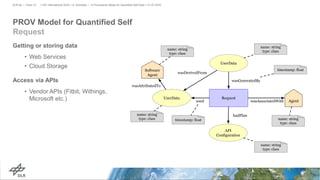
The document proposes a provenance model for quantified self data based on the W3C PROV standard. It describes motivations like understanding how QS data is produced, processed and accessed. The PROV standard concepts of entities, activities and agents are used to model common QS workflows like input, export, request, aggregate and visualize. Examples demonstrate exporting data from an app and visualizing with a script. The model could be used to standardize provenance for developers and allow traceability, reproducibility and analytics of QS data.