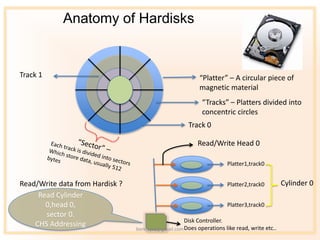
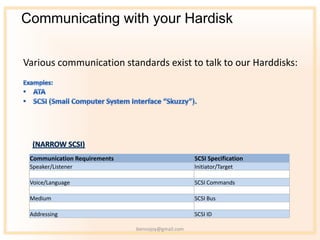
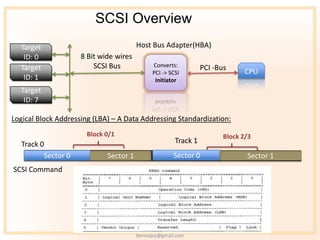
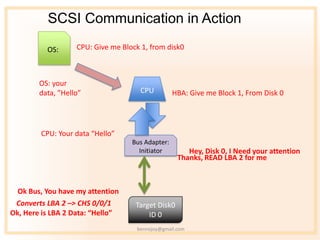
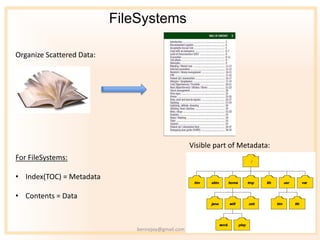
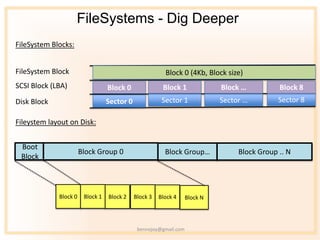
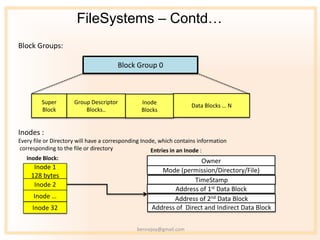
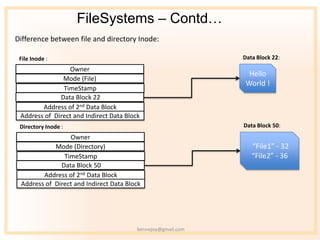
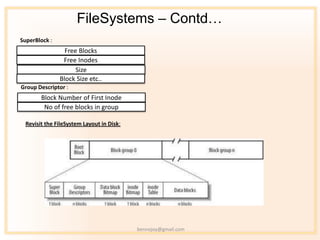
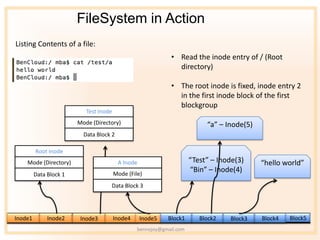
The document discusses the anatomy of file systems and how they are organized on hard disks. It explains that file systems organize scattered data using indexes containing metadata and data blocks containing file contents. File system blocks are mapped to disk blocks using logical block addressing. File systems use inodes to store file and directory metadata, with each file or directory having a corresponding inode containing attributes like owner, size, and pointers to data blocks. Block groups contain groups of inodes and data blocks to organize the file system layout on disk.