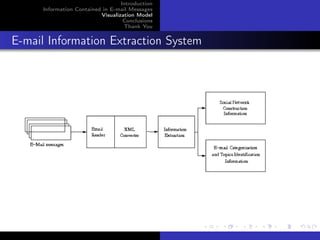
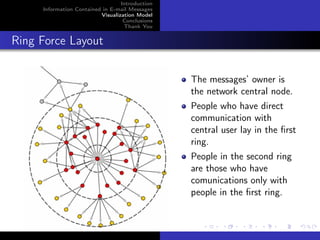
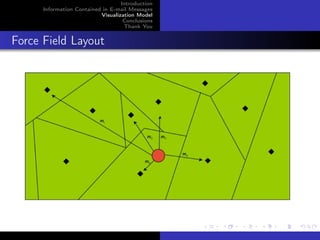
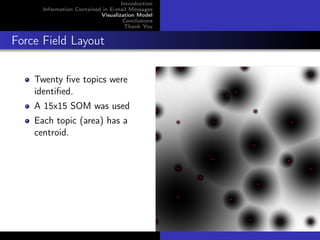
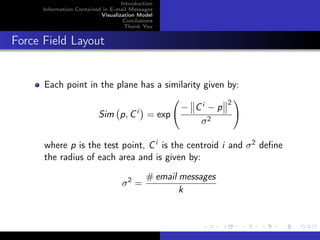
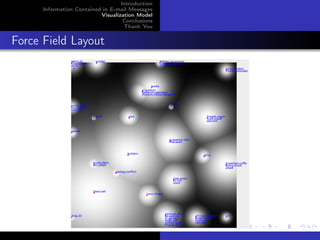
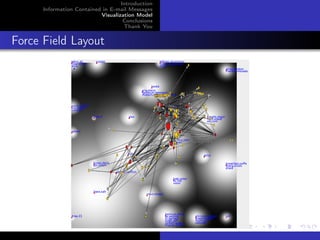
The document discusses a model for visualizing information contained in email messages, emphasizing the extraction of both content and contact information. It explains how emails can reveal connections within a personal social network and how different layouts, such as force field and Som maps, can represent these relationships based on topics and communication patterns. The conclusions highlight that email messages contain valuable, often hidden, information that can be leveraged to understand user interactions and topics of interest.