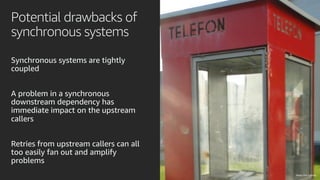
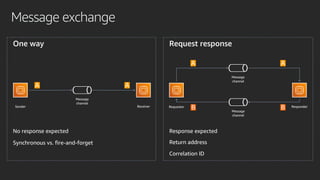
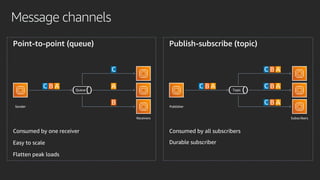
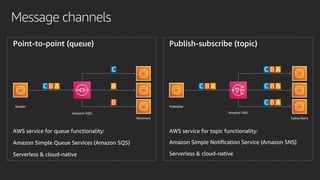
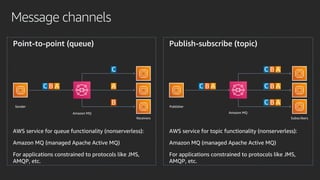
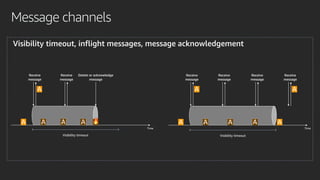
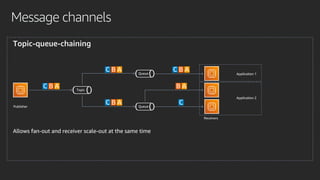
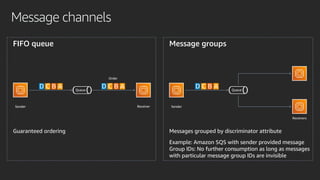
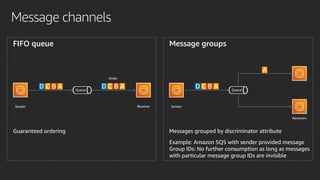
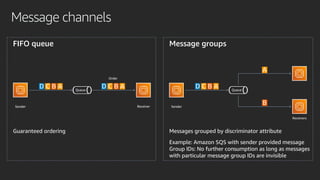
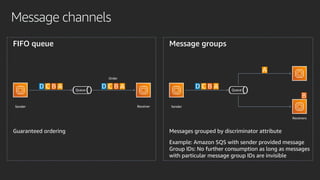
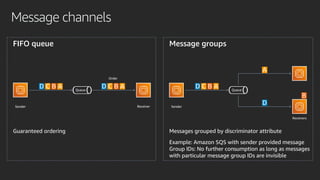
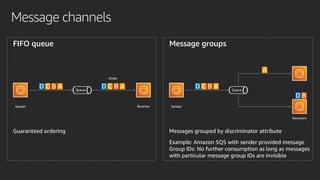
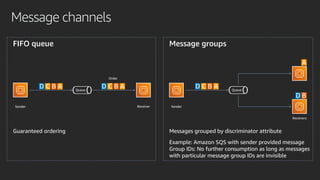
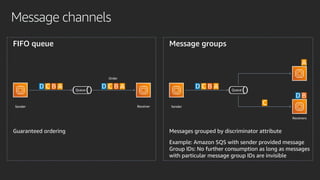
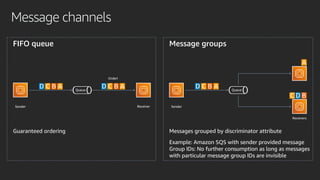
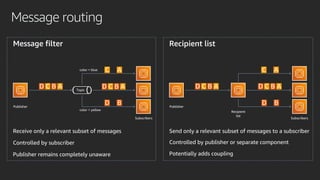
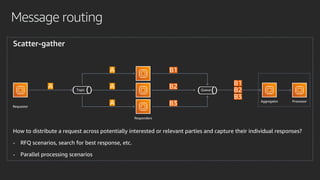
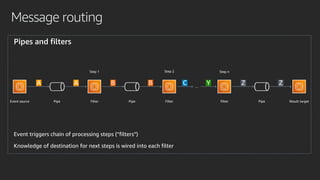
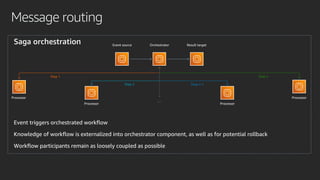
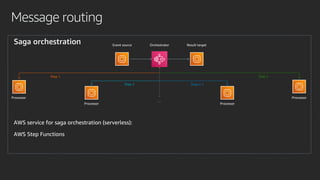
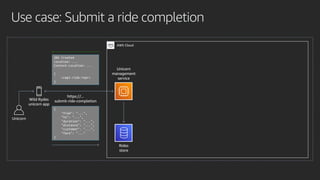
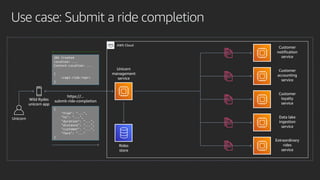
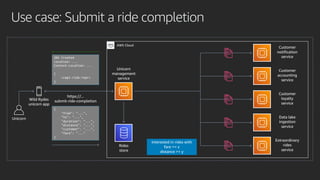
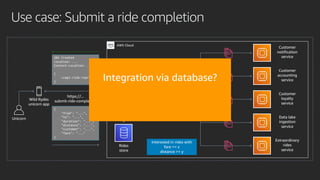
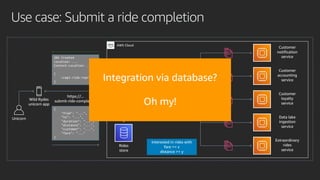
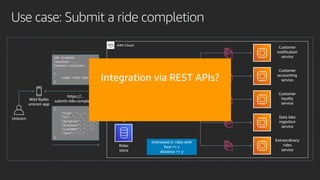
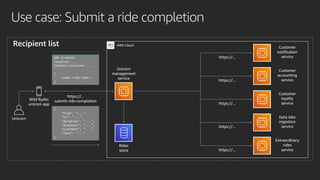
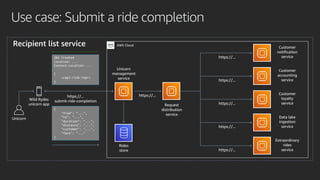
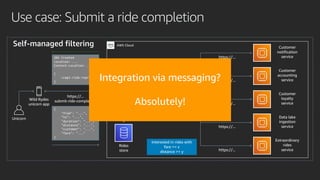
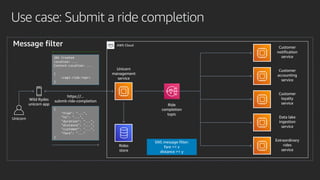
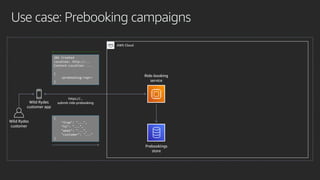
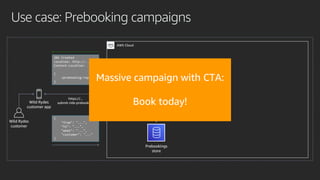
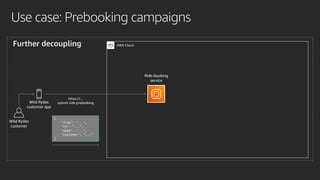
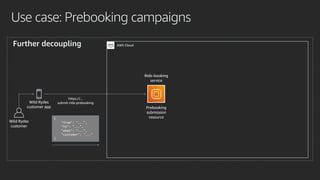
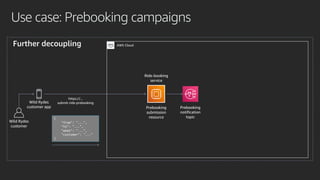
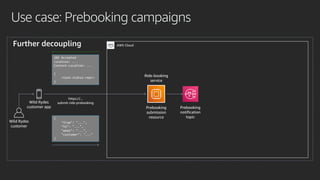
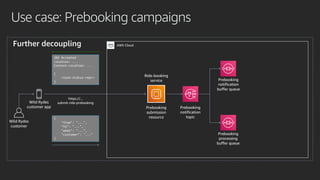
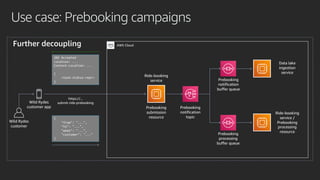
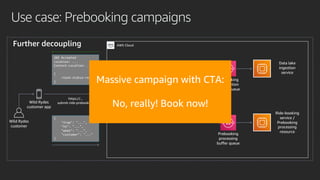
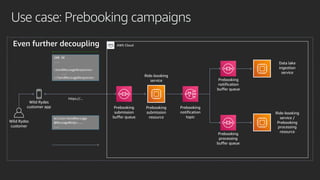
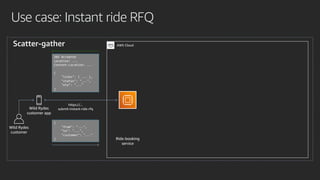
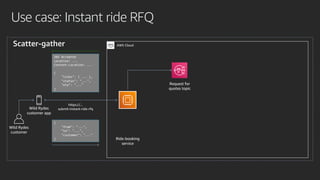
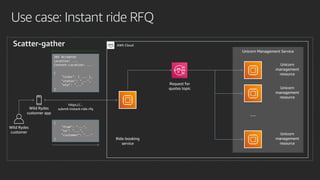
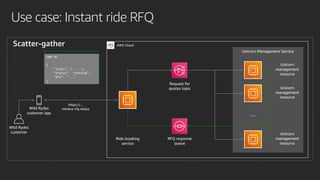
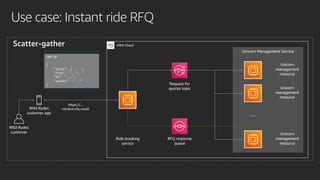
The document presents application integration patterns for microservices, highlighting key architectural principles such as 'divide and conquer' and 'loose coupling.' It discusses various message exchange methods and AWS services like SQS and SNS for queue and topic functionality, emphasizing the importance of messaging components in cloud-native architectures. Additionally, the document outlines use cases for integrating microservices and processes, focusing on scenarios like ride completions and prebooking campaigns.