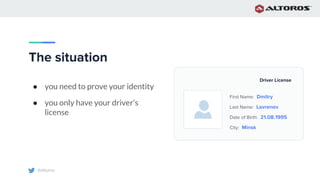
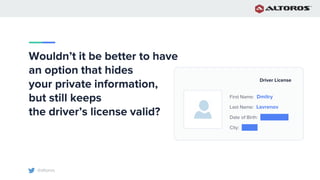
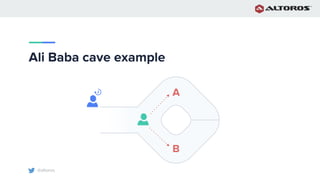
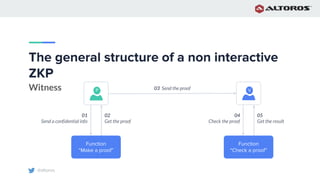
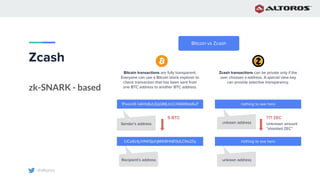
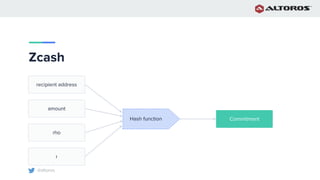
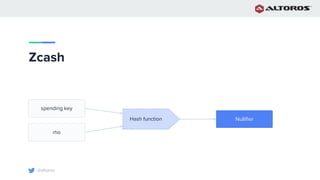
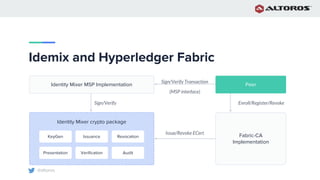
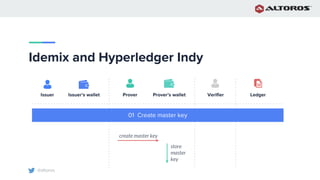
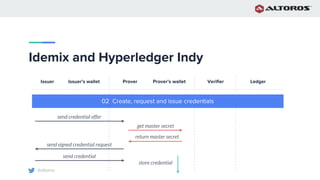
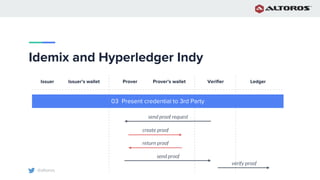
The document discusses zero-knowledge proofs (ZKPs) as a method for proving one’s identity while keeping personal information private, highlighting the cryptographic protocol's components and conditions like completeness, soundness, and zero knowledge. It elaborates on applications of ZKPs in various fields, mentioning implementations such as Zcash and Ethereum's Aztec protocol which leverage zk-SNARKs for privacy in transactions. The document also touches on practical implementations of identity verification using ZKPs within the Hyperledger frameworks.







![@altoros
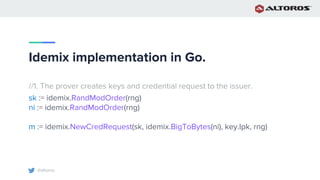
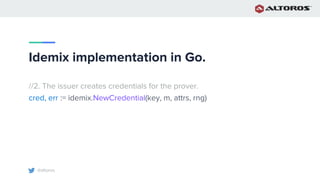
Idemix implementation in Go
AttributeNames := [ ]string{"First Name", "Last Name", "Age", "City"}
data := [ ]string{"Dmitry00000000000000000000000000",
"Lavrenov000000000000000000000000",
"23000000000000000000000000000000",
"Minsk000000000000000000000000000"}](https://image.slidesharecdn.com/azero-knowledgeproofimprovingprivacyonablockchain-190404121133/85/A-Zero-Knowledge-Proof-Improving-Privacy-on-a-Blockchain-43-320.jpg)
![@altoros
Idemix implementation in Go.
// 3. The prover signs the credentials without disclosure Age and City.
disclosure = [ ]byte{1, 1, 0, 0}
sig, err = idemix.NewSignature(cred, sk, Nym, RandNym, key.Ipk,
disclosure, msg, rhindex, cri, rng)
attrs[2] = FP256BN.NewBIGint(0)
attrs[3] = FP256BN.NewBIGint(1)](https://image.slidesharecdn.com/azero-knowledgeproofimprovingprivacyonablockchain-190404121133/85/A-Zero-Knowledge-Proof-Improving-Privacy-on-a-Blockchain-46-320.jpg)