The document discusses the UK Defence and Security Accelerator (DSA) and its collaboration with various industry sectors to address security challenges. It highlights the objectives of the Joint Security and Resilience Centre (JSARC) in fostering collaboration between government and the private sector, promoting innovation, and improving procurement processes. Key themes include technological advancements in situational awareness, protection, power provision, and the development of resilient systems in the defence and security landscape.






![+
© Crown30 January
Possible Security interests in the “Enduring Challenge”
Protection
Personnel,
platforms, facilities,
digital systems,
materials
Enduring challenge
competition
Data
Cyber, information, big data,
management and processing,
sense-making, visualisation,
delivery, interoperability
Power
Provision/sources, non-fossil,
hybrid, management,
fuel efficiency
Communications
Secure, unsecure, mobile,
novel forms
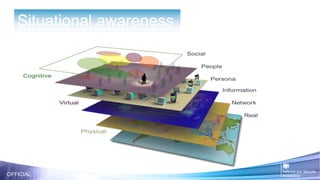
Situational Awareness
Sensors, precision navigation
& timing, reduced GPS
dependability, persistent
surveillance
Lethality
Weapons – conventional, novel
directed energy, defence, less-
than-lethal
Mobility
Platforms [air, land, sea, space,
human], means of propulsion
Human Performance
Physical and mental, systems
interface, survivability, training,
medical
Lower cost of ownership
Platforms, equipment, facilities](https://image.slidesharecdn.com/finalsession2acceleratorenduringchallenge26jan17nonames-170130085837/85/Accelerator-Enduring-Competition-Challenge-Session-2-13-320.jpg)


![OFFICIAL
Enduring challenge
competition
Power
Provision/sources, non-fossil,
hybrid, management,
fuel efficiency
Communications
Secure, unsecure, mobile,
novel forms
Situational Awareness
Sensors, precision navigation
& timing, reduced GPS
dependability, surveillance
Lethality
Weapons – conventional,
novel directed energy,
defence, less-than-lethal
Mobility
Platforms [air, land, sea,
space, human],
means of propulsion
Human
Performance
Physical and mental,
systems interface,
survivability, training,
medical
Lower
cost of ownership
Platforms, equipment,
facilities
Protection
Personnel, platforms,
facilities, digital systems,
materials
Data
Cyber, information, big data,
management and processing,
sense-making, visualisation,
delivery, interoperability
9 challenge areas of defence and security](https://image.slidesharecdn.com/finalsession2acceleratorenduringchallenge26jan17nonames-170130085837/85/Accelerator-Enduring-Competition-Challenge-Session-2-17-320.jpg)













![OFFICIAL
Enduring challenge
competition
Power
Provision/sources, non-fossil,
hybrid, management,
fuel efficiency
Communications
Secure, unsecure, mobile,
novel forms
Situational Awareness
Sensors, precision navigation
& timing, reduced GPS
dependability, surveillance
Lethality
Weapons – conventional,
novel directed energy,
defence, less-than-lethal
Mobility
Platforms [air, land, sea,
space, human],
means of propulsion
Human
Performance
Physical and mental,
systems interface,
survivability, training,
medical
Lower
cost of ownership
Platforms, equipment,
facilities
Protection
Personnel, platforms,
facilities, digital systems,
materials
Data
Cyber, information, big data,
management and processing,
sense-making, visualisation,
delivery, interoperability
9 challenge areas of defence and security](https://image.slidesharecdn.com/finalsession2acceleratorenduringchallenge26jan17nonames-170130085837/85/Accelerator-Enduring-Competition-Challenge-Session-2-34-320.jpg)
















![OFFICIAL
Enduring challenge
competition
Power
Provision/sources, non-fossil,
hybrid, management,
fuel efficiency
Communications
Secure, unsecure, mobile,
novel forms
Situational Awareness
Sensors, precision navigation
& timing, reduced GPS
dependability, surveillance
Lethality
Weapons – conventional,
novel directed energy,
defence, less-than-lethal
Mobility
Platforms [air, land, sea,
space, human],
means of propulsion
Human
Performance
Physical and mental,
systems interface,
survivability, training,
medical
Lower
cost of ownership
Platforms, equipment,
facilities
Protection
Personnel, platforms,
facilities, digital systems,
materials
Data
Cyber, information, big data,
management and processing,
sense-making, visualisation,
delivery, interoperability
9 challenge areas of defence and security](https://image.slidesharecdn.com/finalsession2acceleratorenduringchallenge26jan17nonames-170130085837/85/Accelerator-Enduring-Competition-Challenge-Session-2-58-320.jpg)