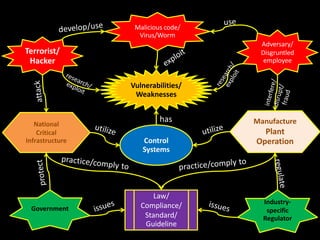
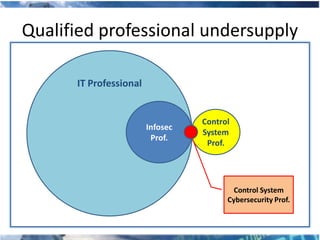
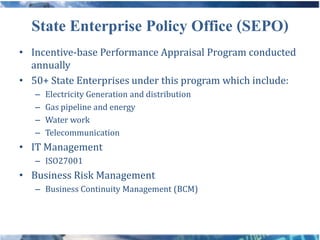
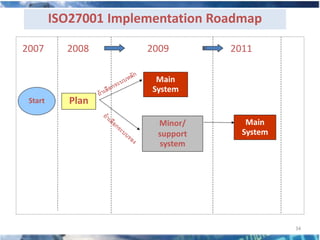
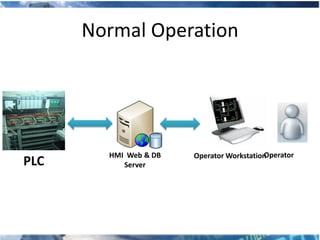
The document discusses addressing critical infrastructure protection (CIP) in Thailand and challenges associated with CIP where it is not regulated, including limited security professionals and low awareness among stakeholders. It provides examples of how Thailand has worked to raise CIP awareness through training and introducing ISO 27001, and notes that more remains to be done to address the challenges. The speaker is the chief security officer of a Thai company who has contributed to cybersecurity efforts in Thailand.

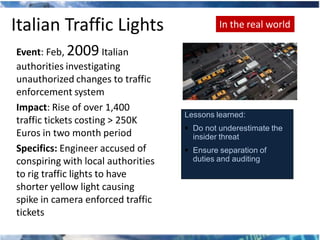
![Transportation – Road Signs In the real world
Event: Jan 2009, Texas road
signs compromised
Impact: Motorists distracted and
provided false information
Specifics: Some commercial road
signs can be easily altered because
their instrument panels are frequently
Lessons learned:
left unlocked and their default
Use robust physical access passwords are not changed.
controls
"Programming is as simple as
Change all default passwords scrolling down the menu selection," a
Work with manufacturers to blog reports. "Type whatever you want
identify and protect password to display … In all likelihood, the crew
reset procedures will not have changed [the password]."
8](https://image.slidesharecdn.com/addressing-cip-1280332172-phpapp01/85/Addressing-CIP-8-320.jpg)