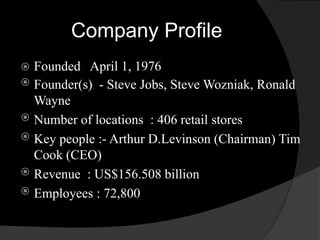
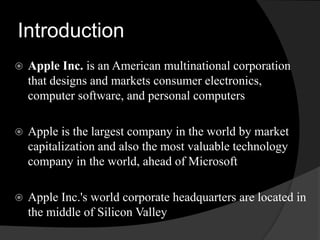
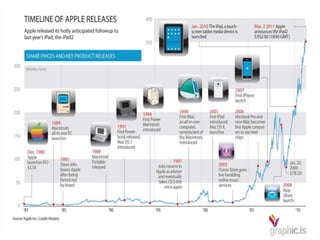
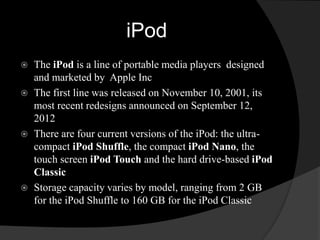
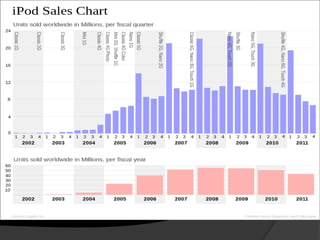
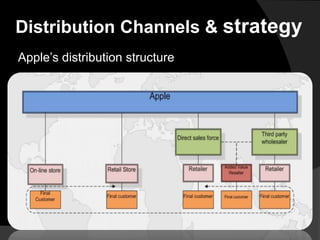
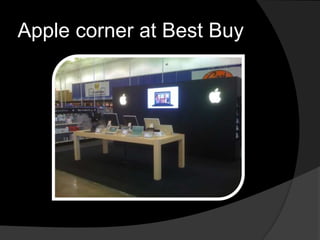
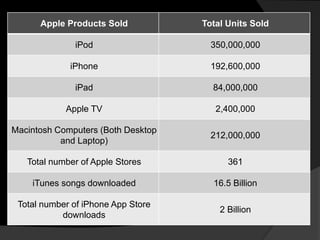
This document discusses Apple's corporate strategy and products from the iPod to the iPad. It provides an overview of Apple's history and products like the iPod and iPad. It also discusses Apple's distribution strategy through their retail and online stores. Finally, it analyzes Apple's strengths, weaknesses, opportunities, and threats through a SWOT analysis.




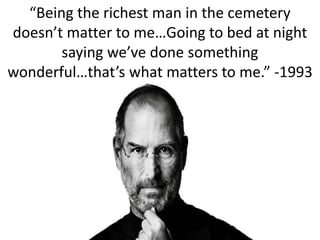
![“I mean, some people say, ‘Oh, God, if [Jobs] got
run over by a bus, Apple would be in trouble.’ And,
you know, I think it wouldn’t be a party, but there
are really capable people at Apple. My job is to
make the whole executive team good enough to be
successors, so that’s what I try to do.”](https://image.slidesharecdn.com/applecasestudy-140914235230-phpapp02/85/Apple-from-the-iPod-to-the-iPad-28-320.jpg)