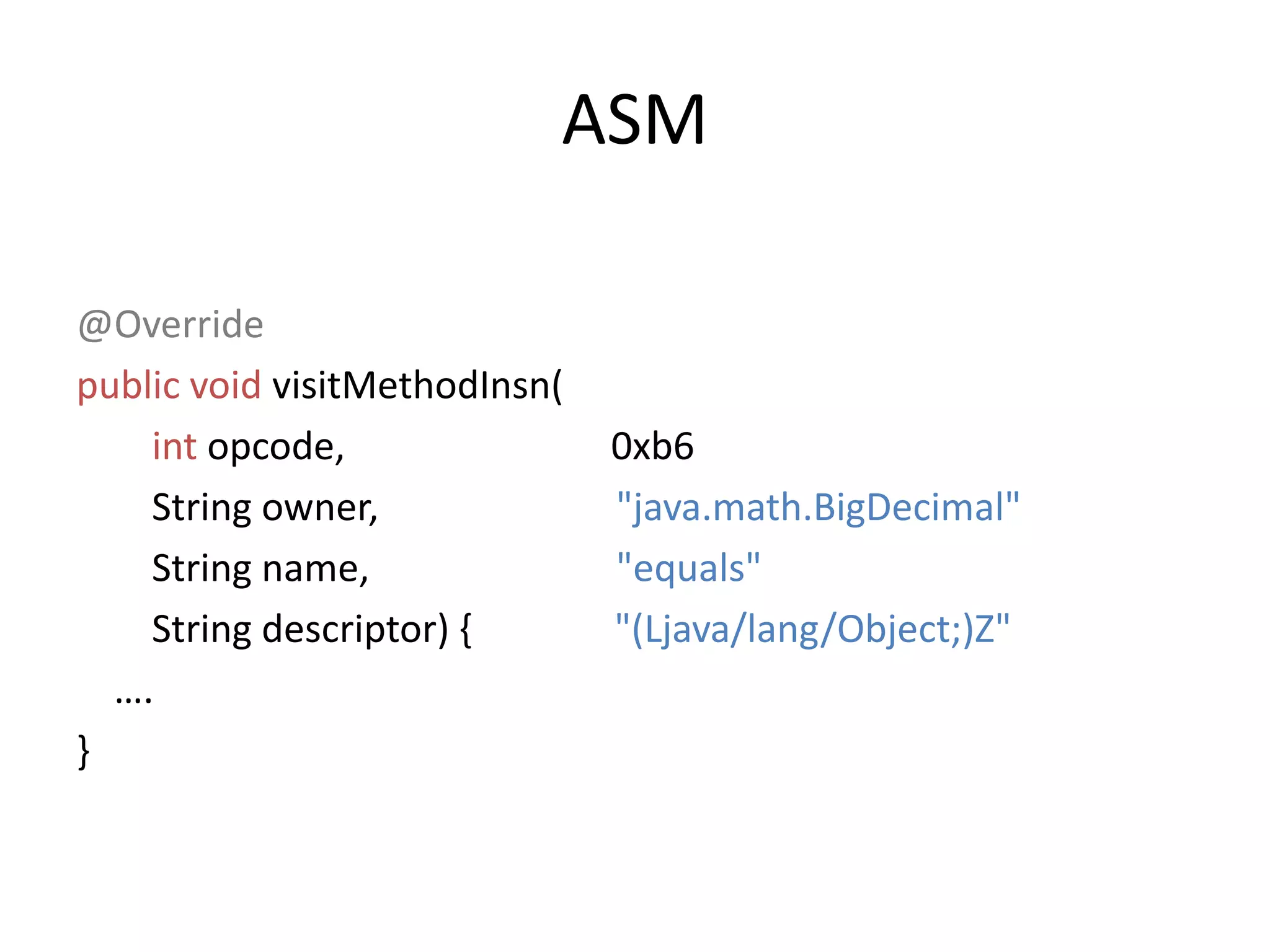
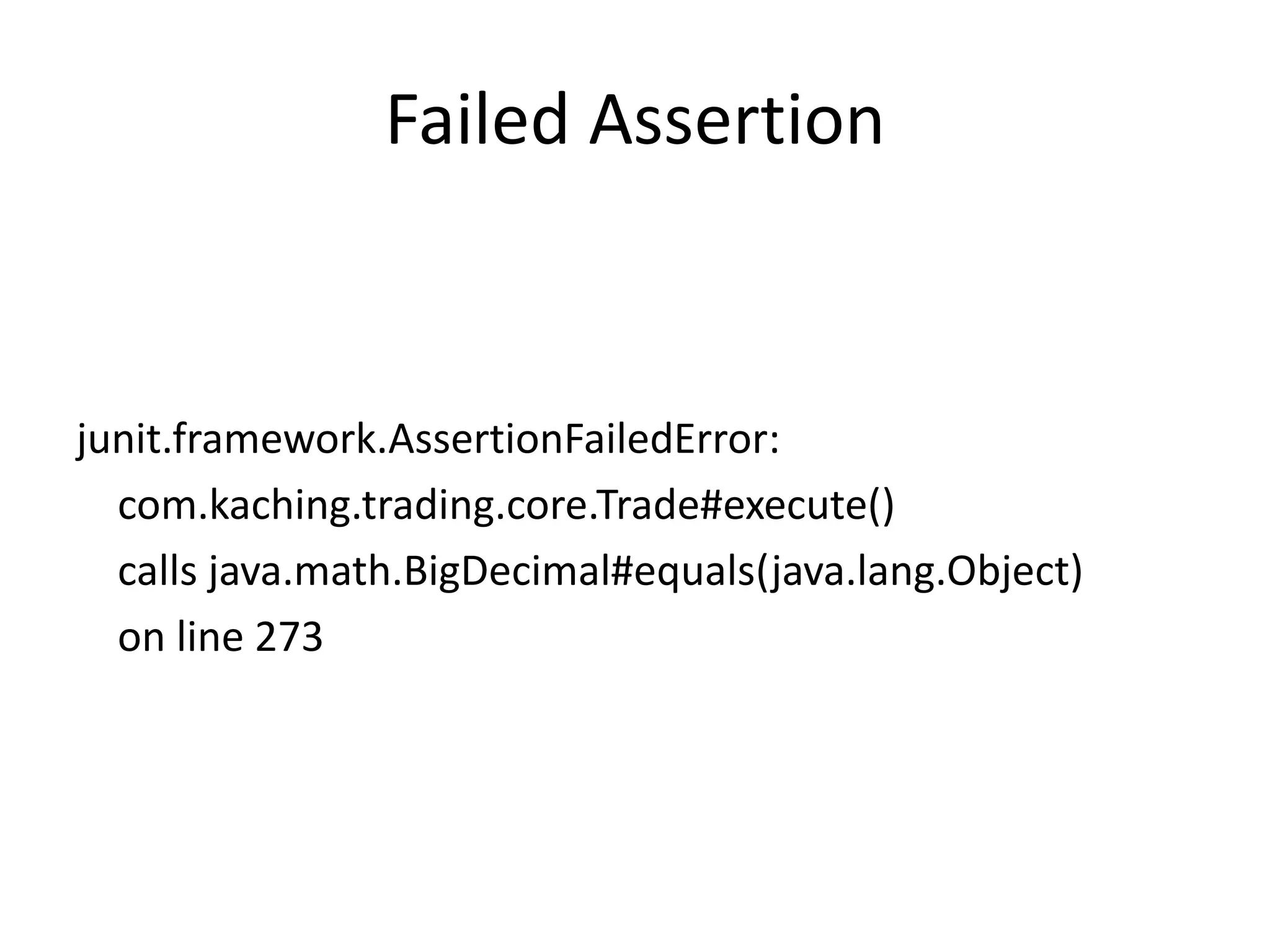
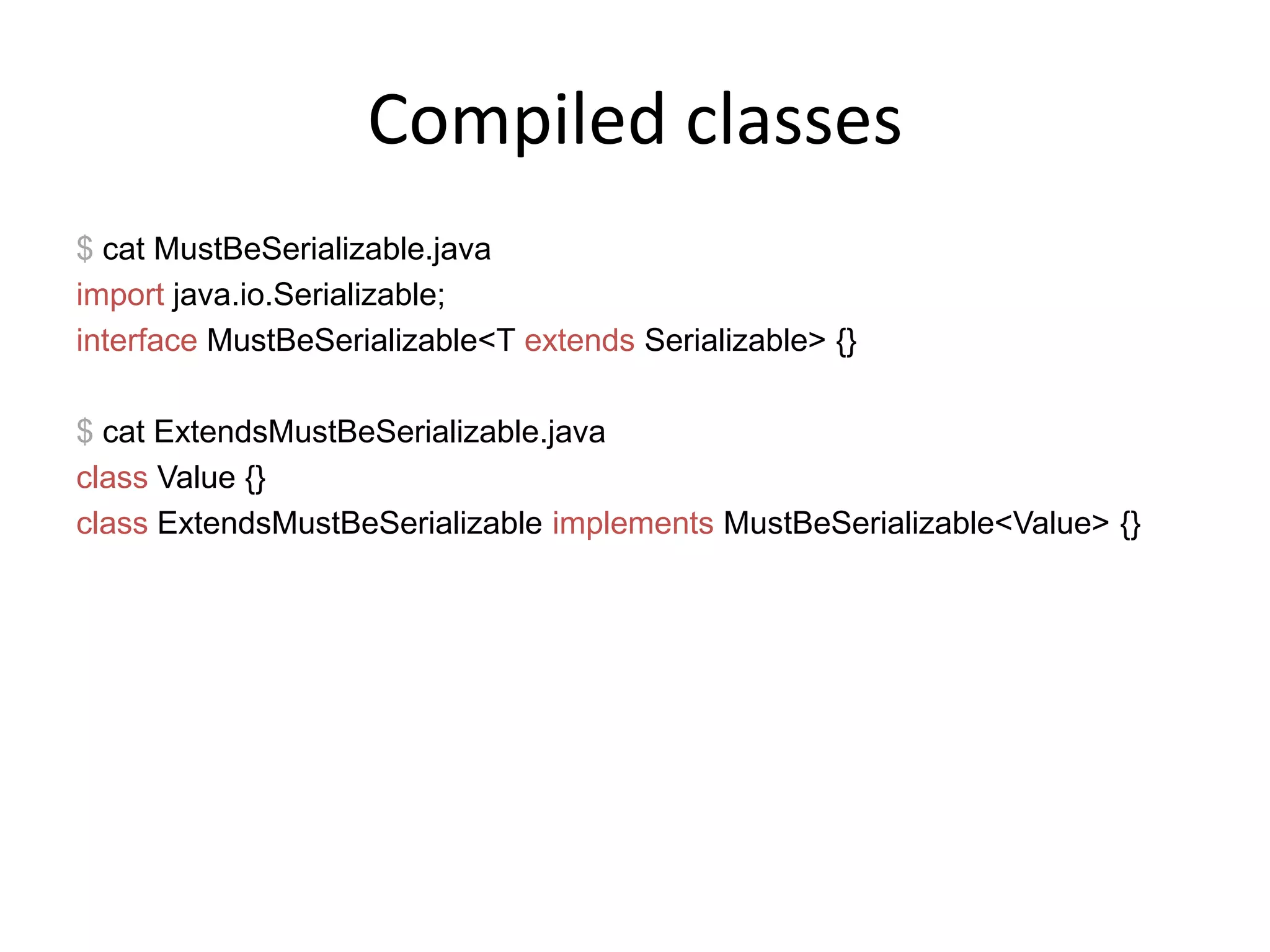
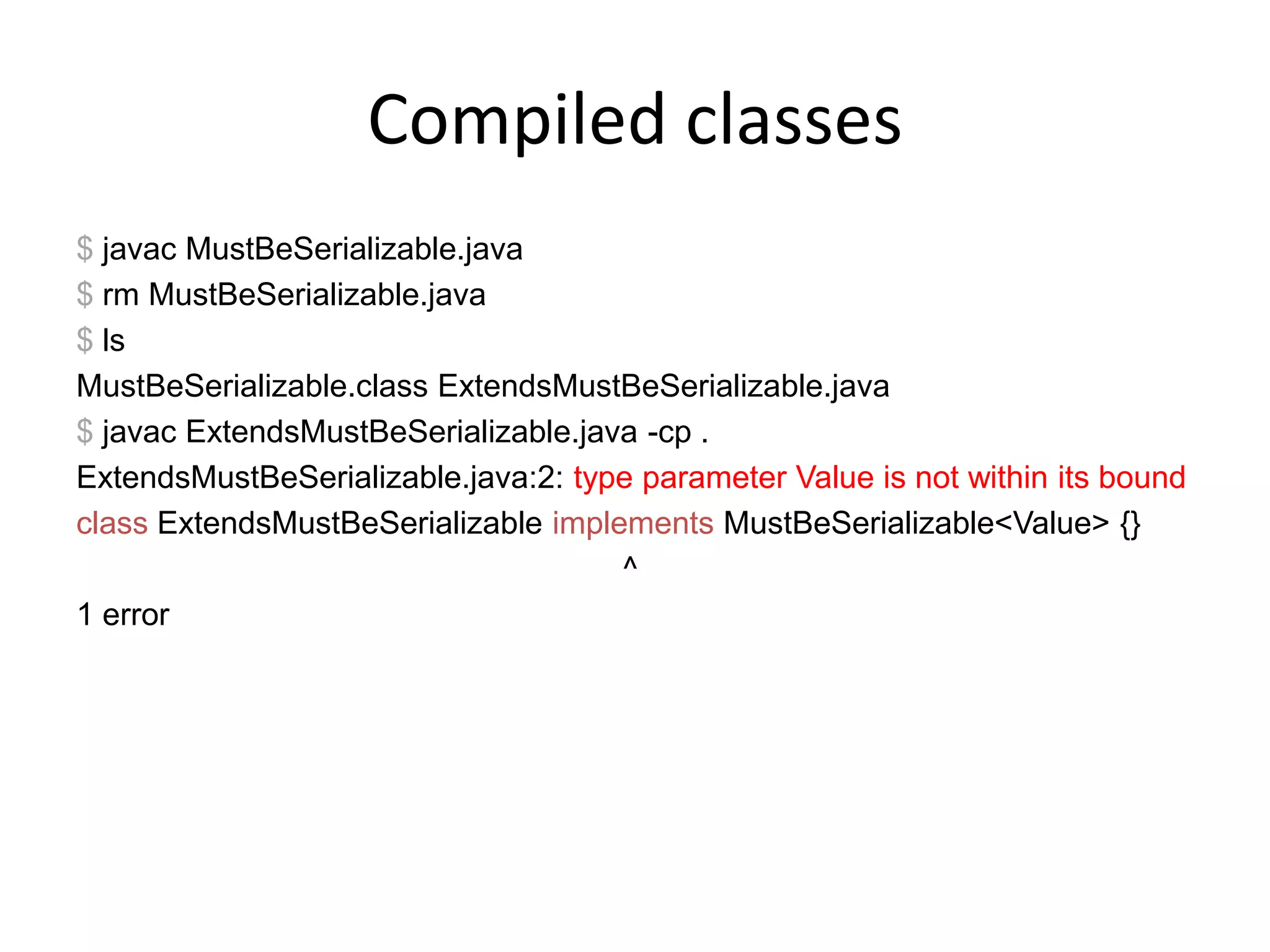
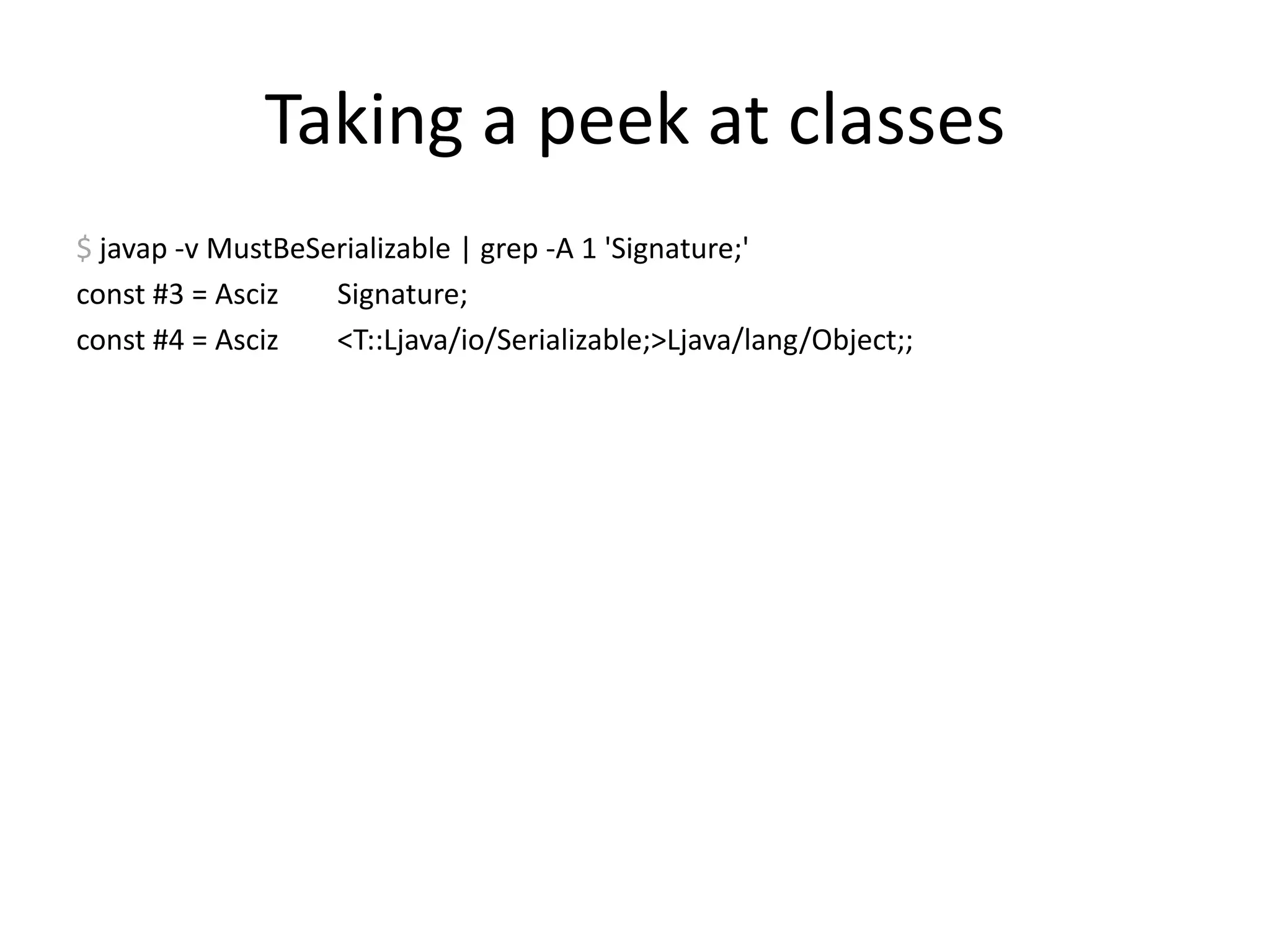
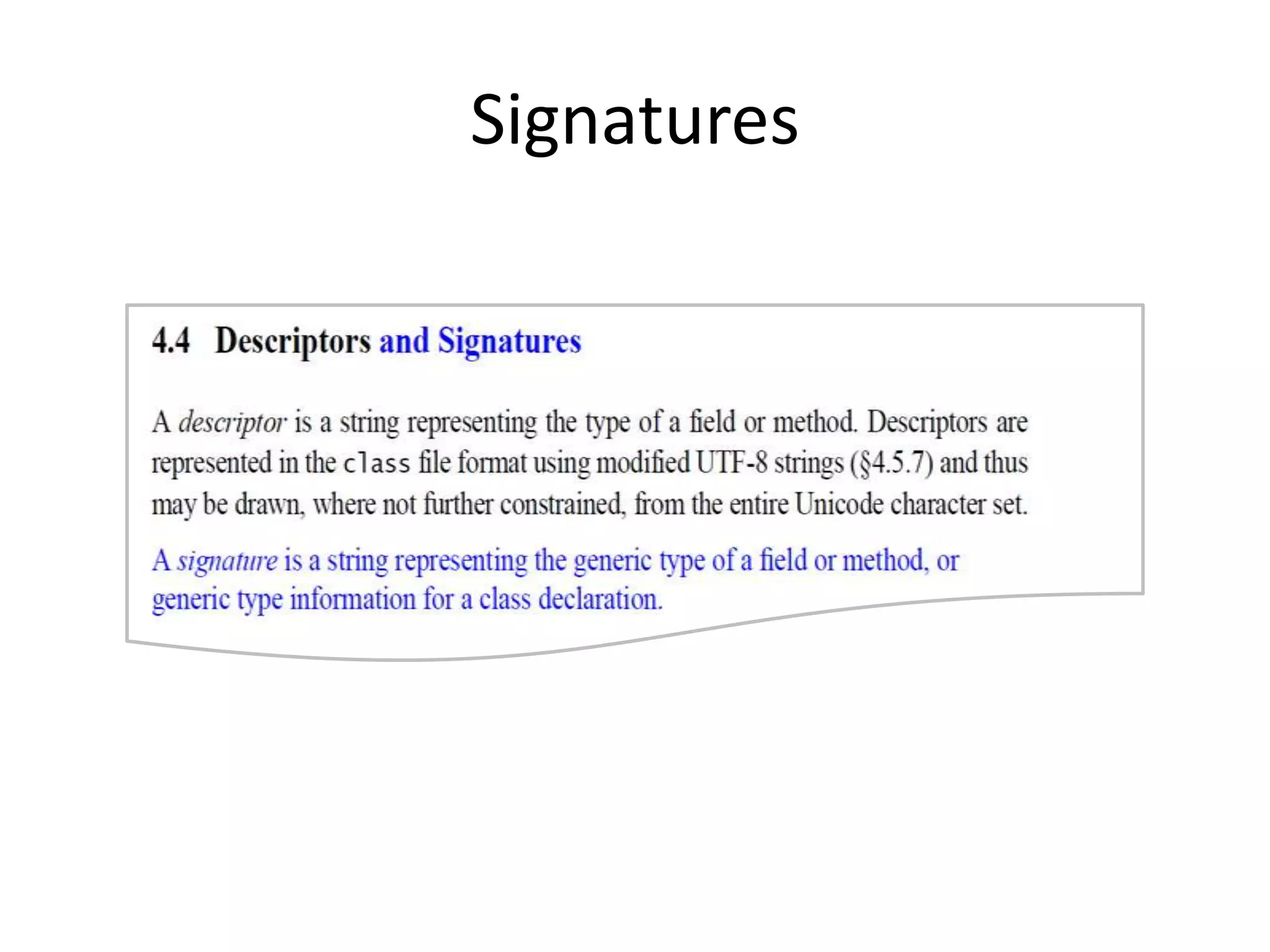
The document discusses applying compiler techniques to improve software development efficiency, including rapid testing and deployment. It details the anatomy of a compiler and various analyses to catch coding mistakes, such as syntax and semantic errors via abstract syntax trees and optimization methods. Practical code examples and references to tools used for static code analysis and type safety in Java are also provided.
![ClassFile { u4 magic; u2 minor_version; u2 major_version; u2 constant_pool_count;cp_infoconstant_pool[constant_pool_count-1]; u2 access_flags; u2 this_class; u2 super_class; u2 interfaces_count; u2 interfaces[interfaces_count]; u2 fields_count;field_infofields[fields_count]; u2 methods_count;method_infomethods[methods_count]; u2 attributes_count;attribute_infoattributes[attributes_count];}](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-30-2048.jpg)
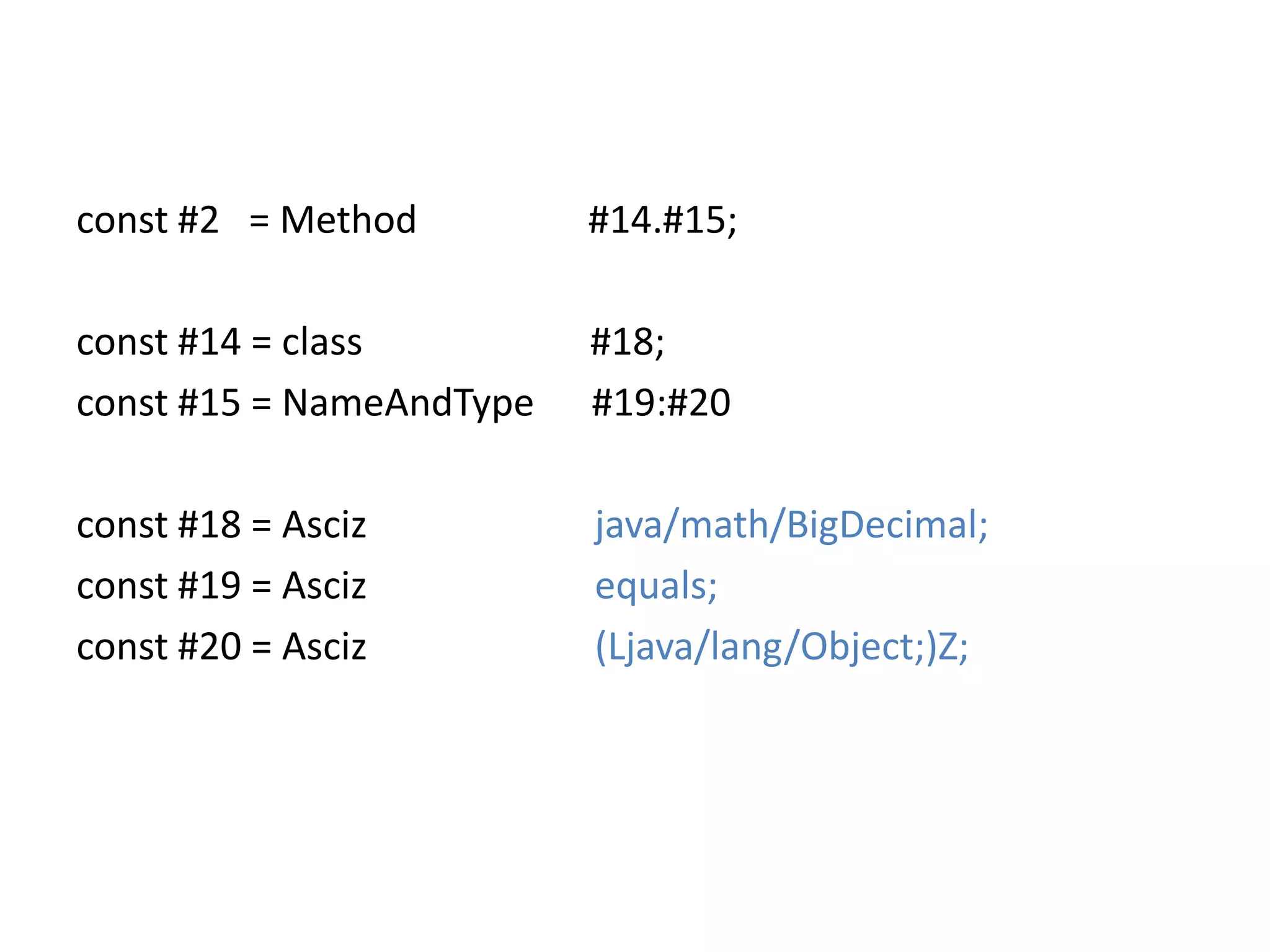
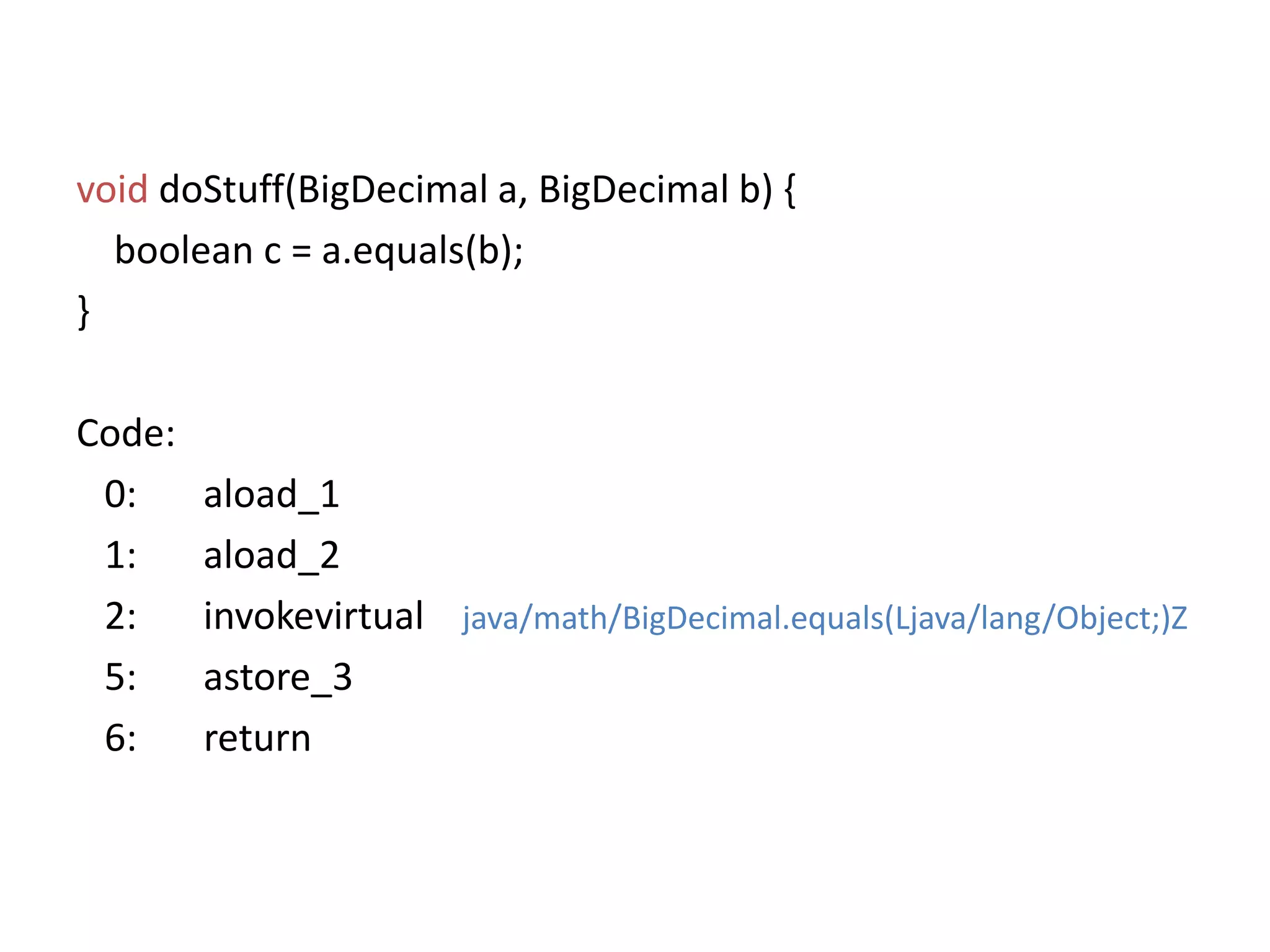
![ClassFile { u4 magic; u2 minor_version; u2 major_version; u2 constant_pool_count;cp_infoconstant_pool[constant_pool_count-1];u2 access_flags; u2 this_class; u2 super_class; u2 interfaces_count; u2 interfaces[interfaces_count]; u2 fields_count;field_infofields[fields_count]; u2 methods_count;method_infomethods[methods_count]; u2 attributes_count;attribute_infoattributes[attributes_count];}const #18 = Ascizjava/math/BigDecimal;const #19 = Ascizequals;const #20 = Asciz(Ljava/lang/Object;)Z;](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-31-2048.jpg)
![ClassFile { u4 magic; u2 minor_version; u2 major_version; u2 constant_pool_count;cp_infoconstant_pool[constant_pool_count-1]; u2 access_flags; u2 this_class; u2 super_class; u2 interfaces_count; u2 interfaces[interfaces_count]; u2 fields_count;field_infofields[fields_count]; u2 methods_count;method_infomethods[methods_count];u2 attributes_count;attribute_infoattributes[attributes_count];}method_info { u2 access_flags; u2 name_index; u2 descriptor_index; u2 attributes_count;attribute_infoattributes[attributes_count];}](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-32-2048.jpg)
![method_info{ u2 access_flags; u2 name_index; u2 descriptor_index; u2 attributes_count;attribute_info attributes[attributes_count];}Code_attribute { u2 attribute_name_index; u4 attribute_length; u2 max_stack; u2 max_locals; u4 code_length; u1 code[code_length]; u2 exception_table_length; { u2 start_pc; u2 end_pc; u2 handler_pc; u2 catch_type; } exception_table[exception_table_length]; u2 attributes_count;attribute_infoattributes[attributes_count];}](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-33-2048.jpg)
![Code_attribute { u2 attribute_name_index; u4 attribute_length; u2 max_stack; u2 max_locals; u4 code_length; u1 code[code_length];u2 exception_table_length; { u2 start_pc; u2 end_pc; u2 handler_pc; u2 catch_type; } exception_table[exception_table_length]; u2 attributes_count;attribute_info attributes[attributes_count];} 0: aload_11: aload_22: invokevirtual #2;5: astore_36: return](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-34-2048.jpg)

![SignaturesPrimitivesB for byte, C for char, D for double, …ObjectsLclassname; such as Ljava/lang/String;Arrays[B for byte[], [[D for double[][]VoidV… 8 pages of documentation](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-53-2048.jpg)
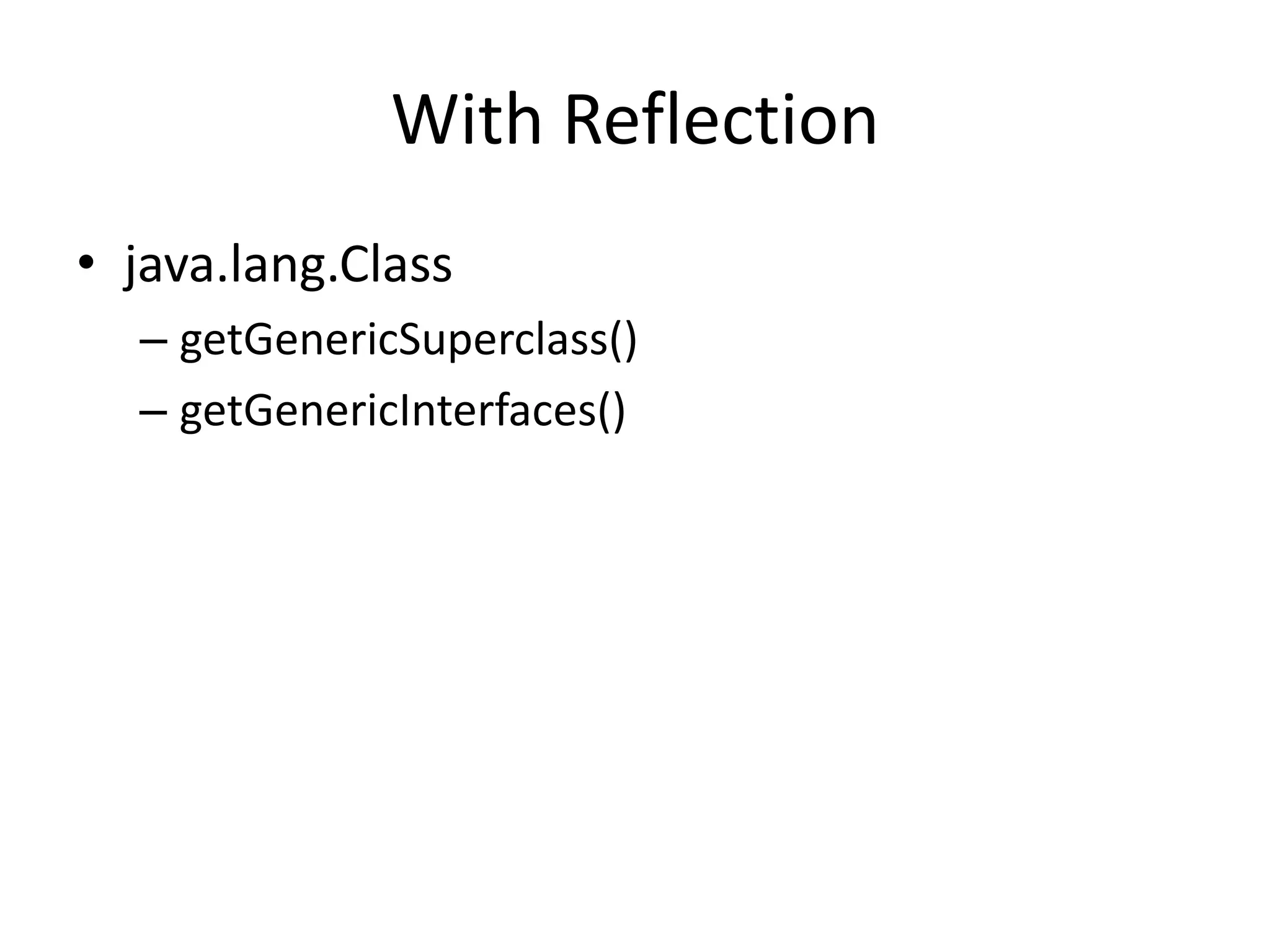
![With Reflectionjava.lang.reflect.TypeClassGenericArrayType(Type component)ParametrizedType(Type raw, Type[] arguments)TypeVariable(Type[] bounds, Sting name)WildcardType( Type[] lowerBounds, Type[] upperBounds)](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-55-2048.jpg)
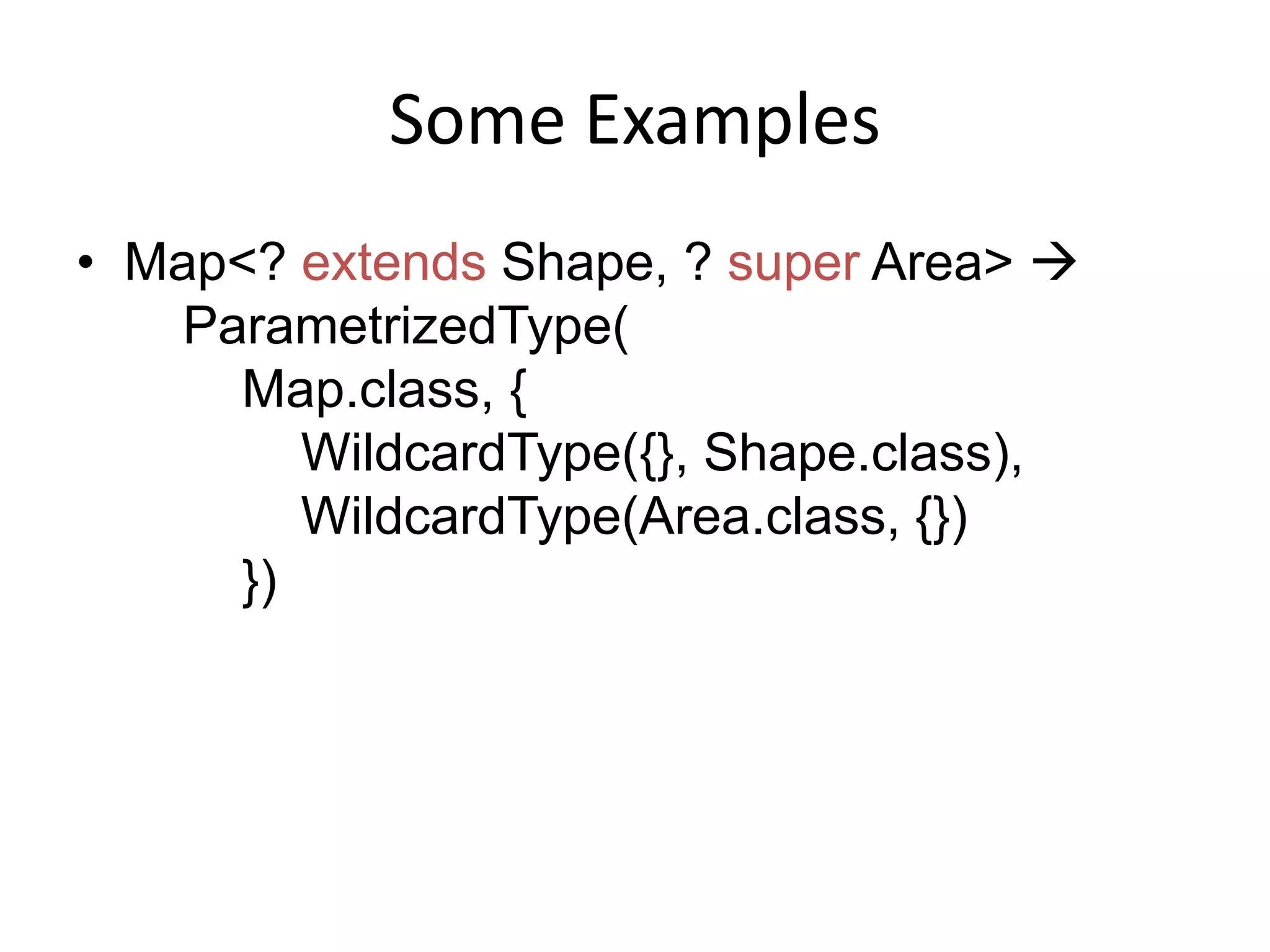
![Some ExamplesString.class Class<String>List<Integer> ParametrizedType(List.class, Integer.class)List<int[]> ParametrizedType(List.class, GenericArrayType(int.class))](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-56-2048.jpg)
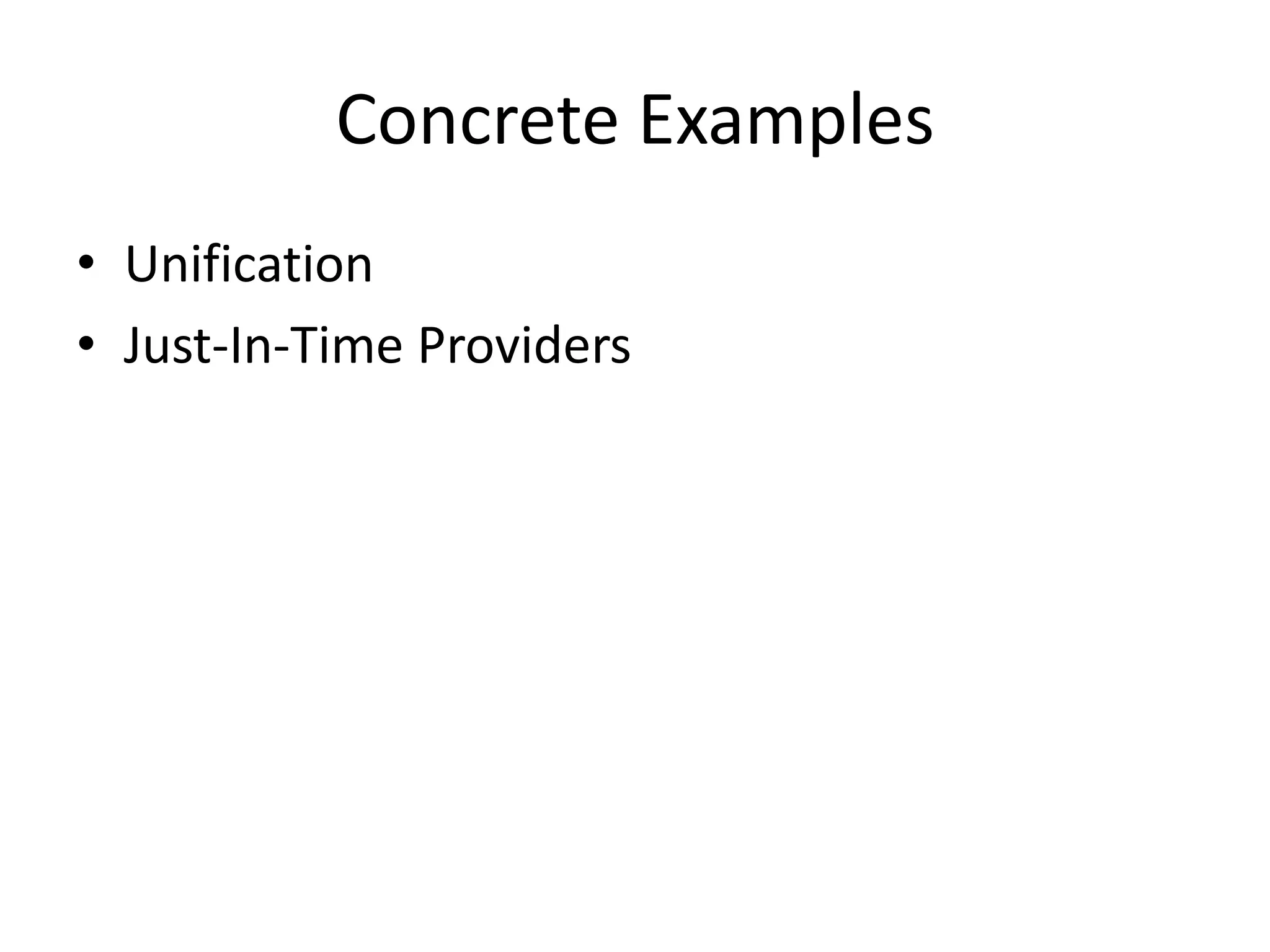
![UnificationMyClassimplements Callable<String> { …MyClass.class .getGenericInterfaces()[0] .getActualTypeArguments()[0] String.class!](https://image.slidesharecdn.com/slides-101010111117-phpapp02/75/Applying-Compiler-Techniques-to-Iterate-At-Blazing-Speed-60-2048.jpg)