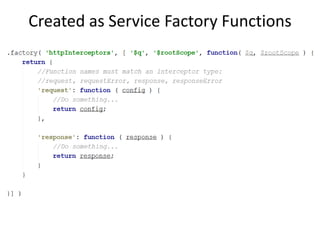
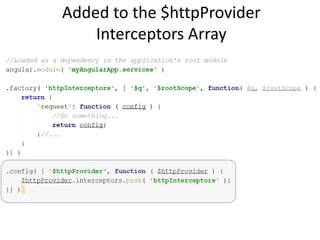
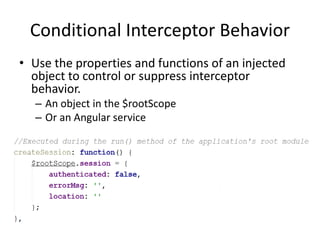
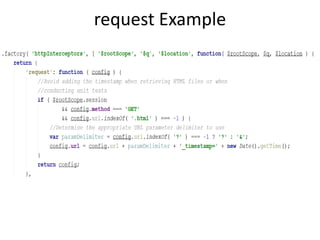
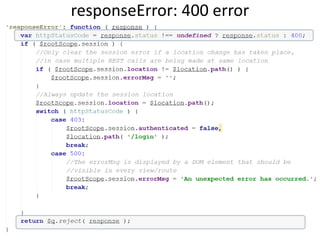
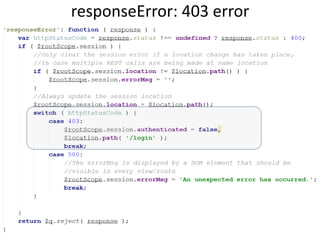
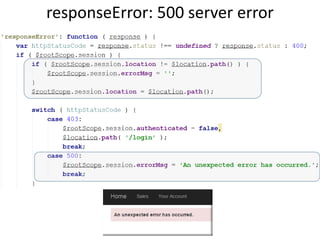
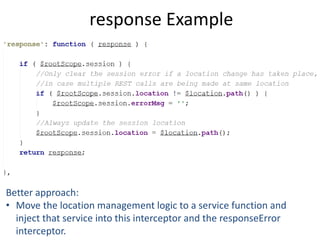
This document discusses AngularJS $http interceptors, which are event functions triggered during HTTP requests made with $http, $resource, and $httpBackend. There are four types of interceptors: request, requestError, response, and responseError. Interceptors are created as service factory functions and added to the $httpProvider interceptors array. They are useful for applying cross-cutting concerns like request configuration, response transformation, error handling, and authentication checks across an application. Interceptors can control their behavior conditionally based on injected services or objects. Examples demonstrate interceptors for request configuration, 400/403/500 error handling, and response processing.