Embed presentation
Download as PDF, PPTX
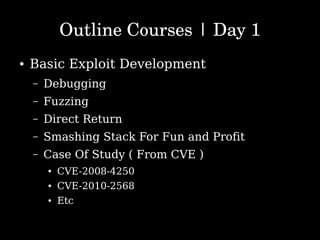
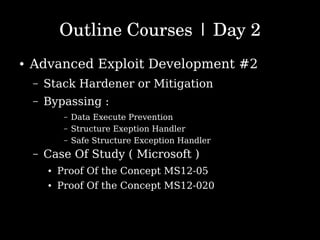
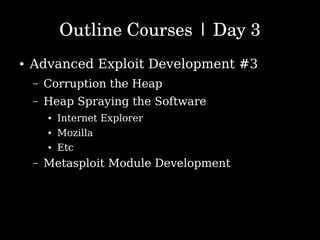


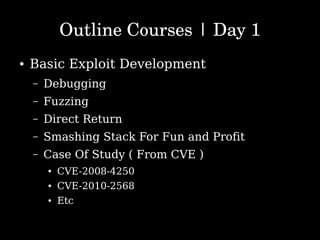
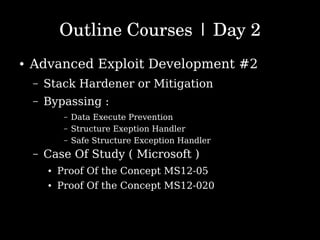
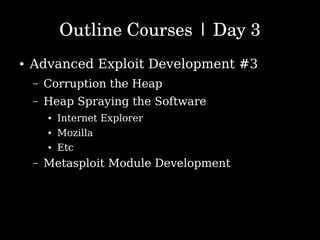
The document outlines a training session led by Danang Heriyadi on advanced exploit development over four days. Topics include basic and advanced techniques such as debugging, fuzzing, stack manipulation, mitigation strategies, and shellcode development, with case studies from various CVEs. The course is aimed at enhancing skills related to exploit development and vulnerability reporting.