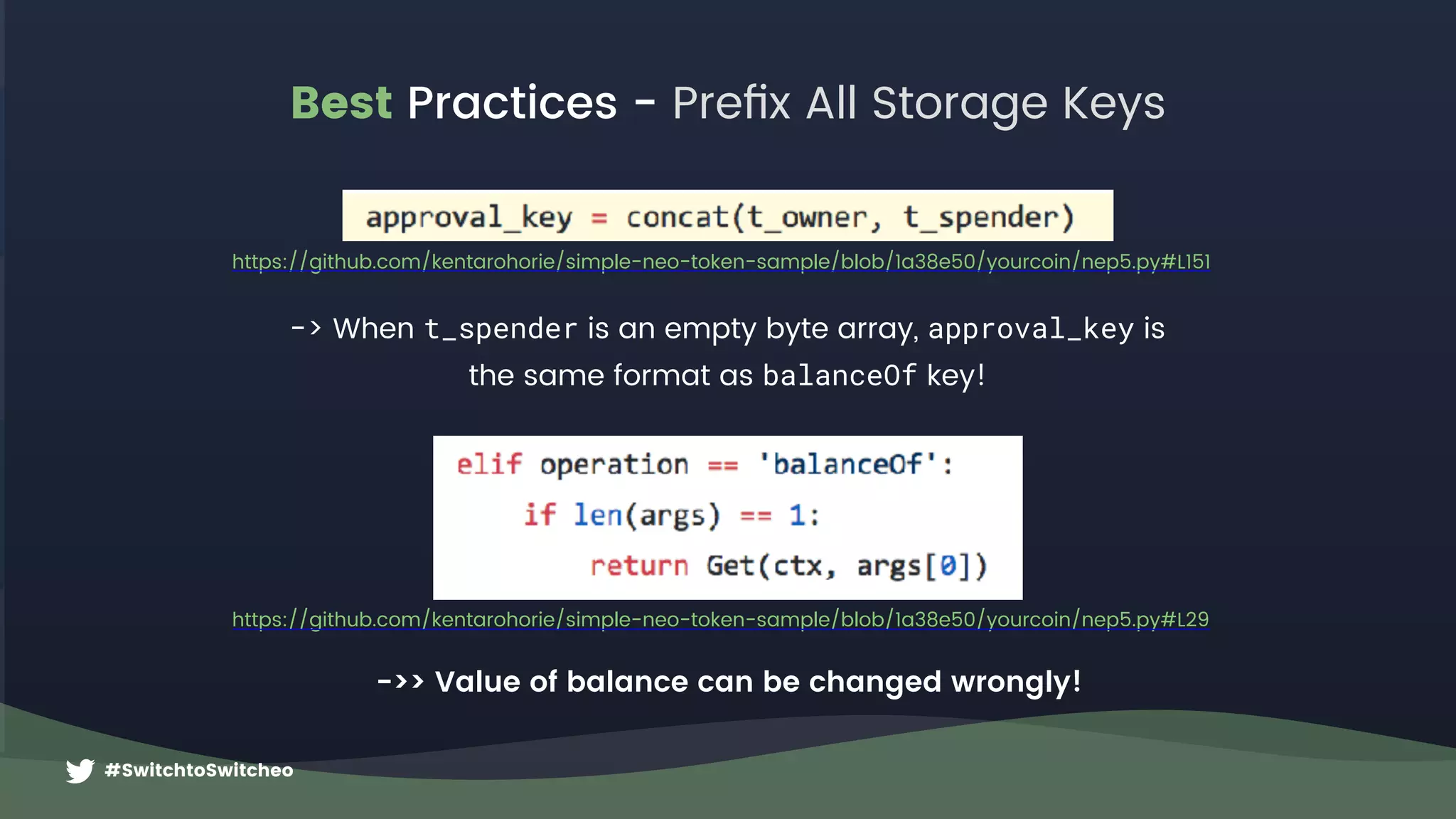
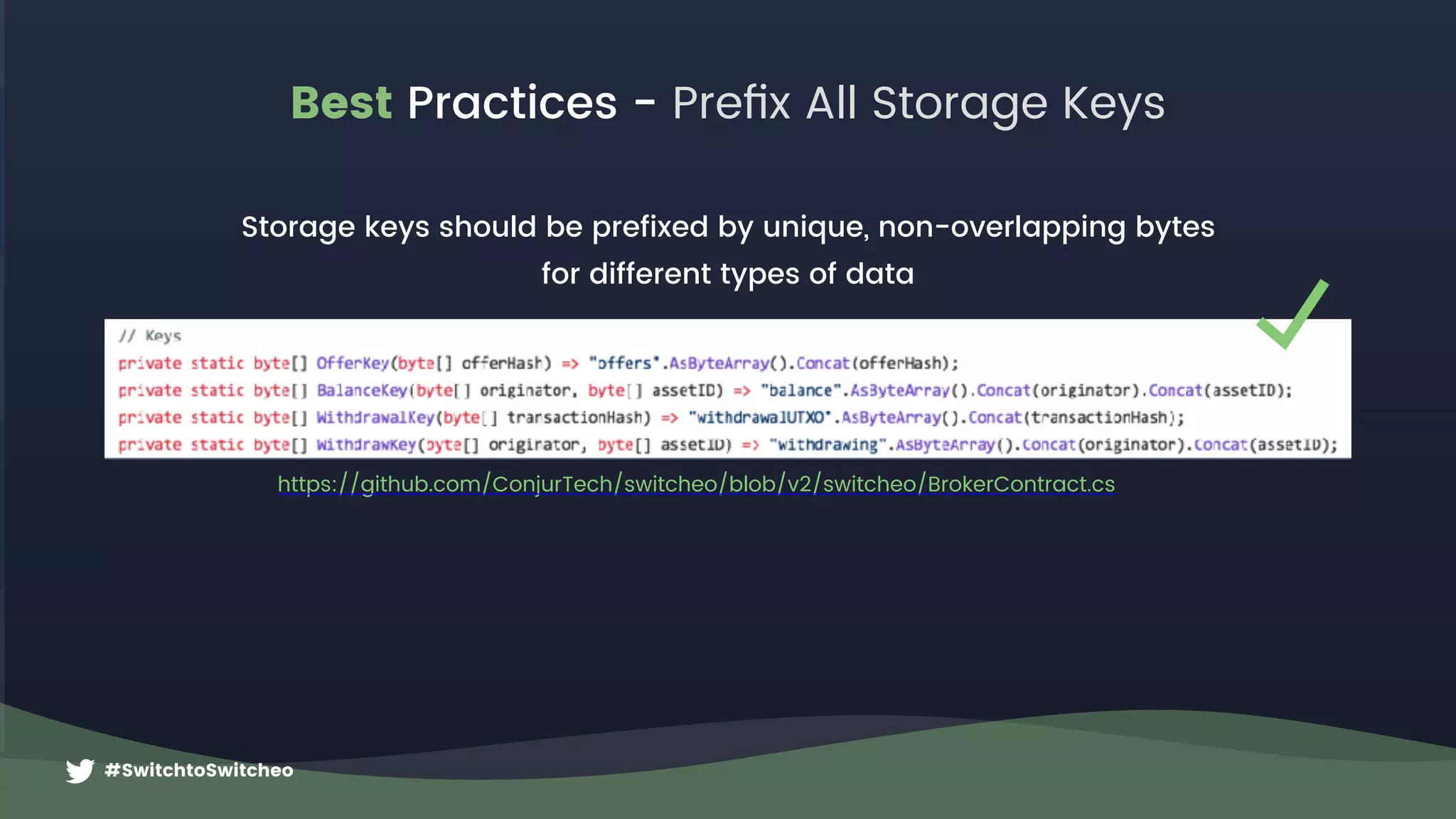
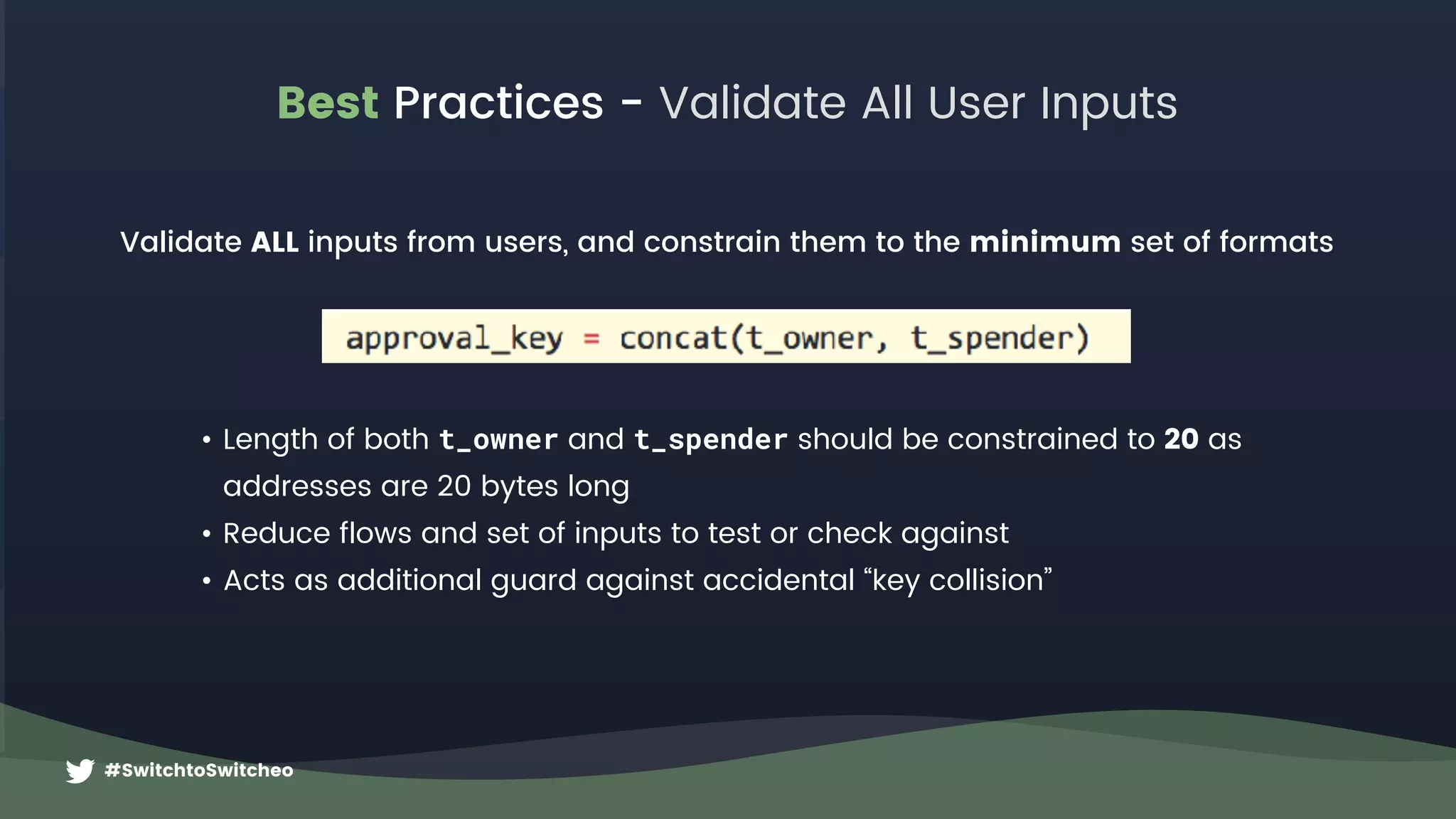
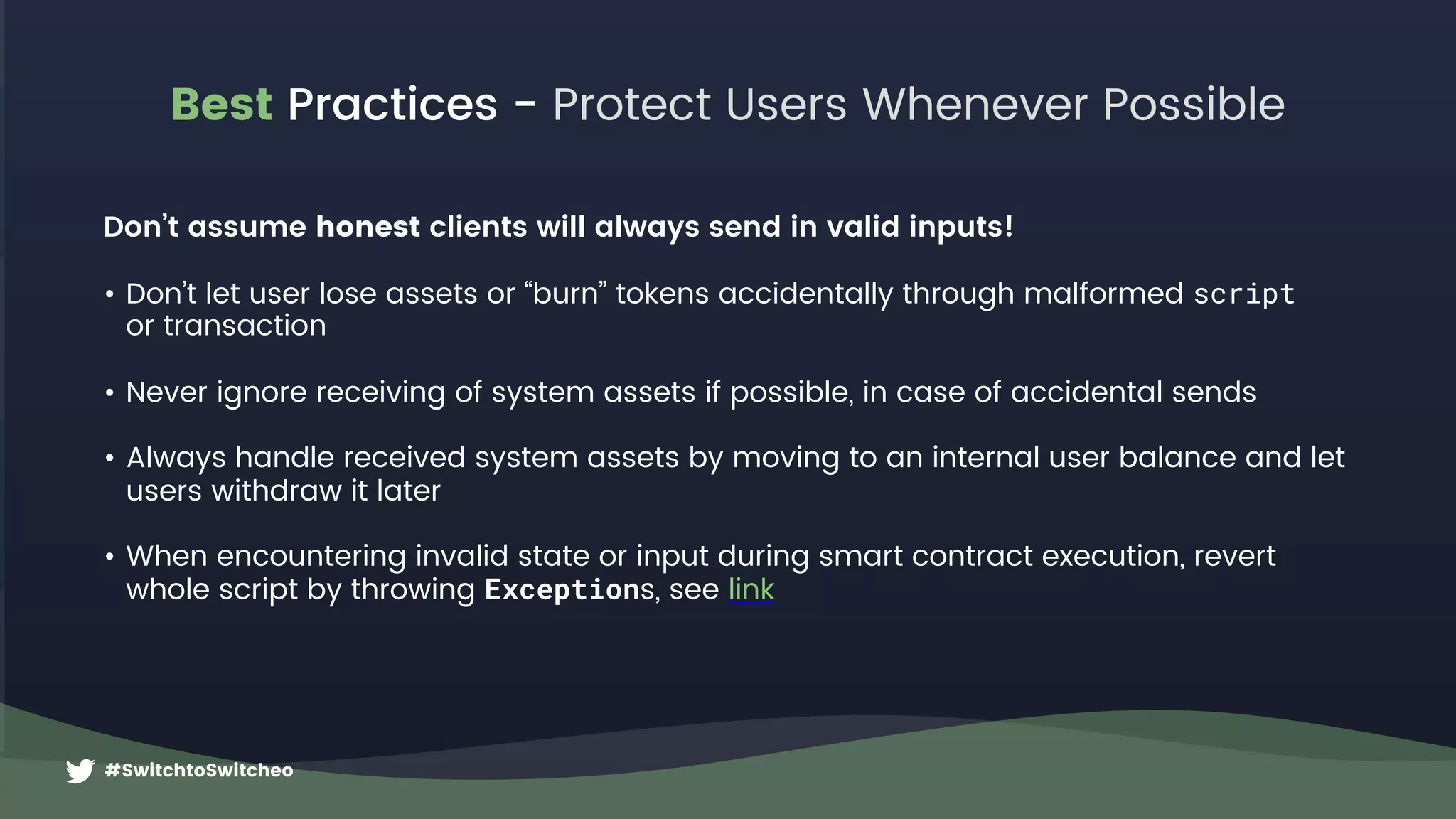
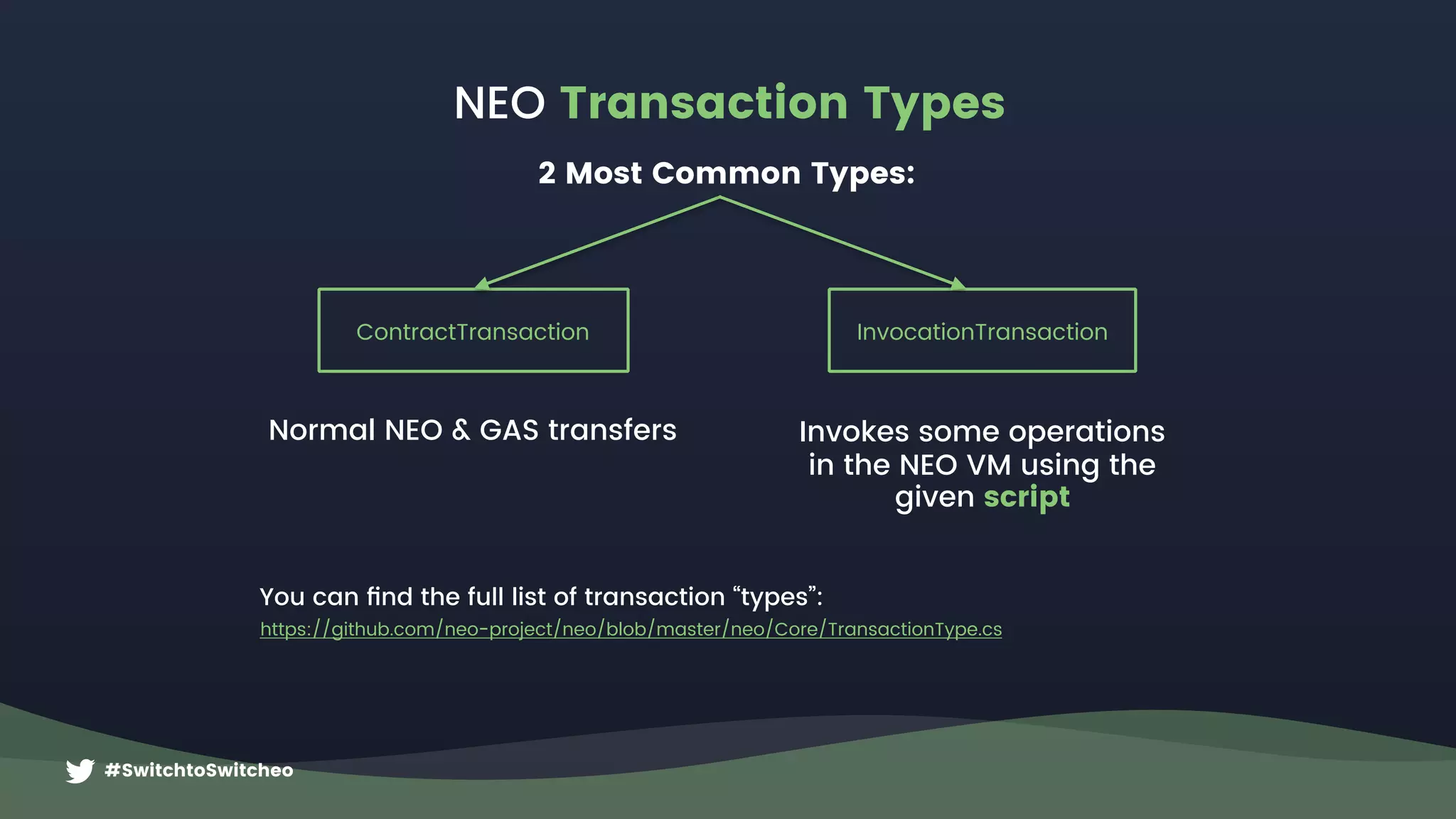
This document provides an overview of advanced NEO smart contracts. It begins with an agenda for the workshop and questions about transaction experience. It then discusses how NEO verifies transactions using witness scripts and unspent outputs. Details are given on transaction structure, types, and attributes. Best practices are outlined around constraining invocation scripts, guarding dynamic invokes, prefixing storage keys, validating inputs, and protecting users. The presentation encourages following Switcheo for an upcoming API development competition.



![#SwitchtoSwitcheo
NEO Transaction Structure
https://github.com/CityOfZion/neon-js/blob/e5b63db/src/
transactions/core.js#L79
f9592fc8a8fbc6be23963983f28179dcb341219b
a12431d0b9db640034b0cdfceef9cce161e62be4
560827208eed0ec04254f523cd5373ec1b394683
6e3382c4c4a69a3a62b489a456b327b5d301bea6
8888888721e49496726d4bf1c32876c0b41cd01f
https://github.com/neo-project/neo/blob/
23bbe9b/neo/Core/Transaction.cs#L18
JSON Byte Code
{
“type”: …,
“version”: …,
“attributes”: […],
“inputs”: […],
“outputs”: […],
“scripts”: […],
“script”: …,
}](https://image.slidesharecdn.com/switcheoneoworkshop30jun-180705162252/75/Switcheo-Network-Advanced-NEO-Smart-Contracts-7-2048.jpg)
![#SwitchtoSwitcheo
NEO Inputs & Outputs
{
inputs: [{
txid: “0xa…”,
index: 0,
address: A,
amount: 5,
}, {
txid: “0xb…”,
index: 0,
address: B,
amount: 7,
}],
outputs: [{
address: C,
amount: 12
}],
attributes: [{
usage: 0x20, // Script
data: <addr D>],
}
Transaction
must be
witnessed by
A+B+D
Address A
+5
Address B
+7
Address C
12
https://bitcoin.org/en/developer-guide#block-chain](https://image.slidesharecdn.com/switcheoneoworkshop30jun-180705162252/75/Switcheo-Network-Advanced-NEO-Smart-Contracts-10-2048.jpg)
![#SwitchtoSwitcheo
{
scripts: [{
invocation: <addressA_Signature>,
verification: <addressA_VerificationScript>
},
invocation: <addressB_Signature>,
verification: <addressB_VerificationScript>
},
invocation: <addressD_Signature>,
verification: <addressD_VerificationScript>
},
],
}
NEO Witness Scripts
0x … … … … … …
ECDSA Signature
0x … … … …
Public Key
0xac
Check Signature
64 bytes long
33 bytes long
Invocation: https://github.com/CityOfZion/neon-js/blob/4634e74/src/wallet/core.js#L84
Verification: https://github.com/CityOfZion/neon-js/blob/4634e74/src/transactions/core.js#L150
Witness Scripts for a standard “wallet contract”
0x40
Push 40 Bytes
invocation
0x21
Push 33 Bytesverification](https://image.slidesharecdn.com/switcheoneoworkshop30jun-180705162252/75/Switcheo-Network-Advanced-NEO-Smart-Contracts-11-2048.jpg)
![#SwitchtoSwitcheo
OpCode Hex Explanation
PUSH20 0x20 Pushes the next 20 bytes onto the stack
<from> 0x11fg876d..
Push the “from” address for an NEP-5 transfer
operation
PUSH3 0x53 Pushes the number ‘3' onto the stack
0x11fg876d..
0x225ab73..
0x3356765..
3
… … … … … … … … … … … …
PACK 0xC1
Pops N from stack and combines the next N items into an
array
PUSHBYTES8 0x08 Pushes the next 8 bytes onto the stack
“transfer” 0x7472616e73666572
the operation string as bytes in this case it is the
“transfer” operation for NEP-5
APPCALL 0x67
Reads the next 20 bytes and invokes the corresponding
deployed contract with Application Trigger.
<scriptHash> 0xa12cde… The hash of the deployed smart contract to invoke
So transaction will have: { …, “script”:“020bf1920…” }
0x11 0x22 0x3
0x7472616..
Stack
https://github.com/neo-project/neo-vm/blob/master/src/neo-vm/OpCode.cs
Script example for a standard entrypoint: Main(string operation, params object[] args)
NEO Script](https://image.slidesharecdn.com/switcheoneoworkshop30jun-180705162252/75/Switcheo-Network-Advanced-NEO-Smart-Contracts-13-2048.jpg)
![#SwitchtoSwitcheo
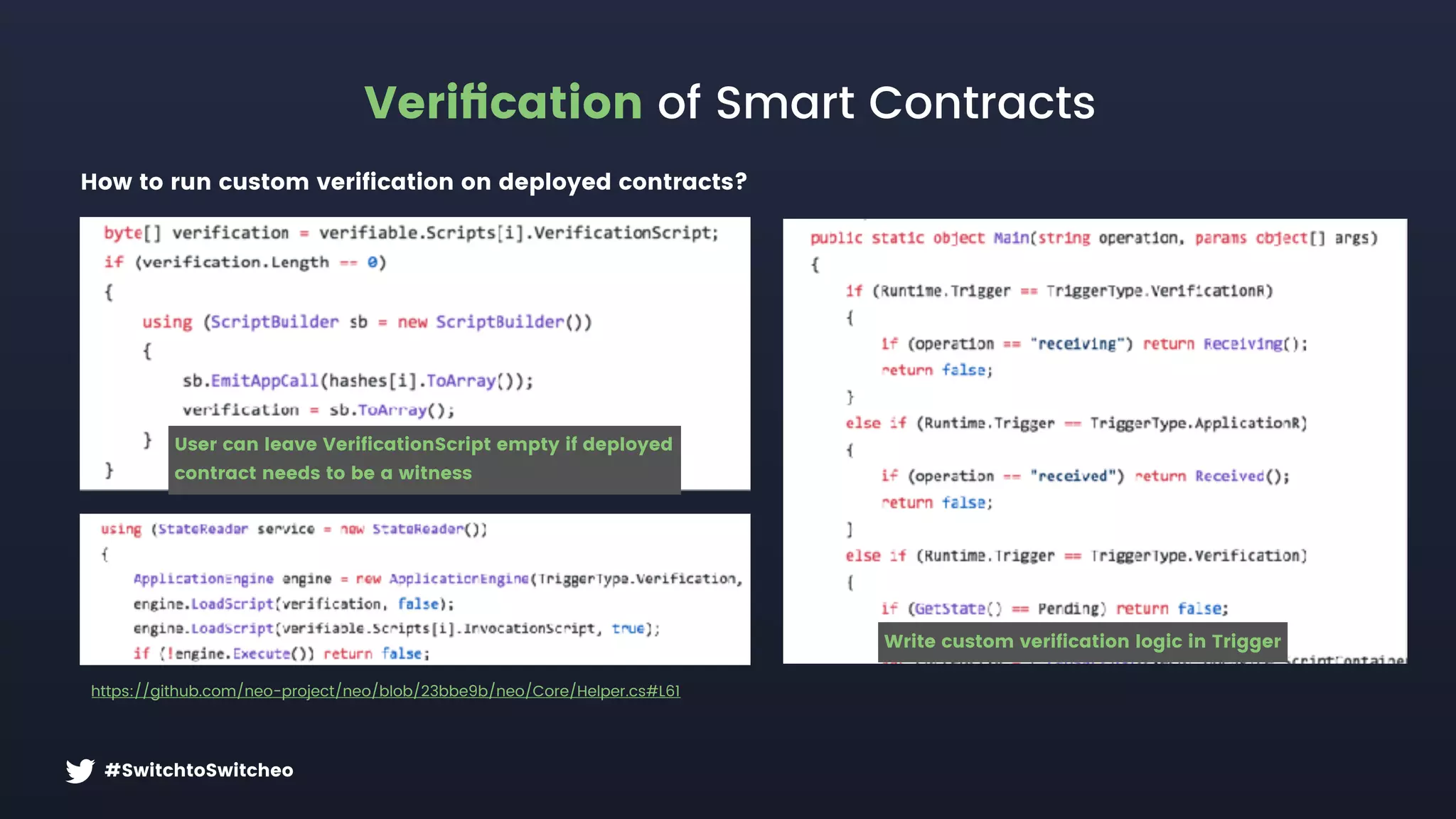
Verification of Smart Contracts
Verify([mempool]) VerifyScripts(IVerifiable) GetScriptHashesForVerifying()
https://github.com/neo-project/neo/blob/
23bbe9b/neo/Core/Transaction.cs#L330
https://github.com/neo-project/neo/blob/
23bbe9b/neo/Core/Helper.cs#L46
https://github.com/neo-project/neo/blob/
23bbe9b/neo/Core/Transaction.cs#L227
Check Double Spend,
etc..
Get hashes that must match
Verification Scripts
(found in “scripts”)
Get hashes of inputs
Add data (hash) in
transaction attribute
0x20 (usage “Script”
a.k.a. “Additional
Witness”)
This is useful if you
want to ensure
Verification runs on a
deployed contract, but
are not using inputs
from a smart contract
Hashes each VerificationScript
and compares hashes in order.
Fails if any missing or does
not match.
Executes Invocation Script
+ Verification Script.
Fails if hash mismatch, or
does not return true
Pass!](https://image.slidesharecdn.com/switcheoneoworkshop30jun-180705162252/75/Switcheo-Network-Advanced-NEO-Smart-Contracts-14-2048.jpg)