Adapting IT Operations with CompTIA Cloud+
•
0 likes•153 views
In this document: - Adapting IT Operations with CompTIA Cloud+ - Measuring CompTIA Cloud+ Difficulty - Why Hybrid Testing Approaches Work Best - Mapping the NICE Cybersecurity Workforce Framework
Report
Share
Report
Share
Download to read offline
Recommended
Meeting the Cybersecurity Skills Challenge with CompTIA Security+

In this document:
- Meeting the Cybersecurity Skills Challenge with CompTIA Security+
- Measuring CompTIA Security+ Difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Keeping the World Connected with CompTIA Network+

In this document:
- Keeping the World Connected with CompTIA Network+
- Measuring CompTIA Network+ Difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Closing the Gap for Advanced Enterprise Cybersecurity Skills with CompTIA Adv...

- Closing the Gap for Advanced Enterprise Cybersecurity Skills with CompTIA Advanced Security Practitioner (CASP)
- Measuring CASP difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Meeting Today’s IT Support Challenges with CompTIA A+

This document discusses CompTIA A+ certification and its role in validating the skills needed by today's IT professionals. It addresses the increased diversity of knowledge and skills required to support modern heterogeneous technology environments. The certification covers topics like troubleshooting, networking, security, operating systems and hardware. It emphasizes applying these skills over simple recall of information, with 79% of exam objectives requiring analysis or application of knowledge. The document advocates for a hybrid testing approach that includes both knowledge-based and performance-based questions. It provides an example mapping of the certification objectives to the National Initiative for Cybersecurity Education Framework.
CISA Domain 3 - Information Systems Acquisition, Development and Implementation

The document discusses key concepts relating to CISA Domain 3 on information systems acquisition, development, and implementation. It covers 14 knowledge statements, including benefits realization practices, project governance mechanisms, requirements analysis and management practices, system development methodologies and tools, and post-implementation review objectives and practices. The document also summarizes important concepts for the exam such as project portfolio management, business case development, benefit realization techniques, project management structure, project communication and culture, and defining project objectives using an object breakdown structure and work breakdown structure.
CISA Domain 4 Information Systems Operation | Infosectrain

Study Flashcards On CISA Domain 4 Information Systems Operations, Maintenance and Support at Cram.com. Quickly memorize the terms, phrases and much more. Infosectrain.com makes it easy to get the grade you want!
Software Reliability and Quality Assurance Challenges in Cyber Physical Syste...

Software Reliability is the probability of failure-free software operation for a specified period of time in a specified environment. Cyber threats on software security have been prevailing and have increased exponentially, posing a major challenge on software reliability in the cyber physical systems (CPS) environment. Applying patches after the software has been developed is outdated and a major security flaw. However, this has posed a major software reliability challenge as threat actors are exploiting unpatched and insecure software configuration vulnerabilities that are not identified at the design phase. This paper aims to investigate the SDLC approach to software reliability and quality assurance challenges in CPS security. To demonstrate the applicability of our work, we review existing security requirements engineering concepts and methodologies such as TROPOS, I*, KAOS, Tropos and Secure Tropos to determine their relevance in software security. We consider how the methodologies and function points are used to implement constraints to improve software reliability. Finally, the function points concepts are implemented into the CPS security components. The results show that software security threats in CPS can be addressed by integrating the SRE approach and function point analysis in the development to improve software reliability.
PTX12_Presentation_George Delikouras AIA

The document outlines a framework for developing an information security strategy and proposal for an organization. It recommends taking a top-down approach by first identifying the key sectors of people, processes, and technology and then drilling down to specific domains and technologies within each sector. It provides examples of domains such as identity and access management or network security. The framework is meant to help information security officers understand needs, prioritize investments, and develop a proposal to present to top management to obtain approval and funding for security initiatives.
Recommended
Meeting the Cybersecurity Skills Challenge with CompTIA Security+

In this document:
- Meeting the Cybersecurity Skills Challenge with CompTIA Security+
- Measuring CompTIA Security+ Difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Keeping the World Connected with CompTIA Network+

In this document:
- Keeping the World Connected with CompTIA Network+
- Measuring CompTIA Network+ Difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Closing the Gap for Advanced Enterprise Cybersecurity Skills with CompTIA Adv...

- Closing the Gap for Advanced Enterprise Cybersecurity Skills with CompTIA Advanced Security Practitioner (CASP)
- Measuring CASP difficulty
- Why Hybrid Testing Approaches Work Best
- Mapping the NICE Cybersecurity Workforce Framework
Meeting Today’s IT Support Challenges with CompTIA A+

This document discusses CompTIA A+ certification and its role in validating the skills needed by today's IT professionals. It addresses the increased diversity of knowledge and skills required to support modern heterogeneous technology environments. The certification covers topics like troubleshooting, networking, security, operating systems and hardware. It emphasizes applying these skills over simple recall of information, with 79% of exam objectives requiring analysis or application of knowledge. The document advocates for a hybrid testing approach that includes both knowledge-based and performance-based questions. It provides an example mapping of the certification objectives to the National Initiative for Cybersecurity Education Framework.
CISA Domain 3 - Information Systems Acquisition, Development and Implementation

The document discusses key concepts relating to CISA Domain 3 on information systems acquisition, development, and implementation. It covers 14 knowledge statements, including benefits realization practices, project governance mechanisms, requirements analysis and management practices, system development methodologies and tools, and post-implementation review objectives and practices. The document also summarizes important concepts for the exam such as project portfolio management, business case development, benefit realization techniques, project management structure, project communication and culture, and defining project objectives using an object breakdown structure and work breakdown structure.
CISA Domain 4 Information Systems Operation | Infosectrain

Study Flashcards On CISA Domain 4 Information Systems Operations, Maintenance and Support at Cram.com. Quickly memorize the terms, phrases and much more. Infosectrain.com makes it easy to get the grade you want!
Software Reliability and Quality Assurance Challenges in Cyber Physical Syste...

Software Reliability is the probability of failure-free software operation for a specified period of time in a specified environment. Cyber threats on software security have been prevailing and have increased exponentially, posing a major challenge on software reliability in the cyber physical systems (CPS) environment. Applying patches after the software has been developed is outdated and a major security flaw. However, this has posed a major software reliability challenge as threat actors are exploiting unpatched and insecure software configuration vulnerabilities that are not identified at the design phase. This paper aims to investigate the SDLC approach to software reliability and quality assurance challenges in CPS security. To demonstrate the applicability of our work, we review existing security requirements engineering concepts and methodologies such as TROPOS, I*, KAOS, Tropos and Secure Tropos to determine their relevance in software security. We consider how the methodologies and function points are used to implement constraints to improve software reliability. Finally, the function points concepts are implemented into the CPS security components. The results show that software security threats in CPS can be addressed by integrating the SRE approach and function point analysis in the development to improve software reliability.
PTX12_Presentation_George Delikouras AIA

The document outlines a framework for developing an information security strategy and proposal for an organization. It recommends taking a top-down approach by first identifying the key sectors of people, processes, and technology and then drilling down to specific domains and technologies within each sector. It provides examples of domains such as identity and access management or network security. The framework is meant to help information security officers understand needs, prioritize investments, and develop a proposal to present to top management to obtain approval and funding for security initiatives.
Hands on IT risk assessment

This document outlines a risk assessment methodology for organizations. It discusses how risk assessments are often not implemented formally or do not provide practical advice. The presented method uses foundation documents, risk evaluation criteria, and a multi-round review process called the Delphic Technique to provide a standardized risk assessment. It recommends developing reusable templates, defining assessment scope and objectives, using the methodology to identify and evaluate risks, and creating formal treatment plans. Time is included as a variable to show changing risks over time. The goal is for assessments to identify practical risk reduction options.
Xevgenis_Michail_CI7130 Network and Information Security

- The document discusses a security assessment of an organization that provides secure data storage for clients. It outlines the organization's key assets including proper system operation, data security, software, hardware, and employees.
- An analysis team is formed to conduct the security assessment using the OCTAVE framework. The team includes specialists in networking, IT, human resources, security, and business.
- The assessment will identify vulnerabilities and develop security strategies to mitigate risks to the organization's reputation, data protection, availability, and proper operation. Countermeasures proposed will focus on improving the organization's defensive capabilities.
Engineering Software Products: 4. software architecture

Introduces architectural design for software products. Covers architectural models including the MVC model and technology choices.
Pev program criteria training 2020 21

This document provides training for program evaluators (PEVs) on evaluating electrical, computer, communications, and similarly named engineering programs. It contains two sections:
1. Training on the program criteria for programs where IEEE contributes PEVs. This includes reviewing the current program criteria and discussing common shortcomings from previous visits.
2. Information to help PEVs understand upcoming changes to the general ABET criteria that will be effective for visits in fall 2019.
The document reviews the relevant program criteria, provides examples of case studies for PEVs to evaluate, and defines key terms like deficiencies and weaknesses. It aims to equip both new and experienced PEVs with the information needed to properly evaluate programs according to
Pev training 2019 2020

This case study involves an IEEE PEV evaluating a Computer and Software Engineering department that offers separate degree programs in Computer Engineering and Software Engineering. The Computer Engineering program emphasizes hardware design while exposing students to some software topics. The Software Engineering program emphasizes software design. Students from both programs collaborate on senior design projects, with Computer Engineering students focusing more on hardware and Software Engineering students focusing more on software. The case study concludes that the program meets requirements, as Computer Engineering students are knowledgeable in software topics and Software Engineering students can analyze, design, verify, validate, implement, apply and maintain software systems as required by their program criteria.
CISA Domain 1 The Process On AUDITING INFORMATION SYSTEMS

ISACA IS Audit and Assurance Standards, Guidelines, and Tools & Techniques, Code of Professional Ethics & other applicable standard.
https://www.infosectrain.com/blog/cisa-domain-1-part-3-the-process-on-auditing-information-systems/
Program criteria-training 2018-19

The program being evaluated is officially named "Computer and Software Engineering" and offers both computer engineering and software engineering options. While the department head suggested using the electrical/computer/communications criteria since it was used previously, the correct approach is to use both the electrical/computer criteria and the software engineering criteria, as the program contains elements of both and the PEV must be qualified to evaluate both types of programs.
Tamara M Hayajneh

Tamara Hayajneh is a senior information security analyst with over 5 years of experience in network and security fields. She currently works at IT Security Training & Solutions, where her responsibilities include real-time security monitoring, investigating incidents, and managing a security operations center. She previously worked as a network engineer and technical support engineer. Her education includes a bachelor's degree in communication engineering and various security certifications. She is skilled in SIEM solutions, firewall management, and security analysis.
A deployment scenario a taxonomy mapping and keyword searching for the appl...

This document discusses developing a taxonomy to map relationships between applications, virtual machines, hosts, and clients when performing upgrades and patches. It proposes creating a taxonomy based on analyzing errors that occur during application execution to understand dependencies. The taxonomy would classify applications based on their libraries, operating systems, and browsers to provide a troubleshooting guideline for upgrades. An experiment upgrading an application called Crawling encountered errors due to dependencies on older software versions. Mapping the application criteria and relationships in a taxonomy could help identify the root cause of issues and the steps to resolve them.
Secured cloud support for global software

This document summarizes a research paper that proposes a methodology called TSPS (Theory/SWEBOK/Project Security) to improve software engineering education. The methodology aims to collaborate between academic and industrial practices. It involves students working on projects with guidance from both mentors and industry practitioners. Data from literature reviews on software security engineering education is analyzed. A cloud-based system is developed to securely store project documents by encrypting and splitting files across multiple cloud nodes. The methodology and secure cloud storage approach are concluded to provide strategies to mitigate risks in software projects and benefit both education and industry.
Validation of early testing method for e government projects by requirement ...

The document describes a validation study of an Early Requirement Testing Method (ERTM) for e-government projects. Test engineers used the ERTM, which involves reviewing requirements documents and providing feedback, on six e-government projects. The number of defects found before and after applying the ERTM and providing interventions was compared using a statistical test. The results showed that overall, there was a statistically significant reduction in the number of defects found after applying the ERTM, suggesting it is useful for improving requirements documentation. However, one project saw an increase in defects due to additional requirements added later in the project.
Ch7

The document discusses the design and implementation process in software engineering. It covers topics like using the Unified Modeling Language (UML) for object-oriented design, design patterns, and implementation issues. It then discusses the design process, including identifying system contexts and interactions, architectural design, identifying object classes, and creating design models like subsystem, sequence, and state diagrams. The example of designing a weather station system is used to illustrate these design concepts and activities.
Ian Sommerville, Software Engineering, 9th Edition Ch 4

The document discusses requirements engineering and summarizes key topics covered in Chapter 4, including:
- The importance of specifying both functional and non-functional requirements. Non-functional requirements place constraints on system functions and development process.
- The software requirements specification document defines what the system must do and includes both user and system requirements. It should not describe how the system will be implemented.
- Requirements engineering involves eliciting, analyzing, validating and managing requirements throughout the development lifecycle. Precise, complete and consistent requirements are important for development.
Chapter 05 developing_the_security_program

The document discusses developing an information security program, including training methods and project planning tools. It provides examples of true/false questions about security program elements like the security education, training, and awareness program and work breakdown structure. Key aspects covered include the purpose of SETA to reduce accidental breaches, training methods like one-on-one and formal classes, and that the WBS documents minimum task attributes like work, individuals assigned, dates and expenses.
Ch1-Software Engineering 9

This document provides an introduction to software engineering topics including:
1. What software engineering is, its importance, and the software development lifecycle activities it encompasses.
2. The many different types of software systems that exist and how software engineering approaches vary depending on the application.
3. Key fundamentals of software engineering that apply universally, including managing development processes, dependability, and reusing existing software components.
Computer Information System Specialist

Information on the Computer Information System Specialist program available at Carl Sandburg College in Galesburg, IL.
Chapter 10 planning_for_contingencies

This document contains a chapter about contingency planning that discusses various concepts like disaster recovery plans, incident response plans, and business continuity plans. It provides examples of different types of backup sites like cold sites, warm sites, and hot sites. It also discusses testing strategies for contingency plans like simulations and full interruptions. Digital forensics methodology and concepts like chain of custody are explained. The document quizzes the reader with multiple choice questions about these contingency planning topics.
IMPLEMENTATION OF MOSRE FRAMEWORK FOR A WEB APPLICATION - A CASE STUDY

The Security Engineering discipline has become more and more important in the recent years. Security requirements engineering is essential to assure the Quality of the resulting software. An increasing part of the communication and sharing of information in our society utilize Web Applications. Last two years have
seen a significant surge in the amount of Web Application specific vulnerabilities that are disclosed to the public because of the importance of Security Requirements Engineering for Web based systems and as it is still underestimated. Integration of Web and object technologies offer a foundation for expanding the Web to a new generation of applications. In this paper, we outline our proposed Model- Oriented Security Requirement Engineering (MOSRE) Framework for Web Applications. By applying Object-Oriented technologies and modeling to Security Requirement phase. So the completeness, consistency, traceability and reusability of Security Requirements can be cost effectively improved. We implemented our MOSRE Framework for E-Voting Application and set of Security Requirements are identified.
Ch3. agile sw dev

The document discusses agile software development methods. It covers topics like agile methods, techniques, and project management. Agile development aims to rapidly develop and deliver working software through iterative processes, customer collaboration, and responding to changing requirements. Extreme programming (XP) is an influential agile method that uses practices like test-driven development, pair programming, frequent refactoring, and user stories for requirements specification. The key principles of agile methods are also outlined.
Cloud Computing Presentation

The document discusses cloud computing training and certification programs. It provides an overview of cloud computing challenges such as a lack of standard terminology and cloud competencies. It then describes a cloud competence development program that includes cloud computing foundation training and exams. The goal is to provide a common understanding of cloud computing, ensure business-IT alignment, and increase employee skills and career prospects. An example program for ING Banking is given that helped with a large-scale cloud project through developing internal cloud capabilities.
Which Azure certification is good for my career growth

Are you planning to take a Microsoft Azure certification for a long time but unable to decide which one to take? Here is a document that can help you decide.
Comptia cloud-essentials

The CompTIA Cloud Essentials certifi cation is a part of the CompTIA specialty series.
Cloud computing is clearly the next big revolution in the world of IT, and involves
computing over a network of remote servers that are hosted on the Internet.
CompTIA Cloud Essentials teaches the fundamentals of moving to and governing
the cloud, and outlines the bene fits and opportunities that cloud has to o
ffer.
More Related Content
What's hot
Hands on IT risk assessment

This document outlines a risk assessment methodology for organizations. It discusses how risk assessments are often not implemented formally or do not provide practical advice. The presented method uses foundation documents, risk evaluation criteria, and a multi-round review process called the Delphic Technique to provide a standardized risk assessment. It recommends developing reusable templates, defining assessment scope and objectives, using the methodology to identify and evaluate risks, and creating formal treatment plans. Time is included as a variable to show changing risks over time. The goal is for assessments to identify practical risk reduction options.
Xevgenis_Michail_CI7130 Network and Information Security

- The document discusses a security assessment of an organization that provides secure data storage for clients. It outlines the organization's key assets including proper system operation, data security, software, hardware, and employees.
- An analysis team is formed to conduct the security assessment using the OCTAVE framework. The team includes specialists in networking, IT, human resources, security, and business.
- The assessment will identify vulnerabilities and develop security strategies to mitigate risks to the organization's reputation, data protection, availability, and proper operation. Countermeasures proposed will focus on improving the organization's defensive capabilities.
Engineering Software Products: 4. software architecture

Introduces architectural design for software products. Covers architectural models including the MVC model and technology choices.
Pev program criteria training 2020 21

This document provides training for program evaluators (PEVs) on evaluating electrical, computer, communications, and similarly named engineering programs. It contains two sections:
1. Training on the program criteria for programs where IEEE contributes PEVs. This includes reviewing the current program criteria and discussing common shortcomings from previous visits.
2. Information to help PEVs understand upcoming changes to the general ABET criteria that will be effective for visits in fall 2019.
The document reviews the relevant program criteria, provides examples of case studies for PEVs to evaluate, and defines key terms like deficiencies and weaknesses. It aims to equip both new and experienced PEVs with the information needed to properly evaluate programs according to
Pev training 2019 2020

This case study involves an IEEE PEV evaluating a Computer and Software Engineering department that offers separate degree programs in Computer Engineering and Software Engineering. The Computer Engineering program emphasizes hardware design while exposing students to some software topics. The Software Engineering program emphasizes software design. Students from both programs collaborate on senior design projects, with Computer Engineering students focusing more on hardware and Software Engineering students focusing more on software. The case study concludes that the program meets requirements, as Computer Engineering students are knowledgeable in software topics and Software Engineering students can analyze, design, verify, validate, implement, apply and maintain software systems as required by their program criteria.
CISA Domain 1 The Process On AUDITING INFORMATION SYSTEMS

ISACA IS Audit and Assurance Standards, Guidelines, and Tools & Techniques, Code of Professional Ethics & other applicable standard.
https://www.infosectrain.com/blog/cisa-domain-1-part-3-the-process-on-auditing-information-systems/
Program criteria-training 2018-19

The program being evaluated is officially named "Computer and Software Engineering" and offers both computer engineering and software engineering options. While the department head suggested using the electrical/computer/communications criteria since it was used previously, the correct approach is to use both the electrical/computer criteria and the software engineering criteria, as the program contains elements of both and the PEV must be qualified to evaluate both types of programs.
Tamara M Hayajneh

Tamara Hayajneh is a senior information security analyst with over 5 years of experience in network and security fields. She currently works at IT Security Training & Solutions, where her responsibilities include real-time security monitoring, investigating incidents, and managing a security operations center. She previously worked as a network engineer and technical support engineer. Her education includes a bachelor's degree in communication engineering and various security certifications. She is skilled in SIEM solutions, firewall management, and security analysis.
A deployment scenario a taxonomy mapping and keyword searching for the appl...

This document discusses developing a taxonomy to map relationships between applications, virtual machines, hosts, and clients when performing upgrades and patches. It proposes creating a taxonomy based on analyzing errors that occur during application execution to understand dependencies. The taxonomy would classify applications based on their libraries, operating systems, and browsers to provide a troubleshooting guideline for upgrades. An experiment upgrading an application called Crawling encountered errors due to dependencies on older software versions. Mapping the application criteria and relationships in a taxonomy could help identify the root cause of issues and the steps to resolve them.
Secured cloud support for global software

This document summarizes a research paper that proposes a methodology called TSPS (Theory/SWEBOK/Project Security) to improve software engineering education. The methodology aims to collaborate between academic and industrial practices. It involves students working on projects with guidance from both mentors and industry practitioners. Data from literature reviews on software security engineering education is analyzed. A cloud-based system is developed to securely store project documents by encrypting and splitting files across multiple cloud nodes. The methodology and secure cloud storage approach are concluded to provide strategies to mitigate risks in software projects and benefit both education and industry.
Validation of early testing method for e government projects by requirement ...

The document describes a validation study of an Early Requirement Testing Method (ERTM) for e-government projects. Test engineers used the ERTM, which involves reviewing requirements documents and providing feedback, on six e-government projects. The number of defects found before and after applying the ERTM and providing interventions was compared using a statistical test. The results showed that overall, there was a statistically significant reduction in the number of defects found after applying the ERTM, suggesting it is useful for improving requirements documentation. However, one project saw an increase in defects due to additional requirements added later in the project.
Ch7

The document discusses the design and implementation process in software engineering. It covers topics like using the Unified Modeling Language (UML) for object-oriented design, design patterns, and implementation issues. It then discusses the design process, including identifying system contexts and interactions, architectural design, identifying object classes, and creating design models like subsystem, sequence, and state diagrams. The example of designing a weather station system is used to illustrate these design concepts and activities.
Ian Sommerville, Software Engineering, 9th Edition Ch 4

The document discusses requirements engineering and summarizes key topics covered in Chapter 4, including:
- The importance of specifying both functional and non-functional requirements. Non-functional requirements place constraints on system functions and development process.
- The software requirements specification document defines what the system must do and includes both user and system requirements. It should not describe how the system will be implemented.
- Requirements engineering involves eliciting, analyzing, validating and managing requirements throughout the development lifecycle. Precise, complete and consistent requirements are important for development.
Chapter 05 developing_the_security_program

The document discusses developing an information security program, including training methods and project planning tools. It provides examples of true/false questions about security program elements like the security education, training, and awareness program and work breakdown structure. Key aspects covered include the purpose of SETA to reduce accidental breaches, training methods like one-on-one and formal classes, and that the WBS documents minimum task attributes like work, individuals assigned, dates and expenses.
Ch1-Software Engineering 9

This document provides an introduction to software engineering topics including:
1. What software engineering is, its importance, and the software development lifecycle activities it encompasses.
2. The many different types of software systems that exist and how software engineering approaches vary depending on the application.
3. Key fundamentals of software engineering that apply universally, including managing development processes, dependability, and reusing existing software components.
Computer Information System Specialist

Information on the Computer Information System Specialist program available at Carl Sandburg College in Galesburg, IL.
Chapter 10 planning_for_contingencies

This document contains a chapter about contingency planning that discusses various concepts like disaster recovery plans, incident response plans, and business continuity plans. It provides examples of different types of backup sites like cold sites, warm sites, and hot sites. It also discusses testing strategies for contingency plans like simulations and full interruptions. Digital forensics methodology and concepts like chain of custody are explained. The document quizzes the reader with multiple choice questions about these contingency planning topics.
IMPLEMENTATION OF MOSRE FRAMEWORK FOR A WEB APPLICATION - A CASE STUDY

The Security Engineering discipline has become more and more important in the recent years. Security requirements engineering is essential to assure the Quality of the resulting software. An increasing part of the communication and sharing of information in our society utilize Web Applications. Last two years have
seen a significant surge in the amount of Web Application specific vulnerabilities that are disclosed to the public because of the importance of Security Requirements Engineering for Web based systems and as it is still underestimated. Integration of Web and object technologies offer a foundation for expanding the Web to a new generation of applications. In this paper, we outline our proposed Model- Oriented Security Requirement Engineering (MOSRE) Framework for Web Applications. By applying Object-Oriented technologies and modeling to Security Requirement phase. So the completeness, consistency, traceability and reusability of Security Requirements can be cost effectively improved. We implemented our MOSRE Framework for E-Voting Application and set of Security Requirements are identified.
Ch3. agile sw dev

The document discusses agile software development methods. It covers topics like agile methods, techniques, and project management. Agile development aims to rapidly develop and deliver working software through iterative processes, customer collaboration, and responding to changing requirements. Extreme programming (XP) is an influential agile method that uses practices like test-driven development, pair programming, frequent refactoring, and user stories for requirements specification. The key principles of agile methods are also outlined.
What's hot (19)
Xevgenis_Michail_CI7130 Network and Information Security

Xevgenis_Michail_CI7130 Network and Information Security
Engineering Software Products: 4. software architecture

Engineering Software Products: 4. software architecture
CISA Domain 1 The Process On AUDITING INFORMATION SYSTEMS

CISA Domain 1 The Process On AUDITING INFORMATION SYSTEMS
A deployment scenario a taxonomy mapping and keyword searching for the appl...

A deployment scenario a taxonomy mapping and keyword searching for the appl...
Validation of early testing method for e government projects by requirement ...

Validation of early testing method for e government projects by requirement ...
Ian Sommerville, Software Engineering, 9th Edition Ch 4

Ian Sommerville, Software Engineering, 9th Edition Ch 4
IMPLEMENTATION OF MOSRE FRAMEWORK FOR A WEB APPLICATION - A CASE STUDY

IMPLEMENTATION OF MOSRE FRAMEWORK FOR A WEB APPLICATION - A CASE STUDY
Similar to Adapting IT Operations with CompTIA Cloud+
Cloud Computing Presentation

The document discusses cloud computing training and certification programs. It provides an overview of cloud computing challenges such as a lack of standard terminology and cloud competencies. It then describes a cloud competence development program that includes cloud computing foundation training and exams. The goal is to provide a common understanding of cloud computing, ensure business-IT alignment, and increase employee skills and career prospects. An example program for ING Banking is given that helped with a large-scale cloud project through developing internal cloud capabilities.
Which Azure certification is good for my career growth

Are you planning to take a Microsoft Azure certification for a long time but unable to decide which one to take? Here is a document that can help you decide.
Comptia cloud-essentials

The CompTIA Cloud Essentials certifi cation is a part of the CompTIA specialty series.
Cloud computing is clearly the next big revolution in the world of IT, and involves
computing over a network of remote servers that are hosted on the Internet.
CompTIA Cloud Essentials teaches the fundamentals of moving to and governing
the cloud, and outlines the bene fits and opportunities that cloud has to o
ffer.
IRJET- SAAS Attacks Defense Mechanisms and Digital Forensic

This document discusses security challenges and digital forensic techniques for Software as a Service (SaaS) applications in cloud computing environments. It first describes SaaS and its benefits and outlines common security issues like data security, application security, and deployment security. It then reviews related work on securing cloud data storage and integrity. Various digital forensic challenges of investigating crimes in cloud environments are discussed, like lack of transparency and complex virtualized systems. A proposed cloud forensic strategy is described to help investigators collect and analyze evidence from cloud systems in an effective manner. Key security attacks on SaaS like SQL injection and cross-site scripting are also mentioned.
itsas

This document provides information on the Information Technology - Systems Administration Specialist associate degree program at Western Technical College. The 2-year program focuses on providing students with foundational computer systems and networking skills in the first year, then focuses on server administration, virtualization, and cloud computing concepts in the second year. Graduates will be prepared for certifications like MCTS, MCITP, and VCP. The program emphasizes hands-on learning and collaboration with industry partners. Career opportunities for graduates include positions like systems administrator, storage administrator, and help desk analyst.
Cc unit 4 updated version

This document provides an overview of resource management and security in cloud computing. It discusses inter-cloud resource management, resource provisioning models including advance, dynamic and user self-provisioning, and the global exchange of cloud resources. It also covers why cloud security governance is needed, what cloud security governance entails, common challenges around lack of management buy-in, controls, roles and metrics. Finally, it discusses key objectives for an effective cloud security governance model and what virtualized security is compared to traditional physical security.
Ijmer 41025357

This document summarizes a research paper on designing a secure cloud-assisted mobile health monitoring system. The system aims to address privacy and security issues while lowering healthcare costs. It incorporates techniques like multi-dimensional range queries, outsourcing decryption to the cloud, and proxy re-encryption to shift computational tasks to the cloud without compromising privacy. The system architecture allows a mobile health service provider to store encrypted data and programs in the cloud and deliver them securely. It enables clients to query the cloud for monitoring programs using privacy-preserving tokens. The cloud assists with computationally intensive tasks without learning private query inputs or outputs, to protect all parties' privacy and data.
Ijmer 41025357

This document summarizes a research paper that proposes a secure cloud-based mobile health monitoring system called CAM. The system aims to protect patient privacy and the intellectual property of healthcare service providers. It incorporates techniques like anonymous identity-based encryption and outsourced decryption to encrypt health data and shift decryption tasks to the cloud. The system also randomizes diagnostic programs and decision thresholds stored in the cloud to protect provider content. The goal is to allow resource-constrained providers to participate in mobile healthcare via cloud support while preserving security and privacy.
Ijmer 41025357

This document summarizes a research paper on designing a secure cloud-assisted mobile health monitoring system. The system aims to address privacy and security issues while lowering healthcare costs. It incorporates techniques like multi-dimensional range queries, outsourcing decryption to the cloud, and proxy re-encryption to shift computational tasks to the cloud without compromising privacy. The system architecture allows a mobile health service provider to store encrypted data and programs in the cloud and deliver them securely. It enables clients to query the cloud for monitoring programs using privacy-preserving tokens. The cloud assists with computationally intensive tasks without learning private query inputs or outputs. The system aims to achieve effective privacy preservation while reducing the workload on clients and the service provider.
Secure Multi-Owner Group Signature Based Secure M-Health Records in Cloud 

This document summarizes a research paper that proposes a secure cloud-based mobile health monitoring system called CAM. The system aims to protect patient privacy and the intellectual property of healthcare service providers. It incorporates techniques like anonymous identity-based encryption and outsourced decryption to encrypt health data and shift decryption tasks to the cloud. The system also randomizes diagnostic programs and decision thresholds stored in the cloud to protect provider content. The final scheme enables resource-constrained providers to participate by reducing their computational burden through techniques like key-private proxy re-encryption.
6 in-1 enterprise cloud certification training program

This document provides an overview of a 6-in-1 cloud certification program that combines key topics from various vendor-neutral cloud certification programs. The program uses confidence-based learning methodology to enhance understanding through online assessments of concepts. Modules cover topics such as foundational technologies, virtualization, storage, networking, delivery models, service management, risk management, and security. The program aims to prepare professionals for multiple cloud certifications and provide a flexible learning experience.
Cloud Computing Course Overview

The document provides an overview of the EXIN Cloud Computing Foundation certification. It describes cloud computing as providing computational power on demand and allowing IT services to focus on their core competencies without worrying about infrastructure difficulties. The certification helps IT professionals improve their cloud computing knowledge and attain global recognition. It covers topics like cloud types, benefits, architecture, services, applications, management, security, trends and is beneficial for roles like IT specialists, managers, architects, and consultants. Choosing Trainings24x7 for training provides accredited materials, free practice tests, experienced trainers, and globally recognized certification.
Iaetsd design and implementation of secure cloud systems using

The document proposes a Business Continuity Management (BCM) framework to address data security issues when transforming cloud systems into a meta cloud. BCM is a holistic management process that identifies risks and reduces the impacts of data leakage. It involves understanding the organization, determining continuity strategies, developing response plans, and exercising/reviewing plans. The framework contains components like business continuity leads, working groups, and links to emergency preparedness. It uses a plan-do-check-act approach and aims to embed continuity into the organization's culture.
Cloud Computing Course Content

EXIN Cloud Computing Foundation is a demanding certification required by many IT organizations all over the world. The Cloud Computing Elementary Professional Certification provides clearly and concisely the basis of cloud computing. It is a technology of providing computational power on tap for IT service and allows IT service providers to concentrate on their chief competence by managing customers without worrying about the difficulties of infrastructure.
Certified Cloud Computing Specialist (CCCS)

GICT Certified Cloud Computing Specialist (CCCS) provides participants with knowledge about service delivery models and architecture of cloud computing
Find Out More : https://globalicttraining.com
CompTIA CASP+ | Everything you need to know about the new exam

Want to be an advanced cybersecurity practitioner? Then CompTIA’s CASP+ certification may be the perfect fit for you. The popular certification is getting an overhaul heading into 2022 to ensure it validates the most relevant and in-demand skills — from security architecture and operations to engineering and governance.
Network Security Expert Professional (002)

This document provides information about a Network Security Expert Professional course offered by Global Information Technology. The 477-hour course prepares students to take and pass certification exams for A+, Network+, Linux+, Security+, MCSA 2012, and CCNA. Upon completing the course and exams, students will have an impressive portfolio of six IT certifications to include on their resume. The course teaches skills needed for careers such as network administrator, security engineer, help desk technician, and more. It covers topics like networking, security, operating systems, and troubleshooting. The growing demand for IT and cybersecurity professionals makes this an exciting and rewarding career path.
Moving Apps to Cloud

This document discusses moving applications to the cloud, including:
- Assessing whether an application is suitable for the cloud based on business need, feasibility, and technical fit. Not all applications need to or should move.
- Identifying applications that are good candidates based on factors like usage patterns, requirements for scale, and external usage. Applications with many users or public usage are better candidates.
- Defining an approach that involves assessing business value, technical fitment, identifying suitable cloud providers, migrating or reengineering components, testing, and managing applications in the cloud. The approach should be aligned with the organization's cloud strategy.
cloud Resilience 

The document discusses cloud resilience, provisioning, and asset management.
For cloud resilience, it outlines a structured 4-step approach: 1) Assessing assets and requirements, 2) Planning and designing resilience strategies, 3) Implementing and testing, and 4) Managing and sustaining resilience over time.
Cloud provisioning refers to how, what, and when cloud services are provisioned, including dynamic, user, and post-sales models.
Cloud asset management is about managing cloud applications, platforms, and infrastructure to address challenges like lack of visibility, usage data, and spending controls across cloud services. Effective cloud asset management provides benefits like cost optimization and readiness for cloud migrations.
NEC Employee Accreditation Activity ProjectNetwork Enterpriser.docx

NEC Employee Accreditation Activity Project
Network Enterprisers Corporation
Employee Accreditation Activity Project
Version 0.1
June 25, 2015
Presented by:
Mr. Mariano Maldonaldo
Ms. Charlene Stroud
Project Proposal
Developing an Employee Accreditation Activity process is an important step toward the Network Enterprisers Corporation’s vision as a winning business in a competitive market. This proposal will outline the methods and resources needed to be successful in tracking employee training and certification.
Table of Contents
I.
TABLE OF CONTENTS
II.
ACKNOWLEDGEMENTS
III.
LIST OF FIGURES
1.1
GOALS AND OBJECTIVES
1.2
SYSTEM STATEMENT OF WORK
1.2.1 General Requirements
1.2.2 Extended Requirements
1.3
System Context
1.4
Major Constraints
2.0
PROJECT ESTIMATES
2.1
Historical Data
2.2
Applied Techniques and Results
2.2.1 Activity, Task and Function List
2.2.2 Best Effort Estimation
2.3
Project Resources
2.4.1 Manpower
2.4.2 Hardware Requirements
2.4.3 Software Requirements
3.0
RISK ASSESSMENT
3.1
Risk Assessment Activities
3.2
Risk Management Roles
4.0
PROJECT SCHEDULE
4.1
Deliverables and Milestones
4.2
Work Structure Breakdown
5.0
PROJECT MANAGEMENT TEAM
5.1
Structure
5.2
Responsibilities
6.0
TRACKING AND CONTROL DEVICE
6.1
Quality Assurance
6.2
Change Management
7.0
Database Management
7.1
User Interface Design and Relationships
7.2
Support Services
ANNEX A
APPENDIX B
List of Figures
Figure 1: Organization Chart
6
Figure 2: Current System
6
Figure 3: Problem Statement
8
Figure 4: Development Cost
12
Figure 5: Min Computer Requirements
14
Figure 6: Server Specifications:
15
Figure 7: Personnel Management Development Table
16
Figure 8: Database Relationships:
17
Figure 9: Physical Design
18
Figure 10: Form Wizard Employee Information
19
Figure 11: Form Wizard Visitor Information
19
Figure 12: Controlled Access Management Information
20
Figure 13: Sample Input
22
Figure 14: Request For Services
23
Figure 15: Sample Output
24
Figure 16: Database Document
25
Figure 17: Repository
82
Figure 18: Context Model
83
Figure 19: Functional Decomposition Diagram
84
Goals and Objectives
The Network Enterpriser Corporation (NEC) will need a training tracking database for the Information and Programming Department (IPD) to pass the August Security Manager’s Quality Control Inspection. Employees are required to make sure that all of their certification and course requirements are up to date. If a NEC employee does not have the proper certification and training requirements they will lose access to controlled areas and or information. This proposal is to determine if creating a Share Point Excel Training Management tracking system to track classroom and online training will assist in keeping all employees in the Information and Programming Department current on all training and certification requirements. The proposed database i.
Similar to Adapting IT Operations with CompTIA Cloud+ (20)
Which Azure certification is good for my career growth

Which Azure certification is good for my career growth
IRJET- SAAS Attacks Defense Mechanisms and Digital Forensic

IRJET- SAAS Attacks Defense Mechanisms and Digital Forensic
Secure Multi-Owner Group Signature Based Secure M-Health Records in Cloud 

Secure Multi-Owner Group Signature Based Secure M-Health Records in Cloud
6 in-1 enterprise cloud certification training program

6 in-1 enterprise cloud certification training program
Iaetsd design and implementation of secure cloud systems using

Iaetsd design and implementation of secure cloud systems using
CompTIA CASP+ | Everything you need to know about the new exam

CompTIA CASP+ | Everything you need to know about the new exam
NEC Employee Accreditation Activity ProjectNetwork Enterpriser.docx

NEC Employee Accreditation Activity ProjectNetwork Enterpriser.docx
More from CompTIA
CompTIA IT Employment Tracker – December 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – November 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – October 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – September 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – July 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – June 2021

The document provides data on technology employment trends in the United States from May 2021. It finds that hiring for top tech jobs increased month-over-month in May, with software developers seeing the largest gain. By state, Florida, Georgia and Virginia saw the highest increases in tech job postings. The Washington D.C. metro area had the largest month-over-month growth in postings. Remote and work from home opportunities were most commonly advertised for software developers and related roles. Overall, the tech sector workforce grew slightly in May while unemployment rates remained low.
Trends in Automation 2021

The document summarizes survey results about trends in automation from organizations. It finds that most organizations take a balanced approach to technology that monitors emerging trends while prioritizing current operations. The top strategic business goals for using automation are improving efficiency and maintaining customer accounts. Over 40% of organizations feel extremely or highly confident in applying technology to their goals. Common barriers to automation include unsure benefits, lack of technical skills, and insufficient budget. The top automation initiatives are administrative tasks, detecting cybersecurity incidents, and configuring virtual machines.
CompTIA IT Employment Tracker – May 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – April 2021

This document summarizes technology employment and job posting trends from March 2021. It finds that hiring for top tech jobs increased 14,600 compared to February, led by gains in software development. The tech sector added 9,700 jobs overall. California, Texas and New York had the most tech job postings, while the largest metro areas were New York, Washington D.C. and Dallas. Artificial intelligence postings accounted for 14.9% of emerging tech jobs. The unemployment rate for IT occupations was 1.9% in March.
IT Operations and Emerging Technology

CompTIA's IT Operations and Emerging Tech tracker monitors the investments companies are making across the four pillars of IT and the adoption of emerging technology.
CompTIA IT Employment Tracker – March 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
Help Desk Trends

CompTIA's Trends in Help Desk survey explores the areas businesses are focusing on as they manage their help desk function, including IT priorities, required skills, and emerging technologies.
CompTIA IT Employment Tracker – February 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA 2021 IT Industry Outlook

CompTIA’s annual Industry Outlook report examines 10 trends that businesses will use as they rebuild from a challenging year, along with focused sections on expectations for IT professionals and for IT channel firms.
CompTIA IT Employment Tracker - January 2021

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – November 2020

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – October 2020

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – September 2020

This document provides data and analysis on IT sector employment, job postings, and unemployment from August 2020. Some key points:
- Software developers and IT support specialists remained the most sought-after IT occupations in August based on job posting data.
- The IT sector added over 9,000 jobs in August compared to July, with the largest gains in computer systems design.
- California, Texas, and Virginia had the highest numbers of IT job postings, while Florida, Colorado, and New Jersey saw the largest monthly increases.
- Remote/work from home IT job postings grew over 20% in August, led by postings for software developers, IT support specialists, and web developers.
CompTIA IT Employment Tracker – August 2020

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
CompTIA IT Employment Tracker – July 2020

Monthly data, analysis, and trending covering the state of employment in the information technology (IT) sector and IT occupations. Released in conjunction with the U.S. Bureau of Labor Statistics monthly employment update. #JobsReport
More from CompTIA (20)
Recently uploaded
How MJ Global Leads the Packaging Industry.pdf

MJ Global's success in staying ahead of the curve in the packaging industry is a testament to its dedication to innovation, sustainability, and customer-centricity. By embracing technological advancements, leading in eco-friendly solutions, collaborating with industry leaders, and adapting to evolving consumer preferences, MJ Global continues to set new standards in the packaging sector.
Best practices for project execution and delivery

A select set of project management best practices to keep your project on-track, on-cost and aligned to scope. Many firms have don't have the necessary skills, diligence, methods and oversight of their projects; this leads to slippage, higher costs and longer timeframes. Often firms have a history of projects that simply failed to move the needle. These best practices will help your firm avoid these pitfalls but they require fortitude to apply.
Industrial Tech SW: Category Renewal and Creation

Every industrial revolution has created a new set of categories and a new set of players.
Multiple new technologies have emerged, but Samsara and C3.ai are only two companies which have gone public so far.
Manufacturing startups constitute the largest pipeline share of unicorns and IPO candidates in the SF Bay Area, and software startups dominate in Germany.
The Steadfast and Reliable Bull: Taurus Zodiac Sign

Explore the steadfast and reliable nature of the Taurus Zodiac Sign. Discover the personality traits, key dates, and horoscope insights that define the determined and practical Taurus, and learn how their grounded nature makes them the anchor of the zodiac.
The Genesis of BriansClub.cm Famous Dark WEb Platform

BriansClub.cm, a famous platform on the dark web, has become one of the most infamous carding marketplaces, specializing in the sale of stolen credit card data.
DearbornMusic-KatherineJasperFullSailUni

My powerpoint presentation for my Music Retail and Distribution class at Full Sail University
Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...

Dive into the steadfast world of the Taurus Zodiac Sign. Discover the grounded, stable, and logical nature of Taurus individuals, and explore their key personality traits, important dates, and horoscope insights. Learn how the determination and patience of the Taurus sign make them the rock-steady achievers and anchors of the zodiac.
Digital Transformation Frameworks: Driving Digital Excellence

[To download this presentation, visit:
https://www.oeconsulting.com.sg/training-presentations]
This presentation is a curated compilation of PowerPoint diagrams and templates designed to illustrate 20 different digital transformation frameworks and models. These frameworks are based on recent industry trends and best practices, ensuring that the content remains relevant and up-to-date.
Key highlights include Microsoft's Digital Transformation Framework, which focuses on driving innovation and efficiency, and McKinsey's Ten Guiding Principles, which provide strategic insights for successful digital transformation. Additionally, Forrester's framework emphasizes enhancing customer experiences and modernizing IT infrastructure, while IDC's MaturityScape helps assess and develop organizational digital maturity. MIT's framework explores cutting-edge strategies for achieving digital success.
These materials are perfect for enhancing your business or classroom presentations, offering visual aids to supplement your insights. Please note that while comprehensive, these slides are intended as supplementary resources and may not be complete for standalone instructional purposes.
Frameworks/Models included:
Microsoft’s Digital Transformation Framework
McKinsey’s Ten Guiding Principles of Digital Transformation
Forrester’s Digital Transformation Framework
IDC’s Digital Transformation MaturityScape
MIT’s Digital Transformation Framework
Gartner’s Digital Transformation Framework
Accenture’s Digital Strategy & Enterprise Frameworks
Deloitte’s Digital Industrial Transformation Framework
Capgemini’s Digital Transformation Framework
PwC’s Digital Transformation Framework
Cisco’s Digital Transformation Framework
Cognizant’s Digital Transformation Framework
DXC Technology’s Digital Transformation Framework
The BCG Strategy Palette
McKinsey’s Digital Transformation Framework
Digital Transformation Compass
Four Levels of Digital Maturity
Design Thinking Framework
Business Model Canvas
Customer Journey Map
Best Forex Brokers Comparison in INDIA 2024

Navigating the world of forex trading can be challenging, especially for beginners. To help you make an informed decision, we have comprehensively compared the best forex brokers in India for 2024. This article, reviewed by Top Forex Brokers Review, will cover featured award winners, the best forex brokers, featured offers, the best copy trading platforms, the best forex brokers for beginners, the best MetaTrader brokers, and recently updated reviews. We will focus on FP Markets, Black Bull, EightCap, IC Markets, and Octa.
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The Radar reflects input from APCO’s teams located around the world. It distils a host of interconnected events and trends into insights to inform operational and strategic decisions. Issues covered in this edition include:
The latest Heat Pump Manual from Newentide

𝐔𝐧𝐯𝐞𝐢𝐥 𝐭𝐡𝐞 𝐅𝐮𝐭𝐮𝐫𝐞 𝐨𝐟 𝐄𝐧𝐞𝐫𝐠𝐲 𝐄𝐟𝐟𝐢𝐜𝐢𝐞𝐧𝐜𝐲 𝐰𝐢𝐭𝐡 𝐍𝐄𝐖𝐍𝐓𝐈𝐃𝐄’𝐬 𝐋𝐚𝐭𝐞𝐬𝐭 𝐎𝐟𝐟𝐞𝐫𝐢𝐧𝐠𝐬
Explore the details in our newly released product manual, which showcases NEWNTIDE's advanced heat pump technologies. Delve into our energy-efficient and eco-friendly solutions tailored for diverse global markets.
Maksym Vyshnivetskyi: PMO KPIs (UA) (#12)

Maksym Vyshnivetskyi: PMO KPIs (UA)
Lemberg PMO School 2024
Website – https://lembs.com/pmoschool
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Anny Serafina Love - Letter of Recommendation by Kellen Harkins, MS.

This letter, written by Kellen Harkins, Course Director at Full Sail University, commends Anny Love's exemplary performance in the Video Sharing Platforms class. It highlights her dedication, willingness to challenge herself, and exceptional skills in production, editing, and marketing across various video platforms like YouTube, TikTok, and Instagram.
TIMES BPO: Business Plan For Startup Industry

Starting a business is like embarking on an unpredictable adventure. It’s a journey filled with highs and lows, victories and defeats. But what if I told you that those setbacks and failures could be the very stepping stones that lead you to fortune? Let’s explore how resilience, adaptability, and strategic thinking can transform adversity into opportunity.
HOW TO START UP A COMPANY A STEP-BY-STEP GUIDE.pdf

How to Start Up a Company: A Step-by-Step Guide Starting a company is an exciting adventure that combines creativity, strategy, and hard work. It can seem overwhelming at first, but with the right guidance, anyone can transform a great idea into a successful business. Let's dive into how to start up a company, from the initial spark of an idea to securing funding and launching your startup.
Introduction
Have you ever dreamed of turning your innovative idea into a thriving business? Starting a company involves numerous steps and decisions, but don't worry—we're here to help. Whether you're exploring how to start a startup company or wondering how to start up a small business, this guide will walk you through the process, step by step.
The Most Inspiring Entrepreneurs to Follow in 2024.pdf

In a world where the potential of youth innovation remains vastly untouched, there emerges a guiding light in the form of Norm Goldstein, the Founder and CEO of EduNetwork Partners. His dedication to this cause has earned him recognition as a Congressional Leadership Award recipient.
Recently uploaded (20)
The Steadfast and Reliable Bull: Taurus Zodiac Sign

The Steadfast and Reliable Bull: Taurus Zodiac Sign
The Genesis of BriansClub.cm Famous Dark WEb Platform

The Genesis of BriansClub.cm Famous Dark WEb Platform
Registered-Establishment-List-in-Uttarakhand-pdf.pdf

Registered-Establishment-List-in-Uttarakhand-pdf.pdf
Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...

Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...
Digital Transformation Frameworks: Driving Digital Excellence

Digital Transformation Frameworks: Driving Digital Excellence
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...
Anny Serafina Love - Letter of Recommendation by Kellen Harkins, MS.

Anny Serafina Love - Letter of Recommendation by Kellen Harkins, MS.
HOW TO START UP A COMPANY A STEP-BY-STEP GUIDE.pdf

HOW TO START UP A COMPANY A STEP-BY-STEP GUIDE.pdf
The Most Inspiring Entrepreneurs to Follow in 2024.pdf

The Most Inspiring Entrepreneurs to Follow in 2024.pdf
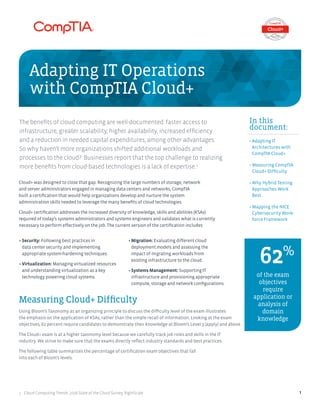
Adapting IT Operations with CompTIA Cloud+
- 1. • Security: Following best practices in data center security and implementing appropriate system-hardening techniques. • Virtualization: Managing virtualized resources and understanding virtualization as a key technology powering cloud systems. • Migration: Evaluating different cloud deployment models and assessing the impact of migrating workloads from existing infrastructure to the cloud. • Systems Management: Supporting IT infrastructure and provisioning appropriate compute, storage and network configurations. The benefits of cloud computing are well-documented: faster access to infrastructure, greater scalability, higher availability, increased efficiency and a reduction in needed capital expenditures, among other advantages. So why haven’t more organizations shifted additional workloads and processes to the cloud? Businesses report that the top challenge to realizing more benefits from cloud-based technologies is a lack of expertise.1 Cloud+ was designed to close that gap. Recognizing the large numbers of storage, network and server administrators engaged in managing data centers and networks, CompTIA built a certification that would help organizations develop and nurture the system administration skills needed to leverage the many benefits of cloud technologies. Cloud+ certification addresses the increased diversity of knowledge, skills and abilities (KSAs) required of today’s systems administrators and systems engineers and validates what is currently necessary to perform effectively on the job. The current version of the certification includes: 1 Cloud Computing Trends: 2016 State of the Cloud Survey, RightScale Adapting IT Operations with CompTIA Cloud+ In this document: • Adapting IT Architectures with CompTIA Cloud+ • Measuring CompTIA Cloud+ Difficulty • Why Hybrid Testing Approaches Work Best • Mapping the NICE Cybersecurity Work- force Framework of the exam objectives require application or analysis of domain knowledge 62% Measuring Cloud+ Difficulty Using Bloom’s Taxonomy as an organizing principle to discuss the difficulty level of the exam illustrates the emphasis on the application of KSAs, rather than the simple recall of information. Looking at the exam objectives, 62 percent require candidates to demonstrate their knowledge at Bloom’s Level 3 (apply) and above. The Cloud+ exam is at a higher taxonomy level because we carefully track job roles and skills in the IT industry. We strive to make sure that the exams directly reflect industry standards and best practices. The following table summarizes the percentage of certification exam objectives that fall into each of Bloom’s levels. 1
- 2. Bloom’s Level and Description Total Cloud+ Objectives Security Virtualization Level 1: Remembering/Recalling Information The candidate is able to recall, restate and remember learned information. 0% 0% 0% Level 2: Understanding/Explaining Ideas or Concepts The learner grasps the meaning of information by interpreting and translating what has been learned. 38% 43% 29% Level 3: Applying Knowledge and Skills The learner makes use of information in a new situation from the one in which it was learned. 34% 14% 57% Level 4: Analyzing The learner breaks learned information into parts to best understand that information in an attempt to identify evidence for a conclusion. 22% 43% 14% Level 5: Evaluating The learner makes decisions based on in depth reflection, criticism and assessment. 6% 0% 0% Level 6: Creating The learner creates new ideas and information using what has been previously learned. 0% 0% 0% Cloud+ Executive Summary Why Hybrid Testing Approaches Work Best Over the past several years, cybersecurity practitioners and educators have debated as to which of the following is more important to validate: 1. An individual’s conceptual knowledge, as validated by “linear” multiple choice items, or 2. Performance associated with a particular job or responsibility, as validated by performance-based items. Advocates for each of these two aspects of validation often hold one of the approaches as superior over the other, with most individuals favoring only performance-based items. CompTIA regards this rift in opinion as a false dilemma. Both domain knowledge expertise and practical skills are absolutely vital and should be a part of any serious competency training and validation process. Both knowledge- and performance-based aspects are necessary for training, and nothing can substitute for hands-on learning. The same principle applies to assessment. This is why CompTIA adopted performance-based items into its certification exams starting in 2011. The following CompTIA exams contain roughly 10 percent performance-based items: On average, it takes a test taker roughly one-third of the examination time to complete these performance- based items. Performance-based items include simulations of technology solutions and story-based items that require advanced cognitive thinking on the part of the successful test taker. A+ | Network+ | Security+ | Cybersecurity Analyst (CSA+) | CompTIA Advanced Security Practitioner (CASP) 2
- 3. System Administrator (OM-SA-001) CompTIA Cloud+ Description Installs, configures, troubleshoots and maintains hardware and software, and administers system accounts. Cloud+ focuses on validating the skills needed for those in a defined family of job roles – those related to IT infrastructure and operations. The certification validates a candidate’s ability to implement, maintain and deliver cloud technologies and infrastructures. Sample KSA Comparisons K0053 Knowledge of measures or indicators of system performance and availability. Domain 4-Resource Management 4.1— Given a scenario, implement and use proper resource monitoring techniques 4.2 — Given a scenario, appropriately allocate physical (host) resources using best practices 4.3 — Given a scenario, appropriately allocate virtual (guest) resources using best practices Domain 6-Systems Management 6.2 — Given a scenario, diagnose, remediate and optimize physical host performance 6.3 — Explain common performance concepts as they relate to the host and the guest 6.4 — Implement appropriate testing techniques when deploying cloud services Domain 7-Business Continuity in the Cloud 7.2 — Deploy solutions to meet availability requirements S0073 Skill in using virtual machines. K0130 Knowledge of virtualization technologies and virtual machine development and maintenance. Domain 2-Virtualization 2.1 — Explain the differences between hypervisor types 2.2 — Install, configure and manage virtual machines and devices 2.3 — Given a scenario, perform virtual resource migration 2.4 — Explain the benefits of virtualization in a cloud environment 2.5 — Compare and contrast virtual components used to construct a cloud environment Domain 3-Infrastructure 3.8 — Explain common hardware resources and features used to enable virtual environments Mapping the NICE Cybersecurity Workforce Framework CompTIA Cloud+ certification aligns with the System Administrator work role (OM-SA-001) as described in the National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework (NCWF), draft NIST special publication 800-181. Both the work role and the certification share a focus on systems installation, maintenance and troubleshooting, with Cloud+ specifically addressing the impact of cloud technologies on the system administrator and engineer roles. Cloud+ Executive Summary LEARN MORE For government inquiries contact: GovernmentSales@CompTIA.org. For corporate inquiries contact: Jennifer Herroon at jherroon@CompTIA.org 3
- 4. Cloud+ Executive Summary © 2017 CompTIA Properties, LLC, used under license by CompTIA Certifications, LLC. All rights reserved. All certification programs and education related to such programs are operated exclusively by CompTIA Certifications, LLC. CompTIA is a registered trademark of CompTIA Properties, LLC in the U.S. and internationally. Other brands and company names mentioned herein may be trademarks or service marks of CompTIA Properties, LLC or of their respective owners. Reproduction or dissemination prohibited without written consent of CompTIA Properties, LLC. Printed in the U.S. 03724-Apr2017 4
