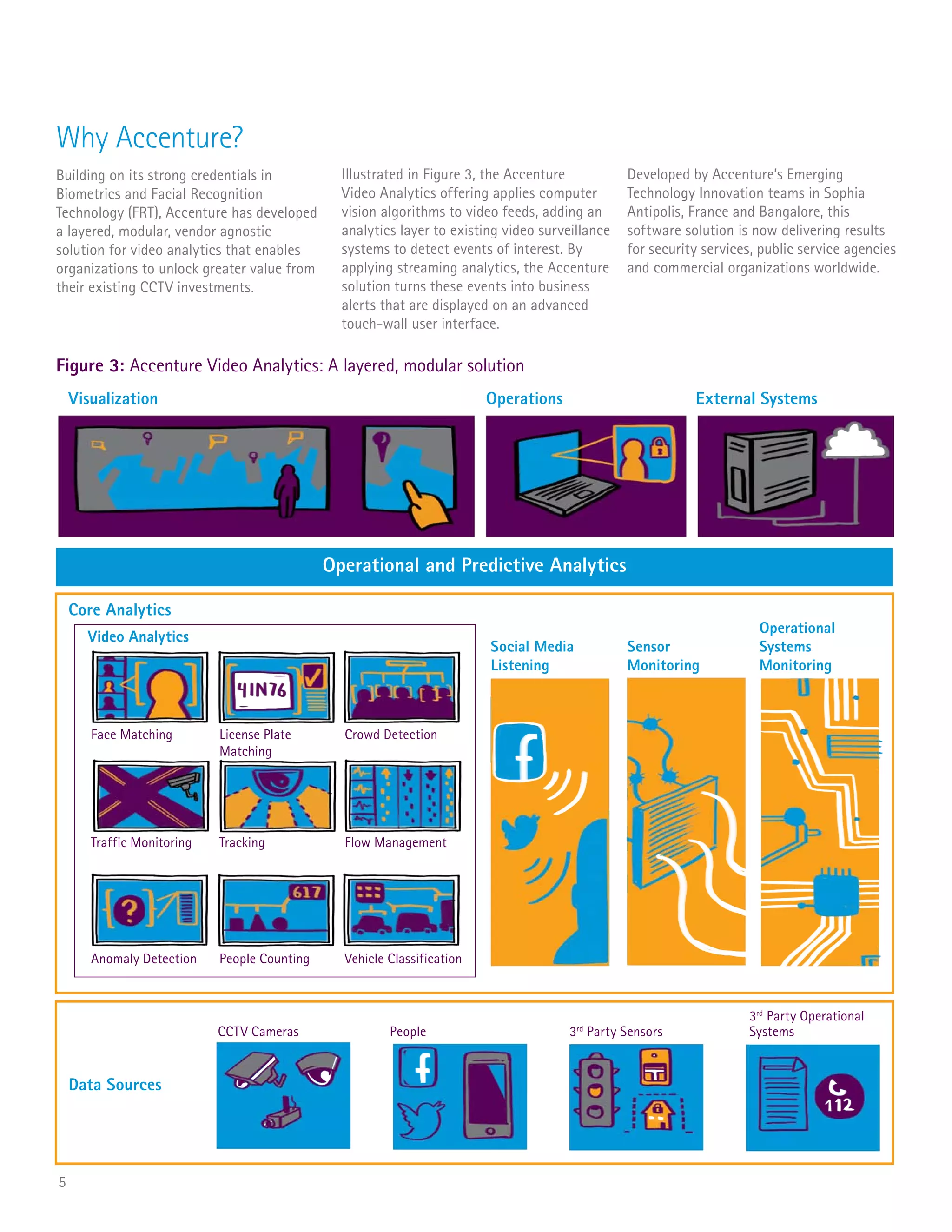
This document discusses how video analytics can provide operational, marketing, and security insights by applying computer vision algorithms to existing CCTV video feeds. Specifically:
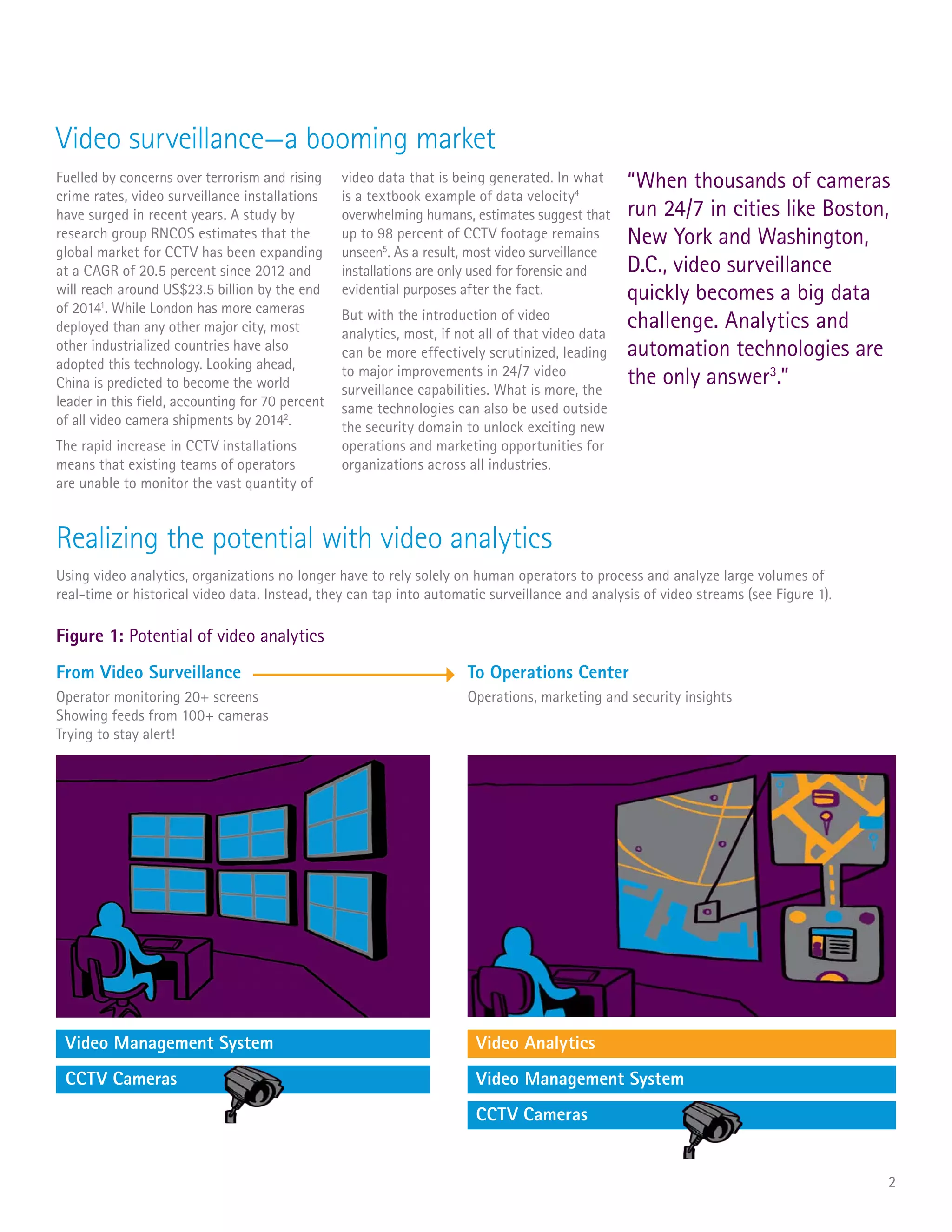
- Video analytics technologies can automate the analysis of large volumes of video data that would otherwise overwhelm human operators, and provide insights beyond just security like optimizing operations and understanding customer behavior.
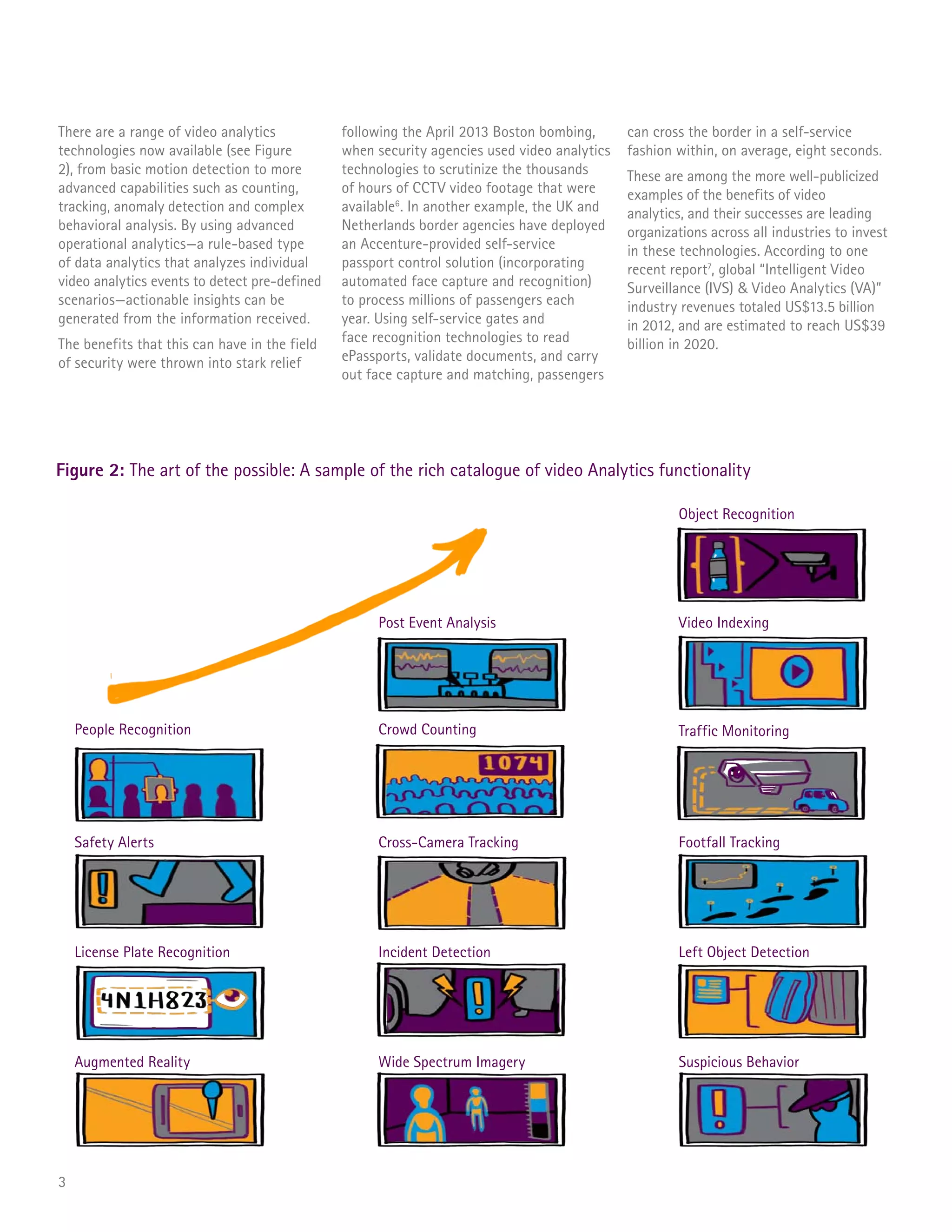
- Advancements in video analytics technologies now enable capabilities like people counting, queue monitoring, and detecting pre-defined scenarios to generate actionable insights.
- As video analytics technologies continue advancing and becoming more affordable, organizations are using them to gain real-time insights into space usage, foot traffic, wait times, and typical usage patterns to optimize operations and target marketing.