- The document discusses a security assessment of an organization that provides secure data storage for clients. It outlines the organization's key assets including proper system operation, data security, software, hardware, and employees.
- An analysis team is formed to conduct the security assessment using the OCTAVE framework. The team includes specialists in networking, IT, human resources, security, and business.
- The assessment will identify vulnerabilities and develop security strategies to mitigate risks to the organization's reputation, data protection, availability, and proper operation. Countermeasures proposed will focus on improving the organization's defensive capabilities.


![FACULTY OF ENGINEERING
DEPARTMENTS OF ELECTRONICS ENGINEERING AND AUTOMATION ENGINEERING
TECHNOLOGICAL EDUCATIONAL INSTITUTE OF PIRAEUS
Preparation
During this report we will fulfill a security assessment based on OCTAVE-S
Framework. The three basic principles that the security assessment is based on are the
confidentiality, the integrity and the availability of the information. The OCTAVE method is a
qualitative method and is self-directed by enabling people to learn about security issues [1].
Also, OCTAVE consists of a set of criteria that includes principles, attributes and outputs. By
implementing the OCTAVE approach we organize workshops in our company and the
decisions ,concerning the level of importance for particular data resources, are taken by the
employees. The threats in this framework are defined by three logical structures . The first
phase is to build asset based threat profiles. In the second phase we identify infrastructure
vulnerabilities and in the third phase we develop security strategy and plans.[1],[2]
The OCTAVE method is ideal for our assessment because it is perfectly adjusted to
our company’s policies. Nowadays every company has information that needs to be
protected. By applying this method we can improve the organization’s security posture
without the involvement of outside experts and vendors , so the company’s budget will not
suffer any loss. Furthermore, by using this framework we can develop a team working spirit
and establish an open communication with the employees and also discover vulnerabilities
in our system and focus in critical issues. Nevertheless, this kind of approach should be
applied regularly because the flow of information is constant. However , the lack of
regularity may lead to data compromise or legal consequences. In addition , the OCTAVE
method is time consuming but it should not be neglected.[1]
As we aforementioned the execution of OCTAVE requires the creation of an analysis
team. During the first workshop we create the team that will cooperate with us to complete
our assessment. Our analysis team consists of the Network Administrator , the IT manager
,the HR manager , the Security officer and the Business Consult. The Network Administrator
plays a key role because he knows the architecture of the implemented network and he is
responsible for the maintenance of the network and its operation. The IT manager is
responsible for the operation of our company by testing our software equipment and by
evaluating our software problems mostly for the applications and operation systems that our
company uses. The HR manager also plays a key role because he is responsible for the
evaluation of the employees and the creation of profiles for every employee according to
their character. The Security officer is responsible for collecting information about new
cyberattacks and new hacking techniques. The Business Consult is responsible for the
financial part of our company that includes the distribution of the budget for the company’s
needs and also for the financial analysis of a possible failure of our company’s properly
operation.
The members of this analysis team have been chosen carefully in order to complete
the security assessment for our company. They have key roles in the company and each of
them is a part of the big puzzle that reflects our company’s security. The Network
Administrator and the IT manager have proven their knowledge in the field of
telecommunications and in the field of information and they will contribute in the matters of
technology .The HR manager has proven his knowledge in the field of psychology and
evaluation of an employee’s behavior that is a very important tool to fight back the social
Module:
Module Coordinator:](https://image.slidesharecdn.com/3497b940-bf66-4ccd-a6f7-08d3d2afb109-160202165554/85/Xevgenis_Michail_CI7130-Network-and-Information-Security-5-320.jpg)
![FACULTY OF ENGINEERING
DEPARTMENTS OF ELECTRONICS ENGINEERING AND AUTOMATION ENGINEERING
TECHNOLOGICAL EDUCATIONAL INSTITUTE OF PIRAEUS
engineering. The Security officer has knowledge about new malicious techniques that have
been implemented by attackers and their frequency which are implemented. Also the
Business Consult has knowledge about the financial parts of the company and he can
indicate us which of the solutions that we propose are realistic and furthermore the financial
impact that the company can suffer in case of a failure.
Organization Overview
Our organization is responsible for the secure storage of classified records of our
clients. These records consist of critical information about the security of our clients. The
hardware that our clients use for their protection, as also the codes of the access cards and
the security alarms that they use, are very important information that needs to be classified.
Our ultimate goal is to avoid the violation of confidentiality, integrity and availability of our
information. The important assets of our company are the proper operation of our systems
and our data security. Furthermore, our software and our hardware are key components of
our organization's proper operation and are also critical assets. Nevertheless, it is a fact that
nowadays social engineering is a growing method that may lead to harmful consequences
for our company, so the people are also a key asset. Our goal is to improve our safety and
mitigate the risk of a danger. In addition, we should provide with information only people who
have the authorization and only after the procedure of their identification. Every employee,
according to the job role who has, has also the right privilege and the access in the system’s
operation.
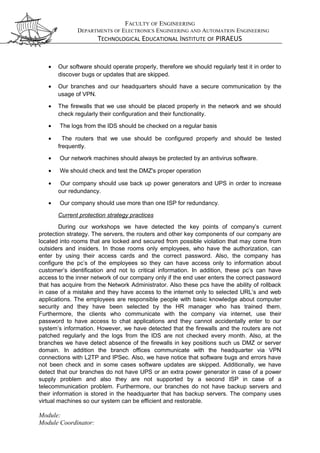
The company is geographically distributed and consists of three branch offices and
one headquarter. The headquarter is located in Athens which is the capital of Greece and
the largest city in terms of population. Also in Athens the one of our three branches is
located in order to service the majority of our clients. The second branch is located in
Thessaloniki that is the second large city in Greece in terms of population and covers the
north region of the country. Our third branch is located in Chania in order to service our
customers in the south region of the country.
Furthermore, the headquarter and the branches communicate via VPN (Virtual
Private Network) connections. Each branch office consists of servers, switches, routers, pcs
and firewalls that are important for the company’s operation and their operation system is
Windows. At the application layer our company uses the web application Siebel that creates
the customers profile with all the necessary information. The headquarter is the center of
that enterprise network and consists of all the aforementioned machines too. At the
headquarter the most critical information is stored and secured the most critical information,
therefore it must be heavily secured. Nevertheless, it is important to provide internet access
when a customer visits the branch, therefore we provide a Wi-Fi connection. In addition,
clients who are away from our branch should be able to communicate with us via a WAN
(Wide Area Network) connection (Internet).
However, our employees who have access to critical information should use their pcs
wisely in order to keep the information secure and to service the clients. The operation of the
pc’s system is also Windows and is the version 7-64 bits. Also there are implemented
mechanisms for those pcs to avoid critical mistakes and to mitigate the risk of danger. For
the proper operation of our company we use the hardware that covers our needs. To
establish a secure communication between the headquarters and the branch offices we use
the Cisco RV320 Dual Gigabit WAN VPN Router [3]. Moreover, the company uses the Cisco
Module:
Module Coordinator:](https://image.slidesharecdn.com/3497b940-bf66-4ccd-a6f7-08d3d2afb109-160202165554/85/Xevgenis_Michail_CI7130-Network-and-Information-Security-6-320.jpg)
![FACULTY OF ENGINEERING
DEPARTMENTS OF ELECTRONICS ENGINEERING AND AUTOMATION ENGINEERING
TECHNOLOGICAL EDUCATIONAL INSTITUTE OF PIRAEUS
SRP546W for the wireless internet connection of the customers who visit our branches [4].
The switches that we use in our company are Cisco 220 Series Smart Plus Switches [5].
DMZ
Interne t Fire wall
Wi-Fi
Inne r Firewall
Web Serve r/V M
Exchang e Server
A pplication
Se rver/VM
Database Serve r
Web Serve r
Customer
Interne t Firewa ll
Interne t
End Use r
E nd User
WAN Connection
VPN Connection
DMZ
Internet Fire wall
W i-Fi
Inne r Firewall
Web Serve r/VM
Exchang e Se rver
Applica tion Server/
VM Databa se
Se rver
Web Serve r
Custome r
Interne t
E nd User
End User
WAN Connection
VPN Connection
DMZ
Interne t Fire wall
Wi-Fi
Web Serve r/VM
E xchange Server
Applica tion Serve r/
V M Da tabase
Se rve r
W eb Serve r
Customer
Interne t
E nd Use r
E nd Use r
WAN Connection
VPN Connection
Internet Firewa ll
Interne t Firewall
DMZ
Internet Firewa ll
W i-Fi
Inne r Firew all
Web Serve r/V M
Exchange Se rver
Applica tion S erver/VM
Da tabase Serve r
Web Server
Customer
Interne t Fire wall
Internet
End Use r
End Use r
WAN Connection
VPN Connection
Backup Application
Server/V M Da tabase
Serve r
Backup W eb Server/VM
Exchang e Se rver
Internet Fire wall
Figure1. Network Map
Security Assessment
Important assets and areas of concern
During our security assessment we focus on company’s important assets that are
critical for our organization’s proper operation and for our data security. The important assets
for our company are the proper operation of our system and the confidentiality integrity and
availability of our information. Also, the functionality of our software and the proper operation
of our hardware are important assets and they influence the proper operation of the
company and the data security. However, the trustworthiness of our company is based on
the employees that we have selected, so the human factor is also an important asset.
Nevertheless, the important assets that we highlighted above should be protected
from possible threats. Threats that may damage our systems functionality and our data
security may occur by humans who use physical access to our machines either accidentally
either deliberately, for example a thief brakes into and steals the server. Another type of
threat is the human that uses network access and causes a system problem that may occur
accidentally or deliberately. Also, a software bug or a software malfunction should be
consider as a threat as well as a malfunction of the hardware that may lead also to the crash
of our system. However, threats may occur due to other reasons such us power supply
problems, telecommunications problems or unavailability and natural disasters.
Security Requirements
In order to face the possible threats that may lead to the organization’s malfunction
we should consider our security requirements. The following steps indicate our security
requirements:
• Our hardware equipment should be protected from unauthorized access by placing it
in rooms in which only authorized employees can enter by using their access cards.
Module:
Module Coordinator:](https://image.slidesharecdn.com/3497b940-bf66-4ccd-a6f7-08d3d2afb109-160202165554/85/Xevgenis_Michail_CI7130-Network-and-Information-Security-7-320.jpg)
![FACULTY OF ENGINEERING
DEPARTMENTS OF ELECTRONICS ENGINEERING AND AUTOMATION ENGINEERING
TECHNOLOGICAL EDUCATIONAL INSTITUTE OF PIRAEUS
Organizational vulnerabilities
Finishing our workshops we were able to detect the organizational vulnerabilities.
One of those vulnerabilities is that the Network Administrator does not patch the routers and
the firewalls regularly and that may lead to harmful situations. Also in some cases firewalls
are not present or they are misplaced in critical points of the network. In addition, the logs
that the IDS provides us are not often observed so we cannot have a clear picture of the
traffic that the IDS captures. Also the IT manager does not check the software operation
regularly so bugs and errors are often skipped and the employees most of the time they do
not run the updates. Furthermore the fact that the branches do not have UPS or a power
generator and they do not use a second ISP and they do not have backup servers may lead
also to harmful situations.
Selection of critical assets and creation of threat profiles
Considering the current strategy of our company and the company’s vulnerabilities
we proceed to threat analysis. The properties of threat consist of the asset, the access, the
actor, the motive and the outcome. Building our threat profiles around the properties of
threat, we select the most critical assets for our company. The critical assets that we select
are the data protection, the software’s proper operation and the hardware’s proper operation.
Based on those critical assets we proceed to the creation of threat profiles. [2]
Table 1. Threat profiles
Asset Access Actor Motive Outcome
Data confidentiality Network access Outside Deliberate A hacker gains access to the
data of our clients so can cause
disclosure of data.
Data integrity Network access Outside Deliberate A hacker gains access to the
data of our clients and can
cause modification of data.
Data availability Network access Outside Deliberate A hacker may enter to our
system by exploiting our
vulnerabilities and may delete
our data and cause loss or
destruction of data.
Data availability Network access Outside Deliberate A hacker may enter our system
and may apply a DOS attack. As
a result the clients cannot have
access to their data until the
system has recovered. That is
an interruption to the company’s
operation and the data are not
available.
Software operation - Software defects - The lack of the regular updates
and the fact that the bugs are
not checked may cause
malfunction of our software and
as a result we may have data
modification.
Software operation - Software defects - The lack of the regular testing of
our software for bugs and
updates that are skipped can
cause malfunction and probably
loss or destruction of our data.
Module:
Module Coordinator:](https://image.slidesharecdn.com/3497b940-bf66-4ccd-a6f7-08d3d2afb109-160202165554/85/Xevgenis_Michail_CI7130-Network-and-Information-Security-9-320.jpg)


![FACULTY OF ENGINEERING
DEPARTMENTS OF ELECTRONICS ENGINEERING AND AUTOMATION ENGINEERING
TECHNOLOGICAL EDUCATIONAL INSTITUTE OF PIRAEUS
connectivity to external networks, or every 6 months if they are not connected to external
networks. In addition the logs from the IDS should be checked in a regular basis in order to
have a clear picture of the malicious attempts of an outsider. Also the software that we use
should be tested frequently and every anomalous behavior should be analyzed in order to
face bugs or other vulnerabilities. The employees should not skip the updates. [6]
Furthermore, our software needs to be maintained and we should purchase devices
for backup in case of a failure. Also our company should use honeypots. By the usage of
honeypots we can buy some time by tricking the intruder and as a result we can save our
data and we can organize better our defensive line. Also by the implementation of honeypots
we may gain some information about the attacker [8]. In addition, the internet connection
and the wireless connections should be segregated by the use of DMZ (De-Militarized
Zone), which should contain application layer firewalls and strong authentication.
Furthermore, in order to face power supply problems, natural disasters or telecommunication
problems, we should use power generators and UPS in case of a power supply problem, our
data should be saved in a place that is located at another geographical domain in case of
natural disaster and we should use more than one ISP in case of a telecommunication
problem. [6]
REFERENCES
1. The OCTAVE methodology as a risk analysis tool for business resources, Pyka Marek, Januszkiewicz
Paulina ,Academy of Business in Dąbrowa Górnicza, Poland.
2. OCTAVESM* Threat Profiles, Christopher Alberts and Audrey Dorofee, Software Engineering Institute
Carnegie Mellon University.
3. http://www.cisco.com/c/en/us/products/collateral/routers/small-business-srp500-series-services-ready-
platforms/data_sheet_c78-550705.html
4. http://www.cisco.com/c/en/us/products/collateral/routers/rv320-dual-gigabit-wan-vpn-
router/data_sheet_c78-726132.html
5. http://www.cisco.com/c/en/us/products/collateral/switches/small-business-220-series-smart-plus-
switches/datasheet-c78-731284.html
6. CGIAR Network Infrastructure, Security Good Practice Guide ,August 2009
7. Security Assessments, Eckhard Pfluegel
8. Honeypots Revealed ,Mohamed Noordin Yusuff, IT Security Officer , Specialist Dip. Info Security, MA.
Internet Security Mgmt (Ongoing)
Module:
Module Coordinator:](https://image.slidesharecdn.com/3497b940-bf66-4ccd-a6f7-08d3d2afb109-160202165554/85/Xevgenis_Michail_CI7130-Network-and-Information-Security-12-320.jpg)
